Cumulus Linux Network Command Line Utility (NCLU)
While ranting about Linux data plane configuration, I mentioned an interesting solution: Cumulus Linux Network Command Line Utility (NCLU), an attempt to make Linux networking more palatable to more traditional networking engineers.
NCLU is a simple wrapper around ifupdown2 and frr packages. You can execute net add and net del commands to set or remove configuration parameters1, and NCLU translates those commands into changes to corresponding configuration files.
Cumulus Linux Network Command Line Utility (NCLU)
While ranting about Linux data plane configuration, I mentioned an interesting solution: Cumulus Linux Network Command Line Utility (NCLU), an attempt to make Linux networking more palatable to more traditional networking engineers.
NCLU is a simple wrapper around ifupdown2 and frr packages. You can execute net add and net del commands to set or remove configuration parameters1, and NCLU translates those commands into changes to corresponding configuration files.
Privacy And Networking Part 7: DNS Queries And Having A Breach Plan
In the final post in this privacy series, Russ White looks at privacy information that can be gleaned from DNS queries, and outlines essential steps in developing your breach plan. Don't have a breach plan? Here's your opportunity to start one.
The post Privacy And Networking Part 7: DNS Queries And Having A Breach Plan appeared first on Packet Pushers.
“Trees Grow” and Other Tales of Wireless Deployment Challenges
Telcos offering 5G must analyze massive network usage, vegetation, building height, and other datasets, looking for changes and seeking ways to optimize antenna deployment to match services with demand.Day Two Cloud 165: Does Your Infrastructure Need Istio?
On today's Day Two Cloud we dive into Istio with Kevin Davin, a senior back end engineer who works deeply with Istio. We discuss Istio's promises, balancing its complexity with the capabilities it enables, understanding when and when not to use it, and more.
The post Day Two Cloud 165: Does Your Infrastructure Need Istio? appeared first on Packet Pushers.
Day Two Cloud 165: Does Your Infrastructure Need Istio?
On today's Day Two Cloud we dive into Istio with Kevin Davin, a senior back end engineer who works deeply with Istio. We discuss Istio's promises, balancing its complexity with the capabilities it enables, understanding when and when not to use it, and more.Announcing Turnstile, a user-friendly, privacy-preserving alternative to CAPTCHA


Today, we’re announcing the open beta of Turnstile, an invisible alternative to CAPTCHA. Anyone, anywhere on the Internet, who wants to replace CAPTCHA on their site will be able to call a simple API, without having to be a Cloudflare customer or sending traffic through the Cloudflare global network. Sign up here for free.
There is no point in rehashing the fact that CAPTCHA provides a terrible user experience. It's been discussed in detail before on this blog, and countless times elsewhere. The creator of the CAPTCHA has even publicly lamented that he “unwittingly created a system that was frittering away, in ten-second increments, millions of hours of a most precious resource: human brain cycles.” We hate it, you hate it, everyone hates it. Today we’re giving everyone a better option.
Turnstile is our smart CAPTCHA alternative. It automatically chooses from a rotating suite of non-intrusive browser challenges based on telemetry and client behavior exhibited during a session. We talked in an earlier post about how we’ve used our Managed Challenge system to reduce our use of CAPTCHA by 91%. Now anyone can take advantage of this same technology to stop using CAPTCHA on their own site.
UX Continue reading
Monitor your own network with free network flow analytics from Cloudflare


As a network engineer or manager, answering questions about the traffic flowing across your infrastructure is a key part of your job. Cloudflare built Magic Network Monitoring (previously called Flow Based Monitoring) to give you better visibility into your network and to answer questions like, “What is my network’s peak traffic volume? What are the sources of that traffic? When does my network see that traffic?” Today, Cloudflare is excited to announce early access to a free version of Magic Network Monitoring that will be available to everyone. You can request early access by filling out this form.
Magic Network Monitoring now features a powerful analytics dashboard, self-serve configuration, and a step-by-step onboarding wizard. You’ll have access to a tool that helps you visualize your traffic and filter by packet characteristics including protocols, source IPs, destination IPs, ports, TCP flags, and router IP. Magic Network Monitoring also includes network traffic volume alerts for specific IP addresses or IP prefixes on your network.
Making Network Monitoring easy
Magic Networking Monitoring allows customers to collect network analytics without installing a physical device like a network TAP (Test Access Point) or setting up overly complex remote monitoring systems. Our product works Continue reading
Introducing Cloudflare’s free Botnet Threat Feed for service providers

We’re pleased to introduce Cloudflare’s free Botnet Threat Feed for Service Providers. This includes all types of service providers, ranging from hosting providers to ISPs and cloud compute providers.
This feed will give service providers threat intelligence on their own IP addresses that have participated in HTTP DDoS attacks as observed from the Cloudflare network — allowing them to crack down on abusers, take down botnet nodes, reduce their abuse-driven costs, and ultimately reduce the amount and force of DDoS attacks across the Internet. We’re giving away this feed for free as part of our mission to help build a better Internet.
Service providers that operate their own IP space can now sign up to the early access waiting list.
Cloudflare’s unique vantage point on DDoS attacks
Cloudflare provides services to millions of customers ranging from small businesses and individual developers to large enterprises, including 29% of Fortune 1000 companies. Today, about 20% of websites rely directly on Cloudflare’s services. This gives us a unique vantage point on tremendous amounts of DDoS attacks that target our customers.
DDoS attacks, by definition, are distributed. They originate from botnets of many sources — in some cases, from hundreds of thousands to millions Continue reading
Private by design: building privacy-preserving products with Cloudflare’s Privacy Edge


When Cloudflare was founded, our value proposition had three pillars: more secure, more reliable, and more performant. Over time, we’ve realized that a better Internet is also a more private Internet, and we want to play a role in building it.
User awareness and expectations of and for privacy are higher than ever, but we believe that application developers and platforms shouldn’t have to start from scratch. We’re excited to introduce Privacy Edge – Code Auditability, Privacy Gateway, Privacy Proxy, and Cooperative Analytics – a suite of products that make it easy for site owners and developers to build privacy into their products, by default.
Building network-level privacy into the foundations of app infrastructure
As you’re browsing the web every day, information from the networks and apps you use can expose more information than you intend. When accumulated over time, identifiers like your IP address, cookies, browser and device characteristics create a unique profile that can be used to track your browsing activity. We don’t think this status quo is right for the Internet, or that consumers should have to understand the complex ecosystem of third-party trackers to maintain privacy. Instead, we’ve been working on technologies that encourage and enable Continue reading
We’ve shipped so many products the Cloudflare dashboard needed its own search engine


Today we’re proud to announce our first release of quick search for the Cloudflare dashboard, a beta version of our first ever cross-dashboard search tool to help you navigate our products and features. This first release is now available to a small percentage of our customers. Want to request early access? Let us know by filling out this form.
What we’re launching
We’re launching quick search to speed up common interactions with the Cloudflare dashboard. Our dashboard allows you to configure Cloudflare’s full suite of products and features, and quick search gives you a shortcut.
To get started, you can access the quick search tool from anywhere within the Cloudflare dashboard by clicking the magnifying glass button in the top navigation, or hitting Ctrl + K on Linux and Windows or ⌘ + K on Mac. (If you find yourself forgetting which key combination it is just remember that it’s ⌘ or Ctrl-K-wik.) From there, enter a search term and then select from the results shown below.
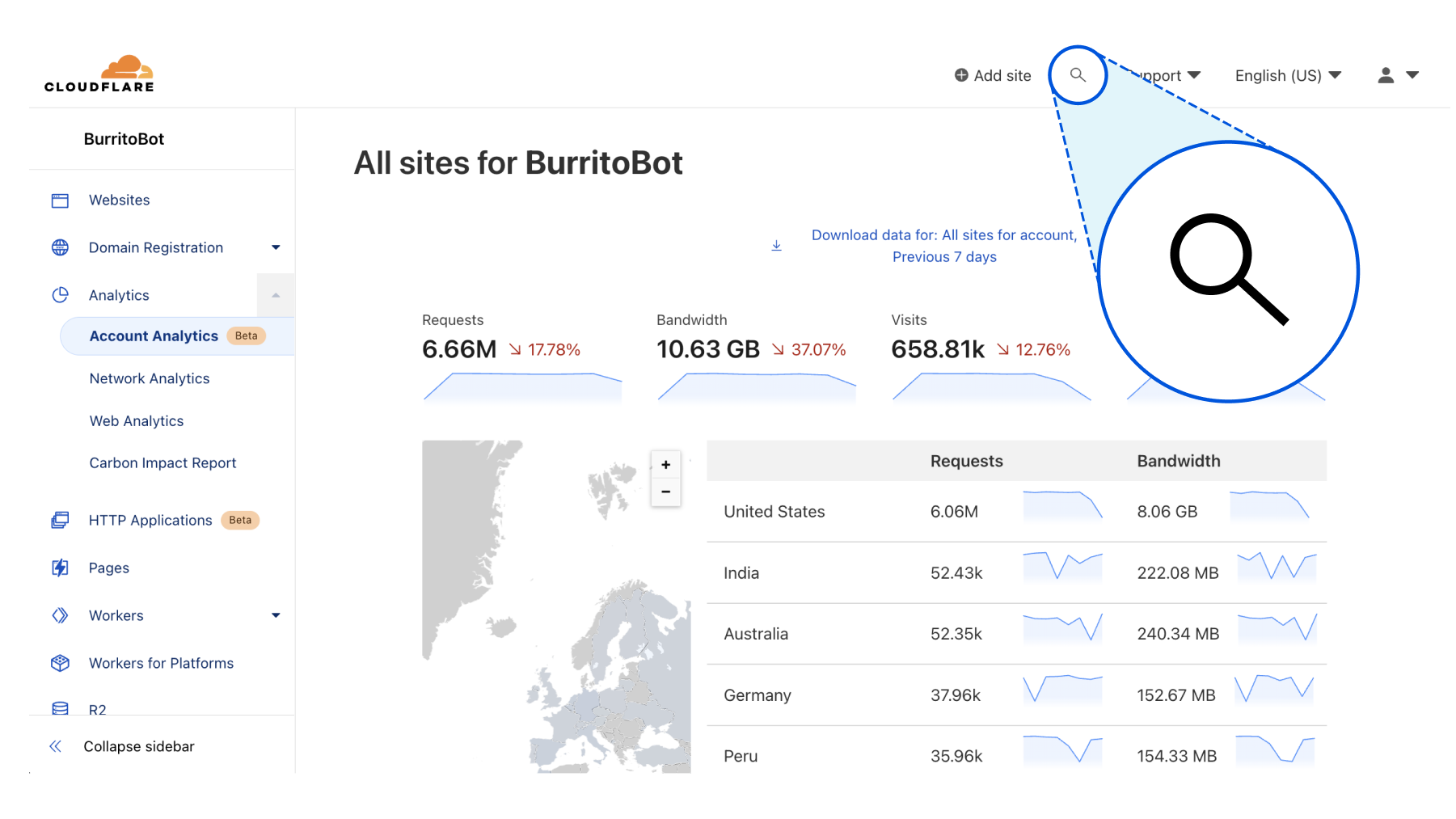
Current supported functionality
What functionality will Continue reading
Combining MLAG Clusters with VXLAN Fabric
In the previous MLAG Deep Dive blog posts we discussed the innards of a standalone MLAG cluster. Now let’s see what happens when we connect such a cluster to a VXLAN fabric – we’ll use our standard MLAG topology and add a VXLAN transport underlay to it with another switch connected to the other end of the underlay network.
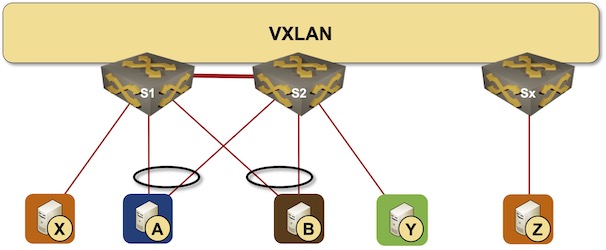
MLAG cluster connected to a VXLAN fabric
Combining MLAG Clusters with VXLAN Fabric
In the previous MLAG Deep Dive blog posts we discussed the innards of a standalone MLAG cluster. Now let’s see what happens when we connect such a cluster to a VXLAN fabric – we’ll use our standard MLAG topology and add a VXLAN transport underlay to it with another switch connected to the other end of the underlay network.
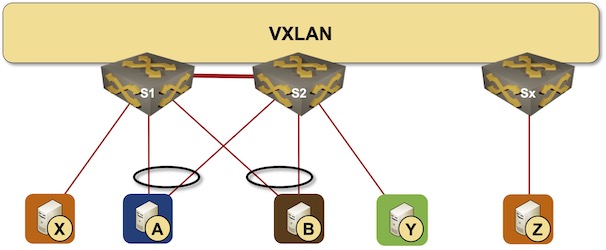
MLAG cluster connected to a VXLAN fabric
Revisiting BGP EVPN VXLAN to the hosts with SR Linux 22.6.3
Featuring Netlab 1.3.1 and FRR 8.3.1

At the beginning of this year I wrote about my SR Linux BGP EVPN adventures, with considerations around underlay and overlay design and the illustrious iBGP-over-eBGP approach. Some readers may have noticed a resemblance to the constellation of Ursa Major — the Big Bear: A reference to our friends at CloudBear, a recent SR Linux customer.
Fast forward to September 2022 and we now have SR Linux 22.6.3 with some features I have been waiting for, like (e)BGP Unnumbered. From my side, I have been working with the open source community to extend support for tools like Netlab (formerly Netsim-tools), Containerlab and FRR to enable sophisticated and advanced network topologies using truly open source tools and components.
New features and changes
The issue of running BGP to Linux hosts using FRR popped up in several discussions. Though technically possible, it can be challenging to configure, and there are many design variations with implications that aren’t always obvious. To enable simple experimentation and quick design iterations, I decided to help out by extending Netlab with VLAN, VXLAN and VRF support for FRR. I also made some changes to Continue reading
Service Mesh and Ingress In Kubernetes: Lesson 6 – Consul Service Mesh And App Installation – Video
Continuing with examples of installing a service mesh, this video walks through deploying the Consul mesh. Host Michael Levan brings his background in system administration, software development, and DevOps to this video series. He has Kubernetes experience as both a developer and infrastructure engineer. He’s also a consultant and Pluralsight author, and host of the […]
The post Service Mesh and Ingress In Kubernetes: Lesson 6 – Consul Service Mesh And App Installation – Video appeared first on Packet Pushers.