Response:Ingram Micro Sold. Supply Chain Integrity Question
One of the biggest distributors of IT technology is now owned by a Chinese company. Supply chain integrity anyone ?
The post Response:Ingram Micro Sold. Supply Chain Integrity Question appeared first on EtherealMind.
Research ‘net: Dirt jumper -smart

Distributed Denial of Service (DDoS) attacks are often used to hold companies—particularly wealthy companies, like financial institutions—to ransom. Given the number of botnets in the world which can be purchased by the hour, and the relative ease with which new systems can be infected (especially given the rise of the Internet of Things), it’s important to find new and innovative ways to protect against such attacks. Dirt Jumper is a common DDoS platform based on the original Dirt, widely used to initiate such attacks. Probably the most effective protection against DDoS attacks, particularly if you can’t pin down the botnet and block it on a per-IP-address basis (try that one some time) is to construct a tar pit that will consume the attacker’s resources at a rate faster than your server’s are consumed.
The paper linked here describes one such tar pit, and even goes into detail around a defect in the Dirt Jumper platform, and how the defenders exploited the defect. This is not only instructive in terms of understanding and countering DDoS attacks, it’s also instructive from another angle. If you think software is going to eat the world, remember that even hacking software has defects that Continue reading
Verizon Chooses Viptela’s SD-WAN
 Where does this leave Versa?
Where does this leave Versa?
Golang is GO GO GO!
You will have to be a programmer if you’re going to be a network engineer in the future,
they say. I don’t agree, but it surely helps you do your job. But what language should you learn? Perl? (no) Python? (maybe) Ruby? (perhaps) Every time I say something about learning Python, a little voice on Twitter says Or Go!
. Go? Go. And so, sucker that I am, I gave it a go (pun intended). TLDR: I think you should, too.
The Go Programming Language
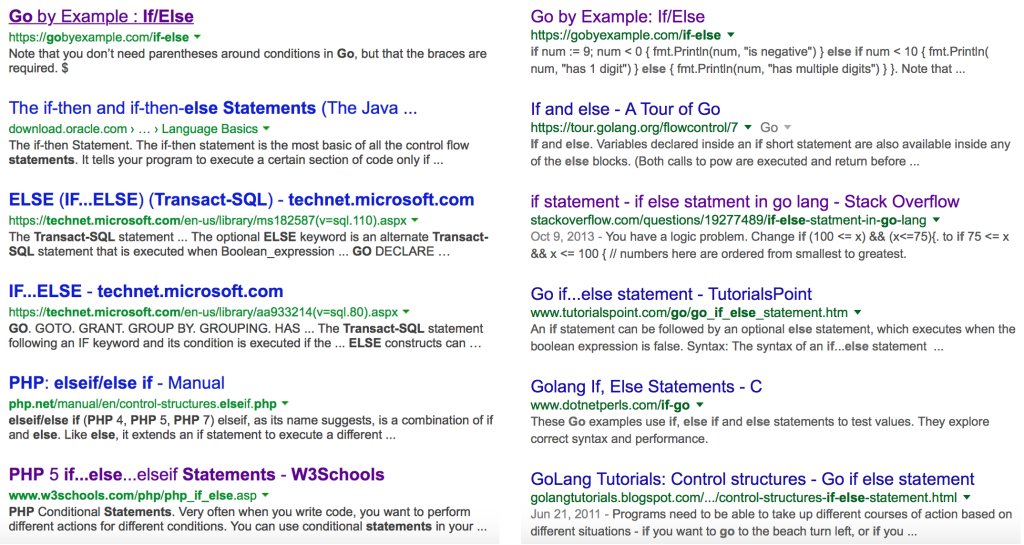
The name Go feels like it should be a terrible word to search for on the Internet because it’s so short, but searches actually work remarkably well if you use Google Search. Compare the results of a search for “go if then else” from Bing and Google below; I’ll let you guess which is which:
Maybe Google has learned from my search history. So, what’s important to know? Go is:
- Open source. The source code is readily available and can sometimes be helpful to figure out what’s going on.
- Free, obviously
- Pretty fast
- Multi-platform (Linux, OS X, Windows for starters)
- A compiled language
- Strongly typed
- Capable of Continue reading
Nuage Networks White Paper: How to Accelerate Docker Container Networking Tasks with SDN and Policy-Based Automation
 Explore the solutions the Nuage VSP & Docker offer to connect the networking environment to container-based applications with this white paper.
Explore the solutions the Nuage VSP & Docker offer to connect the networking environment to container-based applications with this white paper.
Worth Reading: Networking Field Day on Skyport Systems

The post Worth Reading: Networking Field Day on Skyport Systems appeared first on 'net work.
Disrupting Mobile Networking with Programmable Mobility Management
On February 16, 2016, Brocade made two strategically important announcements that outlined the overall mobile network strategy and additions to the open mobile networking ecosystem. As mentioned in my prior blog on Mobile World Congress, the mobile industry is about to go through a mega transition, from 3G/4G networks to 5G. However, unlike both 3G... Read more →
9 Tech Companies Leading The IoT Charge
Cisco and Intel are among the technology heavyweights influencing the Internet of Things landscape.
vBrownBag: Techniques of a Network Detective
An essential part of running any network is being able to quickly diagnose and resolve service impacting events. But how does one do that in the world of IT where the only thing constant about technology is the constant change? We need to lean more heavily on the troubleshooting methodology and approach. On the “techniques” of being a Network Detective. How does one work towards solving ANY “who done it”? Simple…. one Gathers the Facts Collects the Clues Follows the Evidence Interviews the Witnesses, and Questions the Suspects We will take this approach and show how one can use this and apply it in troubleshooting any networking “who done it”
Looking for more on some of the Techniques of a Network Detective? Check out CiscoLive on Demand Library for BRKARC-2002 or my blog on Packet Pushers. Note: CiscoLive On Demand Library is completely free.
Just click on the one you want.  Have fun!
Have fun!
Why Private Cloud Needs DevOps And SDN
Building a private cloud requires treating the infrastructure as code.
Programmable ASICs
I love learning about network hardware, but I’ve always found it difficult to get detailed information on ASICS. We had a great presentation from Dave Zacks on the Cisco 3850 programmable ASIC at the Cisco Live Europe Tech Field Day … Continue reading
The post Programmable ASICs appeared first on The Network Sherpa.