netlab MPLS Support
netlab release 1.2.0 adds full-blown MPLS and MPLS/VPN support:
- VRF definitions and layer-3 VRFs
- VRF-aware OSPF, IS-IS and BGP
- Traditional MPLS with LDP (SR-MPLS was already available)
- BGP Labeled Unicast
- MPLS/VPN: VPNv4 and VPNv6 address family support
It’s never been easier to build full-blown MPLS/VPN labs ;)… if you’re OK with using Cisco IOS or Arista EOS. Please feel free to submit a PR to add support for other platforms.
You might want to start with the VRF tutorial to see how simple it is to define VRFs, and follow the installation guide to set up your lab – if you’re semi-fluent in Linux, the easiest option would be to run Arista cEOS.
Ipfixprobe Installation and Testing
Ipfixprobe is a project created by CESNET. CESNET is an association of universities and the Academy of Sciences of the Czech Republic that operates and develops a national e-infrastructure for science, research and education, including a computer network, computing grids, data repositories, collaborative environments and offering a wide range of services. Ipfixprobe, as its name […]Continue reading...
Ipfixprobe Installation and Testing
Ipfixprobe is a project created by CESNET. CESNET is an association of universities and the […]
The post Ipfixprobe Installation and Testing first appeared on Brezular's Blog.
Networking Field Day: Service Provider – Arista VPLS
During the first networking field day: service provider one of the big topics was EVPN versus VPLS. Arista has put a lot of work into their EVPN deployment and this has give then a ton of success in the data center. However, a large portion of the provider space, especially last mile providers, rely on VPLS heavily. This naturally led to discussion about Arista VPLS support.
I’m pleased to see that there is now basic support in EOS as of EOS 4.27.2F and more on the roadmap. Hopefully, we’ll see the off ramp, RFC8560, from VPLS to EVPN which was a hot button topic throughout the week.
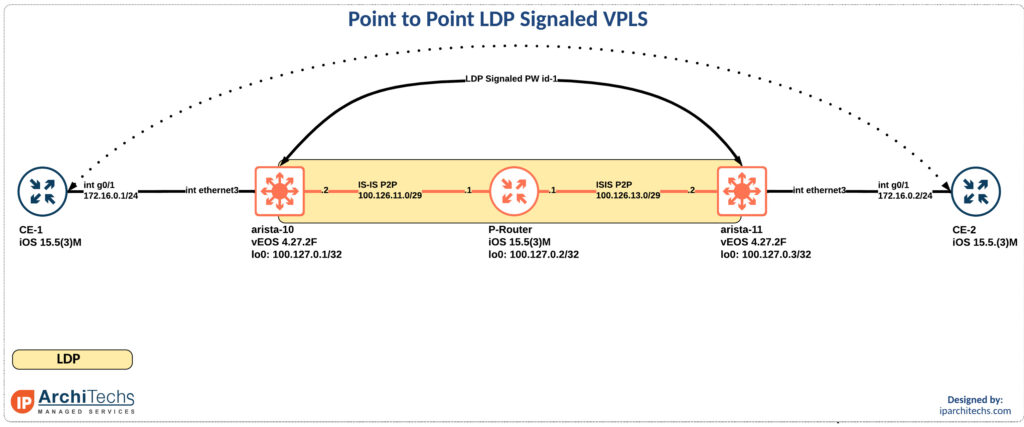
In the release notes for EOS 4.27.2F it calls our basic VPLS support. So I took a look. Reviewing the new 4.27.2F manual I found support for LDP PWs on RFC4447 which is virtual private wire support. This also appeared to be in EOS 4.26 but not earlier. I might have missed a different call out in the doc, if I did someone please point me in the right direction so I can update this post!
In the meantime lets review how this works:
mpls Continue readingWorth Reading: Higher Levels of Address Aggregation
Every now and then someone tells me how much better the global Internet would be if only we were using recursive layers (RINA) and hierarchical addresses. I always answer “that’s a business problem, not a technical one, and you cannot solve business problems by throwing technology at them”, but of course that has never persuaded anyone who hasn’t been running a large-enough business for long enough.
Geoff Huston is doing a much better job in the March 2022 ISP Column – read the Higher Levels of Address Aggregation, and if you still need more technical details, there’s 30+ pages of RFC 4984.
Worth Reading: Higher Levels of Address Aggregation
Every now and then someone tells me how much better the global Internet would be if only we were using recursive layers (RINA) and hierarchical addresses. I always answer “that’s a business problem, not a technical one, and you cannot solve business problems by throwing technology at them”, but of course that has never persuaded anyone who hasn’t been running a large-enough business for long enough.
Geoff Huston is doing a much better job in the March 2022 ISP Column – read the Higher Levels of Address Aggregation, and if you still need more technical details, there’s 30+ pages of RFC 4984.
What Cloudflare is Doing to Keep the Open Internet Flowing into Russia and Keep Attacks from Getting Out


Following Russia’s unjustified and tragic invasion of Ukraine in late February, the world has watched closely as Russian troops attempted to advance across Ukraine, only to be resisted and repelled by the Ukrainian people. Similarly, we’ve seen a significant amount of cyber attack activity in the region. We continue to work to protect an increasing number of Ukrainian government, media, financial, and nonprofit websites, and we protected the Ukrainian top level domain (.ua) to help keep Ukraine’s presence on the Internet operational.
At the same time, we’ve closely watched significant and unprecedented activity on the Internet in Russia. The Russian government has taken steps to tighten its control over both the technical components and the content of the Russian Internet. For their part, the people in Russia are doing something very different. They have been adopting tools to maintain access to the global Internet, and they have been seeking out non-Russian media sources. This blog post outlines what we’ve observed.
The Russian Government asserts control over the Internet
Over the last five years, the Russian government has taken steps to tighten its control of a sovereign Internet within Russia’s borders, including laws requiring Russian ISPs to install equipment allowing Continue reading
OSPF Area Types
OSPF Areas are used for OSPF Scalability. In this post, we will have a look at many different topics about OSPF Area Types, their usage, limitations, different router types, and so on.
In OSPF, we have in general two different Area Types. OSPF Backbone Area and OSPF Non-Backbone Area.
There are many different OSPF Non-Backbone Area types and we will cover each one of them, their use case, limitations, and benefits in this post.
OSPF Area 0 – OSPF Backbone Area
First of all, Let’s start with Area 0.
It is known as the Backbone area in OSPF and if there are many different areas, non-backbone areas can communicate with each other through OSPF Area 0.
Let’s use the below topology for the rest of the OSPF Area Types discussion.

Figure – OSPF Area Types
In the above topology, OSPF Area 0, which is OSPF Backbone Area, physically connects different OSPF Non-Backbone Areas.
OSPF Router Types in OSPF Area 0 are known as Internal Backbone Routers. We don’t have OSPF LSA restrictions when it comes to OSPF Area 0, all the LSAs are allowed in this OSPF Area, except Type 4 and Type 7. Type 4 LSA is used for Continue reading
Failed the CCIE lab. Now what?
This is a blog post that could’ve and perhaps should’ve been written many years ago. Knowing what happened in 2008 might only help very few with their CCIE journeys today. But on that summer afternoon, I made up my mind when the plane made a noisy landing in Tokyo, where many passengers had masks on, […]
The post Failed the CCIE lab. Now what? appeared first on Packet Pushers.
Introduction to Pulumi for Infrastructure as Code Deployments
Introduction I’ve been itching to introduce Pulumi to you all for the longest time. I heard about Pulumi in the mid-point of 2021. At the time I was going through Microsoft AZ-700 studies and figured it would be fun to double up the learning and get my hands on Pulumi. Long story short, I really […]
The post Introduction to Pulumi for Infrastructure as Code Deployments appeared first on Packet Pushers.
Worth Reading: Career Advice I’d Give to Younger Me
You MUST read the next masterpiece coming from Ethan Banks: Career Advice I’d Give To 20, 30 and 40-Something Year Old Me. I found this bit particularly relevant:
Your life is at least half over. Stop wasting time doing things other people think is important.
If only Ethan would have told me that wisdom ten years ago.
Worth Reading: Career Advice I’d Give to Younger Me
You MUST read the next masterpiece coming from Ethan Banks: Career Advice I’d Give To 20, 30 and 40-Something Year Old Me. I found this bit particularly relevant:
Your life is at least half over. Stop wasting time doing things other people think are important.
If only Ethan would have told me that wisdom ten years ago.
VPP Configuration – Part2
About this series
I use VPP - Vector Packet Processor - extensively at IPng Networks. Earlier this year, the VPP community merged the Linux Control Plane plugin. I wrote about its deployment to both regular servers like the Supermicro routers that run on our AS8298, as well as virtual machines running in KVM/Qemu.
Now that I’ve been running VPP in production for about half a year, I can’t help but notice one specific
drawback: VPP is a programmable dataplane, and by design it does not include any configuration or
controlplane management stack. It’s meant to be integrated into a full stack by operators. For end-users,
this unfortunately means that typing on the CLI won’t persist any configuration, and if VPP is restarted,
it will not pick up where it left off. There’s one developer convenience in the form of the exec
command-line (and startup.conf!) option, which will read a file and apply the contents to the CLI line
by line. However, if any typo is made in the file, processing immediately stops. It’s meant as a convenience
for VPP developers, and is certainly not a useful configuration method for all but the simplest topologies.
Luckily, VPP comes Continue reading
Moonlander Keyboard
For the past year and a half or so, I have been using the Keycaps I didn't like they keycaps that shipped with the board (although they were fine). I swapped them out for these retro gaming style XDA profile keycaps. XDA profile keys are all the same height and shape. Key Switches I...continue reading
Heavy Networking 624: Solving Network Problems With Opmantek’s NMIS (Sponsored)
On today's sponsored Heavy Networking we speak with Opmantek, a FirstWave company. Opmantek's NMIS is a suite of network monitoring applications for managing fault, performance, configuration, compliance and automation. It supports multi-vendor, multi-tenant and multi-server solutions. We discuss the latest features and real-world use cases.
The post Heavy Networking 624: Solving Network Problems With Opmantek’s NMIS (Sponsored) appeared first on Packet Pushers.
Heavy Networking 624: Solving Network Problems With Opmantek’s NMIS (Sponsored)
On today's sponsored Heavy Networking we speak with Opmantek, a FirstWave company. Opmantek's NMIS is a suite of network monitoring applications for managing fault, performance, configuration, compliance and automation. It supports multi-vendor, multi-tenant and multi-server solutions. We discuss the latest features and real-world use cases.Fast Friday Thoughts on Leadership

I’m once more taking part in the BSA Wood Badge leadership course for my local council. I enjoy the opportunity to hone my skills when it comes to leading others and teaching them how to train their own leaders. A lot of my content around coaching, mentoring, and even imposter syndrome has come from the lessons I’ve learned during Wood Badge. It sounds crazy but I enjoy taking vacation time to staff something that looks like work because it feels amazing!
A few random thoughts from the week:
- You need a sense of urgency in everything you do. You may not know exactly what’s coming or how to adjust for what needs to be done but you need to be moving with purpose to get it done. Not only does that help you with your vision to make things happen but it encourages others to do the same.
- Team building happens when you’re not focused entirely on the goal. It doesn’t take much for your group to come together but it can only happen when they aren’t charging toward the finish line. Remember that taking a few moments here and there to reinforce the group dynamic can do a lot Continue reading
The end of the road for Cloudflare CAPTCHAs


There is no point in rehashing the fact that CAPTCHA provides a terrible user experience. It's been discussed in detail before on this blog, and countless times elsewhere. One of the creators of the CAPTCHA has publicly lamented that he “unwittingly created a system that was frittering away, in ten-second increments, millions of hours of a most precious resource: human brain cycles.” We don’t like them, and you don’t like them.
So we decided we’re going to stop using CAPTCHAs. Using an iterative platform approach, we have already reduced the number of CAPTCHAs we choose to serve by 91% over the past year.
Before we talk about how we did it, and how you can help, let's first start with a simple question.
Why in the world is CAPTCHA still used anyway?
If everyone agrees CAPTCHA is so bad, if there have been calls to get rid of it for 15 years, if the creator regrets creating it, why is it still widely used?
The frustrating truth is that CAPTCHA remains an effective tool for differentiating real human users from bots despite the existence of CAPTCHA-solving services. Of course, this comes with a huge trade off in terms Continue reading