The Demise of G-Suite

In case you missed it this week, Google is killing off the free edition of Google Apps/G-Suite/Workspace. The short version is that you need to convert to a paid plan by May 1, 2022. If you don’t you’re going to lose everything in July. The initial offering of the free tier was back in 2006 and the free plan hasn’t been available since 2012. I suppose a decade is a long time to enjoy custom email but I’m still a bit miffed at the decision.
Value Added, Value Lost
It’s pretty easy to see that the free version of Workspace was designed to encourage people to use it and then upgrade to a paid account to gain more features. As time wore on Google realized that people were taking advantage of having a full suite of 50 accounts and never moving, which is why 2012 was the original cutoff date. Now there has been some other change that has forced their hand into dropping the plan entirely.
I won’t speculate about what’s happening because I’m sure it’s complex and tied to ad revenue and privacy restrictions that people are implementing that is reducing the value of the data Google has Continue reading
Troubleshooting 101 – What About the Ports?
Tony Fortunato of The Technology Firm walks you through a typical network performance troubleshooting workflow.Emotet Is Not Dead (Yet)
The state of cyber security is a typical example of a cat-and-mouse game between hackers and defenders. Sometimes, a threat that appears to be under control, if not completely mitigated, comes back with a vengeance. This is exactly what happened to Emotet.
It has been just about a year since the Emotet botnet was taken down, thanks to the international efforts of multiple law enforcement agencies. But the silence from Emotet attackers did not last long. Late last year, we saw a report on the resurface of Emotet distributed by Trickbot. Recently VMware’s Threat Analysis Unit saw another Emotet campaign—where the attacks leveraged the increasingly abused Excel 4.0 (XL4) macros to spread Emotet payloads.
In this blog post, we investigate the first stage of the recent Emotet attacks by analyzing one of the samples from the recent campaign and reveal novel tactics, techniques, and procedures (TTPs) that were not used by Emotet in the past.
The Recent Emotet Campaign
Figure 1 shows the detection timeline of a recent Emotet campaign that affected some of our customers—mostly in the EMEA region. The campaign started on January 11 and peaked the next day before fading Continue reading
Follow Up: Bootstrapping Servers into Ansible
Seven years ago, I wrote a quick post on bootstrapping servers into Ansible. The basic gist of the post was that you can use variables on the Ansible command-line to specify hosts that aren’t part of your inventory or log in via a different user (useful if the host doesn’t yet have a dedicated Ansible user account because you want to use Ansible to create that account). Recently, though, I encountered a situation where this approach doesn’t work, and in this post I’ll describe the workaround.
In one of the Slack communities I frequent, someone asked about using the approach described in the original blog post. However, they were having issues connecting. Specifically, this error was cropping up in the Ansible output (names have been changed to protect the innocent):
fatal: [new-server.int.domain.test]: UNREACHABLE! => {"changed": false, "msg": "Failed to connect to the host via ssh: [email protected]: Permission denied (publickey,password).", "unreachable": true}
Now, this is odd, because the Ansible command-line being executed included the parameters I mentioned in the original blog post:
ansible-playbook bootstrap.yml -i inventory/hosts -K --extra-vars "hosts=new-server.int.domain.test user=john"
For some reason, though, it was ignoring that parameter and Continue reading
Why global DDoS protection is essential for Anycast networks
PAID FEATURE In October 2021, in an incident lasting more than six hours, Facebook disappeared from the Internet. …
Why global DDoS protection is essential for Anycast networks was written by David Gordon at The Next Platform.
Heavy Networking 614: eBPF, Cloud-Native Networking, And Other Modern Networking Trends
Today's Heavy Networking gets deep in the guts of what’s going on with all the modern trends in networking: cloud-native, containers, eBPF, Kubernetes, DPUs, and so on. Guests Brent Salisbury and Dave Tucker give their insider’s view of developments in cutting-edge networking tech. You’ll walk away with a better idea of what to pay attention to in the months and years to come.Heavy Networking 614: eBPF, Cloud-Native Networking, And Other Modern Networking Trends
Today's Heavy Networking gets deep in the guts of what’s going on with all the modern trends in networking: cloud-native, containers, eBPF, Kubernetes, DPUs, and so on. Guests Brent Salisbury and Dave Tucker give their insider’s view of developments in cutting-edge networking tech. You’ll walk away with a better idea of what to pay attention to in the months and years to come.
The post Heavy Networking 614: eBPF, Cloud-Native Networking, And Other Modern Networking Trends appeared first on Packet Pushers.
Internet outage in Yemen amid airstrikes

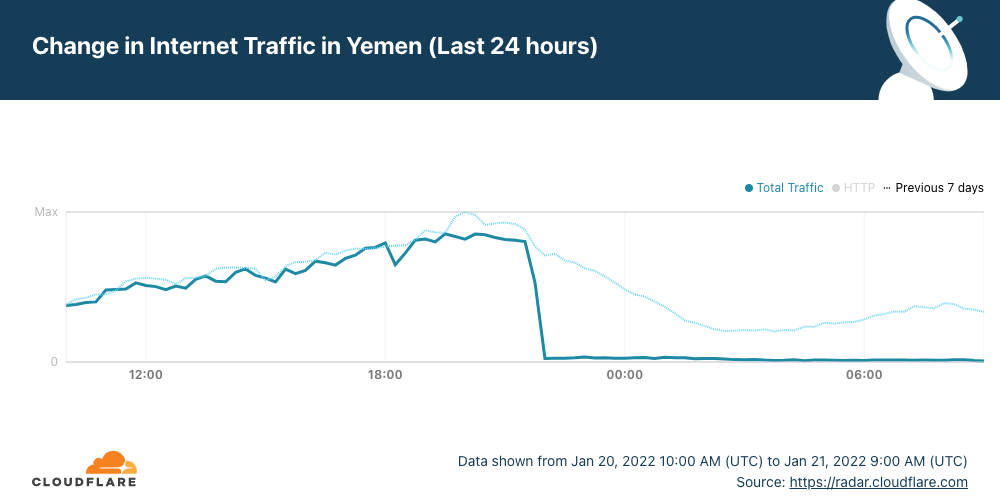
The early hours of Friday, January 21, 2022, started in Yemen with a country-wide Internet outage. According to local and global news reports airstrikes are happening in the country and the outage is likely related, as there are reports that a telecommunications building in Al-Hudaydah where the FALCON undersea cable lands was hit.
Cloudflare Radar shows that Internet traffic dropped close to zero between 21:30 UTC (January 20, 2022) and by 22:00 UTC (01:00 in local time).
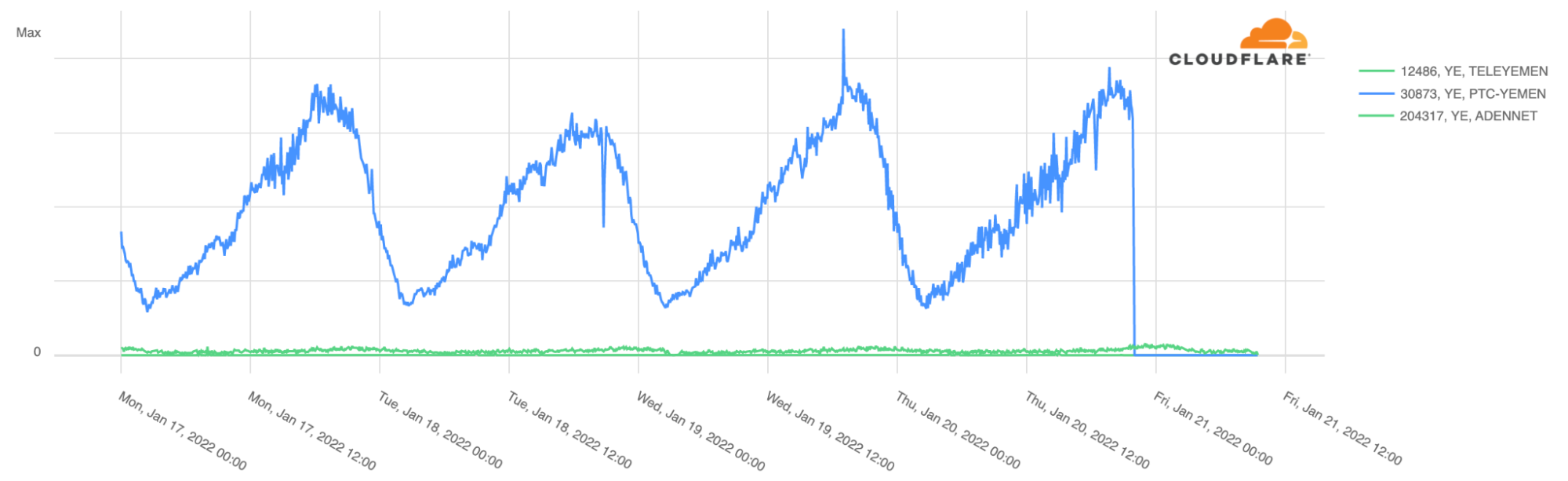
The outage affected the main state-owned ISP, Public Telecommunication Corporation (AS30873 in blue in the next chart), which represents almost all the Internet traffic in the country.
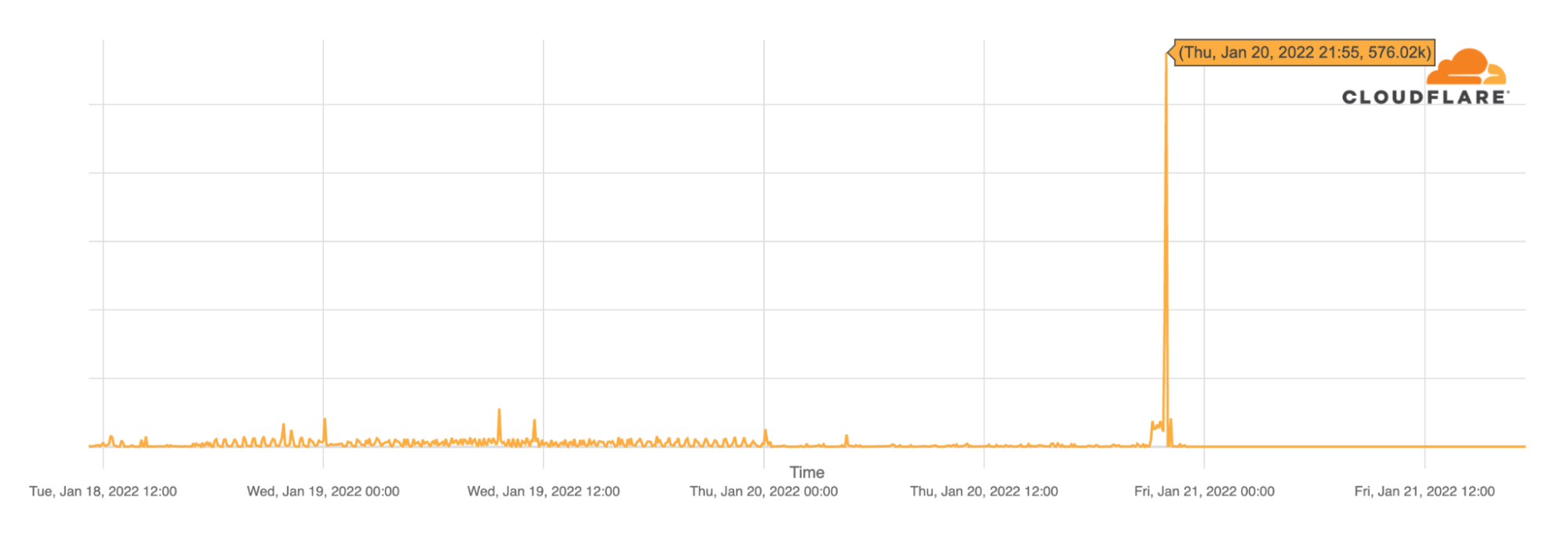
Looking at BGP (Border Gateway Protocol) updates from Yemen’s ASNs around the time of the outage, we see a clear spike at the same time the main ASN was affected ~21:55 UTC, January 20, 2022. These update messages are BGP signalling that Yemen’s main ASN was no longer routable, something similar to what we saw happening in The Gambia and Kazakhstan but for very different reasons.
So far, 2022 has started with a few significant Internet disruptions for different reasons:
1. An Internet outage in The Gambia because of a cable problem.
2. An Internet Continue reading
Technology Short Take 151
Welcome to Technology Short Take #151, the first Technology Short Take of 2022. I hope everyone had a great holiday season and that 2022 is off to a wonderful start! I have a few more links than normal this time around, although I didn’t find articles in a couple categories. Don’t worry—I’ll keep my eyes peeled and my RSS reader ready to pull in new articles in those categories for next time. And now for the content!
Networking
- Mike Fiedler explores differences in ways for container-to-container communication to occur.
- Aidan Steele examines how VPC sharing could potentially improve security and reduce cost.
- What do you think microsegmentation means?
- Nick Schmidt talks about using GitOps with the NSX Advanced Load Balancer.
Servers/Hardware
- The Next Platform takes a look at Amazon’s Graviton3 processor.
- Ru Singh provides a review of his M1-based MacBook Air.
- Here’s a great review of the Framework laptop.
- Losing to Apple—whose M-series chips are widely regarded as faster and more efficient than Intel’s chips—has apparently stung the chip giant into revving up the innovation engine. These details on their 12th-generation H processors shows that Intel appears to be intent to regain the lead. Time will tell how successful they Continue reading
Video: Machine Learning Techniques
After Javier Antich walked us through the AI/ML hype and described the basics of machine learning it was time for a more thorough look at:
- Machine learning techniques, including unsupervised learning (clustering and anomaly detection), supervised learning (regression, classification and generation) and reinforced learning
- Machine learning implementations, including neural networks, deep neural networks and convolutional neural networks.
Video: Machine Learning Techniques
After Javier Antich walked us through the AI/ML hype and described the basics of machine learning it was time for a more thorough look at:
- Machine learning techniques, including unsupervised learning (clustering and anomaly detection), supervised learning (regression, classification and generation) and reinforced learning
- Machine learning implementations, including neural networks, deep neural networks and convolutional neural networks.
Juniper Networks’ SD-WAN Can Now Be Operated Via Mist Cloud
Juniper Networks’ SD-WAN appliances and software can now be fully managed from Juniper’s Mist Cloud. It’s part of Juniper’s larger goal to Mist-ify its LAN and WAN portfolio. Juniper’s SD-WAN product is based on the Session Smart Routers (SSRs) from Juniper’s acquisition of 128 Technology. Customers can now use Mist Cloud to onboard SSR hardware, […]
The post Juniper Networks’ SD-WAN Can Now Be Operated Via Mist Cloud appeared first on Packet Pushers.
Hedge 115: Mat Duggan and DevOps

Devops is the new normal—but, far too often, operations folks (like network engineers) are expected to become full-on developers, and developers are expected to understand operations in ways they never had to before. Mat Duggan joins Tom Ammon and Russ White to discuss why operations is not development IT