Silver Peak Partners With NSC for Managed SD-WAN Services
 The partnership gives enterprises and service providers the opportunity to purchase SD-WAN...
The partnership gives enterprises and service providers the opportunity to purchase SD-WAN...
 The partnership gives enterprises and service providers the opportunity to purchase SD-WAN...
The partnership gives enterprises and service providers the opportunity to purchase SD-WAN...

Reading a transcript where Jonathan Davidson is taking to analysts and investors at the recent conference. He is Senior Vice President and General Manager of Cisco’s Service Provider Business since August 2018. He stats that the SP market is three distinct businesses” What SP buy for their own networks What SP consume as corporate IT […]
The post Cisco Sees Service Providers as Three Sales Models appeared first on EtherealMind.

Firefox 67 comes with boosted privacy settings but they aren’t activated by default if you have been using Firefox previously. Blocking trackers and privacy threats sometimes caused web pages to break so Mozilla has taken a cautious approach.
The post Check Your Firefox Privacy Settings appeared first on EtherealMind.
At The Next AI Platform event in May, we brought together a few leading investors on the deep learning chip front to talk about how they consider architecture, software, competitiveness, and market potential from the various approaches for both training and inference. …
VCs Look Beyond Architecture for Next Chip Success Stories was written by Nicole Hemsoth at .
Matt Stratton beams aboard the Datanauts starship to share his opinions and experiences with DevOps. Is DevOps a role you can hire for, or a culture you create? If it's the later, how do you get started, what are the impacts, and how do you iterate?
The post Datanauts 166: Can You Hire ‘DevOps’? appeared first on Packet Pushers.

This is a joint post by Whelan Boyd, Senior Product Manager at Optimizely and Remy Guercio, Product Marketing Manager for Cloudflare Workers.
Experimentation is an important ingredient in driving business growth: whether you’re iterating on a product or testing new messaging, there’s no substitute for the data and insights gathered from conducting rigorous experiments in the wild.
Optimizely is the world’s leading experimentation platform, with thousands of customers worldwide running tests for over 140 million visitors daily. If Optimizely were a website, it would be the third most trafficked in the US. And when it came time to experiment with reinvigorating their own platform, Optimizely chose Cloudflare Workers.
Cloudflare Workers is a globally distributed serverless compute platform that runs across Cloudflare’s network of 180 locations worldwide. Workers are designed for flexibility, with many different use cases ranging from customizing configuration of Cloudflare services and features to building full, independent applications.
In this post, we’re going to focus on how Workers can be used to improve performance and increase agility for more complex applications. One of the key benefits of Workers is that they allow developers to move decision logic and data Continue reading

The negatives of blitzscaling, a critique of building a monopoly
The post Thought For My Day: Blitzscaling is Monopoly Building appeared first on EtherealMind.

Applications are now open for the 2019 Beyond the Net Medium and Large Grants. All Internet Society Chapters and Special Interest Groups (SIGs) in good standing are eligible to apply.
For more than a decade, Beyond the Net Medium and Large Grants and the former Community Grants Programme have played a major role in empowering people to improve their communities via the Internet. These programmes have reached thousands of people by helping to bring to life community-driven projects that teach digital skills, enable continued trust in the Internet, build infrastructure in rural and underserved areas, and connect Indigenous communities.
The Beyond the Net Funding Programme is now part of the Internet Society Foundation, but will continue to support the excellent work of our Chapter and SIG communities. The Medium and Large Grants are available for funding at a maximum of USD $30,000.
Applications are open until 31 July 2019. For more details, visit Beyond the Net Medium and Large Grant Programme page.
While you’re there, check out everything else the Foundation is doing!
The post Want to Make a Difference in Your Community? Apply for a Beyond the Net Medium or Large Grant appeared first on Internet Society.
 The GCP integration will allow Snowflake customers to seamlessly store data in Google's public...
The GCP integration will allow Snowflake customers to seamlessly store data in Google's public...
Hello my friend,
Three years ago, on the 5th June 2016, we have posted the first article about Nokia SR OS/ Cisco IOS XR interop. We can dispute, if it was long ago or not, but what we can’t dispute the amount of information shared with you since that time on various network and automation topics!

2
3
4
5
retrieval system, or transmitted in any form or by any
means, electronic, mechanical or photocopying, recording,
or otherwise, for commercial purposes without the
prior permission of the author.
Over these three years we have posted 75 (seventy five!) articles about the design, configuration and implementation of the multivendor networks with Nokia SR OS, Cisco IOS XR, Arista EOS and Cumulus Linux. Out of that 75, the 21 articles were written in this third year. Thanks to the blog activity we were awarded as the CiscoChampion 2019 as a top tech influencers worldwide.
The last year was a kind of breakthrough, not only based on the topics we were covering, about which we’ll Continue reading
Approximately two years ago I tried to figure out whether aggressive marketing of deep buffer data center switches makes sense, recorded a few podcasts on the topic and organized a webinar with JR Rivers.
Not surprisingly, the question keeps popping up, so it seems it’s time for another series of TL&DR articles. Let’s start with the basics:
Read more ...Data validation for machine learning Breck et al., SysML’19
Last time out we looked at continuous integration testing of machine learning models, but arguably even more important than the model is the data. Garbage in, garbage out.
In this paper we focus on the problem of validation the input data fed to ML pipelines. The importance of this problem is hard to overstate, especially for production pipelines. Irrespective of the ML algorithms used, data errors can adversely affect the quality of the generated model.
Breck et al. describe for us the data validation pipeline deployed in production at Google, “used by hundreds of product teams to continuously monitor and validate several petabytes of production data per day.” That’s trillions of training and serving examples per day, across more than 700 machine learning pipelines. More than enough to have accumulated some hard-won experience on what can go wrong and the kinds of safeguards it is useful to have in place!
The motivating example is based on an actual production outage at Google, and demonstrates a couple of the trickier issues: feedback loops caused by training on corrupted data, and distance between data Continue reading

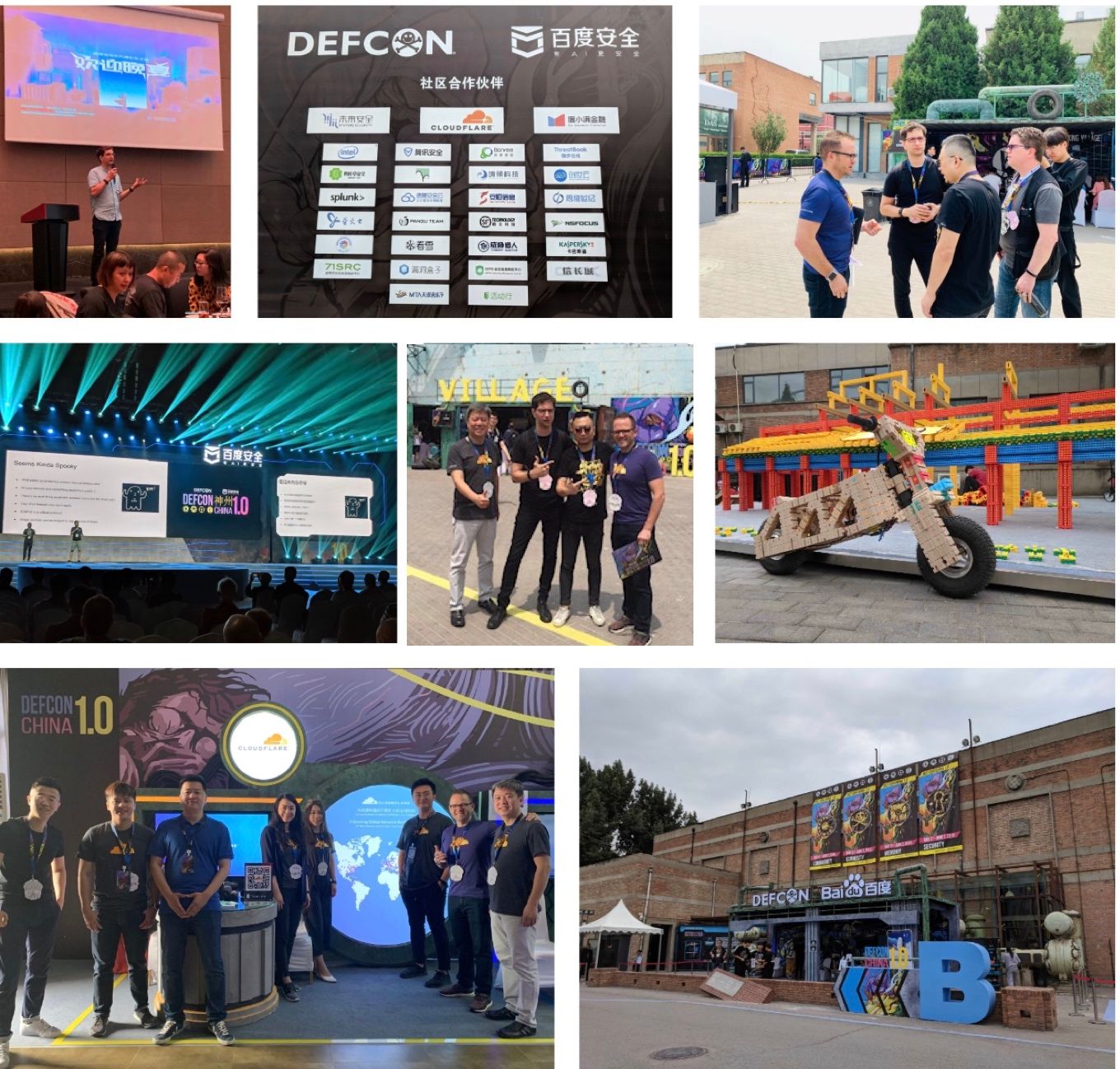
DEF CON is one of the largest and oldest security conferences in the world. Last year, it launched a beta event in China in hopes of bringing the local security communities closer together. This year, the organizer made things official by introducing DEF CON China 1.0 with a promise to build a forum for China where everyone can gather, connect, and grow together.
Themed "Technology's Promise", DEF CON China kicked off on 5/30 in Beijing and attracted participants of all ages. Watching young participants test, play and tinker with new technologies with such curiosity and excitement absolutely warmed our hearts!
It was a pleasure to participate in DEF CON China 1.0 this year and connect with local communities. Great synergy as we exchanged ideas and learnings on cybersecurity topics. Did I mention we also spoiled ourselves with the warm hospitality, wonderful food, live music, and amazing crowd while in Beijing.
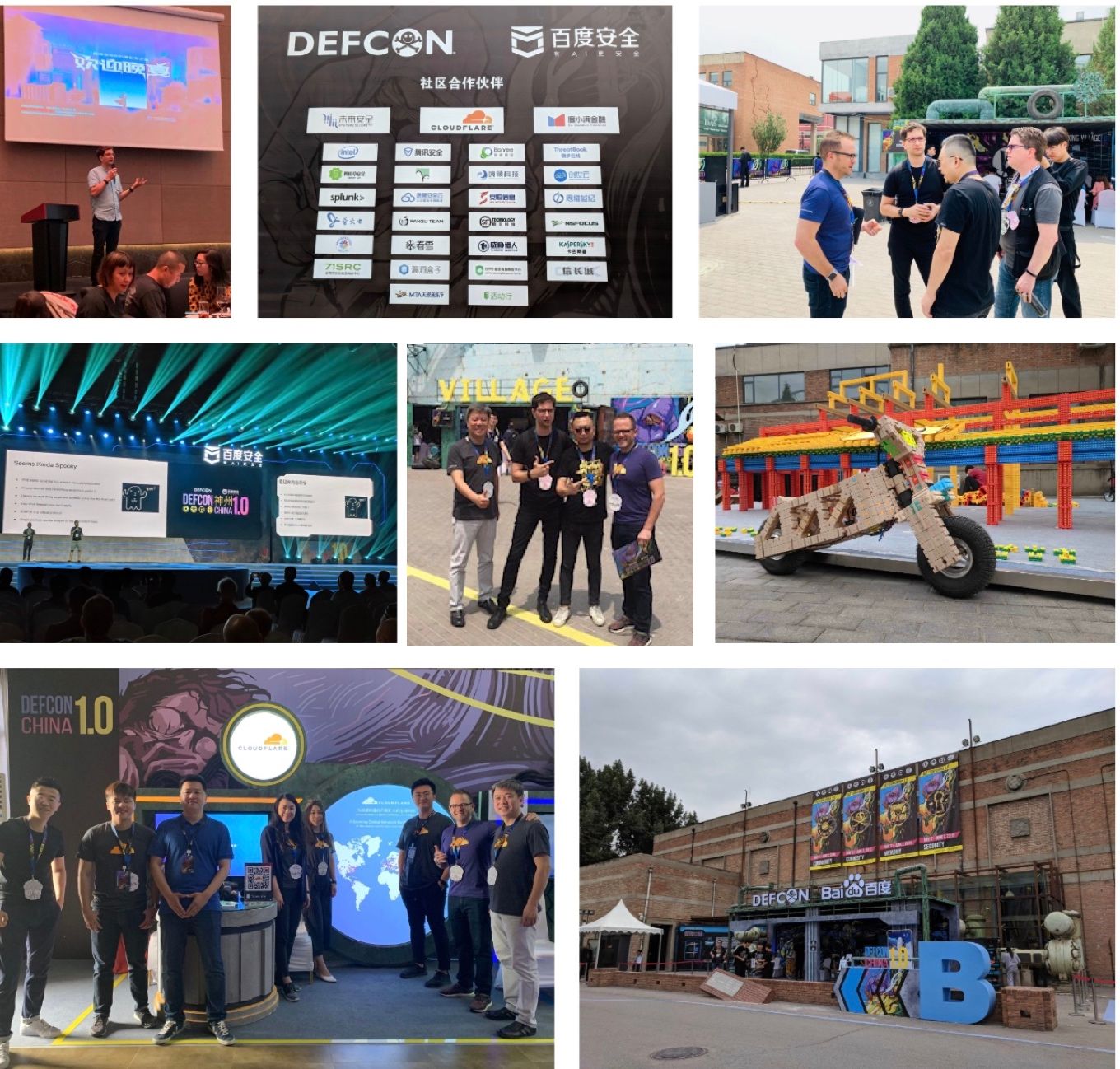
Meet our youngest and cutest attendee today at BugZee village. Meet 8 year old "Joy" from Beijing who did phenomenal soldering. Amazing crowd at Continue reading

科技在发展,时代在进步,许多事情或许本质并没有改变,但呈现的方式已经日新月异,这或许就是我们常说的 — 未来。就像许多年前,我们还通过明信片和相册向亲友分享我们生活中的点点滴滴。许多年后,我们有了朋友圈、微博、Facebook、Instagram、抖音、各式博客。幼时还守着电视看着预录好的节目,接触外界的形形色色,现在我们透过直播的镜头,弹指间便能瞬息感受世界当下的脉动。
许多人都在电影中看到过极客指尖敲动,在数字的世界中急速驰骋的场景。然而现实生活中,这些人在哪儿不得而知。随着技术的发展,越来越多的年轻人加入了这个群体。在国外一直都有 DEF CON 这样的世界极客盛会。中国此前也还没有,直到去年 DEF CON 来到了中国,主办方斥巨资引进大会,想打造属于中国的技术社区,通过这样一个契机,将大家聚在一起,一同成长,最终构建一个属于中国自己的、真正的安全社区。于是,在 DEF CON 的名下,多了一个 DEF CON China。
今年,DEF CON 经过一年的沉淀后,进入了正式版本 1.0,这个世界顶级的安全会议,在五月底,以 "Technology's Promise" — “科技点燃未来” 为主旨,于北京拉开了序幕,像是一位家长等待着 “孩子们” 一起过节。这个六一,还有什么能比来 DEF CON China 1.0 众乐乐更具意涵呢?
作为在中国地区的正式版本,DEF CON China 吸引了很多大咖前来参与,一直致力于网络安全的 Cloudflare,这次也前来共襄盛举,带来了最新的科技跟大家分享。
Meet our youngest and cutest attendee today at BugZee village. Meet 8 year old "Joy" from Beijing who did phenomenal soldering. Amazing crowd at @defcon China. pic.twitter.com/ub1qpGyGso
— Abhinav SP | #BugZee, DEFCON China (@TweetsFromPanda) May 31, 2019
All my root lights are on! #unlocked #DEFCONChina 1.0 @defcon #badgelife @Hyr0n1 ?? pic.twitter.com/YXJDW0vuds
— donds (@donds) May 31, 2019

Cloudflare 成立于 2009 年,是一家跨国科技公司,在全球 80 个国家部有 180 个数据中心。我们的性能和安全服务协同工作,以减少网站、移动应用程序和端到端 API 的延迟,同时防御 DDoS 攻击、滥用机器人和数据泄露。
此次大会是 Cloudflare 在区域深耕的第一小步。相信随着时间的推移,越来越多的用户会认识并了解 Cloudflare,此而加入我们。点此启用免费帐户,立即体验更快更安全的网络:cloudflare.com/sign-up
人才招聘中
Cloudflare 具有全球视野、本地化洞见的团队期待构建更好的全球互联网未来。我们北京和全球的办公室都在招聘人才,欢迎有志一同的伙伴加入我们!cloudflare.com/careers

It is just about time for Cisco Live 2019! Here are some quick things you should know before you go. …
The post Cisco Live – Are you ready? appeared first on Fryguy's Blog.
It is just about time for Cisco Live 2019! Here are some quick things you should know before you go. …
The post Cisco Live – Are you ready? appeared first on Fryguy's Blog.
 Remarks from President Donald Trump suggest the U.K. could change its position on letting Huawei...
Remarks from President Donald Trump suggest the U.K. could change its position on letting Huawei...