Rule 11 Academy 060324
New material at Rule 11 Academy this week:
Understanding Intra-AS BGP
Suboptimal BGP Route Reflection Lab
I’ve done a good bit of BGP to this point; I’m probably going to work on link state or some other part of the outline next week. I’m trying to make certain everyone who signs up for the first time gets the first six months for free; the membership plugin is being a bit squirrely, so you might see accounts expired, etc. I’m fixing these as I see them.
Adopting OpenTelemetry for our logging pipeline

Cloudflare’s logging pipeline is one of the largest data pipelines that Cloudflare has, serving millions of log events per second globally, from every server we run. Recently, we undertook a project to migrate the underlying systems of our logging pipeline from syslog-ng to OpenTelemetry Collector and in this post we want to share how we managed to swap out such a significant piece of our infrastructure, why we did it, what went well, what went wrong, and how we plan to improve the pipeline even more going forward.
Background
A full breakdown of our existing infrastructure can be found in our previous post An overview of Cloudflare's logging pipeline, but to quickly summarize here:
- We run a syslog-ng daemon on every server, reading from the local systemd-journald journal, and a set of named pipes.
- We forward those logs to a set of centralized “log-x receivers”, in one of our core data centers.
- We have a dead letter queue destination in another core data center, which receives messages that could not be sent to the primary receiver, and which get mirrored across to the primary receivers when possible.

The goal of this project was to replace those syslog-ng instances as Continue reading
Public Videos: Network Automation 101

You can access the Network Automation 101 videos without registration. Hope you’ll find them useful if you’re just starting your network automation journey.
Configuring AAA on Arista EOS Devices Using TACACS+ and ISE

In this blog post, let's look at how to configure TACACS+ AAA authentication on Arista EOS devices using Cisco ISE. When someone tries to log in to the device, we want the Arista device to authenticate and authorize the user against Cisco ISE. We'll go through the necessary configurations and steps to set up this integration between Arista EOS and Cisco ISE.
Local Authorization vs ISE Authorization
You could configure this in two ways with a slight difference. With the first method, ISE authenticates the user and tells Arista which role to apply. Arista devices come with two predefined roles, network-admin and network-operator. For example, if we have two different groups of users, network engineers who need full access and NOC engineers who only need read-only access. When the users log in, depending on the policy, ISE will send TACACS+ attributes that tell the switch which role to apply. With this method, the authorization happens locally at the switch.
For the second method, we will not use these two predefined roles. Each command the user enters on the CLI will be authorized by Cisco ISE. For example, we can allow all commands for network engineers and prevent NOC engineers from Continue reading
NetBox in the Cloud, for Free
Yes, you read that right. NetBox Labs is now offering a generous free plan for their SaaS version of NetBox. This change is a big win for many of us who no longer need to worry about managing our own NetBox instances. With this free plan, you can take advantage of all the powerful features of NetBox without the hassle of maintenance and updates.
Why This Matters to Me?
As a blogger, I create a lot of labs and practice a lot of automation. I rely on NetBox for IP Address Management (IPAM) and other network-related tasks. Before this, I had my NetBox running as a Docker container on one of my VMs. However, there were times when I wanted to access NetBox and found out the VM was powered off. This free plan is music to my ears. There is a 100-device limit, but that's more than enough for my needs.
How to Get it?
Getting started with the free plan is as simple as going to their website and signing up for a free plan. I was up and running within a few minutes. The free plan includes up to 100 devices, 500 IP addresses, and 10k API Continue reading
Fat Pipe Transition Notification – June 2024
Hey, everyone. Ethan here with a behind-the-scenes administrative request. Several thousand of you subscribe to the Packet Pushers’ Fat Pipe. In the Fat Pipe, we’ve been stuffing every single podcast we produce. The problem is that we produce way too many shows–one almost every weekday–for the average podcast client to absorb them all. We can... Read more »Pi-hole on Raspberry Pi 3B with Debian
This guide helps you to install Pi-hole on your Raspberry Pi 3B running Debian 12, […]
The post Pi-hole on Raspberry Pi 3B with Debian first appeared on Brezular's Blog.
Network observability in Kubernetes clusters for better security and faster troubleshooting
For DevOps and platform teams working with containers and Kubernetes, reducing downtime and improving security posture is crucial. A clear understanding of network topology, service interactions, and workload dependencies is required in cloud-native applications. This is essential for securing and optimizing the Kubernetes deployment and minimizing response time in the event of failure.
Network observability can highlight gaps in network policies for applications that require network policy controls to reduce the risk of attack from unsecured egress access or lateral movement of threats within the Kubernetes cluster. However, visualizing workload communication, service dependencies, and active and inactive network security policies presents significant challenges due to the distributed and dynamic nature of Kubernetes workloads.
Why is network observability difficult with Kubernetes workloads?
Kubernetes scales up and scales out pods and creates and destroys services depending on real-time business requirements, resulting in dynamic network connections for each workload instance. Network access policies defined for each workload further impact these connections.
In such a scenario, capturing an accurate and up-to-date representation of network traffic, service dependencies, and network policies is difficult. The default Kubernetes implementation provides limited network traffic visibility and policy information, making it challenging for teams to troubleshoot connectivity issues, improve Continue reading
HN736: Understanding VMware by Broadcom (Sponsored)
Today on Heavy Networking, sponsored by Broadcom, we talk about VMware’s transition under Broadcom’s ownership. The acquisition has led to big changes that rolled out very quickly, including how VMware sells products and services – subscription only licensing, bundles of products, a hard stop on sales of existing licenses, overhaul of license issuance, and more.... Read more »Hedge 228: Five Execs Misunderstandings about Tech
Miscommunication between techies and business leaders are often caused by misunderstanding. Listen in as Eyvonne, Tom, and Russ discuss these misunderstandings and how we can address them.
Extending local traffic management load balancing to Layer 4 with Spectrum

In 2023, Cloudflare introduced a new load balancing solution, supporting Local Traffic Management (LTM). This gives organizations a way to balance HTTP(S) traffic between private or internal servers within a region-specific data center. Today, we are thrilled to be able to extend those same LTM capabilities to non-HTTP(S) traffic. This new feature is enabled by the integration of Cloudflare Spectrum, Cloudflare Tunnels, and Cloudflare load balancers and is available to enterprise customers. Our customers can now use Cloudflare load balancers for all TCP and UDP traffic destined for private IP addresses, eliminating the need for expensive on-premise load balancers.

A quick primer
In this blog post, we will be referring to load balancers at either layer 4 or layer 7. This is, of course, referring to layers of the OSI model but more specifically, the ingress path that is being used to reach the load balancer. Layer 7, also known as the Application Layer, is where the HTTP(S) protocol exists. Cloudflare is well known for our layer 7 capabilities, which are built around speeding up and protecting websites which run over HTTP(S). When we refer to layer 7 load balancers, we are referring to HTTP(S)-based services. Our layer Continue reading
Worth Reading: ChatGPT Does Not Summarize
I mostly gave up on LLMs being any help (apart from generating copious amounts of bullshit), but I still thought that generating summaries might be an interesting use case. I was wrong.
As Gerben Wierda explains in his recent “When ChatGPT summarises, it actually does nothing of the kind” blog post, you have to understand a text if you want to generate a useful summary, and that’s not what LLMs do. They can generate a shorter version of the text, which might not focus on the significant bits.
Worth Reading: ChatGPT Does Not Summarize
I mostly gave up on LLMs being any help (apart from generating copious amounts of bullshit), but I still thought that generating summaries might be an interesting use case. I was wrong.
As Gerben Wierda explains in his recent “When ChatGPT summarises, it actually does nothing of the kind” blog post, you have to understand a text if you want to generate a useful summary, and that’s not what LLMs do. They can generate a shorter version of the text, which might not focus on the significant bits.
NAN064: Get to Know NAF Co-Founder: Scott Robohn
Scott Robohn is responsible for so much of the current buzz and awareness of network automation. Today, we sit down with the co-founder of Network Automation Forum to learn about his own journey. We chat about his education and the question of if college degrees are necessary. We also talk about his experience at big... Read more »Disrupting FlyingYeti’s campaign targeting Ukraine

Cloudforce One is publishing the results of our investigation and real-time effort to detect, deny, degrade, disrupt, and delay threat activity by the Russia-aligned threat actor FlyingYeti during their latest phishing campaign targeting Ukraine. At the onset of Russia’s invasion of Ukraine on February 24, 2022, Ukraine introduced a moratorium on evictions and termination of utility services for unpaid debt. The moratorium ended in January 2024, resulting in significant debt liability and increased financial stress for Ukrainian citizens. The FlyingYeti campaign capitalized on anxiety over the potential loss of access to housing and utilities by enticing targets to open malicious files via debt-themed lures. If opened, the files would result in infection with the PowerShell malware known as COOKBOX, allowing FlyingYeti to support follow-on objectives, such as installation of additional payloads and control over the victim’s system.
Since April 26, 2024, Cloudforce One has taken measures to prevent FlyingYeti from launching their phishing campaign – a campaign involving the use of Cloudflare Workers and GitHub, as well as exploitation of the WinRAR vulnerability CVE-2023-38831. Our countermeasures included internal actions, such as detections and code takedowns, as well as external collaboration with third parties to remove the actor’s cloud-hosted malware. Continue reading
Cloudflare acquires BastionZero to extend Zero Trust access to IT infrastructure
We’re excited to announce that BastionZero, a Zero Trust infrastructure access platform, has joined Cloudflare. This acquisition extends our Zero Trust Network Access (ZTNA) flows with native access management for infrastructure like servers, Kubernetes clusters, and databases.
Security teams often prioritize application and Internet access because these are the primary vectors through which users interact with corporate resources and external threats infiltrate networks. Applications are typically the most visible and accessible part of an organization's digital footprint, making them frequent targets for cyberattacks. Securing application access through methods like Single Sign-On (SSO) and Multi-Factor Authentication (MFA) can yield immediate and tangible improvements in user security.
However, infrastructure access is equally critical and many teams still rely on castle-and-moat style network controls and local resource permissions to protect infrastructure like servers, databases, Kubernetes clusters, and more. This is difficult and fraught with risk because the security controls are fragmented across hundreds or thousands of targets. Bad actors are increasingly focusing on targeting infrastructure resources as a way to take down huge swaths of applications at once or steal sensitive data. We are excited to extend Cloudflare One’s Zero Trust Network Access to natively protect infrastructure with user- and device-based policies Continue reading
IPB152: IPv6 and Windows Active Directory
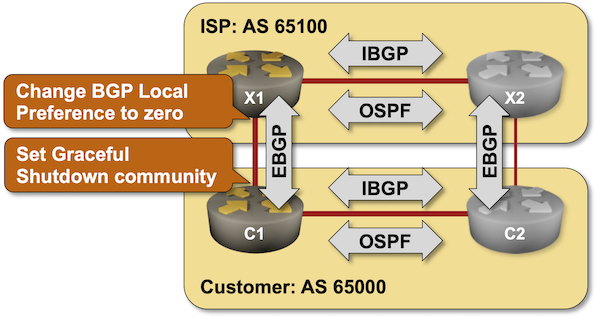
If you’re an Active Directory administrator or part of an enterprise network team working with one, this episode is for you. Ed literally wrote the book “Practical IPv6 for Windows Administrators” so Scott has fun interviewing him as today’s guest. Ed goes over how to diagram out your IPv6 deployment, including address allocation and making... Read more »BGP Labs: Graceful Shutdown
Using the typical default router configurations, it can take minutes between a failure of an inter-AS link and the convergence of BGP routes. You can fine-tune that behavior with BGP timers and BFD (and still get pwned by Graceful Restart). While you can’t influence link failures, you could drain the traffic from a link before starting maintenance operations on it, and it would be a shame not to do that considering there’s a standard way to do that – the GRACEFUL_SHUTDOWN BGP community defined in RFC 8326. That’s what you’ll practice in the next BGP lab exercise.
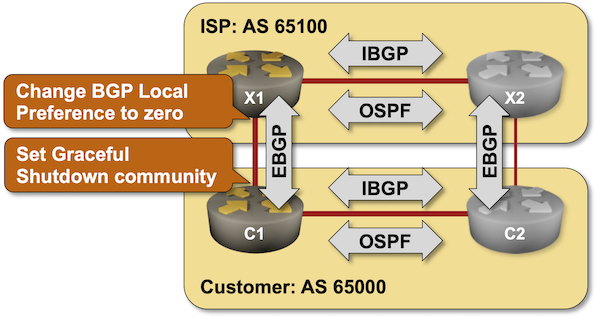
BGP Labs: Graceful Shutdown
Using the typical default router configurations, it can take minutes between a failure of an inter-AS link and the convergence of BGP routes. You can fine-tune that behavior with BGP timers and BFD (and still get pwned by Graceful Restart). While you can’t influence link failures, you could drain the traffic from a link before starting maintenance operations on it, and it would be a shame not to do that considering there’s a standard way to do that – the GRACEFUL_SHUTDOWN BGP community defined in RFC 8326. That’s what you’ll practice in the next BGP lab exercise.