0
Study warns of human rights risks from censoring online terror content
Internet companies should not be required to monitor third-party terrorist content that they host or transmit, nor should they face direct or indirect liability from governments for such content, according to a new study. The Global Network Initiative, a group that represents academics, investors, civil society organizations and companies including Facebook, Google and Microsoft, published its study Tuesday. It's the offshoot of a policy discussion it started in July 2015, exploring key issues such as the human rights implications of government efforts to restrict online content with the aim of protecting public safety.To read this article in full or to leave a comment, please click here
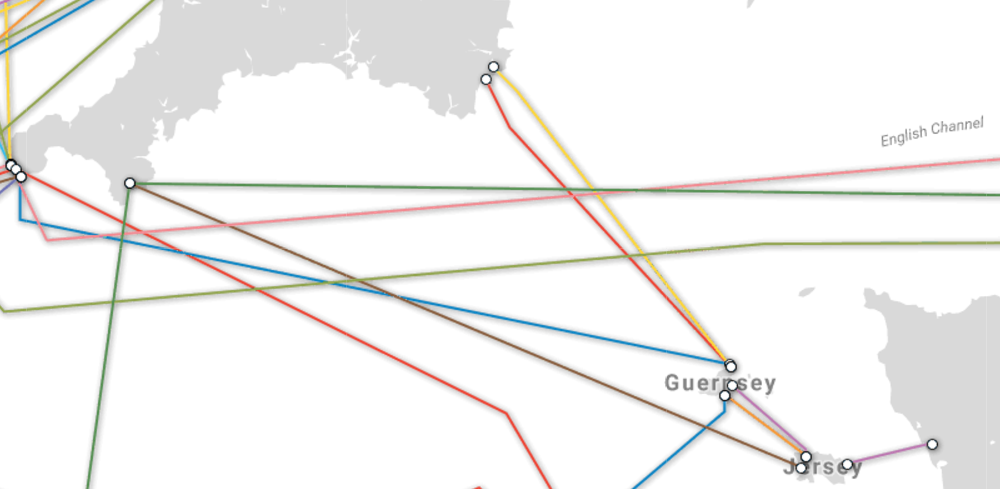 Image courtesy
Image courtesy 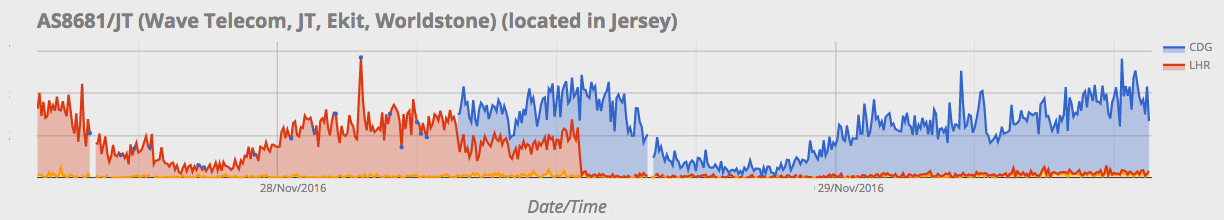 The red traffic is being served from our London data center (the normal location for all Jersey traffic) and the blue traffic is coming from our Paris data center. The step could well be caused by either a delayed break in one of the cables or the
The red traffic is being served from our London data center (the normal location for all Jersey traffic) and the blue traffic is coming from our Paris data center. The step could well be caused by either a delayed break in one of the cables or the  Tom Lantzsch makes the jump in January.
Tom Lantzsch makes the jump in January. Yep, still losing money (but growing mightily).
Yep, still losing money (but growing mightily).