Top 4 Strategies for NFV Success
 NFV can deliver tremendous rewards.
NFV can deliver tremendous rewards.
 NFV can deliver tremendous rewards.
NFV can deliver tremendous rewards.
PlexxiPulse—We’ve been busy in The District!
You may have seen that we announced our partnership with CloudGov Technologies last week, a leading IT provider servicing the government and commercial markets. We spent the week in Baltimore alongside our newest partner and PSSC Labs at the AFCEA Defensive Cyber Operations Symposium spreading the word on how third era solutions transform the agility and performance of federal networks. Next week, we’ll be in Washington, D.C. with CloudGov at the GEOINT 2015 Symposium. This is the first year that the Symposium is being held in the nation’s capital—we’re excited to share our vision with attendees and learn from the impressive list of conference speakers. Drop us a line on Twitter or at [email protected] if you’re in town and interested in chatting with the team or scheduling a live demo!
Below please find a few of our top picks for our favorite news articles of the week. Have a great weekend!
Forbes: Bimodal IT: A New Buzzword For Old Concepts Presents Teachable Moment
By Kurt Marko
IT analysts are like fashion designers, always searching for something new, even if that means recycling age-old concepts in new terminology. But like successful fashionistas, IT Continue reading
Simple two man show this week with Ethan & Greg talking through, oh, I don't know ..... stuff like this
The post Show 242 – Where Have All The Good Staff Gone ? appeared first on Packet Pushers.
 Considerations for the implementation of NFV.
Considerations for the implementation of NFV.
Simple two man show this week with Ethan & Greg talking through, oh, I don't know ..... stuff like this
The post Show 242 – Where Have All The Good Staff Gone ? appeared first on Packet Pushers Podcast and was written by Greg Ferro.
 The closely watched startup is preaching a programmable data plane.
The closely watched startup is preaching a programmable data plane.
Elisa Jasinska, Bob McCouch and I were scheduled to record a NetOps podcast with a major vendor, but unfortunately their technical director cancelled at the last minute. Like good network engineers, we immediately found plan B and focused on Elisa’s specialty: open-source tools.
Read more ...
In my last post, I described the logical model I decided to use in order that I might be able to compute the path between endpoints using the Dijkstra shortest path algorithm. I’ve already discovered the handy Perl module module Paths::Graph that implements Dijkstra for me, so now all I need to do is to turn the network model into a data format that Paths::Graph will accept.
As a reminder, this is the model I’m using for my two-datacenter network:
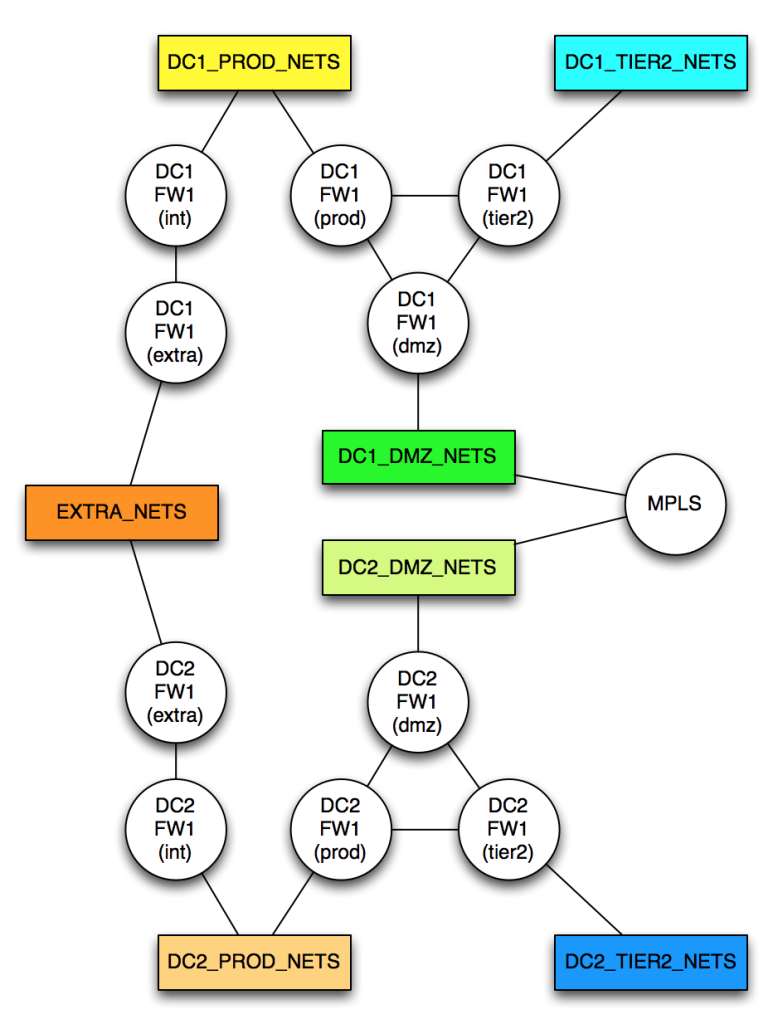
To model this network, I need to allocate a cost to every network link. It turns out that Paths::Graph wants me to create separate links in each direction; this is a huge pain, and makes an already risk-laden process doubly painful. After initially creating the data model directly in the code, I realized that it would be much simpler (hah!) to model the network using YAML, and to remove the requirement to include both directions of any link. In my new YAML mode, a link from A->B automatically implies a link from B->A with the same cost; this halves the number of link descriptions required, which I’ll take as a win. The format is dead simple:
Continue readingIt’s been a while since I’ve done a POI so here we go.
Kaspersky Lab found this new variant of the Duqu malware in their own network. They wrote a paper based on their analysis of this new malware. It fascinates me how sophisticated these software packages are and how much effort the threat actors put into them.
Diffie-Hellman (DH) is the world’s first public key crypto system. It’s used in everything from secure browsing, to secure shell. This video visually demonstrates how the Diffie-Hellman key exchange works. The best part is that you don’t need to know anything about crypto to follow along.
https://firstlook.org/theintercept/2015/03/26/passphrases-can-memorize-attackers-cant-guess/
Use this informative guide to generate secure, human-memorizable passphrases that are suitable for protecting your private PGP key, your private SSH key, and your master key for your password safe.
https://firstlook.org/theintercept/2015/04/27/encrypting-laptop-like-mean/
A well written article about encrypting one’s laptop. Covers topics such as what disk encryption does and does not protect against, attacks against disk encryption, and Continue reading
Much as I’ve been trying to keep up on interesting stuff to read on the right column, I still seem to have built a long list of bookmarks! Having nothing better to do on a Friday morning, I’m dumping them on your.
So there! 
I’ve posted in the past on the problems of the IT job market. Primarily I think it’s too much about “what narrow set of skills do you have,” rather than, “are you a good engineer,” and I think we engineers are as much to blame as anyone else for this. “Yeah, but do you know about the latest gobberfubble embedded fingernail pick API??” we say with pride, trying to find something we know about the person we’re interviewing does. Interviews shouldn’t be about making yourself feel better about your technical skill — they should be about finding a good engineer for your team. Okay, I’ve ranted long enough — it’s time for Infoworld to take over on this score with more practical advice.
The Midyear State of the IT Job Market.
By the way, I know my response to the esoteric game won’t work for everyone, but whenever someone gets me into this position of Continue reading
This blog was originally posted by the Electronic Frontier Foundation who is represents CloudFlare in this case.
JUNE 18, 2015 | BY MITCH STOLTZ
This month, CloudFlare and EFF pushed back against major music labels’ latest strategy to force Internet infrastructure companies like CloudFlare to become trademark and copyright enforcers, by challenging a broad court order that the labels obtained in secret. Unfortunately, the court denied CloudFlare’s challenge and ruled that the secretly-obtained order applied to CloudFlare. This decision, and the strategy that led to it, present a serious problem for Internet infrastructure companies of all sorts, and for Internet users, because they lay out a blueprint for quick, easy, potentially long-lasting censorship of expressive websites with little or no court review. The fight’s not over for CloudFlare, though. Yesterday, CloudFlare filed a motion with the federal court in Manhattan, asking Judge Alison J. Nathan to modify the order and put the responsibility of identifying infringing domain names back on the music labels.
We’ve reported recently about major entertainment companies’ quest to make websites disappear from the Internet at their say-so. The Internet blacklist bills SOPA and PIPA were part of that strategy, along with the Department of Homeland Security’s Continue reading
Open-source DevOps tools are used to deploy applications and services in datacenter server networks, but they may also enable researchers or students to simulate networks. In this post, we will survey popular open-source DevOps tools and provide links to information that shows how to use them to create network simulation scenarios.
Most open-source network simulators simplify the setup and configuration of virtual machines and the networking connections between virtual machines. DevOps tools such as OpenStack do the same things, although they expose more of the complexities of the virtualized infrastructure to the user.
If you are already using DevOps tools for other activities you may find it useful to also use them when you need to create a simulated network instead of learning to use a network simulator.
Both open-source network simulators and a coordinated set of DevOps tools perform the same role: they orchestrate the setup, interconnection, and configuration of virtual nodes in a virtual network.
Open-source simulators are built to support small-scale simulation scenarios on one computer, although some can run in a distributed mode across multiple computers. DevOps tools are designed to work in datacenters composed of hundred or thousands of servers, Continue reading