Cross compiling Rust to Ubiquiti access point
This is not the right way to do it, as will become abundantly clear. But it works.
Set up build environment
rustup toolchain install nightly
rustup component add rust-src --toolchain nightly
apt install {binutils,gcc}-mips-linux-gnu
Create test project
cargo new foo
cd foo
Build most of it
This will build for a while, then fail.
cargo +nightly build --release -Zbuild-std --target mips-unknown-linux-gnu
For some reason it’s trying to use cc to link. I tried putting this
in Cargo.toml, but it does nothing:
[target.mips-unknown-linux-gnu]
linker = "mips-linux-gnu-gcc"
But I found a workaround.
Temporarily change /usr/bin/cc to point to the mips gcc
It does not work if you do this before the previous step.
PREV="$(readlink -v /usr/bin/cc)"
sudo rm /usr/bin/cc
sudo ln -s /usr/bin/mips-linux-gnu-gcc /usr/bin/cc
Link the program
Same command again
cargo +nightly build --release -Zbuild-std --target mips-unknown-linux-gnu
It should succeed. Yay.
Restore /usr/bin/cc
sudo rm /usr/bin/cc
sudo ln -s "${PREV?}" /usr/bin/cc
Change the “interpreter” to what the Ubiquiti system expects
cd target/mips-unknown-linux-gnu/release
patchelf --remove-needed ld.so.1 foo
patchelf --set-interpreter /lib/ld-musl-mips-sf.so.1 foo
Building it again
Probably easiest to rm -fr target, and go back to the step “Build
most of it”.
Does it work?
$ ./foo
Hello, world!
Yay!
Links
- https://doc.rust-lang.org/rustc/targets/custom.html
How CISOs Can Contend With Increasing Scrutiny from Regulators
Senior stakeholders who want to hold on to their CISOs must ensure that they have sufficient incentives and, more importantly, support to cope with the burden of risk that they are carrying.D2C240: The Duality of Enterprise AI
AI has been around forever; AI is emergent. AI is just data analytics; AI hallucinates. AI doesn’t have many business use cases; AI is already being used by your employees. Today, Greg and Johna from the Heavy Strategy podcast join Day Two Cloud to give their takes on enterprise AI. Johna brings with her the... Read more »NAN060: Python for Network Engineering with Kirk Byers (Part 2)
This is Part 2 of Kirk Byers’ interview. We discuss the Git course he’s developing and the need to build bridges between networking and testing so we can move automation forward. This of course leads us to geek out about AutoCon and the talks we’re most excited about. Plus, Kirk shares his wisdom about creating... Read more »Navigating the NaaS Era with a Customer-First Approach
With many enterprises new to NaaS, service providers can differentiate themselves from competitors by prioritizing superior customer service and experiences.How Cloudflare Cloud Email Security protects against the evolving threat of QR phishing
In the ever-evolving landscape of cyber threats, a subtle yet potent form of phishing has emerged — quishing, short for QR phishing. It has been 30 years since the invention of QR codes, yet quishing still poses a significant risk, especially after the era of COVID, when QR codes became the norm to check statuses, register for events, and even order food.
Since 2020, Cloudflare’s cloud email security solution (previously known as Area 1) has been at the forefront of fighting against quishing attacks, taking a proactive stance in dissecting them to better protect our customers. Let’s delve into the mechanisms behind QR phishing, explore why QR codes are a preferred tool for attackers, and review how Cloudflare contributes to the fight against this evolving threat.
How quishing works
The impact of phishing and quishing are quite similar, as both can result in users having their credentials compromised, devices compromised, or even financial loss. They also leverage malicious attachments or websites to provide bad actors the ability to access something they normally wouldn’t be able to. Where they differ is that quishing is typically highly targeted and uses a QR code to further obfuscate itself from detection.
Since Continue reading
FRRouting Loopback Interfaces and OSPF Costs
TL&DR: FRRouting advertises the IP prefix on the lo loopback interface with zero cost.
Let’s start with the background story. When we added FRRouting containers support to netlab, someone decided to use lo0 as the loopback interface name. That device doesn’t exist in a typical Linux container, but it’s not hard to add it:
$ ip link add lo0 type dummy
$ ip link set dev lo0 up
FRRouting Loopback Interfaces and OSPF Costs
TL&DR: FRRouting advertises the IP prefix on the lo loopback interface with zero cost.
Let’s start with the background story. When we added FRRouting containers support to netlab, someone decided to use lo0 as the loopback interface name. That device doesn’t exist in a typical Linux container, but it’s not hard to add it:
$ ip link add lo0 type dummy
$ ip link set dev lo0 up
DNSSEC and .nz
It's a welcome sight to see a careful and thoughtful analysis of a service outage. One such instance was a presentation by .nz's Josh Simpson at the recent NZNOG meeting, reporting on a service outage for .nz domains.PP010: CISA’s Cyber Incident Reporting Law: What You Need to Know
The US government is seeking comment on a new law mandating detailed cyber incident reporting. In this episode, we cover what you need to know about the “Cyber Incident Reporting for Critical Infrastructure Act.” We break down the details, including what kind of companies the law applies to, what it defines as an “incident,” and... Read more »HW025: Easy as Pi: The WLAN Pro’s Swiss Army Knife
In 2016, a handful of wireless engineers got together and decided to create the portable tool they all wish existed. Thus the WLAN Pi was born. Jerry Olla, Nick Turner, and Jiri Brejcha join the show today to talk about the evolution of the open source WLAN Pi and its current capabilities. The latest generation... Read more »DDoS threat report for 2024 Q1

Welcome to the 17th edition of Cloudflare’s DDoS threat report. This edition covers the DDoS threat landscape along with key findings as observed from the Cloudflare network during the first quarter of 2024.
What is a DDoS attack?
But first, a quick recap. A DDoS attack, short for Distributed Denial of Service attack, is a type of cyber attack that aims to take down or disrupt Internet services such as websites or mobile apps and make them unavailable for users. DDoS attacks are usually done by flooding the victim's server with more traffic than it can handle.
To learn more about DDoS attacks and other types of attacks, visit our Learning Center.
Accessing previous reports
Quick reminder that you can access previous editions of DDoS threat reports on the Cloudflare blog. They are also available on our interactive hub, Cloudflare Radar. On Radar, you can find global Internet traffic, attacks, and technology trends and insights, with drill-down and filtering capabilities, so you can zoom in on specific countries, industries, and networks. There’s also a free API allowing academics, data sleuths, and other web enthusiasts to investigate Internet trends across the globe.
To learn how we prepare this report, refer Continue reading
Unintended Consequences of IPv6 SLAAC
One of my friends is running a large IPv6 network and has already experienced a shortage of IPv6 neighbor cache on some of his switches. Digging deeper into the root causes, he discovered:
In my larger environments, I see significant neighbor table cache entries, especially on network segments with hosts that make many long-term connections. These hosts have 10 to 20 addresses that maintain state over days or weeks to accomplish their processes.
What’s going on? A perfect storm of numerous unrelated annoyances:
Unintended Consequences of IPv6 SLAAC
One of my friends is running a large IPv6 network and has already experienced a shortage of IPv6 neighbor cache on some of his switches. Digging deeper into the root causes, he discovered:
In my larger environments, I see significant neighbor table cache entries, especially on network segments with hosts that make many long-term connections. These hosts have 10 to 20 addresses that maintain state over days or weeks to accomplish their processes.
What’s going on? A perfect storm of numerous unrelated annoyances:
Why I joined Cloudflare as Chief Partner Officer

In today's rapidly evolving digital landscape, the decision to join a company is not just about making a career move. Instead, it's about finding a mission, a community, and a platform to make a meaningful impact. Cloudflare’s remarkable technology and incredibly driven teams are two reasons why I’m excited to join the team.
Joining Cloudflare as the Chief Partner Officer is my commitment to driving innovation and impact across the Internet through our channel partnerships. In each conversation throughout the interview process, I found myself getting more and more excited about the opportunity. Several former trusted colleagues who have recently joined Cloudflare repeatedly told me how amazing the people and company culture are. A positive culture driven by people that are passionate about their work is key. We work too hard not to have fun while doing it.
When it comes to partnerships, I see the immense value that partners can provide. My philosophy revolves around fostering collaborative, value-driven partnerships. It is about building ecosystems where we jointly navigate challenges, innovate together, and collectively thrive in a rapidly evolving global marketplace where the success of our channel partners directly influences our collective achievements. It also involves investing in their growth Continue reading
NB474: Intel Strikes Back In GPU Wars; The Fork Is Strong With Valkey
Take a Network Break! This week we start with some FU on Intel drivers, and how FISA affects people outside (and inside) the US. In the news we cover Intel’s rollout of new XPU silicon and associated software as it tries to make up ground against Nvidia’s AI dominance, Zscaler’s acquisition of a microsegmentation startup... Read more »Tech Bytes: Building an Effective Security Platform with Fortinet (Sponsored)
There’s a lot of well-earned criticism of security platforms: They’re a tangle of acquired products, packaged so you pay for more than you need, sucking you into a single vendor. Today John Maddison from Fortinet explains why their security platform is different. Fortinet has one unified fabric with a single operating system, agent, and management... Read more »Where Are You on the Cybersecurity Readiness Index? Cisco Thinks You’re Probably Overconfident
The most alarming takeaway from Cisco’s new Cybersecurity Readiness Index report is that even after decades of having the importance of cybersecurity driven home, cyber threats are still taken too lightly.New Course: Coding Skills for Network Engineers
This Friday, Marlon Bailey and I will be teaching a new four-hour class on coding skills for network engineers over on Safari Books Online through Pearson. From the course description:
Network engineers are increasingly expected to know how to perform basic coding, like building scripts to gather information and build or maintain an automation system. In larger organizations with full-time coders, network engineers are expected to effectively work with coders, on their own turf, to build and maintain network automation systems. All of these tasks require a basic knowledge of the structure and terminology of programming. There are a lot of courses that show you how to build your first program, or how to perform basic tasks using common programming languages—this course is different. This course will help you build a “mental map” of the software development space, gathering ideas and patterns learned across years into a simple-to-understand format. In this course you will learn data structures, program flow control, and—most importantly—how to structure software for efficiency and maintainability over the long haul.
For anyone who doesn’t know Marlon, you can find his LinkedIn profile here.
An Internet traffic analysis during Iran’s April 13, 2024, attack on Israel
(UPDATED on April 15, 2024, with information regarding the Palestinian territories.)
As news came on Saturday, April 13, 2024, that Iran was launching a coordinated retaliatory attack on Israel, we took a closer look at the potential impact on Internet traffic and attacks. So far, we have seen some traffic shifts in both Israel and Iran, but we haven’t seen a coordinated large cyberattack on Israeli domains protected by Cloudflare.
First, let’s discuss general Internet traffic patterns. Following reports of attacks with drones, cruise missiles, and ballistic missiles, confirmed by Israeli and US authorities, Internet traffic in Israel surged after 02:00 local time on Saturday, April 13 (23:00 UTC on April 12), peaking at 75% higher than in the previous week around 02:30 (23:30 UTC) as people sought news updates. This traffic spike was predominantly driven by mobile device usage, accounting for 62% of all traffic from Israel at that time. Traffic remained higher than usual during Sunday.
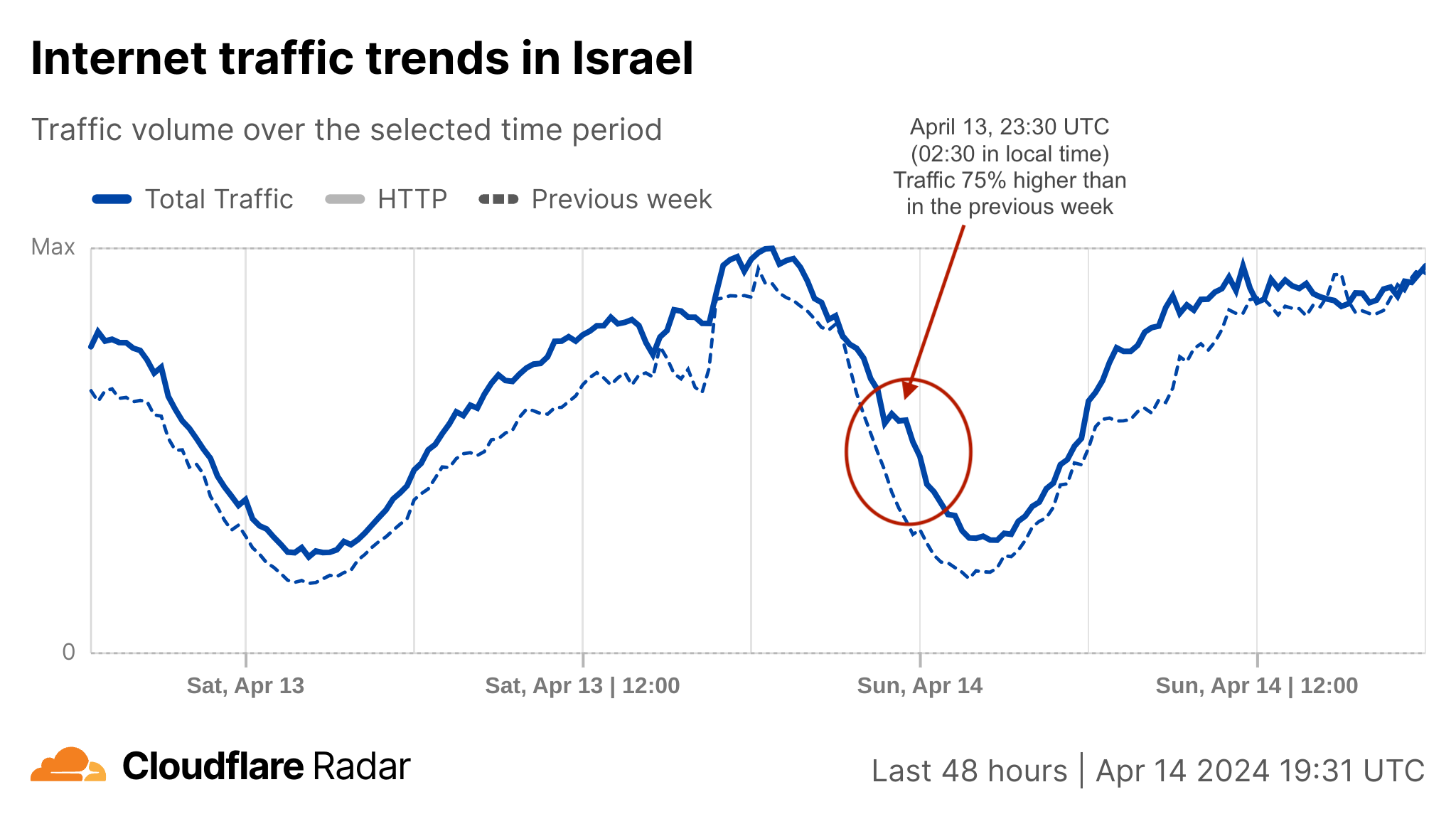
Around that time, at 02:00 local time (23:00 UTC), the IDF (Israel Defense Forces) posted on X that sirens were sounding across Israel because of an imminent attack from Iran.
🚨Sirens sounding across Israel🚨 pic.twitter.com/BuDasagr10
— Israel Defense Forces Continue reading