How Does NetBeez Rate For Troubleshooting?
Continuing from my previous NetBeez post, I’d like to share some more detail on the charting and reporting capabilities of the product, and my experience using NetBeez to troubleshoot some real network issues.
Incidentally, as advertising slogans go, this one is surprisingly effective; I was surprised at how many people do actually approach and say “Ok go on then, tell me about your beez?”
Hands On Operations
I have been able to spend some time digging around the interface in anger, as it were, and seeing whether the NetBeez tools might raise an alert that otherwise wasn’t caught by other systems. To that end, I have one happy story, but also a number of things I found I wanted to be able to do, but couldn’t. These are things I might not have thought about had I not actually been using them for real, rather than just with test data.
Charts
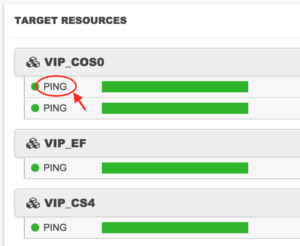
The actual charts are quite nicely put together, although getting there can be a little cumbersome unless linked directly from an alert or something. For example, here is the top of the list of Resources within one of my Target test sets:
If I click on the PING Continue reading