Firepower FMC API – Initial Observations
As many of you know, I am not a developer but I do occasionally hack stuff together. This article is just some of the initial things I have learned working with the Firepower Management Console API.
A good place to start is the Firepower REST API Quick Start Guide. This can be found at the following URL.
Firepower REST API Quick Start Guide
One thing to note is that there is a recommendation to use a dedicated username for the API. I would go a step beyond that with a recommendation for testing and development. During development, I currently have a username for the FMC UI, a username for the API Explorer and a username for whatever tool I’m working with (Postman or a Python Scripts). The reason for the extra accounts is that logging in to any of the UI’s tends to generate a new token (and invalidate the old one). This causes a constant reauthentication to the Web Interfaces.
Here is a screenshot of Postman doing an initial authentication — Post to retrieve an access token.
Generate Token URL
https://<server-ip>/api/fmc_platform/v1/auth/generatetoken

Sending a post with basic authentication to the URL will produce an “x-auth-access-token”. This is good for 30 minutes Continue reading
Firepower FMC API – Initial Observations
As many of you know, I am not a developer but I do occasionally hack stuff together. This article is just some of the initial things I have learned working with the Firepower Management Console API.
A good place to start is the Firepower REST API Quick Start Guide. This can be found at the following URL.
Firepower REST API Quick Start Guide
One thing to note is that there is a recommendation to use a dedicated username for the API. I would go a step beyond that with a recommendation for testing and development. During development, I currently have a username for the FMC UI, a username for the API Explorer and a username for whatever tool I’m working with (Postman or a Python Scripts). The reason for the extra accounts is that logging in to any of the UI’s tends to generate a new token (and invalidate the old one). This causes a constant reauthentication to the Web Interfaces.
Here is a screenshot of Postman doing an initial authentication — Post to retrieve an access token.
Generate Token URL
https://<server-ip>/api/fmc_platform/v1/auth/generatetoken

Sending a post with basic authentication to the URL will produce an “x-auth-access-token”. This is good for 30 minutes Continue reading
Firepower FMC API – Initial Observations
As many of you know, I am not a developer but I do occasionally hack stuff together. This article is just some of the initial things I have learned working with the Firepower Management Console API.
A good place to start is the Firepower REST API Quick Start Guide. This can be found at the following URL.
Firepower REST API Quick Start Guide
One thing to note is that there is a recommendation to use a dedicated username for the API. I would go a step beyond that with a recommendation for testing and development. During development, I currently have a username for the FMC UI, a username for the API Explorer and a username for whatever tool I’m working with (Postman or a Python Scripts). The reason for the extra accounts is that logging in to any of the UI’s tends to generate a new token (and invalidate the old one). This causes a constant reauthentication to the Web Interfaces.
Here is a screenshot of Postman doing an initial authentication — Post to retrieve an access token.
Generate Token URL
https://<server-ip>/api/fmc_platform/v1/auth/generatetoken

Sending a post with basic authentication to the URL will produce an “x-auth-access-token”. This is good for 30 minutes Continue reading
Starting Today: NDSS Highlights the Best in Internet Security Research

You’ve undoubtedly heard about all sorts of Internet security vulnerabilities and incidents causing harm around the world, but the flip side of all that doom and gloom is all the promising efforts underway to create a more secure, private, and trusted Internet. Starting today and going through Wednesday (18-21 February), the Network and Distributed Systems Security (NDSS) Symposium takes place to present groundbreaking research in the world of Internet security.
This year marks the 25th anniversary of NDSS, and the Internet Society is proud to have been associated with it for over 20 years now. A key focus of the Internet Society has long been improving trust in the global open Internet. In order to promote this trust, we need new and innovative ideas and research on the security and privacy of our connected devices and the Internet that brings them together. NDSS is a top tier forum for highlighting this research.
NDSS 2018 is four full days featuring:
- Two exciting keynotes from Ari Juels and Parisa Tabriz
- Four workshops on Binary Analysis Research (BAR), Decentralized IoT Security and Standards (DISS), DNS Privacy (DNSPRIV), and Usable Security (USEC).
- A full program of 71 excellent peer-reviewed research papers organized into Continue reading
The Week in Internet News: Can Blockchain Improve IoT?
Blockchain merges with IoT? Could Blockchain technology help the Internet of Things become more resilient? IBM thinks so. The company is exploring ways to use Blockchain to build trust between devices and to accelerate transactions on the IoT. EETimes explores the issue.
Grand Theft IoT: Someone involved in the online community for the video game, “Grand Theft Auto: San Andreas” has spun up a new botnet made up of IoT devices, according to security firm Radware. For the price of $20, the botnet can supposedly launch a 300gbps Distributed Denial of Service attack, reports Motherboard.
AI on the rise: Nearly after of all CIOs have plans to implement artificial intelligence in the future, according to a recent Gartner survey. The IT research firm recommends that companies rolling out AI projects aim low to start, and focus augmenting workers instead of replacing them, according to a story on TechRepublic.
Where the jobs are: For a time, it appeared that actual deployments of Blockchain seemed to be lagging behind the buzz. But that appears to be changing, with Blockchain developers now in high demand, TechCrunch reports. Blockchain jobs are the second fastest growing category in the labor market, with 14 job openings Continue reading
Worth Reading: Whiteboxes for Everyone
Gian Paolo Boarina wrote a blog post describing why it’s so ridiculous to see everyone excited about the latest thing Netflix (or Google or Amazon or…) managed to pull off. Absolutely worth reading.
On a similar topic: did you notice that Google started promoting clientless SSL VPN as the next great thing? RFC 1925 anyone?
Verizon’s SD-WLAN Service Taps AI-Driven Bluetooth Capabilities
 Mist Systems' technology virtualizes the Bluetooth beacon.
Mist Systems' technology virtualizes the Bluetooth beacon.
Keeping our users safe
To everyone in Cloudflare, account security is one of our most important tasks. We recognize that to every customer on our platform, we are critical infrastructure. We also know that the simplest attacks often lead to the most devastating of outcomes. Most people think that if they are going to get hacked it will be by some clever ”zero day”. The reality couldn’t be farther from the truth.
Attackers are smart and they have realized that even in 2018, the human is still the weakest link in the chain. The 2017 Verizon breach report identified that 81% of hacking related breaches occurred as a result of weak credentials or credential theft, an increase from the 63% reported in 2016’s breach report.
Source: Verizon 2017 data breach report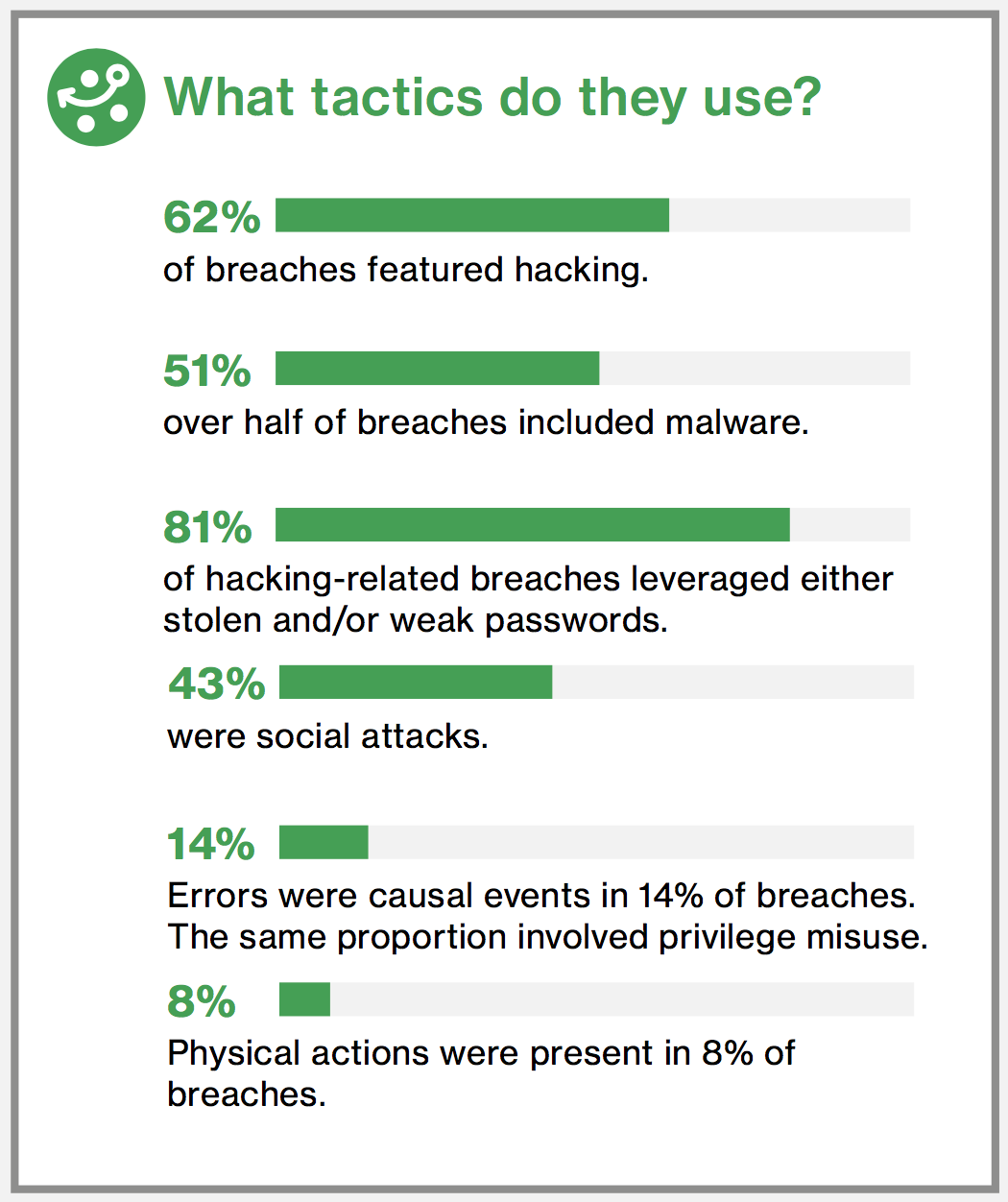
Your credentials are as important as your house or car keys. If someone copies or steals them, the repercussions can be catastrophic. If you suspect someone has access to your house keys you change your locks. If you aren’t fast enough, someone might break in.
Likewise if you realize that someone might have access to your password, the remedy is to change it. Too often, as with house keys, we are slow to Continue reading
Weekend Reads 180216: Skimmers and MITM and x509 Covert Channels, oh my…
He got the idea while analyzing the Vawtrak malware after discovering that it read multiple fields in the X.509 certificate provided by the server before proceeding. Jason initially thought these fields were used as a C2 channel, but then realized that Vawtrak performed a Continue reading
What it means to be an “automation first” enterprise
We’ve previously discussed how automation can give engineers some well-deserved extra free time. So how do those benefits extend to helping the company as a whole? Well, according to TechTarget’s article analyzing Gartner’s recent report about network innovation, there are some pretty obvious indicators that a company is putting automation first and achieving success. All a business has to do is take advantage of the automation practices used by hyperscale data centers. While it may sound impossible to operate on the same level as cloud giants like Amazon and Facebook, Gartner’s report states that there is a remarkable increase in efficiency and agility enterprises mimic from even 1% to 10% of the practices in hyperscale data centers. In this post, we’ll discuss what it looks like to be an “automation first” enterprise. And from what we can tell, it looks pretty good!
Reduced costs
Adopting automation doesn’t just save you time — it also saves you money. Let’s start with the fact that proprietary solutions are incredibly expensive on their own. In addition to steep initial costs, proprietary vendors prevent additional savings by not allowing customers to take advantage of automation tools like Ansible, Puppet and Chef. However, these capabilities Continue reading
Strong Results and Legal Win Not Enough for Arista Investors
 The company expects more modest growth in 2018.
The company expects more modest growth in 2018.
VMware Buys Cloud Security Startup CloudCoreo
 The deal boosts VMware's multi-cloud and security plays.
The deal boosts VMware's multi-cloud and security plays.
Google Pays $50M for IoT Firm Xively
 The deal will give Google more IoT firepower.
The deal will give Google more IoT firepower.
Network Engineer Certification in 2018
Last week I was in Mountain View, in a room full of senior Network Engineers, and we were talking about the skills that need to be developed by more junior Network Engineers. Suddenly someone shouted from the back "CCIE!" and the whole room started laughing.
So CCIE is a laughing stock now?
No need to get offended. You have to understand the context here:
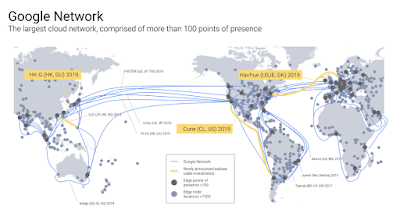
These group of people have been working for the best company in the world. They have been working on the most advanced network infrastructure. The company's undersea cables connect all contingents, to delivers 25% of worldwide Internet traffic.
These people didn't develop their skill through certification. They developed their skills by building the real stuff. When these group of Network Engineers realized the network capacity in the company's data centers has grown so fast that conventional routers and switches can't keep up to meet the requirements of its distributed systems, they decided to build its own instead. These Network Engineers build and operate software-defined networking, before the world invented that terminology. They've been automating network operation in Data Center, WAN, Internet Peering, all the way to Wifi and Enterprise networking, to support 7 company's Continue reading
Show 377: SD-WAN Use Cases With Silver Peak (Sponsored)
We explore real-world SD-WAN use cases, including service chaining and SaaS performance improvement, with sponsor Silver Peak in our latest Weekly Show podcast. The post Show 377: SD-WAN Use Cases With Silver Peak (Sponsored) appeared first on Packet Pushers.Celebrating the 25th Anniversary of NDSS
 This year we are celebrating the 25th anniversary of the Network and Distributed System Security Symposium (NDSS). NDSS is a premier academic research conference addressing a wide range of topics associated with improving trust in the Internet and its connected devices. A key focus of the Internet Society has long been improving trust in the global open Internet. In order to promote this trust, we need new and innovative ideas and research on the security and privacy of our connected devices and the Internet that connects them together.
This year we are celebrating the 25th anniversary of the Network and Distributed System Security Symposium (NDSS). NDSS is a premier academic research conference addressing a wide range of topics associated with improving trust in the Internet and its connected devices. A key focus of the Internet Society has long been improving trust in the global open Internet. In order to promote this trust, we need new and innovative ideas and research on the security and privacy of our connected devices and the Internet that connects them together.
NDSS 2018 is about to get underway in San Diego, CA (18-21 February). It will be the biggest NDSS symposium yet, featuring 71 peer-reviewed papers, 20 posters, 4 workshops, 2 keynotes, and a co-located research group meeting. Record registration numbers are a key indicator that NDSS 2018 is featuring vital and timely topics. Below are some of the highlights expected in the coming week.
Workshops
This year’s program officially starts with four workshops on Sunday, 18 February. NDSS workshops are organized around a single topic and provide an opportunity for greater dialogue amongst researchers and practitioners in the area. Each of this year’s workshop have dynamic agendas.
SDxCentral’s Weekly Roundup — February 15, 2018
 Qualcomm board meets Broadcom; Google releases Beta test of its Cloud TPUs; Tech Mahindra and VMware partner.
Qualcomm board meets Broadcom; Google releases Beta test of its Cloud TPUs; Tech Mahindra and VMware partner.