VMware Inks Deal to Buys Avi Networks
 Avi’s platform includes a software load balancer, web application firewall, analytics and...
Avi’s platform includes a software load balancer, web application firewall, analytics and...
VMware Announces Intent to Acquire Avi Networks to Deliver Software-Defined ADC for the Multi-Cloud Era
By Tom Gillis, SVP/GM of Networking and Security BU
Today I’m excited to announce that VMware has signed a definitive agreement to acquire Avi Networks, a leader of software-defined application delivery services for the multicloud era.
Our vision at VMware is to deliver the “public cloud experience” to developers regardless of what underlying infrastructure they are running. What does this mean? Agility. The ability to quickly deploy new workloads, to try new ideas, and to iterate. Modern infrastructure needs to provide this agility wherever it executes – on premises, in hybrid cloud deployments, or in native public clouds, using VM’s, containers or a combination of the two. VMware is uniquely suited to deliver this, with a complete set of software-defined infrastructure that runs on every cloud, even yours.
Application Delivery Controllers (ADCs) are a critical pillar of a software-defined data center. Many workloads cannot be deployed without one. For many customers, this means writing their application to bespoke and proprietary APIs that are tied to expensive hardware appliances. The Avi Networks team saw this problem and solved it in the right way. They built a software architecture that is truly scale-out, with a centralized controller. This controller manages not Continue reading
Riverbed Siphons Versa for a Stronger SD-WAN Flow
 Despite the Versa deal, Riverbed plans to continue to offer its SteelConnect platform while...
Despite the Versa deal, Riverbed plans to continue to offer its SteelConnect platform while...
Barracuda Adds Analytics to Secure SD-WAN
 Industrial IoT security is a “big growth area” for Barracuda because it plays on its strengths...
Industrial IoT security is a “big growth area” for Barracuda because it plays on its strengths...
German Operators Bemoan High Cost of 5G Spectrum
 German operators are despondent after a spectrum auction reached a price that could limit their...
German operators are despondent after a spectrum auction reached a price that could limit their...
Aviatrix CEO Mullaney Challenges Cisco, VMware: ‘Carnage Is Coming’
 The former CEO at Nicira and SVP of networking and security at VMware came out of retirement to...
The former CEO at Nicira and SVP of networking and security at VMware came out of retirement to...
Protecting Project Galileo websites from HTTP attacks
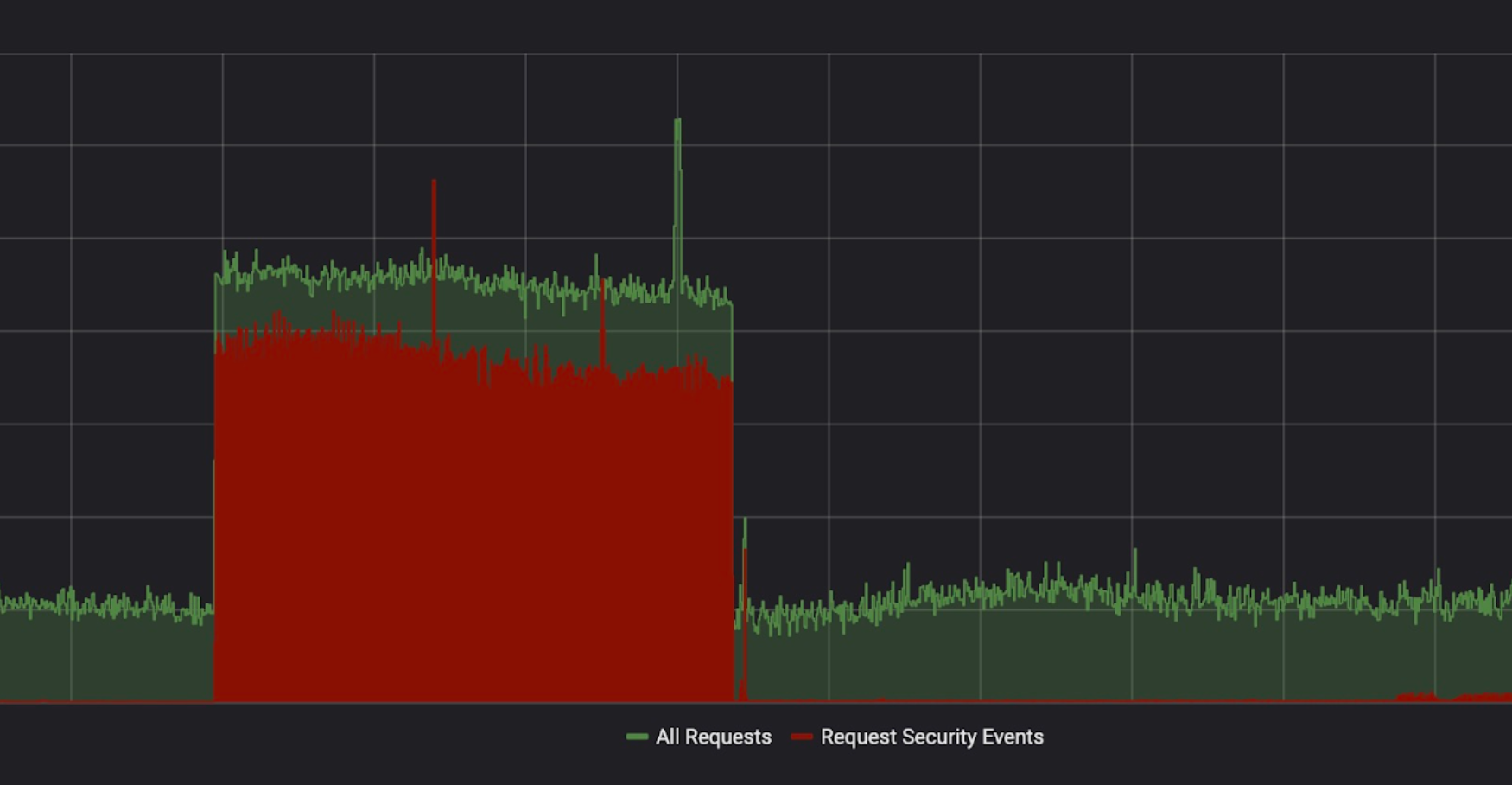
Yesterday, we celebrated the fifth anniversary of Project Galileo. More than 550 websites are part of this program, and they have something in common: each and every one of them has been subject to attacks in the last month. In this blog post, we will look at the security events we observed between the 23 April 2019 and 23 May 2019.
Project Galileo sites are protected by the Cloudflare Firewall and Advanced DDoS Protection which contain a number of features that can be used to detect and mitigate different types of attack and suspicious traffic. The following table shows how each of these features contributed to the protection of sites on Project Galileo.
|
Firewall Feature |
Requests Mitigated |
Distinct originating IPs |
Sites Affected (approx.) |
|
78.7M |
396.5K |
~ 30 |
|
|
41.7M |
1.8M |
~ 520 |
|
|
24.0M |
386.9K |
~ 200 |
|
|
9.4M |
32.2K |
~ 500 |
|
|
4.5M |
163.8K |
~ 200 |
|
|
2.3M |
1.3K |
~ 15 |
|
|
2.0M |
686.7K |
~ 40 |
|
|
1.6M |
360 |
1 |
|
|
623.5K |
6.6K |
~ 15 |
|
|
9.7K |
2.8K |
Teaching a cheap ethernet switch new tricks
Teaching a cheap ethernet switch new tricks
Ethernet rules everything around us, a large proportion of our systems communicate to each other with ethernet somewhere in the line. And the fast pac
IPv6 Buzz 028: Are Container Networks Ready For IPv6?
Shannon McFarland discusses IPv6 and container networking on today's IPv6 Buzz podcast episode. We look at the state of v6 support in containers and orchestration platforms, how v6 addressing works with containers, the role of service meshes, and much more.IPv6 Buzz 028: Are Container Networks Ready For IPv6?
Shannon McFarland discusses IPv6 and container networking on today's IPv6 Buzz podcast episode. We look at the state of v6 support in containers and orchestration platforms, how v6 addressing works with containers, the role of service meshes, and much more.
The post IPv6 Buzz 028: Are Container Networks Ready For IPv6? appeared first on Packet Pushers.
A10 Networks ACOS Root Privilege Escalation
The following summarizes a root privilege escalation vulnerability that I identified in A10 ACOS ADC software. This was disclosed to A10 Networks in June 2016 and mitigations have been put in place to limit exposure to the vulnerability.

SUMMARY OF VULNERABILITY
Any user assigned sufficient privilege to upload an external health monitor (i.e a script) and reference it from a health monitor can gain root shell access to ACOS.
At this point, I respectfully acknowledge Raymond Chen’s wise words about being on the other side of an airtight hatch; if the malicious user is already a system administrator or has broad permissions, then one could argue that they could already do huge damage to the ADC in other ways. However, root access could allow that user to install persistent backdoors or monitoring threats in the underlying OS where other users can neither see nor access them. It could also allow a partition-level administrator to escalate effectively to a global admin, by way of being able to see the files in every partition on the ADC.
SOFTWARE VERSIONS TESTED:
This vulnerability was originally discovered and validated initially in ACOS 2.7.2-P4-SP2 and is present in 4.x as Continue reading
Running OSPF in a Single Non-Backbone Area
One of my subscribers sent me an interesting puzzle:
>One of my colleagues configured a single-area OSPF process in a customer VRF customer, but instead of using area 0, he used area 123 nssa. Obviously it works, but I was thinking: “What the heck, a single OSPF area MUST be in Area 0”
Not really. OSPF behaves identically within an area (modulo stub/NSSA behavior) regardless of the area number…
Read more ...Network-as-a-Service Part 1 – Frameworkless automation
Recently I’ve been pondering the idea of cloud-like method of consumption of traditional (physical) networks. My main premise for this was that users of a network don’t have to wait hours or days for their services to be provisioned when all that’s required is a simple change of an access port. Let me reinforce it by an example. In a typical data center network, the configuration of the core (fabric) is fairly static, while the config at the edge can change constantly as servers get added, moved or reconfigured. Things get even worse when using infrastructure-as-code with CI/CD pipelines to generate and test the configuration since it’s hard to expose only a subset of it all to the end users and it certainly wouldn’t make sense to trigger a pipeline every time a vlan is changed on an edge port.
This is where Network-as-a-Service (NaaS) platform fits in. The idea is that it would expose the required subset of configuration to the end user and will take care of applying it to the devices in a fast and safe way. In this series of blogposts I will describe and demonstrate a prototype of such a platform, implemented on top of Continue reading
Podcast: Multi-Vendor Network Virtualization with EVPN
 In this episode, you’ll hear from Andre Kindness, Principal Analyst, Forrester Research; Jeff...
In this episode, you’ll hear from Andre Kindness, Principal Analyst, Forrester Research; Jeff...