Don’t Be Overly Enthusiastic about Vendor Claims (This Time It’s Brocade)
I was running the first part of the Data Center Fabrics Update webinar last week, mentioned that Brocade VDX 6740 supports Flex ports (a port you can use as Fibre Channel or 10GE port), and someone immediately wrote a comment saying “so does VDX 6940”. I was almost sure Flex ports aren’t available on VDX 6940 yet, and as always turned to vendor documentation to figure it out.
As expected, the data sheet is a bit vague, somewhat reflecting reality, but also veering into the realm of futures instead of features. Here’s what they say:
Read more ...Open Source Routing: A Comparison
I have been getting more interested in open-source networking software, and I figured it was time to write a post comparing some of the more popular open source projects in this space.
Not only do we have several options (which hasn’t always been the case) for running routing protocols in FOSS, but we also have a variety of use cases that are increasing in popularity (using BGP for SDN-type purposes, not just to do internet peering). So isn’t an idea limited to enthusiasts who like to spin their own router - this kind of software has very interesting large-scale applications as well.
This won’t be a comprehensive list, just the top three that I’ve been looking into. I also won’t be going into too much detail on how to set all this software up - I’m saving that for a follow-up post.
Quagga
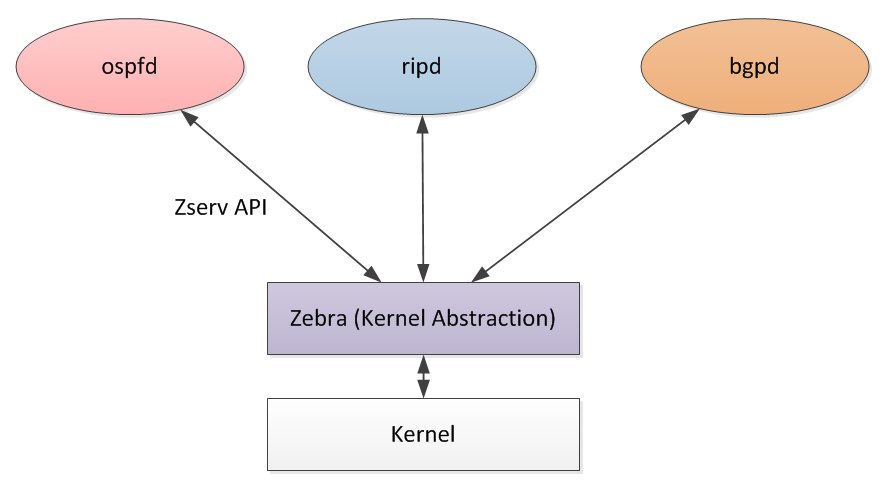
Quagga is at the top of this list primarily because from my perspective, it is the most well-known. It is best to think of Quagga as a collection of smaller daemons, each with a specific task. This task may be to run a routing protocol like OSPF or BGP, or it may be something else.
In this Continue reading
Open Source Routing: A Comparison
I have been getting more interested in open-source networking software, and I figured it was time to write a post comparing some of the more popular open source projects in this space.
Not only do we have several options (which hasn’t always been the case) for running routing protocols in FOSS, but we also have a variety of use cases that are increasing in popularity (using BGP for SDN-type purposes, not just to do internet peering). So isn’t an idea limited to enthusiasts who like to spin their own router - this kind of software has very interesting large-scale applications as well.
This won’t be a comprehensive list, just the top three that I’ve been looking into. I also won’t be going into too much detail on how to set all this software up - I’m saving that for a follow-up post.
Quagga
Quagga is at the top of this list primarily because from my perspective, it is the most well-known. It is best to think of Quagga as a collection of smaller daemons, each with a specific task. This task may be to run a routing protocol like OSPF or BGP, or it may be something else.
In this Continue reading
Programming an ACI Fabric
By now, you’ve probably heard of Cisco’s Software Defined Networking (SDN) solution that is centered around ACI, or the Application Centric Infrastructure. Like most SDN platforms, a key component is the controller otherwise known as the Application Policy Infrastructure Controller (APIC) in the case of ACI. The APIC provides a single pane of glass that centralizes policy, configuration, and monitoring of the complete fabric. It also more importantly exposes the complete system via an object oriented REST API, which is what we’ll look at in this post.
By itself, ACI reduces the number of touch points in the network. This is no different than any other controller-based network that exists today and is a great step in the right direction. We can then honestly say SDN simplifies operations.
The issue is if you don’t have something else driving ACI, or any other SDN solution for that matter, it could take a large number clicks within the UI to configure a new tenant, application, or whatever is being configured. This is error prone as we all know it’s pretty easy to fat finger something! Because of this, it still makes total sense to automate network fabrics even if it’s not for Continue reading
Avago Might Buy Broadcom, Though It’s Hard to Fathom
![]() Rumors of a monster chip deal run counter to Broadcom's personality — but times do change.
Rumors of a monster chip deal run counter to Broadcom's personality — but times do change.