Micro-Fiber, Meet Micro-Segmentation! Columbia Sportswear Virtualizes the Network, Saves Millions
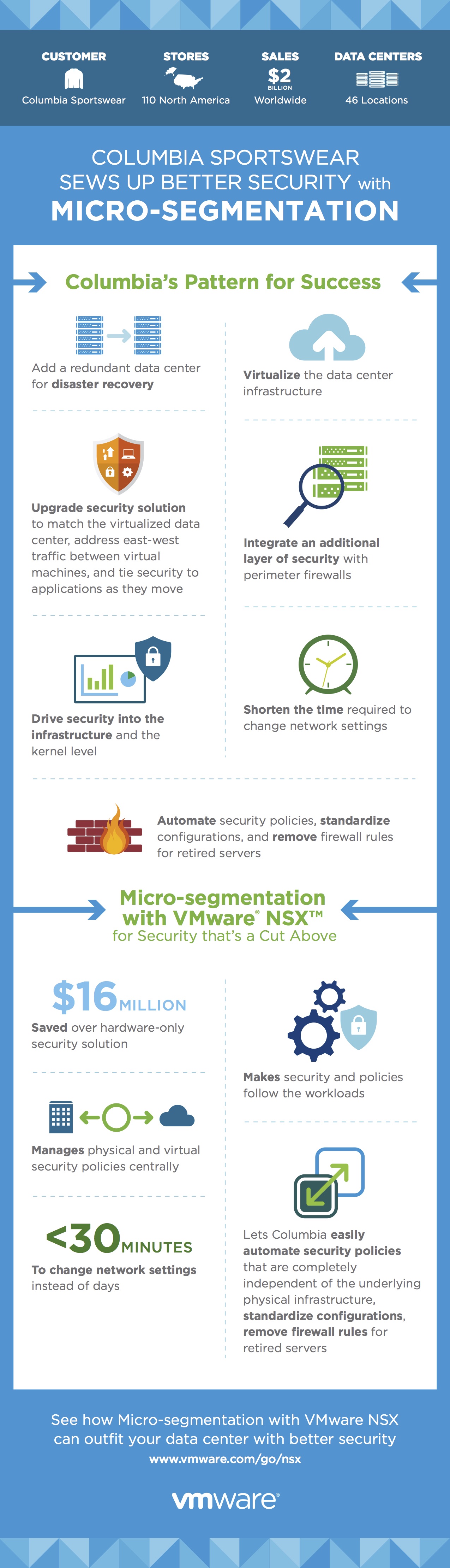
With 110 stores in North America, 46 data center locations, and $2 billion in revenue, Columbia Sportswear is constantly processing huge amounts of data—data whose security was being compromised by their inadequate hardware-defined data center.
When Columbia Sportswear virtualized their network, they not only stepped up their security; they also saved $16 million over a comparable hardware-based security approach.
Download our free ebook: Redefining Networking with Network Virtualization
How? Find out here. Follow their process step by step in the infographic below.
The post Micro-Fiber, Meet Micro-Segmentation! Columbia Sportswear Virtualizes the Network, Saves Millions appeared first on The Network Virtualization Blog.

 Investors wanted more, apparently.
Investors wanted more, apparently. Guidelines will be released in June.
Guidelines will be released in June.