Fortinet Next Generation Firewalls : Fortinet 5000 Series Firewalls
Now I am going to talk about the Fortinet Next Generation Firewalls.
Fortinet Next Generation Firewalls
 |
| Fig 1.1- Fortigate Next Generation Firewalls |
 |
| Fig 1.1- Fortigate Next Generation Firewalls |
The argument for end-to-end encryption is apparently heating up with the work moving forward on TLSv1.3 currently in progress in the IETF. The naysayers, however, are also out in force, arguing that end-to-end encryption is a net negative. What is the line of argument? According to a recent article in CircleID, it seems to be something like this:
The idea of end-to-end encryption is recast as a form of extremism, a radical idea that should not be supported by the network engineering community. Is end-to-end encryption really extremist? Is it really a threat to the social order?
Let me begin here: this is not just a technical issue. There are two opposing worldviews in play. Engineers don’t often study worldviews, or philosophy, so these questions tend to get buried in Continue reading
 The deal gives VMware more networking clout to better compete with Cisco.
The deal gives VMware more networking clout to better compete with Cisco.
OpenStack Summit Sydney is just around the corner, and Cumulus Networks wouldn’t miss it for the world! We’ll be there at our booth, doing daily contests and raffles, so make sure to stop by. If you’re lucky, you might walk away with a 6 pack of Linux Lager. But of course, you don’t need beer to have fun at OpenStack — there’s so much to keep you busy and fired up! With so many amazing panels and presentations, it’s hard to pick and choose which events to attend. Fortunately, we’ve done the research and picked out the top 3 must-attend activities. If you’re going to be at OpenStack in Sydney next week, make sure to check these out:
 Open Baton adds Docker container support to its MANO code.
Open Baton adds Docker container support to its MANO code.
Intesa Sanpaolo is the largest bank in Italy and maintains a network of over 5,000 banking branches across Europe and North Africa. With nearly 19 million customers and €739 billion in assets, Intesa Sanpaolo is an integral part of the financial fabric and as such, Italian regulations require that they keep their business and applications online to serve their customers.
As a bank that can trace its roots back to the early 1800s, the majority of Intesa’s edge applications are still monolithic and hard to move between data centers, never mind migrate to the cloud. Diego Braga, Intesa IT Infrastructure Architect, looked to Docker Enterprise Edition (EE) at the recommendation of his Kiratech business partner Lorenzo Fontana to improve their application availability, portability and add cloud friendly application delivery. With Docker EE, Intesa was able to consolidate infrastructure by nearly 60%, thus saving significant money over their previous design, while also enabling higher application availability across regional data centers and preparing themselves for the cloud.

Prior to the Docker EE implementation, not only were the applications monoliths, but Intesa maintained two separate data centers as mirrors of each other to achieve high availability. This design required excess, cold standby hardware capacity in Continue reading
In September 2016 I wrote the article about EIGRP support in Quagga network routing suite. More than one year later, I am going to check the progress of development EIGRP in Linux again. To do so, I have installed a fork of Quagga - FRRouting (FRR) with EIGRP support on Linux Core. EIGRP routing daemon included inside FRR benefits from active development brought by Cumulus employees. For the purpose of FRR testing, I have created a minimalistic Linux Core Pure64 virtual machine with FRR suite compiled as frr extension. Meanwhile, I have submitted FRR extension so it will be available in the next few days in Tinycore repository.
Content of Disk - CorePure64-frr_3-1.vmdk:
Software:
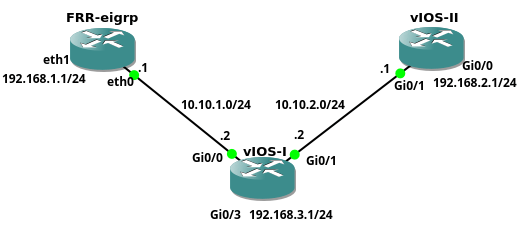 Picture 1 - Network Topology
Picture 1 - Network Topology
The FRR EIGRP instance with attached CorePure64-frr_3-1.vmdk Continue reading
By Milin Desai, Vice President of Products, NSBU
It feels like only yesterday when we started our journey into networking at VMware. Even from the early beginnings in 2011, it became clear to some of us that the abstraction and operations model of virtualization for compute and memory, which completely transformed the modern data center, was something we needed to extend to networking. We understood that that a network based on software and abstraction in the long run would extend beyond our customers’ data centers to public clouds and ultimately to the Edge.
We’ve been executing on this vision for almost eight years; reinventing data center networking and enabling our customers to be smarter about how they secure, manage and connect their applications and users.
Starting with the Data Center
The Nicira acquisition, alongside our internal innovations, resulted in the release of VMware NSX in 2013. VMware NSX made network virtualization a mainstream possibility for the data center. The goal was simple — abstract the application from the physical network and deliver the networking attributes in software at machine speeds. After four years, multiple thousands of customers and the creation of a billion-dollar run rate business, we have transformed the Continue reading
On October 31st, the oVirt project released version 4.2.0 Beta, available for Red Hat Enterprise Linux 7.4, CentOS Linux 7.4, or similar.
Since the release of oVirt 4.2.0 Alpha a month ago, a substantial number of stabilization fixes have been introduced.
Support for LLDP, a protocol for network devices for advertising identity and capabilities to neighbors on a LAN. LLDP information can now be displayed in both the UI and via the API. The information gathered by the protocol can be used for better network configuration.
oVirt 4.2.0 Beta features Gluster 3.12.
oVirt's hyperconverged solution now enables a single replica Gluster deployment.
OVN (Open Virtual Network) is now fully supported and recommended for isolated overlay networks. OVN is automatically deployed on the the host, and made available for VM connectivity.
Snapshots can now be uploaded and downloaded via the REST API (and the SDKs).
An improvement has been introduced to the self-hosted engine. Now, the self-hosted-engine will connect to all IPs discovered, allowing both higher performance via multiple paths as well as high availability in the event that one of the targets fails.
A new Continue reading
With the growth of cloud services, enterprises need to ensure users don't run into network bottlenecks.
With the growth of cloud services, enterprises need to ensure users don't run into network bottlenecks.