Hedge 234: We’re Looking in the Wrong Places to Solve the Cyber Workforce Shortage

We often hear about how there simply aren’t enough tech people out there–especially in cybersecurity. Rex Booth, CISO at Sailpoint, joins Tom and Russ to discuss the problem, and why we should be looking in unconventional places to find the right people.
Worth Reading: Why Do We Have Native VLANs?
Daniel Dib went on another deep dive: Why Do We Have Native VLANs? What I loved most was that he went through the whole 802.1 standard (quite an undertaking) and explained the reasoning that VLAN-aware switches behave the way they do.
You should also read the follow-up post: what happens if a VLAN-unaware switch receives an 802.1Q-tagged frame?
Terraform for Network Engineers: Part Three

If you have not read the previous parts of this series, I recommend you start there.
Welcome back to our journey of exploring Terraform for Network Engineers. In the previous part, we left ourself with a few challenges network engineers face when diving into the world of Terraform. Let's quickly recap those challenges:
- Setup Complexity: Are we really expecting network engineers to set up a Terraform project and write HCL code for creating resources on Panorama?
- Documentation Dive: Are network engineers supposed to dig into Terraform provider documentation to configure their desired resources?
- State File Management: What do we do with the state file? How do we manage it and share it with the team? What if it gets corrupted?
In this part, we'll tackle the first two challenges. We will explore how we can simplify the configuration file and abstract the complexity of the Terraform provider documentation.
Before we dive in, lets decompose the components of a simple Palo Alto Networks security policy configuration. A simple policy is composed of the following components:
- Device Group
- Source and Destination Zones
- Source and Destination Addresses
- Services Continue reading
IPB155: Operational Considerations: DHCP vs DHCPv6
What are the operational considerations and differences between DHCP and DHCPv6? In today’s episode we explore the implications for network management, security, and operational models. We also discuss the challenges of DHCPv6 failover, high availability, complex device tracking and identity management in various environments. Episode Links: Scott’s Infoblox IPv6 CoE blog post Introducing DHCPv6 Prefix... Read more »Application Security report: 2024 update
Over the last twelve months, the Internet security landscape has changed dramatically. Geopolitical uncertainty, coupled with an active 2024 voting season in many countries across the world, has led to a substantial increase in malicious traffic activity across the Internet. In this report, we take a look at Cloudflare’s perspective on Internet application security.
This report is the fourth edition of our Application Security Report and is an official update to our Q2 2023 report. New in this report is a section focused on client-side security within the context of web applications.
Throughout the report we discuss various insights. From a global standpoint, mitigated traffic across the whole network now averages 7%, and WAF and Bot mitigations are the source of over half of that. While DDoS attacks remain the number one attack vector used against web applications, targeted CVE attacks are also worth keeping an eye on, as we have seen exploits as fast as 22 minutes after a proof of concept was released.
Focusing on bots, about a third of all traffic we observe is automated, and of that, the vast majority (93%) is not generated by bots in Cloudflare’s verified list and is potentially malicious.
API traffic Continue reading
Euro 2024’s impact on Internet traffic: a closer look at finalists Spain and England

National team sports unite countries, and football (known as “soccer” in the US) is the world’s most popular sport, boasting approximately 3.5 billion fans globally. The UEFA Euro 2024, running from June 14 to July 14, 2024, significantly impacts Internet traffic across participating European nations. This blog post focuses on the two finalists, Spain and England, and comes after an initial post we published during the first week of the tournament.
Analyzing traffic patterns reveals distinct high-level trends. Spain saw the most significant drops in Internet traffic during games against major teams and former champions such as Italy (the defending champion), Germany, and France. In contrast, England’s games had crucial moments towards the end, leading to the largest traffic reductions in the UK, especially during the knockout stages.
For context, as previously mentioned, football games like the Super Bowl, differ from other events such as elections. When major teams or national squads play, especially in matches that captivate many viewers, Internet traffic often drops. This is particularly true if the game is broadcast on a national TV channel. During such broadcasts, people tend to focus more on their TV sets, relying on the traditional broadcast signal Continue reading
Detecting Mismatched Native VLANs
Many people have seen the message logged to their switch about a mismatched native VLAN on a trunk, but how is it detected? There are two methods of detecting mismatched native VLAN on a trunk link:
- CDP.
- STP when using a Per-VLAN flavor such as PVST+ or RPVST+.
To demonstrate how this happens, I will setup a very simple topology in CML with two switches connected by a trunk link as seen below:
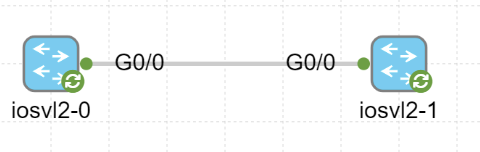
At this point only the following has been configured on the trunk link:
interface GigabitEthernet0/0 switchport trunk encapsulation dot1q switchport mode trunk negotiation auto
Now, let’s take a look at the PDUs being generated, CDP and STP. For CDP we can see the following in Wireshark:
Frame 31: 354 bytes on wire (2832 bits), 354 bytes captured (2832 bits)
IEEE 802.3 Ethernet
Logical-Link Control
Cisco Discovery Protocol
Version: 2
TTL: 180 seconds
Checksum: 0x474d [correct]
[Checksum Status: Good]
Device ID: SW2
Software Version
Platform: Cisco
Addresses
Port ID: GigabitEthernet0/0
Capabilities
VTP Management Domain:
Native VLAN: 1
Type: Native VLAN (0x000a)
Length: 6
Native VLAN: 1
Duplex: Full
Trust Bitmap: 0x00
Untrusted port CoS: 0x00
Management Addresses
Notice that the native VLAN is signaled and that it Continue reading
Again: What Exactly Is MPLS?
Brad Casemore published an interesting analysis explaining why Cisco should accept being a mature company with mature products (yeah, you have to subscribe to view it). I always loved reading his articles, but unfortunately, this time, he briefly ventured into the “I don’t think this word means what you think it means” territory:
MPLS worked – and it still works – but it provided optimal value in an earlier time when the center of gravity was not the cloud. The cloud challenged the efficacy of MPLS, and it wasn’t long before SD-WAN, cloud connects, and interconnects […] represented an implacable threat to a status quo that had once seemed unassailable.
The second part of the paragraph is (almost) true, but it had nothing to do with MPLS.
NAN068: Is Cloud Networking the Future for Network Engineers?
On today’s episode, host Eric Chou and guest Kyler Middleton discuss the transition from on-prem network engineering to cloud networking; the importance of adapting to new platforms such as AWS, Azure, and Terraform; and the future of cloud versus on-premises solutions. We also discuss Kyler’s background, navigating the journey from a farm upbringing to a... Read more »Cloudflare Zaraz adds support for server-side rendering of X and Instagram embeds

We are thrilled to announce Cloudflare Zaraz support of server-side rendering of embeds, featuring two Managed Components: X and Instagram. You can now use Cloudflare Zaraz to effortlessly embed posts from X or Instagram on your website in a performant, privacy-preserving, and secure way. Many traditional tag managers or customer data platforms rely heavily on third-party JavaScript and cookies to embed content, leading to concerns about privacy and performance. In contrast, we designed our solution to work without loading any third-party JavaScript or cookies, and furthermore to completely eliminate communication between the browser and third-party servers.
Starting today, you can use Cloudflare Zaraz not only for server-side data reporting to conventional marketing and analytics tools but also for server-side content rendering on your website. We are excited to pave the way with tools that enhance security, protect user privacy, and improve performance. Take a look at it:
Embed social media content without sacrificing security and speed
Since social media platforms emerged, we have become more and more familiar with seeing posts being embedded on websites, from showcasing user testimonials on product pages to featuring posts from reporters and politicians in news articles or blogs. Traditionally, this process has involved integrating Continue reading
Worth Reading: Terminal Line Editing
In another wonderful deep dive, Julia Evans explains why you can’t edit the command line in some Linux utilities like the ancient sh.
You’ll also figure out:
- Why does CTRL-A jump to the beginning of the line?
- How can you enable command line editing in ancient utilities?
Have fun!
PP022: Inside an Equipment Test Lab
Third-party test labs can help buyers make decisions about which products to purchase. While a testing lab can’t mimic the conditions of your specific production environment, it can assess a product’s fundamental capabilities and measure throughput, performance, and–in the case of security devices–effectiveness against a test suite of malware or attack techniques. On today’s episode... Read more »HW031: Wi-Fi Surveys – Past, Present & Future
The evolution of wireless surveys is the topic of today’s Heavy Wireless podcast with guest Jussi Kivineimi of Hamina. We cover the transition from traditional on-site assessments to predictive tools, with an emphasis on the importance of a hybrid approach for accurate network design. We also tackle the role of APIs in network design, the... Read more »DDoS threat report for 2024 Q2

Welcome to the 18th edition of the Cloudflare DDoS Threat Report. Released quarterly, these reports provide an in-depth analysis of the DDoS threat landscape as observed across the Cloudflare network. This edition focuses on the second quarter of 2024.
With a 280 terabit per second network located across over 230 cities worldwide, serving 19% of all websites, Cloudflare holds a unique vantage point that enables us to provide valuable insights and trends to the broader Internet community.
Key insights for 2024 Q2
- Cloudflare recorded a 20% year-over-year increase in DDoS attacks.
- 1 out of every 25 survey respondents said that DDoS attacks against them were carried out by state-level or state-sponsored threat actors.
- Threat actor capabilities reached an all-time high as our automated defenses generated 10 times more fingerprints to counter and mitigate the ultrasophisticated DDoS attacks.
View the interactive version of this report on Cloudflare Radar.
Quick recap - what is a DDoS attack?
Before diving in deeper, let's recap what a DDoS attack is. Short for Distributed Denial of Service, a DDoS attack is a type of cyber attack designed to take down or disrupt Internet services, such as websites or mobile apps, making them unavailable Continue reading
RADIUS/UDP vulnerable to improved MD5 collision attack
The MD5 cryptographic hash function was first broken in 2004, when researchers demonstrated the first MD5 collision, namely two different messages X1 and X2 where MD5(X1) = MD5 (X2). Over the years, attacks on MD5 have only continued to improve, getting faster and more effective against real protocols. But despite continuous advancements in cryptography, MD5 has lurked in network protocols for years, and is still playing a critical role in some protocols even today.
One such protocol is RADIUS (Remote Authentication Dial-In User Service). RADIUS was first designed in 1991 – during the era of dial-up Internet – but it remains an important authentication protocol used for remote access to routers, switches, and other networking gear by users and administrators. In addition to being used in networking environments, RADIUS is sometimes also used in industrial control systems. RADIUS traffic is still commonly transported over UDP in the clear, protected only by outdated cryptographic constructions based on MD5.
In this post, we present an improved attack against MD5 and use it to exploit all authentication modes of RADIUS/UDP apart from those that use EAP (Extensible Authentication Protocol). The attack allows a Monster-in-the-Middle (MitM) with access to RADIUS traffic Continue reading
802.1Q-Tagged Frames Through Unmanaged Switch – Forwarded or Dropped?
As a follow-up to the post yesterday on native VLANs, there was a question on what would happen to 802.1Q-tagged frames traversing an unmanaged switch. Unmanaged in this case being a switch that does not support VLANs. While this might be more of a theoretical question today, it’s still interesting to dive into it to better understand how a 802.1Q-tagged frame is different from an untagged frame.
Before we can answer the question on what a VLAN-unaware switch should do, let’s refresh our memory on the Ethernet header. The Ethernet frame consists of Destination MAC, Source MAC, Ethertype, and FCS. 802.1Q adds an additional four bytes consisting of Tag Protocol Identifier (TPID) and Tag Control Information (TCI). This is shown below:

Note how the TPID in the tagged frame is in the place of EtherType for untagged frames. It’s also a 2-byte field and the TPID is set to 0x8100 for tagged frames. The EtherType field is still there and would be for example 0x0800 for IPv4 payload.
To demonstrate what this looks like on the wire, I’ve setup two routers with the following configuration:
hostname R1 ! vrf definition ETHERNET ! address-family ipv4 exit-address-family ! interface GigabitEthernet1.100 encapsulation Continue reading
Embracing Modern Virtualization with Calico’s Microsegmentation
In the rapidly evolving landscape of IT infrastructure, enterprises are increasingly moving away from traditional virtualization platforms due to rising licensing costs and the limitations these older systems impose on modern cloud-native application needs. The shift towards Kubernetes, which can manage diverse workloads such as containers, virtual machines (VMs), and bare metal environments, accelerates the migration from traditional virtualization platforms.
The Limitations of Traditional Network Segmentation
Traditionally, enterprises have segmented their virtualized environments using VLANs and logical switches to create distinct virtual networks and security zones. This segmentation was primarily static VM environments. However, this traditional approach to network segmentation is ill-equipped to handle the dynamic nature of Kubernetes environments, where workloads are frequently created and destroyed, leading to rapidly changing network configurations and policies.
Calico’s Solution: Dynamic and Unified Microsegmentation
Calico is designed to address the shortcomings of traditional network segmentation in the age of Kubernetes and container-based architectures. Calico provides a robust, dynamic, and high-performance network policy engine that supports a diverse range of workloads and scales across environments.
Key Features of Calico’s Microsegmentation:
- Unified Security Model: Calico offers a consistent security model across various environments, whether you are managing VMs, containers, or bare metal. This unified approach Continue reading
Embracing Modern Virtualization with Calico’s Microsegmentation
In the rapidly evolving landscape of IT infrastructure, enterprises are increasingly moving away from traditional virtualization platforms due to rising licensing costs and the limitations these older systems impose on modern cloud-native application needs. The shift towards Kubernetes, which can manage diverse workloads such as containers, virtual machines (VMs), and bare metal environments, accelerates the migration from traditional virtualization platforms.
The Limitations of Traditional Network Segmentation
Traditionally, enterprises have segmented their virtualized environments using VLANs and logical switches to create distinct virtual networks and security zones. This segmentation was primarily static VM environments. However, this traditional approach to network segmentation is ill-equipped to handle the dynamic nature of Kubernetes environments, where workloads are frequently created and destroyed, leading to rapidly changing network configurations and policies.
Calico’s Solution: Dynamic and Unified Microsegmentation
Calico’s microsegmentation capabilities are designed to address the shortcomings of traditional network segmentation in the age of Kubernetes and container-based architectures. Calico provides a robust, dynamic, and high-performance network policy engine that supports a diverse range of workloads and scales across environments.
Key Features of Calico’s Microsegmentation:
- Unified Security Model: Calico offers a consistent security model across various environments, whether you are managing VMs, containers, or bare metal. This Continue reading