Red Hat kicks off annual Summit by leaning dev-wards
Red Hat’s annual summit opened today with the announcement of three new products aimed with uncharacteristic directness at developers, rather than the company’s usual target of IT operations staff.Openshift.io is the company’s free SaaS development environment, specifically designed for cloud-native apps, that lets geographically far-flung teams work together and automatically containerizes code for easy deployment. The environment builds on open source projects like Kubernetes-focused development platform fabric8, IDE Eclipse Che, and automation server Jenkins.+ALSO ON NETWORK WORLD: Red Hat CEO: Open-source innovation is always user-led + Which Linux distros should newbies use?To read this article in full or to leave a comment, please click here


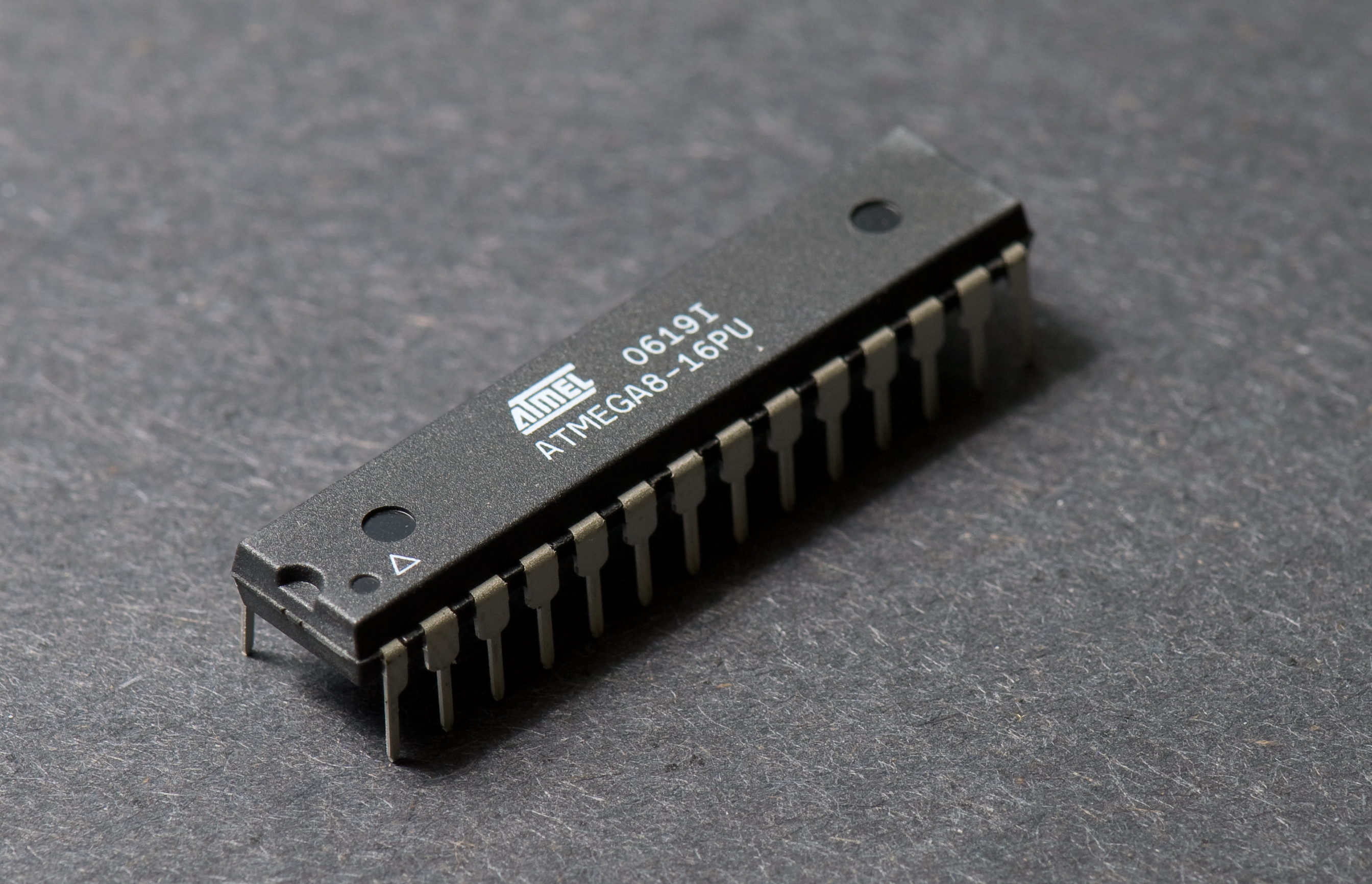
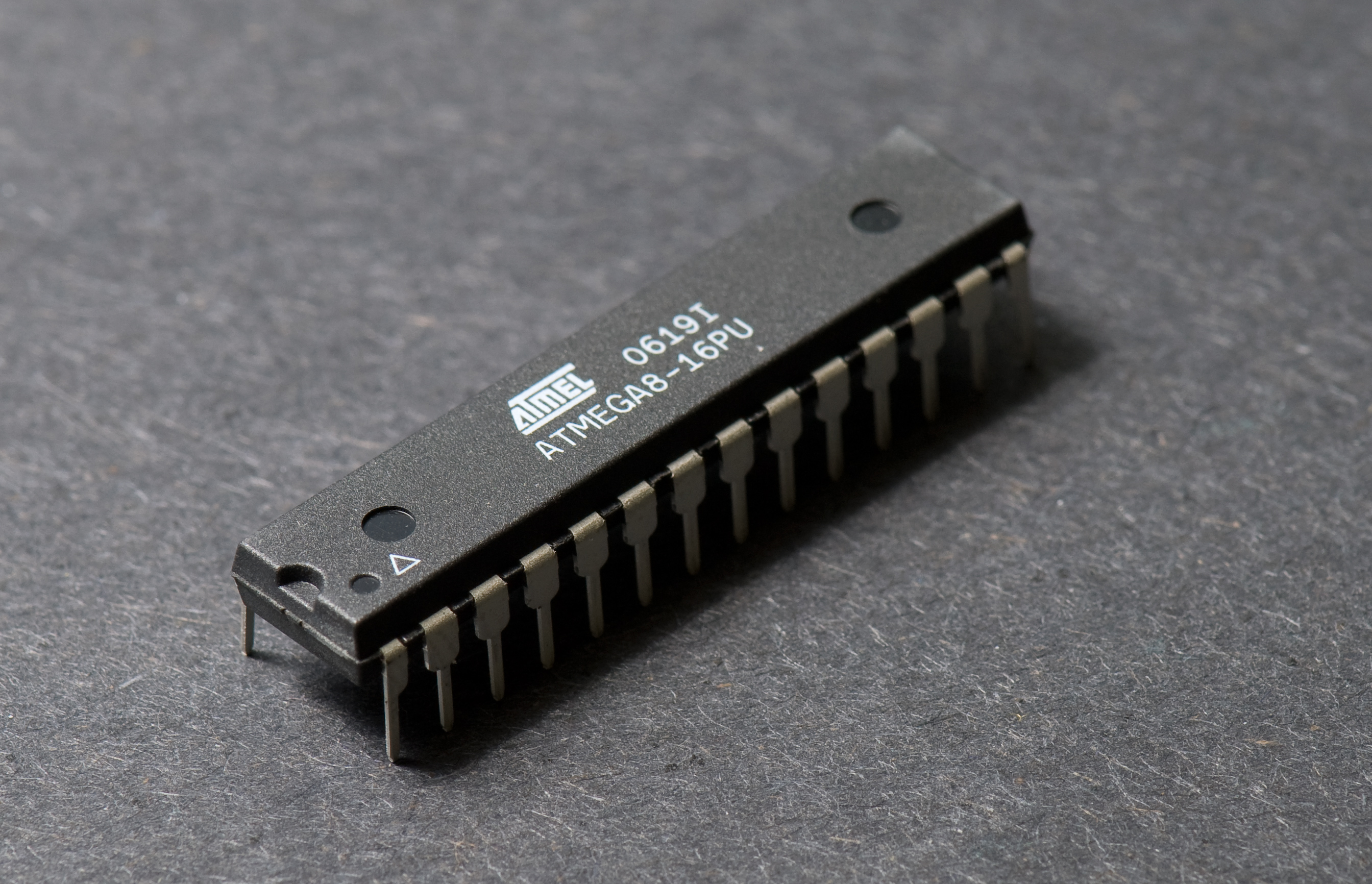 Atmel ATMEGA8 Microcontroller
Atmel ATMEGA8 Microcontroller