Network Break 306: Cloudflare Launches Secure NaaS Offering; SonicWall Vulnerability Affects Nearly 800,000 Devices
Today's Network Break examines a new security service from Cloudflare, a SonicWall vulnerability that affects a massive number of its appliances, a fresh funding round for networking startup Alkira, and more nerdy networking news.Network Break 306: Cloudflare Launches Secure NaaS Offering; SonicWall Vulnerability Affects Nearly 800,000 Devices
Today's Network Break examines a new security service from Cloudflare, a SonicWall vulnerability that affects a massive number of its appliances, a fresh funding round for networking startup Alkira, and more nerdy networking news.
The post Network Break 306: Cloudflare Launches Secure NaaS Offering; SonicWall Vulnerability Affects Nearly 800,000 Devices appeared first on Packet Pushers.
How a Customer’s Trust in Cloudflare Led to a Big Win against Bots
Key Points
- Anyone with public-facing web properties is likely to have bot traffic on their website.
- One type of bot that commonly targets eCommerce and online portals is a ‘scraper bot’.
- Some scraper bots are good (such as those used by search engines to assess your website’s content to inform search results, or price comparison sites to help inform consumer decisions), however many are malicious, and will work to scrape not only images but also pricing data from your site for use by a competitor.
- Many Bot Management providers will need to divert your traffic to a dedicated data centre to analyse your traffic and ‘scrub’ it clean from malicious bot traffic before sending it on to your site. While effective this will almost certainly add latency to the traffic’s ‘journey’ resulting in degraded user experience. Look for a technology partner with an expansive network who can scan your traffic in real time as it passes through any data centre on their network.
- Good and bad scraper bots behave in largely the same way, making it difficult for bot protection systems to differentiate between the two. A common challenge with Bot Management solutions is that they can return a high Continue reading
New on ipSpace.net: Virtualizing Network Devices Q&A
A few weeks ago we published an interesting discussion on network operating system details based on an excellent set of questions by James Miles.
Unfortunately we got so far into the weeds at that time that we answered only half of James’ questions. In the second Q&A session Dinesh Dutt and myself addressed the rest of them including:
- How hard is it to virtualize network devices?
- What is the expected performance degradation?
- Does it make sense to use containers to do that?
- What are the operational implications of running virtual network devices?
- What will be the impact on hardware vendors and networking engineers?
And of course we couldn’t avoid the famous last question: “Should network engineers program network devices?”
You’ll need Standard or Expert ipSpace.net subscription to watch the videos.
New on ipSpace.net: Virtualizing Network Devices Q&A
A few weeks ago we published an interesting discussion on network operating system details based on an excellent set of questions by James Miles.
Unfortunately we got so far into the weeds at that time that we answered only half of James' questions. In the second Q&A session Dinesh Dutt and myself addressed the rest of them including:
- How hard is it to virtualize network devices?
- What is the expected performance degradation?
- Does it make sense to use containers to do that?
- What are the operational implications of running virtual network devices?
- What will be the impact on hardware vendors and networking engineers?
And of course we couldn’t avoid the famous last question: “Should network engineers program network devices?”
You’ll need Standard or Expert ipSpace.net subscription to watch the videos.
The case for a learned sorting algorithm
The case for a learned sorting algorithm, Kristo, Vaidya, et al., SIGMOD’20
We’ve watched machine learning thoroughly pervade the web giants, make serious headway in large consumer companies, and begin its push into the traditional enterprise. ML, then, is rapidly becoming an integral part of how we build applications of all shapes and sizes. But what about systems software? It’s earlier days there, but ‘The case for learned index structures’(Part 1 Part 2), SageDB and others are showing the way.
Today’s paper choice builds on the work done in SageDB, and focuses on a classic computer science problem: sorting. On a 1 billion item dataset, Learned Sort outperforms the next best competitor, RadixSort, by a factor of 1.49x. What really blew me away, is that this result includes the time taken to train the model used!
The big idea
Suppose you had a model that given a data item from a list, could predict its position in a sorted version of that list. 0.239806? That’s going to be at position 287! If the model had 100% accuracy, it would give us a completed sort just by running over the dataset and putting Continue reading
6G: New Generations of Wireless and the Impact on Measurement
Possible 6G use cases include tactile holographic communications, digital twins, Industrial IoT, and a pervasive use of AI to merge communications and computing with society.Worth Reading: Does your hammer own you?
My friend Marjan Bradeško wrote a great article describing how we tend to forget common sense and rely too much on technology. I would strongly recommend you read it and start thinking about the choices you make when building a network with magic software-intent-defined-intelligent technology from your preferred vendor.
Worth Reading: Does your hammer own you?
My friend Marjan Bradeško wrote a great article describing how we tend to forget common sense and rely too much on technology. I would strongly recommend you read it and start thinking about the choices you make when building a network with magic software-intent-defined-intelligent technology from your preferred vendor.
One more (Zero Trust) thing: Cloudflare Intrusion Detection System

Today, we’re very excited to announce our plans for Cloudflare Intrusion Detection System, a new product that monitors your network and alerts when an attack is suspected. With deep integration into Cloudflare One, Cloudflare Intrusion Detection System gives you a bird’s eye view of your entire global network and inspects all traffic for bad behavior, regardless of whether it came from outside or inside your network.
Analyze your network without doing the legwork
Enterprises build firewall rules to keep their networks safe from external and internal threats. When bad actors try to attack a network, those firewalls check if the attack matches a rule pattern. If it does, the firewall steps in and blocks the attack.
Teams used to configure those rules across physical firewall appliances, frequently of different makes and models, deployed to physical locations. Yesterday, we announced Magic Firewall, Cloudflare’s network-level firewall delivered in our data centers around the world. Your team can write a firewall rule once, deploy it to Cloudflare, and our global network will protect your offices and data centers without the need for on-premises hardware.
This is great if you know where attacks are coming from. If you don’t have that level Continue reading
Zero-Touch Provisioning with Nornir
In early 2018 I described how Hans Verkerk implemented zero-touch provisioning with Ansible. Recently he rewrote his scripts as a Python-only solution using Nornir. Enjoy!
Zero-Touch Provisioning with Nornir
In early 2018 I described how Hans Verkerk implemented zero-touch provisioning with Ansible. Recently he rewrote his scripts as a Python-only solution using Nornir. Enjoy!
No, that’s not how warrantee expiration works
The NYPost Hunter Biden story has triggered a lot of sleuths obsessing on technical details trying to prove it's a hoax. So far, these claims are wrong. The story is certainly bad journalism aiming to misinform readers, but it has not yet been shown to be a hoax.
In this post, we look at claim the timelines don't match up with the manufacturing dates of the drives. Sleuths claim to prove the drives were manufactured after the events in question, based on serial numbers.
What this post will show is that the theory is wrong. Manufacturers pad warrantee periods. Thus, you can't assume a date of manufacture based upon the end of a warrantee period.
The story starts with Hunter Biden (or associates) dropping off a laptop at a repair shop because of water damage. The repair shop made a copy of the laptop's hard drive, stored on an external drive. Later, the FBI swooped in and confiscated both the laptop and that external drive.
The serial numbers of both devices are listed in the subpoena published by the NYPost:
You can enter these serial numbers in the support pages at Apple (FVFXC2MMHV29) and Western Digital (WX21A19ATFF3) to discover precisely Continue reading
Next Platform TV: October 16, 2020
Front Row with Frontera; Spectrum Scale Strategy; Computational Storage Deep Dive; Neural Programming Frontiers; MLPerf for HPC + More…
On today’s episode for the week, we talk to Dan Stanzione, director of the Texas Advanced Computing Center, to get an update on the “Frontera” supercomputer. …
Next Platform TV: October 16, 2020 was written by Nicole Hemsoth at The Next Platform.
No, font errors mean nothing in that NYPost article
The NYPost has an article on Hunter Biden emails. Critics claim that these don't look like emails, and that there are errors with the fonts, thus showing they are forgeries. This is false. This is how Apple's "Mail" app prints emails to a PDF file. The font errors are due to viewing PDF files within a web browser -- you don't see them in a PDF app.
In this blogpost, I prove this.
I'm going to do this by creating forged email. The point isn't to prove the email wasn't forged, it could easily have been -- the NYPost didn't do due diligence to prove they weren't forged. The point is simply that that these inexplicable problems aren't evidence of forgery. All emails printed by the Mail app to a PDF, then displayed with Scribd, will look the same way.
To start with, we are going to create a simple text file on the computer called "erratarob-conspire.eml". That's what email messages are at the core -- text files. I use Apple's "TextEdit" app on my MacBook to create the file.
The structure of an email is simple. It has a block of "metadata" consisting of fields separated by a Continue readingUsing Social Media Content for Screening in Recruitment and Selection: Pros and Cons for Employers
Social media has become a popular tool these days. Many organizations use social media content for screening in recruitment and selection to scan and shortlist the job candidates. They do it by learning more about them through Facebook, Twitter, Instagram, and many more platforms. They search for the candidates on these platforms to learn about their lifestyles, interests, and hobbies. In this way, they can deduce whether these candidates can serve as an asset to the organization or not. Thus, it has become a common recruitment process these days.
Just like everything has its pros and cons, using social media content for screening in recruitment and selection: pros and cons are present too. There has been a long debate on the pros and cons of this screening method. Let’s take a look at them below.
Pros of Using Social Media For Screening
· Insight into the Informal Life of the Job Candidate
The candidate tries to be as formal as possible during the job interview. They are pretending to be something they are actually not, because they want to impress the interviewer to land that job. Therefore, employers are not able to deduce what the candidate is actually Continue reading
In Africa, Strengthening Digital Infrastructure for a Safe Return to Schools

When COVID-19 struck Africa, governments imposed temporary or full shutdowns of education systems to contain its spread. At least 53 out of the 54 African countries took measures that canceled or partially closed schools. Kenya, for example, canceled the 2020 academic year in March, before changing its directives six months later to allow schools to reopen.
No Internet, No Schools
Across the Democratic Republic of Congo, Liberia, Nigeria, and South Africa, where governments imposed partial closure, the few students with access to the Internet, mobile devices, and computers continue learning. But for the majority, there is no schooling. Most can’t afford the cost of Internet data, and very few have access to smartphones and computers. They must improvise to learn, thus widening disparities between learners with Internet access and those without. How can Africa close this gap and offer equal learning opportunities to everyone?
As we gear up towards resuming formal education, there is general panic among parents about the implications resulting from the major learning disruptions. Could COVID-19 lead to a lost generation of students?
Solutions for a Safe Return
Fortunately, African decision-makers are shifting their positions on schools as we learn to live with COVID-19. Governments across the Continue reading
How our network powers Cloudflare One
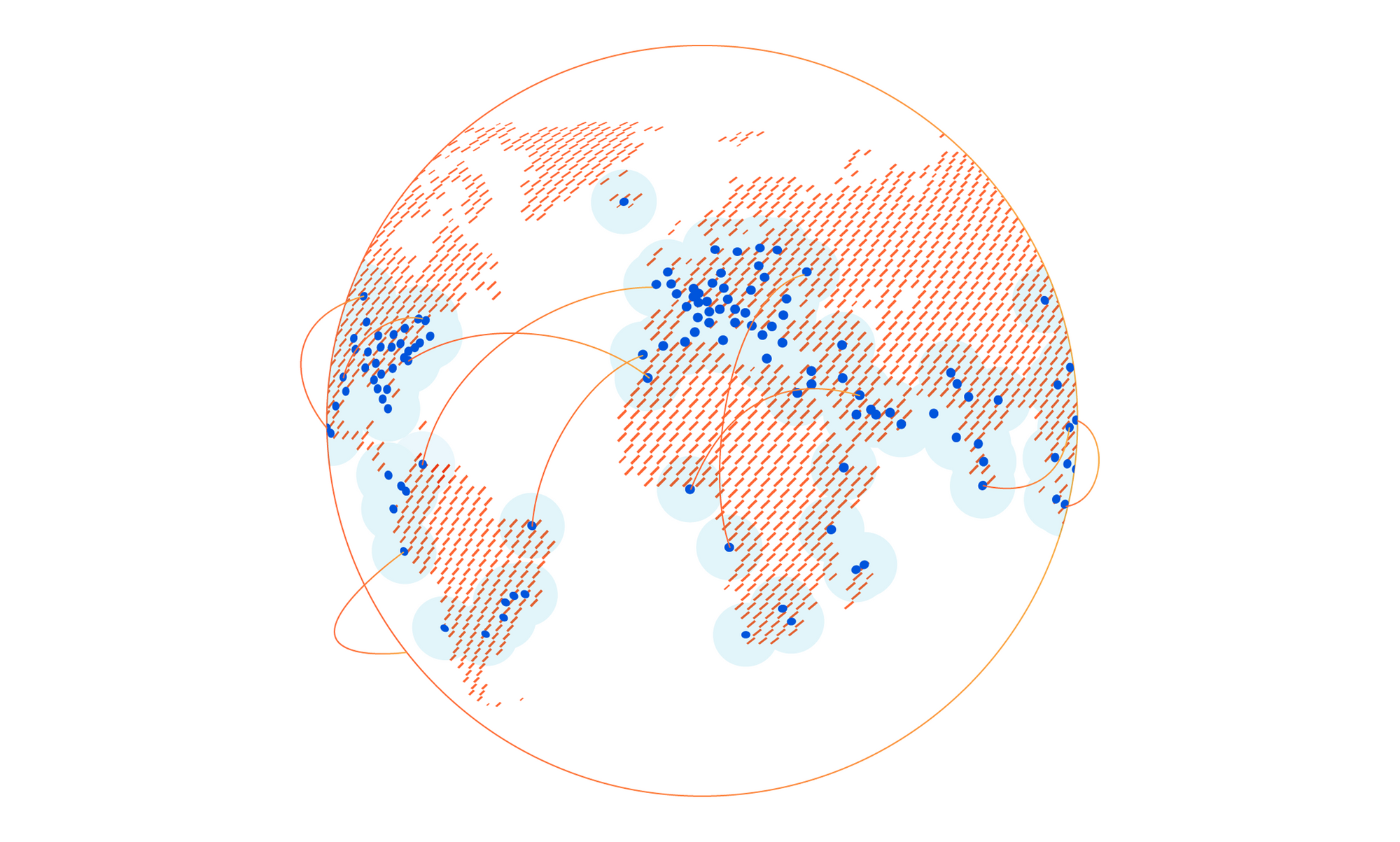
Earlier this week, we announced Cloudflare One™, a unified approach to solving problems in enterprise networking and security. With Cloudflare One, your organization’s data centers, offices, and devices can all be protected and managed in a single control plane. Cloudflare’s network is central to the value of all of our products, and today I want to dive deeper into how our network powers Cloudflare One.
Over the past ten years, Cloudflare has encountered the same challenges that face every organization trying to grow and protect a global network: we need to protect our infrastructure and devices from attackers and malicious outsiders, but traditional solutions aren’t built for distributed networks and teams. And we need visibility into the activity across our network and applications, but stitching together logging and analytics tools across multiple solutions is painful and creates information gaps.

We’ve architected our network to meet these challenges, and with Cloudflare One, we’re extending the advantages of these decisions to your company’s network to help you solve them too.
Distribution
Enterprises and some small organizations alike have team members around the world. Legacy models of networking forced traffic back through central choke points, slowing down users and constraining network scale. Continue reading

