Response: How Ledger Hacked an HSM – Cryptosense

HSM vendor fails basic security and integrity from a pen test.
The post Response: How Ledger Hacked an HSM – Cryptosense appeared first on EtherealMind.

HSM vendor fails basic security and integrity from a pen test.
The post Response: How Ledger Hacked an HSM – Cryptosense appeared first on EtherealMind.

Cloudflare’s operations in Europe, the Middle East and Africa (EMEA) have seen great progress over the past few years and the future looks even brighter. I joined as Head of EMEA Sales, taking responsibility for our customer-facing activity across the region, just over a year ago. I am encouraged by what we are building while being even more motivated by what lies ahead for our customers, our partners and our employees.
Cloudflare has a rich history in EMEA where London was one of the earliest bases for both the company’s engineering and also its customer-facing activities. In the subsequent years, we have expanded our customer-facing activity to include coverage into all the major EMEA countries and regions. We’ve built up a team of professional sales and business development people, capable systems engineers, dedicated customer success managers, thoughtful marketeers and a responsive customer support team who serve our existing customers and develop new ones as a committed and focused team.

We work on developing brand awareness for Cloudflare and extending our reach into the market through communications, events and most of all through ongoing close engagement with customers, prospective customers and partners. We carry the Cloudflare mission of helping build a Continue reading

A new survey shows that only a handful of people who said they distrust the Internet are actively choosing encryption in response.
The survey, called the CIGI-Ipsos Global Survey on Internet Security and Trust, was conducted by Ipsos on behalf of the Canadian think tank the Centre for International Governance Innovation (CIGI). The Internet Society (ISOC) and the United Nations Conference on Trade and Development (UNCTAD) are partners in the survey, which is now in its fifth year.
The survey asked more than 25,000 individuals in 25 economies their opinion on Internet security, privacy, and trust.
Trust is very personal. The word “trust” may mean different things to different people. What we consider to be trust is constantly evolving and is shaped by many factors including our culture, our education, and our experience.
The survey asked users how much they agree or disagree with the statement “Overall, I trust the Internet”. We did not ask users how much they trust the Internet to perform in specific ways or to provide a specific user experience. However, the question provides a rough indicator of positive or negative attitudes towards the Internet.
74% of respondents in 2019 agreed with the statement Continue reading
We got pretty far in our data deduplication in network data model journey, from initial attempts to network modeled as a graph… but we still haven’t got rid of all the duplicate information.
For example, if we have multiple devices connected to the same subnet, why should we have to specify IP address and subnet mask for every device (literally begging the operators to make input errors). Wouldn’t it be better (assuming we don’t care about exact IP addresses on core links) to assign IP addresses automatically?
 Besides macro radio access network equipment, "we have virtually everything else you need to build...
Besides macro radio access network equipment, "we have virtually everything else you need to build...
 Cisco kicked off Cisco Live with a series of updates to its intent-based networking architecture to...
Cisco kicked off Cisco Live with a series of updates to its intent-based networking architecture to...

On May 15th, the White House tweeted it had created a new online surveying tool for Americans to report instances of social media censorship due to political bias. Setting aside the politics of this move, there are serious privacy and security concerns that come with hosting such a survey on its website.
When users visit the reporting site, they’re required to give personal information including their name, citizenship status, zip code, phone number, and email address, all before any questions are actually asked about the alleged social media bias. They are then prompted to include links to their social media platforms, usernames, and other digitally-intrusive information.
Sound fishy? It should.
That is a significant amount of personal, highly-identifiable information to give up as a part of a selective survey. The irrelevance of most of this information to the survey’s purpose begs the question: why does the government need it and what will they use it for?
Neither question is answered anywhere in the survey or its related materials. That alone poses a serious privacy concern. If users don’t know how their data will be used, how can they trust that their information is secure and being used only for the Continue reading
If you want to see what the future of the Kubernetes container management system will look like, then the closed source, homegrown Tupperware container control system that Facebook has been using and evolving since 2011 – before Docker containers and Kubernetes were around – might be a good place to find inspiration. …
Future Kubernetes Will Mimic What Facebook Already Does was written by Timothy Prickett Morgan at .

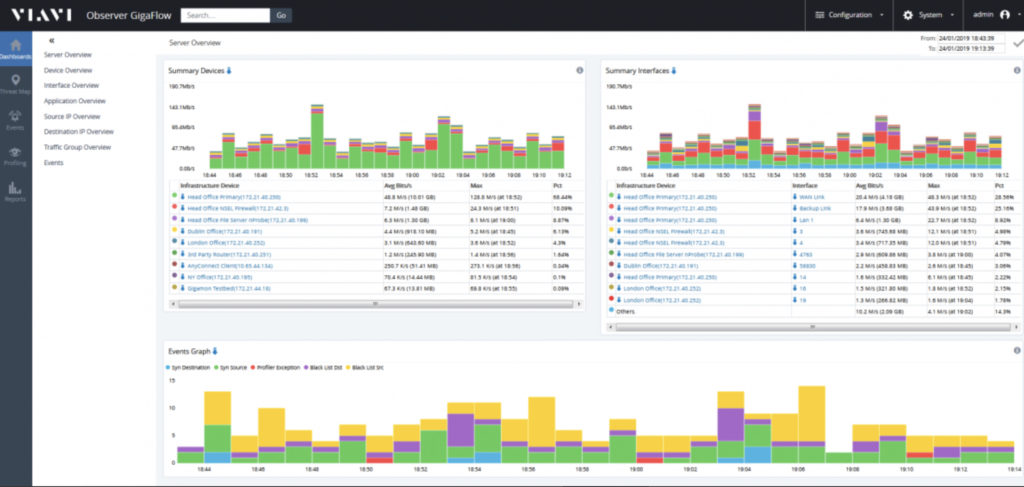
Many of us will have experienced the challenges of taking a performance alert (or user complaint) and drilling down to root cause. Performance issues can be intermittent, and it can be difficult to get visibility of what caused a problem at a particular time. Viavi Enterprise thinks it has the answer, combining analysis of packet feeds (e.g. from taps and mirror ports) and IPFix, xFlow and cloud service flow logs to monitor application performance as it would be experienced by a user. Sounds good? It looked pretty good, too.
Nothing can happen without data, and that comes from a number of potential sources.

The Observer Gigastor product is available as a virtualized solution (to capture east-west traffic in virtualized environments), a portable appliance for tactical deployment, and two hardware appliance models (in a charming shade of purple) which can provide from 96TB to 1.2PB of storage. The idea of Gigastor is to capture packets at line rate and retain the raw packet data in case it’s needed later. The packets are analyzed, and that metadata is fed to the reporting and visualization system, Observer Apex.
It’s not always possible Continue reading

Today is the day that the CCIE changes. A little, at least. The news hit just a little while ago that there are some changes to the way the CCIE certification and recertification process happens. Some of these are positive. Some of these are going to cause some insightful discussion. Let’s take a quick look at what’s changing and how it affects you. Note that these changes are not taking effect until February 24, 2020, which is in about 8 months.
The first big change comes from the test that you take to get yourself ready for the lab. Historically, this has been a CCIE written exam. It’s a test of knowledge designed to make sure you’re ready to take the big lab. It’s also the test that has been used to recertify your CCIE status.
With the new change on Feb. 24th, the old CCIE written will go away. The test that is going to be used to qualify candidates to take the CCIE lab exam is the Core Technology exam from the CCNP track. The Core Technology exam in each CCNP track serves a dual purpose in the new Cisco certification program. If you’re Continue reading
 The nearly $16-billion deal comes just days after Google acquired data analytics firm Looker for...
The nearly $16-billion deal comes just days after Google acquired data analytics firm Looker for...
 The Dell’Oro Group market report also found Dell is the No. 1 server vendor by revenue share...
The Dell’Oro Group market report also found Dell is the No. 1 server vendor by revenue share...

Without access to standards bodies Huawei loses patent rights to a wide range of technology.
The post ◎ Standards Bodies, Patents, Huawei and Unexpected Consquences appeared first on EtherealMind.
 5G rollouts are ramping up in Europe as Vodafone also announced commercial launches in Italy and...
5G rollouts are ramping up in Europe as Vodafone also announced commercial launches in Italy and...
The longer you work on one system or application, the deeper the attachment. For years you have been investing in it—adding new features, updating functionality, fixing bugs and corner cases, polishing, and refactoring. If the product serves a need, you likely reap satisfaction for a job well done (and maybe you even received some raises or promotions as a result of your great work).
Attachment is a two-edged sword—without some form of attachment, it seems there is no way to have pride in your work. On the other hand, attachment leads to poorly designed solutions. For instance, we all know the hyper-certified person who knows every in and out of a particular vendor’s solution, and hence solves every problem in terms of that vendor’s products. Or the person who knows a particular network automation system and, as a result, solves every problem through automation.
The most pernicious forms of attachment in the network engineering world are to a single technology or vendor. One of the cycles I have seen play out many times across the last Continue reading
On today's Network Break we dive into Google's self-inflicted outage, examine Apple's new HomeKit partnerships and Sign In, discuss the IEEE's reversal on Huawei, and parse other IT and tech news bits.
The post Network Break 238: Google Borks Itself; Apple Slices IoT Gadgets Into Security Zones appeared first on Packet Pushers.
At the recent EuroHPC Summit in Poland, the nature of Europe’s first homegrown HPC processor was described in some detail. …
Europe’s Homegrown HPC Compute Begins To Take Shape was written by Michael Feldman at .