HS040 Top Mistakes Technology Strategists Make
It might be curmudgeon day. Johna and Greg ask what are mistakes that we have seen in technology strategies.Machine Learning Models in Your Network: Monitoring and Performance Aspects
A machine learning model behaves differently from traditional IT infrastructure and requires different types of monitoring.A Closer Look at Our Demos at Mobile World Congress 2023
A Closer Look at VMware Networking and Security Demos at MWC 2023
Efficiency, scalability, and security are critical for modern telco networks. Operating modern 5G network infrastructure requires the ability to manage complex network operations across large-scale multi-cloud and edge environments while also meeting complex security requirements.
The VMware Telco Cloud Platform was built from the ground up to help Communications Service Providers (CSPs) meet these challenges. It combines the capabilities of VMware’s cloud infrastructure and network virtualization software (VMware vSphere, vSAN, and NSX) with a set of networking, security, and management tools built for the telco industry. The platform helps CSPs deploy and manage virtualized network functions and containerized network functions (VNFs and CNFs), reduce costs, and enhance network security while enabling new revenue-generating services.

VMware NSX: Integrated Layer 2 to Layer 7 Platform for Telco Networking and Security Services
At MWC 2023, the VMware team will demonstrate four key use cases for the VMware Telco Cloud Platform.

Demo 1 – Network Acceleration for 5G Workloads using SmartNIC for NSX
Networking and Security performance acceleration powered by Data Processing Units (DPUs) enables a telco-grade virtualized 5G infrastructure. VMware is announcing the General Availability of DPU-based acceleration for NSX Continue reading
The Chief Zero Trust Officer: a new role for a new era of cybersecurity

Setting the stage for Zero Trust

Over the last few years the topic of cyber security has moved from the IT department to the board room. The current climate of geopolitical and economic uncertainty has made the threat of cyber attacks all the more pressing, with businesses of all sizes and across all industries feeling the impact. From the potential for a crippling ransomware attack to a data breach that could compromise sensitive consumer information, the risks are real and potentially catastrophic. Organizations are recognizing the need for better resilience and preparation regarding cybersecurity. It is not enough to simply react to attacks as they happen; companies must proactively prepare for the inevitable in their approach to cybersecurity.
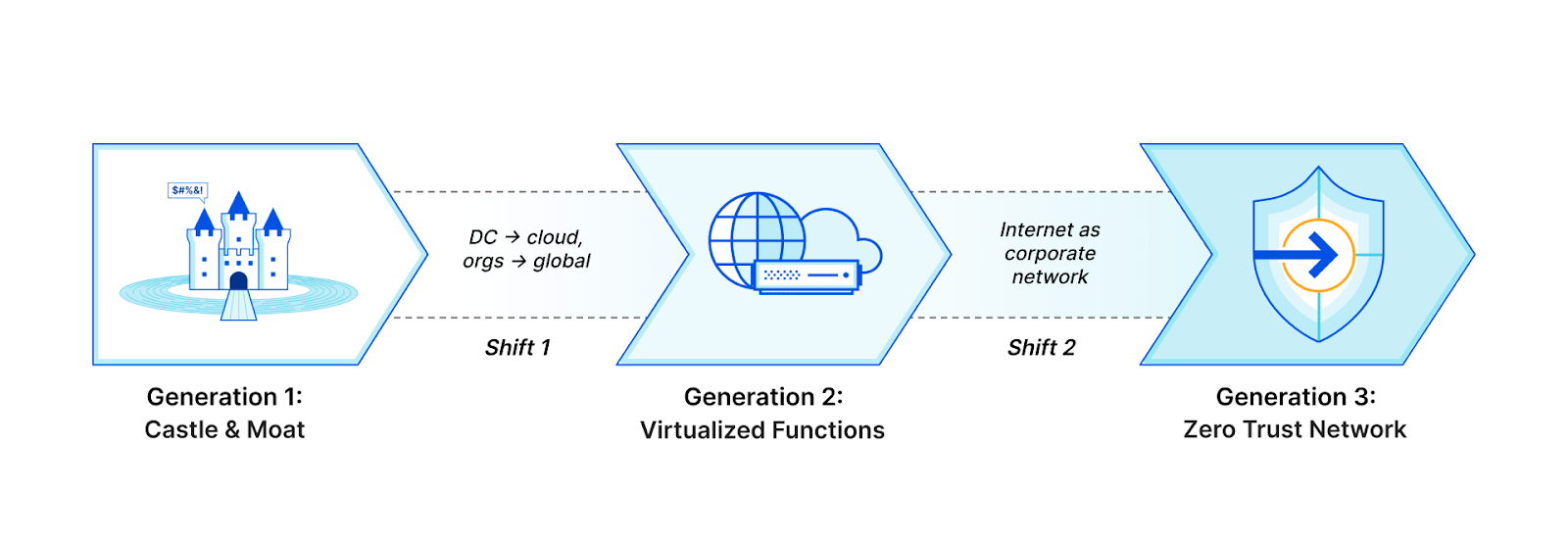
The security approach that has gained the most traction in recent years is the concept of Zero Trust. The basic principle behind Zero Trust is simple: don't trust anything; verify everything. The impetus for a modern Zero Trust architecture is that traditional perimeter-based (castle-and-moat) security models are no longer sufficient in today's digitally distributed landscape. Organizations must adopt a holistic approach to security based on verifying the identity and trustworthiness of all users, devices, and systems that access their networks and data.
Some Operations Are Not Worth Automating
Ish wrote an interesting comment on my Network Automation Expert Beginners blog post. He started with:
[Our network has] about 40 sites, but we don’t do total refresh cycles in bulk, just as needed. Everything we do is sporadic, and I’m trying to see the ROI on learning automation for things that are done once in a while that don’t take much time to do manually anyway.
There are two aspects to this part of his comment:
Some Operations Are Not Worth Automating
Ish wrote an interesting comment on my Network Automation Expert Beginners blog post. He started with:
[Our network has] about 40 sites, but we don’t do total refresh cycles in bulk, just as needed. Everything we do is sporadic, and I’m trying to see the ROI on learning automation for things that are done once in a while that don’t take much time to do manually anyway.
There are two aspects to this part of his comment:
The Magic of Multi-cloud Networking
Any sufficiently advanced technology is indistinguishable from magic. – Arthur C. Clarke.12 Practical Tips for Entry-level Job Seeker and Interns in Tech
It’s been almost 25 long years since I started my bachelor’s degree, some 17 years since I began my master’s degree, and around 15 years since I decided to leave a Ph.D. scholarship behind and go back to full-time professional work. Many things have changed, yet one thing has remained the same: the race among […]
The post 12 Practical Tips for Entry-level Job Seeker and Interns in Tech appeared first on Packet Pushers.
Discover Cloud Networking and Security with VMware at Mobile World Congress 2023

They say you should work smarter, not harder. We agree, which is why we’ll be showcasing work at MWC 2023 that brings efficiency and intelligence to modern networking designed to help businesses thrive in the digital era through telco-friendly, smarter networking solutions.
Keep reading for a preview of what to expect from the VMware Networking and Security team at the event – and join us in person in Hall 3, stand 3M11, to check out the latest innovations in cloud networking and security for yourself.
Smarter, More Efficient Networks
The overall vision that we’ll be displaying in Barcelona at Mobile World Congress from February 27 to March 2 focuses on two key concepts – increasing network efficiency and generating value through smart networking solutions.

Specifically, we’ll be displaying:
- Technology that enhances the Telco Efficiency of Communications Service Provider networks by guiding customers in boosting network density and reducing energy usage. Visit our booth to learn how optimizing the technology stack helps cut costs and enhance service flexibility.
- Solutions for building Smarter Networks by leveraging breakthroughs in RAN to Edge to Core Networks and creating programmable settings that Communications Service Providers can leverage to provide advanced next-generation services. These elevated service Continue reading
Why Aren’t There More Technical MBAs?

This weekend I was listening to the latest episode of the Art of Network Engineering podcast featuring Russ White. Russ is one of those guests that has a breadth of knowledge outside of technology that colors the way he looks at things in the realm of enterprise IT. Plus he’s a fun interview.
One of the questions he asked was around the idea of technical MBAs. For those that might not know, MBA stands for Masters of Business Administration, which is a post-graduate college business degree. An MBA is widely regarded as a way to put yourself on a track to be a manager for a company in some capacity. An MBA is punching a ticket to be a future CEO. Why does it seem like the number of MBAs coming out of prestigious business schools don’t have a technical background then?
Where the Action Is
I’m going to quote liberally from a book I’ve been reading called The Personal MBA by Josh Kaufman. In it, Kaufman lays out the reasoning behind using his book to study the principles behind the information given in MBA classes instead of spending $200,000 to go to a business school for two years for Continue reading
Network Dictionary: “Send-Forth”
 Replacing 'leaving do' with 'send forth'
Replacing 'leaving do' with 'send forth'
Chat-based AI LLMs and Certification Testing
 The end of multi-choice answers might be in sight
The end of multi-choice answers might be in sight
Start Multiple netlab Labs on the Same Server
A heavy netlab user sent me an email along these lines:
We’re running multiple labs in parallel on the same server, and we’re experiencing all sorts of clashes like overlapping management IP addresses. We “solved” that by using static device identifiers in our labs, but I’m wondering if there’s a better way of doing it?
That’s exactly the sort of real-life challenges I love working on, so it wasn’t hard to get me excited, and the results are bundled in netlab release 1.5.
Start Multiple netlab Labs on the Same Server
A heavy netlab user sent me an email along these lines:
We’re running multiple labs in parallel on the same server, and we’re experiencing all sorts of clashes like overlapping management IP addresses. We “solved” that by using static device identifiers in our labs, but I’m wondering if there’s a better way of doing it?
That’s exactly the sort of real-life challenges I love working on, so it wasn’t hard to get me excited, and the results are bundled in netlab release 1.5.
 s inability to access or use its software during a ransomware attack was outside the scope of its “businessowners” policy.
s inability to access or use its software during a ransomware attack was outside the scope of its “businessowners” policy.