Python Decorators – From a Network Engineers Perspective
As going through learning some basic programming, I encountered Decorators. I should be very honest if any of you are trying to figure out or learn what decorators in python do from my blog post you are dangerously in trouble.
So what this post about if not learning, well its mostly on what the functionality is so that you can learn the concept from better programming resources.
Let’s examine the below code
The output will be something like below
What’s in this code:
The first thing you have to realize is that some representation with ‘@’ symbol. If you have noticed get_reinfo and get_modelinfo functions, they have one thing in common which is to connect to the device and get output before they parse the required fields, that what a Decorator is helping us to do here, we extend that wrapping functionality around new functions without having to write everything or globalize everything.
At least that is what I understood. So, next time when you are writing some code try to think if you can incorporate decorators into them.
-Rakesh
Akamai Gets Edgy With Platform Expansion and Upgrades
 The company cited a study that found 85 percent of companies have a hybrid cloud strategy and that...
The company cited a study that found 85 percent of companies have a hybrid cloud strategy and that...
Mortgage Company TruHome Taps Bigleaf SD-WAN to Deliver Cloud Telephony
 As TruHome matured and gained autonomy from its parent company it needed to build out its...
As TruHome matured and gained autonomy from its parent company it needed to build out its...
Context-aware Micro-segmentation with NSX-T 2.4
With last’s week landmark release of NSX-T 2.4, and the RSA conference in full swing, this is the perfect time to talk about to some of the new security functionality we are introducing in NSX-T 2.4.
If you prefer seeing NSX-T in action, you can watch this demo which covers Layer 7 application identity, FQDN Filtering and Ientity Firewall. Or if you are around at RSAC in San Francisco this week, swing by the VMware booth.
Micro-segmentation has been one of the key reasons why our customers deploy NSX. With Micro-segmentation, NSX enables organizations to implement a zero-trust network security model in their on-premise datacenter as well as in the cloud and beyond. A key component making Micro-segmentation possible is the Distributed Firewall, which is deployed at the logical port of every workload allowing the most granular level of enforcement, regardless of the form factor of that workload – Virtual Machine – Container – Bare Metal Server or where that workload resides – On Premise – AWS -Azure – VMC.
NSX-T 2.4 provides significant new security features and functionality such as Context-aware Micro-segmentation, Network (and Security) Intrastructure as Code, E-W Service Insertion and Guest Continue reading
Cumulus content roundup: February
It’s time to officially unveil our Cumulus content roundup- February edition! In case you missed any of the content from the last month we, naturally, have you covered with links to it all below. Dig into the latest and greatest resources and news including two great podcasts that we recommend you queue up and listen to during your commute.
From Cumulus Networks:
How to make CI/CD with containers viable in production: Software-defined infrastructure is no longer a nice to have. It’s an absolute must using modern development approaches, such as CI/CD, containers, etc.
Kernel of Truth season 2 episode 1- EVPN on the host: Guess who’s back? Back again? The real Kernel of Truth is back with season 2 and we’re starting off this season with all things EVPN! This topic is near and dear to Attilla de Groots’ heart having talked about it in his recent blog here. He now joins Atul Patel and our host Brian O’Sullivan to talk more about EVPN on host for multi-tenancy.
BGP: What is it, how can it break, and can Linux BGP fix it?: Border Gateway Protocol is one of the most important protocols on the internet. Linux BGP allows for in-depth monitoring and Continue reading
CenturyLink Threat Research Reemerges as Black Lotus Labs
 The threat researchers say there’s no deeper, symbolic meaning behind the cool new name. But it...
The threat researchers say there’s no deeper, symbolic meaning behind the cool new name. But it...
Headcount: The Latest Hirings, Firings, and Retirings — March 7, 2019
 Verizon makes changes to its board of directors following the retirement of two prominent board...
Verizon makes changes to its board of directors following the retirement of two prominent board...
AT&T Launches New Cybersecurity Division, Joins Global Telco Security Alliance
 The new security division will integrate and automate Alien Lab’s threat intelligence into a...
The new security division will integrate and automate Alien Lab’s threat intelligence into a...
Syniverse, Tata Global IPX Interconnect Deal Preps for 5G, IoT
 The partnership includes “operational interlocks” for single accountability for troubleshooting...
The partnership includes “operational interlocks” for single accountability for troubleshooting...
Vodafone UK 5G Plans Barge Past Rivals
 The U.K. operator goes three better than rival EE with plans to launch 5G in 19 markets this year.
The U.K. operator goes three better than rival EE with plans to launch 5G in 19 markets this year.
Diving into Technical SEO using Cloudflare Workers
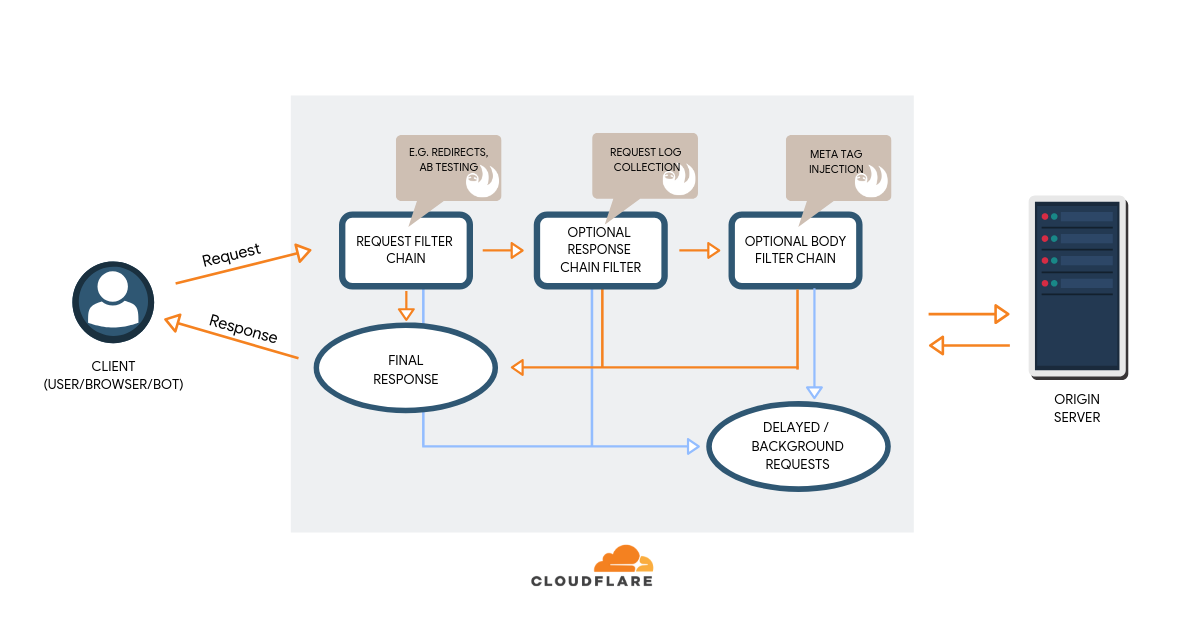
This is a guest post by Igor Krestov and Dan Taylor. Igor is a lead software developer at SALT.agency, and Dan a lead technical SEO consultant, and has also been credited with coining the term “edge SEO”. SALT.agency is a technical SEO agency with offices in London, Leeds, and Boston, offering bespoke consultancy to brands around the world. You can reach them both via Twitter.
With this post we illustrate the potential applications of Cloudflare Workers in relation to search engine optimization, which is more commonly referred to as ‘SEO’ using our research and testing over the past year making Sloth.
This post is aimed at readers who are both proficient in writing performant JavaScript, as well as complete newcomers, and less technical stakeholders, who haven’t really written many lines of code before.
Endless practical applications to overcome obstacles
Working with various clients and projects over the years we’ve continuously encountered the same problems and obstacles in getting their websites to a point of “technical SEO excellence”. A lot of these problems come from platform restriction at an enterprise level, legacy tech stacks, incorrect builds, and years of patching together various services and infrastructures.
As a team of Continue reading
Silo 2: On-Premise with DevOps

I had a great time stirring up the hornet’s nest with the last post about DevOps, so I figured that I’d write another one with some updated ideas and clarifications. And maybe kick the nest a little harder this time.
Grounding the Rules
First, we need to start out with a couple of clarifications. I stated that the mantra of DevOps was “Move Fast, Break Things.” As has been rightly pointed out, this was a quote from Mark Zuckerberg about Facebook. However, as has been pointed out by quite a few people, “The use of basic principles to enable business requirements to get to production deployments with appropriate coordination among all business players, including line of business, developers, classic operations, security, networking, storage and other functional groups involved in service delivery” is a bit more of definition than motto.
What exactly is DevOps then? Well, as I have been educated, it’s a principle. It’s an idea. A premise, if you will. An ideal to strive for. So, to say that someone is on a DevOps team is wrong. There is no such thing as a classic DevOps team. DevOps is instead something that many other teams do in Continue reading
IPv6 Buzz 021: NAT Isn’t Necessary For Security: Answering Listener Questions
Today's episode of IPv6 Buzz answers listener questions including why NAT isn't necessary for security, and the feasibility of scanning a v6 network to discover devices. Thanks for the questions and keep them coming!IPv6 Buzz 021: NAT Isn’t Necessary For Security: Answering Listener Questions
Today's episode of IPv6 Buzz answers listener questions including why NAT isn't necessary for security, and the feasibility of scanning a v6 network to discover devices. Thanks for the questions and keep them coming!
The post IPv6 Buzz 021: NAT Isn’t Necessary For Security: Answering Listener Questions appeared first on Packet Pushers.
Interview with Juniper Networks Ambassador Rob Jeffery
Had a chance to sit down with fellow Ambassador Rob Jeffery at the Juniper NXTWORK 2018 conference in Las Vegas. Rob is the Technical Director and CTO at Next Gen Security based out of the UK, with a heavy focus on bringing emerging network and security products into the marketplace. We discussed his involvement in …Continue reading "Interview with Juniper Networks Ambassador Rob Jeffery"
Building Network Automation Source-of-Truth (Part 2)
In the first blog post of this series I described how you could start building the prerequisite for any network automation solution: the device inventory.
Having done that, you should know what is in your network, but you still don’t know how your network is supposed to work and what services it is supposed to provide. Welcome to the morass known as building your source-of-truth.
Read more ...
