HW016: How mDNS Can Kill Wi-Fi Performance And What To Do About It
If you’re not paying attention to mDNS traffic, it might be hurting your Wi-Fi performance in a big way. Bryan Ward shares his research looking at the mDNS protocol on a higher ed network and its dramatic impact on Wi-Fi airtime.
The post HW016: How mDNS Can Kill Wi-Fi Performance And What To Do About It appeared first on Packet Pushers.
Understanding Cisco’s Generative Artificial Intelligence Strategy
Cisco’s approach to AI includes a processor designed for AI's networking demands, leveraging Cisco’s AI capabilities to bolster security and observability, and more.How to Speed Cyberattack Discovery
Who’s that suspicious network visitor? Is the guest explainable or a potential threat? Cyberattack discovery will help you find the answer.Better debugging for Cloudflare Workers, now with breakpoints
As developers, we’ve all experienced times when our code doesn’t work like we expect it to. Whatever the root cause is, being able to quickly dive in, diagnose the problem, and ship a fix is invaluable.
If you’re developing with Cloudflare Workers, we provide many tools to help you debug your applications; from your local environment all the way into production. This additional insight helps save you time and resources and provides visibility into how your application actually works — which can help you optimize and refactor code even before it goes live.
In this post, we’ll explore some of the tools we currently offer, and do a deep dive into one specific area — breakpoint debugging — looking at not only how to use it, but how we recently implemented it in our runtime, workerd.
Available Debugging Tools
Logs
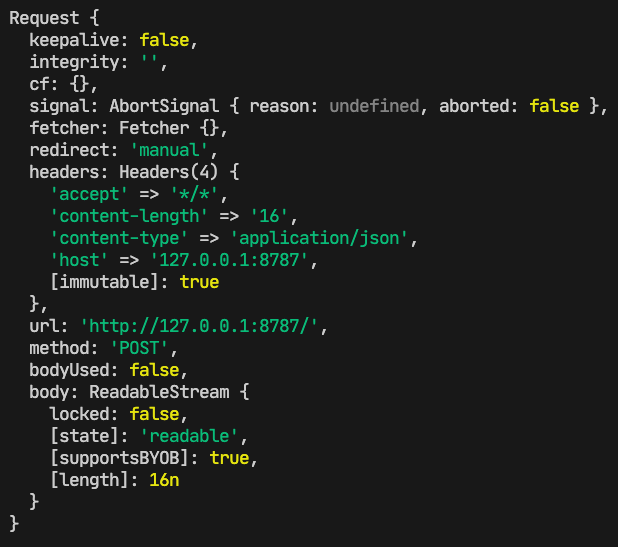
console.log. It might be the simplest tool for a developer to debug, but don’t underestimate it. Built into the Cloudflare runtime is node-like logging, which provides detailed, color-coded logs. Locally, you can view these logs in a terminal window, and they will look like this:
Outside local development, once your Worker is deployed, console.log statements are visible via Continue reading
DNS at IETF 118
The IETF met in Prague in the first week of November 2023, and, as usual there was a flurry of activity in the DNS-related Working groups. Here's a roundup of those DNS topics I found to be of interest at that meeting.Steve Bray: Why I joined Cloudflare

I am excited to announce that I joined Cloudflare last month as Head of Australia & New Zealand, to continue to build on Cloudflare’s success in the region through extending our valuable relationships with our customers and partners.
My journey to Cloudflare
I’ve been fortunate over my 25-year career in the IT industry to have worked for some of the most recognised and innovative organisations such as Oracle, Salesforce, and Zendesk. It’s been exciting to be inside these businesses as they’ve taken new ideas about how software can be developed and delivered to solve real world problems for any organisation’s customers. I’ve learned a lot by being a part of the industry, but probably more importantly, I’ve learned the most from the smart, experienced, diverse groups of talented people that I’ve had the pleasure to work with in ANZ and across Asia Pacific. I have always been interested in the problems that organisations are trying to solve through technology — for example, responding to strategic challenges, reducing cost, improving revenue, reducing risk — and joining Cloudflare is an opportunity to stay focussed on addressing those critical issues with our customers and partners using Cloudflare’s innovative solutions.
So why Cloudflare?
Cloudflare’s Continue reading
NB457: Broadcom, VMware Tie The Knot; Nvidia SuperNICs Target AI Ethernet Acceleration
Broadcom clears the last hurdle to close its $69 billion purchase of VMware, but what comes next? Nvidia debuts a SuperNIC to accelerate Ethernet for AI workloads, China and India advance their satellite Internet efforts, and Nvidia puts up jaw-dropping results in its latest quarterly earnings.
The post NB457: Broadcom, VMware Tie The Knot; Nvidia SuperNICs Target AI Ethernet Acceleration appeared first on Packet Pushers.
NB457: Broadcom, VMware Tie The Knot; Nvidia SuperNICs Target AI Ethernet Acceleration
Now that Broadcom’s $69 billion VMware acquisition is complete, will Broadcom invest more in VMware to compete in multi-cloud or settle for profitable revenue collection from existing customers? Nvidia debuts a SuperNIC designed to accelerate Ethernet to support AI workloads and announces partnerships with server makers to bundle its NIC in an AI Ethernet stack.... Read more »Tech Bytes: Nokia Deepfield Brings Fresh Analytics, New Gear To The DDoS Fight (Sponsored)
Today on Tech Bytes, sponsored by Nokia, we’ll talk about what’s brewing on the DDoS front and how Nokia’s Deepfield is bringing new analytics techniques to the fight.
The post Tech Bytes: Nokia Deepfield Brings Fresh Analytics, New Gear To The DDoS Fight (Sponsored) appeared first on Packet Pushers.
Tech Bytes: Nokia Deepfield Brings Fresh Analytics, New Gear To The DDoS Fight (Sponsored)
Distributed Denial of Service attacks, or DDoS, have plagued the Internet for decades. And attackers are finding new ways to take advantage of higher levels of bandwidth and the ever-growing number of network-connected devices. Today on Tech Bytes, sponsored by Nokia, we’ll talk about what’s brewing on the DDoS front and how Nokia’s Deepfield is... Read more »Cloudflare named a leader in Forrester Edge Development Platforms Wave, Q4 2023
This post is also available in Español, Deutsch, Português, 日本語, 한국어.
Forrester has recognized Cloudflare as a leader in The Forrester Wave™: Edge Development Platforms, Q4 2023 with the top score in the current offering category.
According to the report by Principal Analyst, Devin Dickerson, “Cloudflare’s edge development platform provides the building blocks enterprises need to create full stack distributed applications and enables developers to take advantage of a globally distributed network of compute, storage and programmable security without being experts on CAP theorem.“
Over one million developers are building applications using the Developer Platform products including Workers, Pages, R2, KV, Queues, Durable Objects, D1, Stream, Images, and more. Developers can easily deploy highly distributed, full-stack applications using Cloudflare’s full suite of compute, storage, and developer services.
Workers make Cloudflare’s network programmable
“ A key strength of the platform is the interoperability with Cloudflare’s programmable global CDN combined with a deployment model that leverages intelligent workload placement.”
– The Forrester Wave™: Edge Development Platforms, Q4 2023
Workers run across Cloudflare’s global network, provide APIs to read from and write directly to the local cache, Continue reading
Asking The Right Question About The Wireless Future

It wasn’t that long ago that I wrote a piece about how Wi-Fi 6E isn’t going to move the needle very much in terms of connectivity. I stand by my convictions that the technology is just too new and doesn’t provide a great impetus to force users to upgrade or augment systems that are already deployed. Thankfully, someone at the recent Mobility Field Day 10 went and did a great job of summarizing some of my objections in a much simpler way. Thanks to Nick Swiatecki for this amazing presentation:
He captured so many of my hesitations as he discussed the future of wireless connectivity. And he managed to expand on them perfectly!
New Isn’t Automatically Better
Any time I see someone telling me that Wi-Fi 7 is right around the corner and that we need to see what it brings I can’t help but laugh. There may be devices that have support for it right now, but as Nick points out in the above video, that’s only one part of the puzzle. We still have to wait for the clients and the regulatory bodies to catch up to the infrastructure technology. Could you imagine if we did the same Continue reading
Can a Router Use the Default Route to Reach BGP Next Hops?
TL&DR: Yes.
Starting with RFC 4271, Route Resolvability Condition:
- A route without an outgoing interface is resolvable if its next hop is resolvable without recursively using the same route.
- A route with an outgoing interface is always considered resolvable.
- BGP routes can be resolved through routes with just a next hop or an outgoing interface.
Can a Router Use the Default Route to Reach BGP Next Hops?
TL&DR: Yes.
Starting with RFC 4271, Route Resolvability Condition:
- A route without an outgoing interface is resolvable if its next hop is resolvable without recursively using the same route.
- A route with an outgoing interface is always considered resolvable.
- BGP routes can be resolved through routes with just a next hop or an outgoing interface.
Weekly Roundup: NVIDIA Addresses AI Infrastructure Issues
NVIDIA announcements this week, like other industry efforts this year, aim to speed up Ethernet networking in an AI infrastructure.Worth Reading: Network Automation with GitHub Actions
George Davitiani put together a lovely proof-of-concept using GitHub actions to deploy modified configurations to network devices. Even better, he documented the whole setup, and the way to reproduce it. I’m positive you’ll find a few ideas browsing through what he did.
Worth Reading: Network Automation with GitHub Actions
George Davitiani put together a lovely proof-of-concept using GitHub actions to deploy modified configurations to network devices. Even better, he documented the whole setup, and the way to reproduce it. I’m positive you’ll find a few ideas browsing through what he did.
Worth Reading: Going CCNP Emeritus
Daniel Teycheney decided not to renew his CCNP status and used this opportunity to publish his thoughts on IT certifications. Not surprisingly, I agree with most of the things he said, but I never put it in writing so succinctly.
Red Pill Warning: Reading his blog post might damage your rosy view of the networking industry. You’ve been warned ;)
Worth Reading: Going CCNP Emeritus
Daniel Teycheney decided not to renew his CCNP status and used this opportunity to publish his thoughts on IT certifications. Not surprisingly, I agree with most of the things he said, but I never put it in writing so succinctly.
Red Pill Warning: Reading his blog post might damage your rosy view of the networking industry. You’ve been warned ;)
Do hackers eat turkey? And other Thanksgiving Internet trends
Thanksgiving is a tradition celebrated by millions of Americans across six time zones and 50 states, usually involving travel and bringing families together. This year, it was celebrated yesterday, on November 23, 2023. With the Internet so deeply enmeshed into our daily lives, anything that changes how so many people behave is going to also have an impact on online traffic. But how big an impact, exactly?
At a high level: a 10% daily decrease in Internet traffic in the US (compared to the previous week). That happens to be the exact same percentage decrease we observed in 2022. So, Thanksgiving in the US, at least in the realm of Internet traffic, seems consistent with last year.
Let’s dig into more details about how people deal with cooking (or online ordering!) and whether family gatherings are less online, according to our Cloudflare Radar data. We’ll also touch on whether hackers stop for turkey, too.
The Thanksgiving hour: around 15:00 (local time)
While we can see a 10% overall daily drop in US traffic due to Thanksgiving, the drop is even more noticeable when examining traffic on an hour-by-hour basis. Internet activity began to decrease significantly after 12:00 EST, persisting Continue reading