Palo Alto Networks Launches Prisma Cloud Security as Twistlock Acquisition Rumors Swirl
 The vendor has reportedly reached deals to buy container security startup Twistlock for between...
The vendor has reportedly reached deals to buy container security startup Twistlock for between...
 The vendor has reportedly reached deals to buy container security startup Twistlock for between...
The vendor has reportedly reached deals to buy container security startup Twistlock for between...
In this episode we take a look at the gradual shift to subscription based licensing, how 5g could potentially set back weather radar 30+ years, and a conversation about the hype cycle in networking.
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Creative Commons: By Attribution 3.0 License
http://creativecommons.org/licenses/by/3.0/
The post Subscription Licensing, The 5g Time Machine & The Trough Of Disillusionment appeared first on Network Collective.
Earlier in May during The Next AI Platform event in San Jose, we conducted live, technical interviews with a broad range of experts in various areas of deep learning hardware. …
AI Chip Leads Debate Training, Inference Accelerator Trends was written by Nicole Hemsoth at .

We're excited to announce that Red Hat Ansible Tower 3.5 is now generally available. In this release, there are several enhancements that can help improve automation practices. Engineering has been working hard to enhance Ansible Tower and here are a few things we're most excited about:
In addition to a number of enhancements that have been made, the Ansible Tower 3.5 release saw over 160 issues closed. Let’s go over the highlights in this release.
Red Hat Enterprise Linux is an innovative operating system, designed to provide a consistent foundation for the enterprise hybrid cloud. It offers one enterprise Linux experience for applications across IT environments. With Ansible Tower 3.5 (and Ansible Engine 2.8), support for managing RHEL 8 nodes is baked in. Ansible Tower 3.5 can also be run on Red Hat Enterprise Linux 8 as the control node for Red Hat Ansible Automation.
Ansible Tower 3.5 brings support for external credential vaults. The existing credential store is still available for use. However, Continue reading

Red Hat Ansible Engine 2.8 is now available. This release features many improvements and enhancements (please refer to the CHANGELOG for more details). Also, new features worth highlighting here are Ansible content (Collections), BECOME being the default privilege escalation path, no longer depending on paramiko, and BECOME plugins, and other notable improvements and changes.
The Ansible community is excited to provide new modules and plugins for Ansible users. This keeps Ansible maintainers busy; merging new code into repositories as fast as a team can. Occasionally, things get left behind. Content that could have been released ends up waiting for the next Ansible Engine release. Currently, the official Ansible Engine release process is the only way for users to utilize or consume new content easily.
As such, the Ansible community has begun the journey of providing our users with more flexibility to create and consume content. In Ansible Engine 2.8, modifications are in place for how Ansible Engine handles content not delivered in the official release. These changes allow for the creation of a new delivery method to users. This delivery method should not depend on Ansible maintainers to manage content Continue reading

After more than a decade of regulatory ping pong, net neutrality’s future in the United States is still unclear.
Since 2004, FCC rulemakings have been caught in a vicious cycle. They have been passed, fought in court, and returned to the FCC with minor (and sometimes major) revisions. In the last few years there have also been numerous attempts to pass legislation, cementing net neutrality once and for all, but nothing has succeeded in Congress.
Recognizing the importance of finding a sustainable solution, the Internet Society proposed a collaborative process to help experts find common ground on this complex policy issue. Starting in June 2018, we convened an ideologically diverse group of experts to create a baseline set of principles for an open Internet.
The Net Neutrality Experts’ Roundtable series included representatives from the technical community, edge providers, academia, Internet service providers, industry associations, and both left- and right-leaning civil society groups.
In a series of meetings over ten months, participants discussed how to create a sustainable solution for net neutrality that protect the interests of Internet users while fostering an environment that encourages investment and innovation.
Ultimately, the group was able to create a consensus-driven set of bipartisan principles for an open Continue reading

Cloudflare is partnering with PiscArt to create a meetup this month at PicsArt office in Yerevan. We would love to invite you to join us to learn about the newest in the Internet industry. You'll join Cloudflare's users, stakeholders from the tech community, and Engineers from both Cloudflare and PicsArt.
PicsArt office, Yerevan

View Event Details & Register Here »
We'll hope to meet you soon. Here are some photos from the meetup at PicsArt last year:




TL&DR: MIA
Six years ago, when I was talking about overlay virtual networks at Interop, I loved to joke that we must be living on a weird planet where Microsoft has the best overlay virtual networking implementation… at least as far as IPv6 goes.
Even then, their data plane implementation which was fully dual-stack-aware on both tenant- and underlay level was way ahead of what System Center could do.
Read more ...Boosted race trees for low energy classification Tzimpragos et al., ASPLOS’19
We don’t talk about energy as often as we probably should on this blog, but it’s certainly true that our data centres and various IT systems consume an awful lot of it. So it’s interesting to see a paper using nano-Joules per prediction as an evaluation metric. The goal is to produce a low-energy hardware classifier for embedded applications doing local processing of sensor data. To get there, the authors question a whole bunch of received wisdom, beginning with this: do we really need to convert the analog sensor data into a digital signal?! Here’s another fun one: what if instead of being something you worked hard to avoid, you had to build your whole application based on the outcomes of data races??!
Typically, a sensor gathers analog information from the physical world and then converts it into a conventional digital signal… While this binary-represented integer is perfectly efficient for storage as bits in memory and for typical general purpose computing operations, it is unclear that this is the most efficient for our target application. One such possible representation is pure analog signalling.
Of course analog signalling comes Continue reading
The Antidote network emulator, part of the Network Reliability Engineering project, offers a web interface that presents network emulation scenarios to users as documented lessons. Each lesson is presented in a window running Jupyter Notebooks and contains commands that the user can click on to run them on the virtual nodes in the network emulation scenario.

The NRE Labs developers intend for Antidote to be used as an educational tool. Its lesson-focused user interface supports students’ learning progress. This post is a tutorial showing how to create and test two simple, but different, Antidote lessons.
At the time I wrote this post, the Antidote documentation does not provide enough practical information about how to create new Antidote labs. However, useful information is spread around in a few different locations, which I list below:
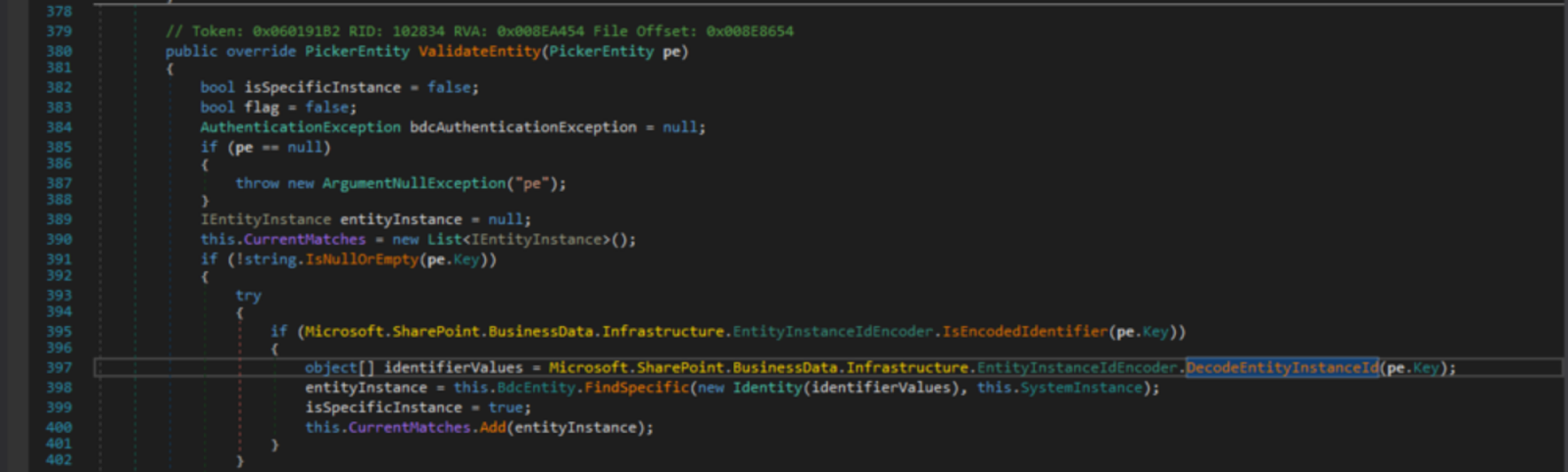
On Saturday, 11th May 2019, we got the news of a critical web vulnerability being actively exploited in the wild by advanced persistent threats (APTs), affecting Microsoft’s SharePoint server (versions 2010 through 2019).
This was CVE-2019-0604, a Remote Code Execution vulnerability in Microsoft SharePoint Servers which was not previously known to be exploitable via the web.
Several cyber security centres including the Canadian Centre for Cyber Security and Saudi Arabia’s National Center put out alerts for this threat, indicating it was being exploited to download and execute malicious code which would in turn take complete control of servers.
The affected software versions:
The vulnerability was initially given a critical CVSS v3 rating of 8.8 on the Zero Day Initiative advisory (however the advisory states authentication is required). This would imply only an insider threat, someone who has authorisation within SharePoint, such as an employee, on the local network could exploit the vulnerability.
We discovered that was not always Continue reading

Open, free and ready for you to join.
The post Virtual Design Clinic 5 – Continues appeared first on EtherealMind.
 The server manufacturer also said it will contribute an open firmware development kit to the...
The server manufacturer also said it will contribute an open firmware development kit to the...
 If Sprint and T-Mobile gain approval from regulators to merge, it will impact infrastructure...
If Sprint and T-Mobile gain approval from regulators to merge, it will impact infrastructure...

In Red Hat Ansible Tower 3.1 we released a feature called Workflows. The feature, effectively, allowed users to compose job templates into arbitrary graph trees. A simple workflow we saw users creating was a linear pipeline; similar to the workflow below.

The workflow feature also allowed branching. Each branch can run in parallel.

But something was missing. The ability to wait for previous parallel operations to finish before proceeding. If this existed, you could simplify the above workflow (see below).

In Red Hat Ansible Tower 3.4 the above workflow is now possible with the introduction of the Workflow Convergence feature.
For you computer sciencey folks, workflows are no longer restricted to a tree, you can create a DAG. More simply, we call this convergence; two nodes are allowed to point to the same downstream node. The concept is best shown through an example. Above, we have a workflow with 3 nodes. The first two job templates run in parallel. When they both finish the 3rd downstream, convergence node, will trigger.
In this blog post we will cover the changes to workflow failure scenarios, how workflow node failure and success propagate, how this affects the runtime graph and how Continue reading