Worth Reading: What if there is no money in systems?
The post Worth Reading: What if there is no money in systems? appeared first on rule 11 reader.
CA and Netrounds Partner to Combine Monitoring and Testing
 CA wants to be the go-to vendor for Cisco's SD-WAN environment.
CA wants to be the go-to vendor for Cisco's SD-WAN environment.
CCIE/CCDE Re-certification: An Opportunity to Learn and Grow
I did not pass my CCDE re-certification last week. Why write a blog about a “failure”? Honestly? Because I think we as an IT industry overly focus and give too many kudos to the passing only. Not to the hours and hours of studying and learning… not to the lessons learned… not to the growth gained from the studying journey. Just to the “pass/fail”. Well damn… no wonder people cheat. Their focus isn’t on the learning or the journey. Just the passing.
I thoroughly believe the expression –
Sometimes you win….. Sometimes you learn.
Did I want to pass last week? ROFL! Are you kidding? Of course I did! Did I “deserve” to pass? Well…. um…. err… not exactly.
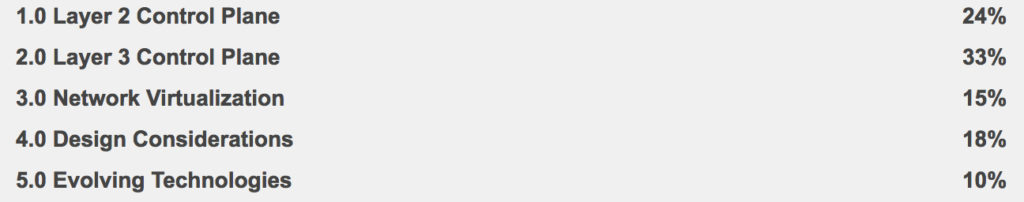
See that 10% at the bottom of the “Written Exam Topics v2.1?” Truth be told I didn’t quite exactly study that part very much.
So what is my plan now?
LEARN
Honestly in my job I am not doing much Cloud, SDN, or IoT. AND I have to admit I am quite happy I am now essentially forced to learn these to a Continue reading
Watch Out for Comcast in Network Virtualization, Says TBR
 SDN and NFV spending will reach $168B by 2022.
SDN and NFV spending will reach $168B by 2022.
Broadcom Adds Software Control Over Chip-Based Switches
 Programmability move looks to target a recent play by Barefoot Networks.
Programmability move looks to target a recent play by Barefoot Networks.
CCNA Wireless – CCNA Wireless Notes Chapter 6
802.11 Frame Format
In a wired Ethernet network, the switch is not an active participant in communication at L2. In a wireless LAN, the AP is an active participant unless something like 802.11z, Extension to Direct Link Setup (DLS) is used.
To direct frames through the AP, the radio must have a MAC address, known as the BSSID.
802.11 frames can carry a maximum payload of 2304 bytes.
To support wireless communication, the Ethernet frame format is quite different compared to wired networks. The Ethernet frame starts out with a 2-byte Frame Control field, identifying the frame type, the direction the frame is traveling in and more.
| Name | Length (bits) |
|---|---|
| Protocol Version | 2 |
| Type | 2 |
| Subtype | 4 |
| To DS | 1 |
| From DS | 1 |
| More Frag | 1 |
| Retry | 1 |
| Pwr Mgmt | 1 |
| More Data | 1 |
| WEP | 1 |
| Order | 1 |
In a common scenario with multiple clients associated with an AP that is connected to an DS, frames travel from clients towards the DS or from the DS towards the clients.
The frame motion is indicated by two bits, To DS and From DS, in the Frame Control field.
Frames sent by a wireless client will Continue reading
Nokia’s Silicon is the ‘Best Router Chip on the Planet,’ Says Analyst
![]() Nokia’s FP4 silicon enables petabit-class routers.
Nokia’s FP4 silicon enables petabit-class routers.
MemSQL Managed Cloud Database Supports AWS and Microsoft Azure
 Microsoft, Facebook alums founded the database startup.
Microsoft, Facebook alums founded the database startup.
For Me the Internet Is Everything: Supporting Local Heroes in Armenia
Andranik, Sipan, Rudolf and Vahan have several things in common: they are young, they have dreams, they love music, and they love the Internet. The four of them are visual impaired.
They met through the Internet Availability Center at the Cultural House of the Armenian Society of Blinds (ASB).
I had the chance to visit the Center last year and Rudolf told me: “For me the Internet is everything. I cannot imagine what my life, my studies would be without it.”
Worth Reading: The next five years of IPv6
The post Worth Reading: The next five years of IPv6 appeared first on rule 11 reader.