Join The Packet Pushers For A Live Stream With Gluware June 28, 2022
We're hosting the "Real World Enterprise Automation" live stream with sponsor Gluware on June 28, 2022. Gluware is a network automation vendor that's especially good at taking your existing, multi-vendor network and adding automation to it. We'd like it if you'd register to attend this hour-or-so event in real-time via https://packetpushers.net/live. Thanks!
The post Join The Packet Pushers For A Live Stream With Gluware June 28, 2022 appeared first on Packet Pushers.
Zero-trust for cloud-native workloads – part 2: Mitigating future Log4j incidents
Zero-trust for cloud-native workloads – part 2: Mitigating future Log4j incidents
In my previous blog, I introduced the brief history of zero trust, the core pillars of a zero-trust model, and how to build a zero-trust model for cloud-native workloads. In this blog, you will learn how Calico can help mitigate vulnerabilities such as the recent zero-day Log4j vulnerability with its zero-trust workload security approach.
Zero trust: a quick refresher
The starting point for building a zero-trust model is understanding your attack and protect surface. The outcome of designing your security plan should be eliminating the attack surface completely.
Enterprises are realizing that the best approach to mitigating breaches and protecting their sensitive assets from both internal and external threats is by applying the three principles of zero trust to their security plan. These three principles are:
- Always use least-privilege access
- Always authenticate and authorize before providing access
- Always assume breach
While stakeholders are busy creating design architectures, collecting asset information, and considering tools required to achieve their zero trust goals, there are also new challenges that some decision-makers should consider. As microservices are becoming the de facto standard for application developers, it has introduced new technologies and methodologies Continue reading
Early Hints update: How Cloudflare, Google, and Shopify are working together to build a faster Internet for everyone

A few months ago, we wrote a post focused on a product we were building that could vastly improve page load performance. That product, known as Early Hints, has seen wide adoption since that original post. In early benchmarking experiments with Early Hints, we saw performance improvements that were as high as 30%.
Now, with over 100,000 customers using Early Hints on Cloudflare, we are excited to talk about how much Early Hints have improved page loads for our customers in production, how customers can get the most out of Early Hints, and provide an update on the next iteration of Early Hints we’re building.
What Are Early Hints again?
As a reminder, the browser you’re using right now to read this page needed instructions for what to render and what resources (like images, fonts, and scripts) need to be fetched from somewhere else in order to complete the loading of this (or any given) web page. When you decide you want to see a page, your browser sends a request to a server and the instructions for what to load come from the server’s response. These responses are generally composed of a multitude of resources that tell the browser Continue reading
Kubernetes Unpacked 003: Beginner Lab Environments For Learning Kubernetes
Today's Kubernetes Unpacked podcast explores entry-level lab environments for IT professionals interested in learning Kubernetes, including suggestions for simple container-based apps you can run to get familiar with Kubernetes essentials.
The post Kubernetes Unpacked 003: Beginner Lab Environments For Learning Kubernetes appeared first on Packet Pushers.
Kubernetes Unpacked 003: Beginner Lab Environments For Learning Kubernetes
Today's Kubernetes Unpacked podcast explores entry-level lab environments for IT professionals interested in learning Kubernetes, including suggestions for simple container-based apps you can run to get familiar with Kubernetes essentials.A stronger bridge to Zero Trust
We know that migration to Zero Trust architecture won’t be an overnight process for most organizations, especially those with years of traditional hardware deployments and networks stitched together through M&A. But part of why we’re so excited about Cloudflare One is that it provides a bridge to Zero Trust for companies migrating from legacy network architectures.
Today, we’re doubling down on this — announcing more enhancements to the Cloudflare One platform that make a transition from legacy architecture to the Zero Trust network of the future easier than ever: new plumbing for more Cloudflare One on-ramps, expanded support for additional IPsec parameters, and easier on-ramps from your existing SD-WAN appliances.
Any on- or off-ramp: fully composable and interoperable
When we announced our vision for Cloudflare One, we emphasized the importance of allowing customers to connect to our network however they want — with hardware devices they’ve already deployed, with any carrier they already have in place, with existing technology standards like IPsec tunnels or more Zero Trust approaches like our lightweight application connector. In hundreds of customer conversations since that launch, we’ve heard you reiterate the importance of this flexibility. You need a platform that meets you where you Continue reading
Using Cloudflare Tunnel and Access with Postgres


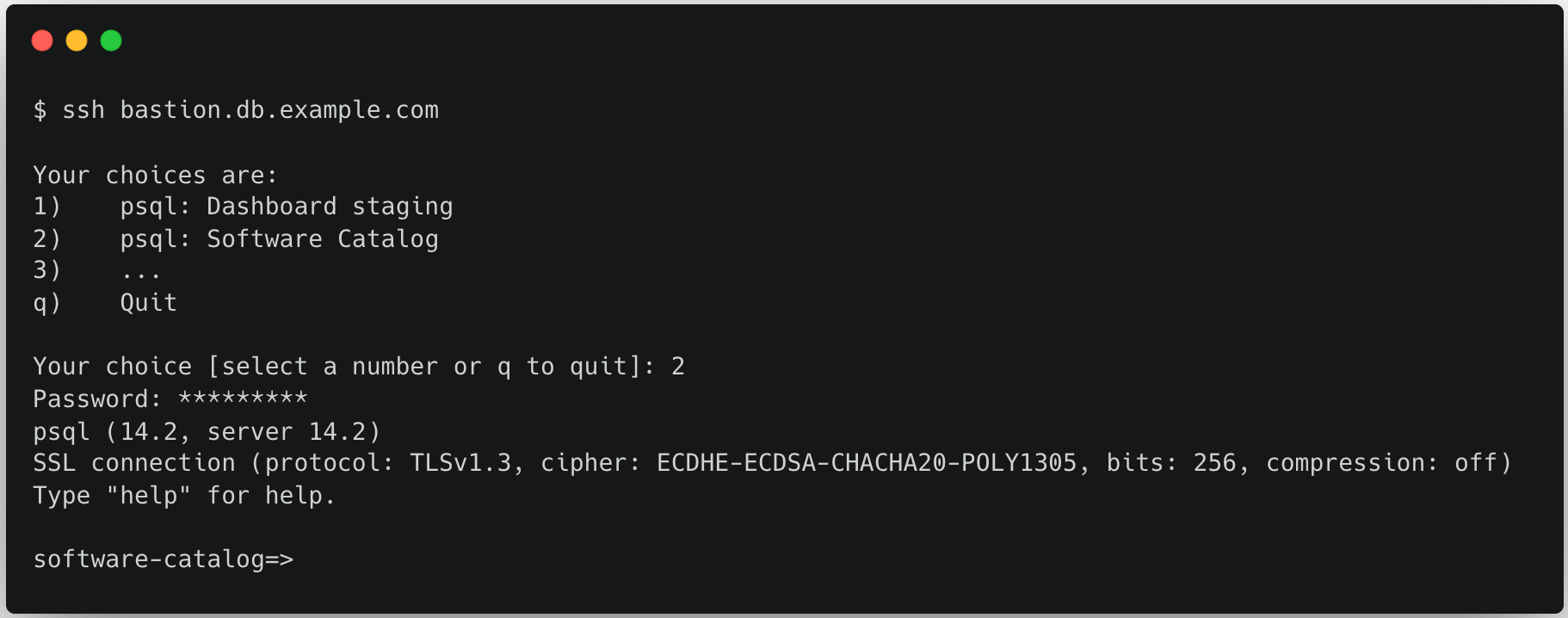
For a long time we used the traditional method of accessing internal database clusters by SSHing to a bastion host. Due to the overhead and limitations of maintaining the SSH configuration, we’ve moved to using Cloudflare Tunnels combined with Cloudflare Access to dramatically improve the user experience and onboarding times related to database access.
How we used to work
Internally we rely heavily on PostgreSQL to power many services at Cloudflare – including Stream, Images and the Cloudflare Dashboard itself. We run our Postgres clusters on our own hardware within our data centers, and they are not accessible to the public Internet, including employee laptops.
When an employee requires access to one of these databases – be it for staging environments, incident management, or supporting production services – an SSH user account is required. This SSH account has limited access on a bastion host, purely for querying databases within the data center.
The pain we experienced
Provisioning an SSH account to these bastion hosts requires submitting a pull request to our main Infrastructure-as-Code git repository. For engineers this is a cumbersome process, and for non-engineers it is either an unnecessary learning experience, or a burden to whomever they have to Continue reading
Cloudflare integrates with Microsoft Intune to give CISOs secure control across devices, applications, and corporate networks


Today, we are very excited to announce our new integration with Microsoft Endpoint Manager (Intune). This integration combines the power of Cloudflare’s expansive network and Zero Trust suite, with Endpoint Manager. Via our existing Intune integration, joint customers can check if a device management profile such as Intune is running on the device or not and grant access accordingly.
With this expanded integration, joint customers can identify, investigate, and remediate threats faster. The integration also includes the latest information from Microsoft Graph API which provides many added, real-time device posture assessments and enables organizations to verify users' device posture before granting access to internal or external applications.
"In today’s work-from-anywhere business culture, the risk of compromise has substantially increased as employees and their devices are continuously surrounded by a hostile threat environment outside the traditional castle-and-moat model. By expanding our integration with Cloudflare, we are making it easier for joint customers to strengthen their Zero Trust security posture across all endpoints and their entire corporate network."
– Dave Randall, Sr Program Manager, Microsoft Endpoint Manager
Before we get deep into how the integration works, let’s first recap Cloudflare’s Zero Trust Services.
Cloudflare Access and Gateway
Cloudflare Access determines if Continue reading
Cloudflare Gateway dedicated egress and egress policies
Today, we are highlighting how Cloudflare enables administrators to create security policies while using dedicated source IPs. With on-premise appliances like legacy VPNs, firewalls, and secure web gateways (SWGs), it has been convenient for organizations to rely on allowlist policies based on static source IPs. But these hardware appliances are hard to manage/scale, come with inherent vulnerabilities, and struggle to support globally distributed traffic from remote workers.
Throughout this week, we’ve written about how to transition away from these legacy tools towards Internet-native Zero Trust security offered by services like Cloudflare Gateway, our SWG. As a critical service natively integrated with the rest of our broader Zero Trust platform, Cloudflare Gateway also enables traffic filtering and routing for recursive DNS, Zero Trust network access, remote browser isolation, and inline CASB, among other functions.
Nevertheless, we recognize that administrators want to maintain the convenience of source IPs as organizations transition to cloud-based proxy services. In this blog, we describe our approach to offering dedicated IPs for egressing traffic and share some upcoming functionality to empower administrators with even greater control.
Cloudflare’s dedicated egress IPs
Source IPs are still a popular method of verifying that traffic originates from a known organization/user when Continue reading
MPLS to Zero Trust in 30 days
Employees returning to the office are experiencing that their corporate networks are much slower compared to what they’ve been using at home. It’s partly due to outdated line speeds, and also partly due to security requirements that force all traffic to get backhauled through centralized data centers. While 44% of the US currently has access to fiber-based broadband Internet with speeds reaching 1 Gbps, many MPLS sites are still on old 1.5 Mbps circuits. This is a reality check and a reminder that the current MPLS based networks are unable to support the shift from centralized applications in the datacenter to a distributed SaaS and hybrid multi-cloud world.
In this post, we are going to outline the steps required to take your network from MPLS to Zero Trust. But, before we do — a little about how we ended up in this situation.
Enterprise networks today
Over the past 10 years, most enterprise networks have evolved from perimeter hub and spoke networks into franken-networks as a means to solve connectivity and security issues. We have not had a chance to redesign them holistically for distributed application access. The band-aid and point solutions have only pushed the problems further down Continue reading
Announcing the Cloudflare One Partner Program

This post is also available in 简体中文, 日本語, Deutsch, Français.

Today marks the launch of the Cloudflare One Partner Program, a program built around our Zero Trust, Network as a Service and Cloud Email Security offerings. The program helps channel partners deliver on the promise of Zero Trust while monetizing this important architecture in tangible ways – with a comprehensive set of solutions, enablement and incentives. We are delighted to have such broad support for the program from IT Service companies, Distributors, Value Added Resellers, Managed Service Providers and other solution providers.
This represents both a new go-to-market channel for Cloudflare, and a new way for companies of all sizes to adopt Zero Trust solutions that have previously been difficult to procure, implement and support.
The Cloudflare One Partner Program consists of the following elements:
- New, fully cloud-native Cloudflare One product suites that help partners streamline and accelerate the design of holistic Zero Trust solutions that are easier to implement. The product suites include our Zero Trust products and Cloud Email Security products from our recent acquisition of Area 1 Security.
- All program elements are fully operationalized through Cloudflare's Distributors to make it easier to evaluate, quote Continue reading
How To Reference Nested Python Lists & Dictionaries
This post originally appeared in the Packet Pushers’ Ignition site on March 10, 2020. When getting data back from API queries in Python, the data is often delivered in JSON format. Python libraries such as requests will convert that JSON data structure into a Python-native data structure you can work with. That Python data structure […]
The post How To Reference Nested Python Lists & Dictionaries appeared first on Packet Pushers.
VLAN Module in netsim-tools Is Complete
One of the last things I did before starting the 2022 summer break was to push out the next release of netsim-tools.
It includes support for routed VLAN subinterfaces (needed to implement router-on-a-stick) and routed VLANs (needed to implement multi-hop VRF lite), completing the lengthy (and painful) development of the VLAN configuration module. Stefano Sasso added VLAN support for Mikrotik RouterOS and VyOS, and Jeroen van Bemmel completed VLAN implementation for Nokia SR Linux. Want to see VLANs on other platforms? Read the contributor guidelines and VLAN developer docs, and submit a PR.
I’ll be back in September with more blog posts, webinars, and cool netsim-tools features. In the meantime, automate everything, get away from work, turn off the Internet, and enjoy a few days in your favorite spot with your loved ones!
netlab VLAN Module Is Complete
One of the last things I did before starting the 2022 summer break was to push out the next netlab release.
It includes support for routed VLAN subinterfaces (needed to implement router-on-a-stick) and routed VLANs (needed to implement multi-hop VRF lite), completing the lengthy (and painful) development of the VLAN configuration module. Stefano Sasso added VLAN support for Mikrotik RouterOS and VyOS, and Jeroen van Bemmel completed VLAN implementation for Nokia SR Linux. Want to see VLANs on other platforms? Read the contributor guidelines and VLAN developer docs, and submit a PR.
I’ll be back in September with more blog posts, webinars, and cool netlab features. In the meantime, automate everything, get away from work, turn off the Internet, and enjoy a few days in your favorite spot with your loved ones!