As 5G Connections Grow, Automation will be Mission-Critical
Operators need to rapidly mature and scale software if they are to maximize the speed and agility of 5G deployment and operations.More: Hardware Differences between Routers and Switches
Aaron Glenn sent me his thoughts on hardware differences between routers and switches based on the last paragraph of Dmytro Shypovalov’s views on the topic
To conclude, what is the difference between routers and switches in my opinion? I have absolutely no idea.
More: Hardware Differences between Routers and Switches
Aaron Glenn sent me his thoughts on hardware differences between routers and switches based on the last paragraph of Dmytro Shypovalov’s views on the topic
To conclude, what is the difference between routers and switches in my opinion? I have absolutely no idea.
What to Expect from Network as a Service (NaaS) Technology
NaaS is gaining momentum. Is your organization going to jump onboard?Tech Bytes: Managing SaaS Risks With Smarter, Cloud-Delivered Security (Sponsored)
On today’s Tech Bytes podcast, sponsored by Palo Alto Networks, we’re going to talk about how a SASE architecture and a next-generation CASB, or Cloud Access Security Broker, can help security teams manage SaaS risks.
The post Tech Bytes: Managing SaaS Risks With Smarter, Cloud-Delivered Security (Sponsored) appeared first on Packet Pushers.
Tech Bytes: Managing SaaS Risks With Smarter, Cloud-Delivered Security (Sponsored)
On today’s Tech Bytes podcast, sponsored by Palo Alto Networks, we’re going to talk about how a SASE architecture and a next-generation CASB, or Cloud Access Security Broker, can help security teams manage SaaS risks.Network Break 366: Microsoft Spends $68.7 Billion On Games; Wi-Fi 7 On The Horizon
Take a Network Break! This week we examine the drivers behind Microsoft's proposed $68.7 billion acquisition of gaming company Activision Blizzard, Juniper integrates its SD-WAN portfolio with Mist Cloud, and Wi-Fi 7 emerges on the horizon. Cisco announces a new Catalyst switch for industrial use cases, Telia Carrier rebrands, and JP Morgan Chase discloses tidbits about its IT strategy.
The post Network Break 366: Microsoft Spends $68.7 Billion On Games; Wi-Fi 7 On The Horizon appeared first on Packet Pushers.
Network Break 366: Microsoft Spends $68.7 Billion On Games; Wi-Fi 7 On The Horizon
Take a Network Break! This week we examine the drivers behind Microsoft's proposed $68.7 billion acquisition of gaming company Activision Blizzard, Juniper integrates its SD-WAN portfolio with Mist Cloud, and Wi-Fi 7 emerges on the horizon. Cisco announces a new Catalyst switch for industrial use cases, Telia Carrier rebrands, and JP Morgan Chase discloses tidbits about its IT strategy.Introducing New NSX Upgrade Capabilities for NSX-T 3.2
We’re introducing new capabilities to help our customers prepare for upgrading to the latest releases — now available with NSX-T Data Center 3.2.0.1.
To ensure that existing NSX deployments can be successfully upgraded to NSX-T Data Center 3.2.x, we have provided an NSX Upgrade Evaluation Tool that operates non-intrusively as a separate downloadable tool to check the health and readiness of your NSX Managers prior to upgrade. Using NSX Upgrade Evaluation Tool can help avoid potential upgrade failures and save time by avoiding a rollback from a failed upgrade.
Customers upgrading to NSX-T 3.2.x are strongly encouraged to review the Upgrade Checklist and run the NSX Upgrade Evaluation Tool before starting the upgrade process.
In what follows, we’ll go over the details of the NSX Upgrade Evaluation Tool:
- How the tool works
- When to use the tool
- What the tool can and cannot do
- How to use the tool
How the NSX Upgrade Evaluation Tool Works

The main component of the NSX Upgrade Evaluation Tool is the database where a copy of NSX objects will be stored. The tool starts by making a secure copy of the database from an existing NSX Manager Continue reading
Burkina Faso experiencing second major Internet disruption this year

The early hours of Sunday, January 23, 2022, started in Burkina Faso with an Internet outage or shutdown. Heavy gunfire in an army mutiny could be related to the outage according to the New York Times (“mobile Internet services were shut down”). As of today, there are three countries affected by major Internet disruptions — Tonga and Yemen are the others.
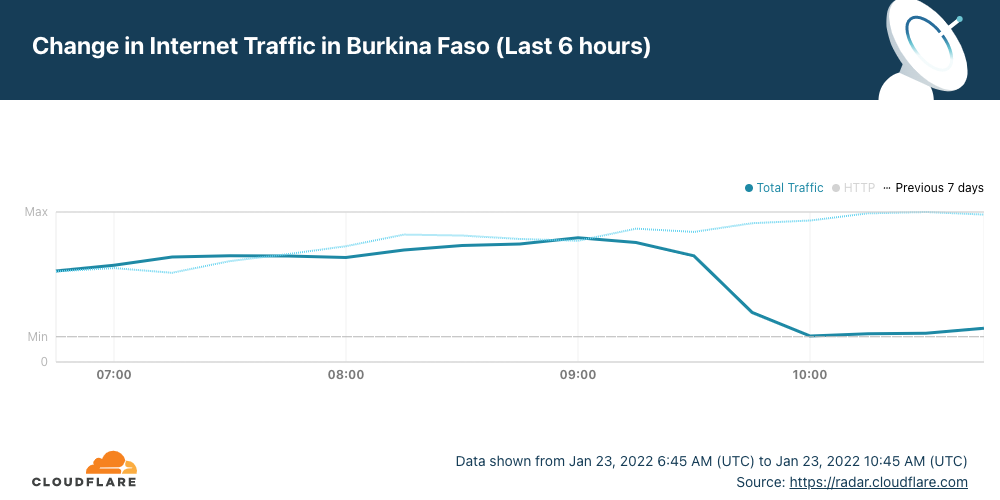
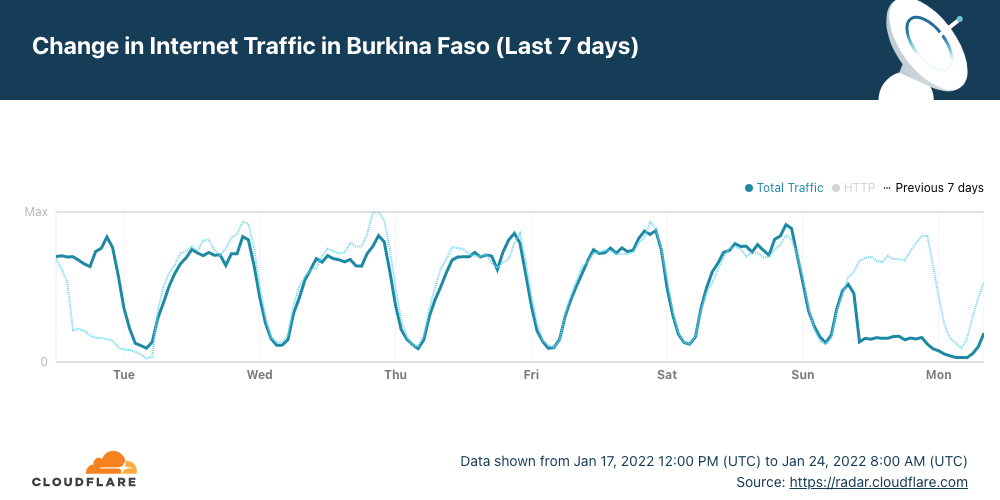
Cloudflare Radar shows that Internet traffic dropped significantly in the West African country after ~09:15 UTC (the same in local time) and remains low more than 24 hours later. Burkina Faso also had a mobile Internet shutdown on January 10, 2022, and another we reported in late November 2021.
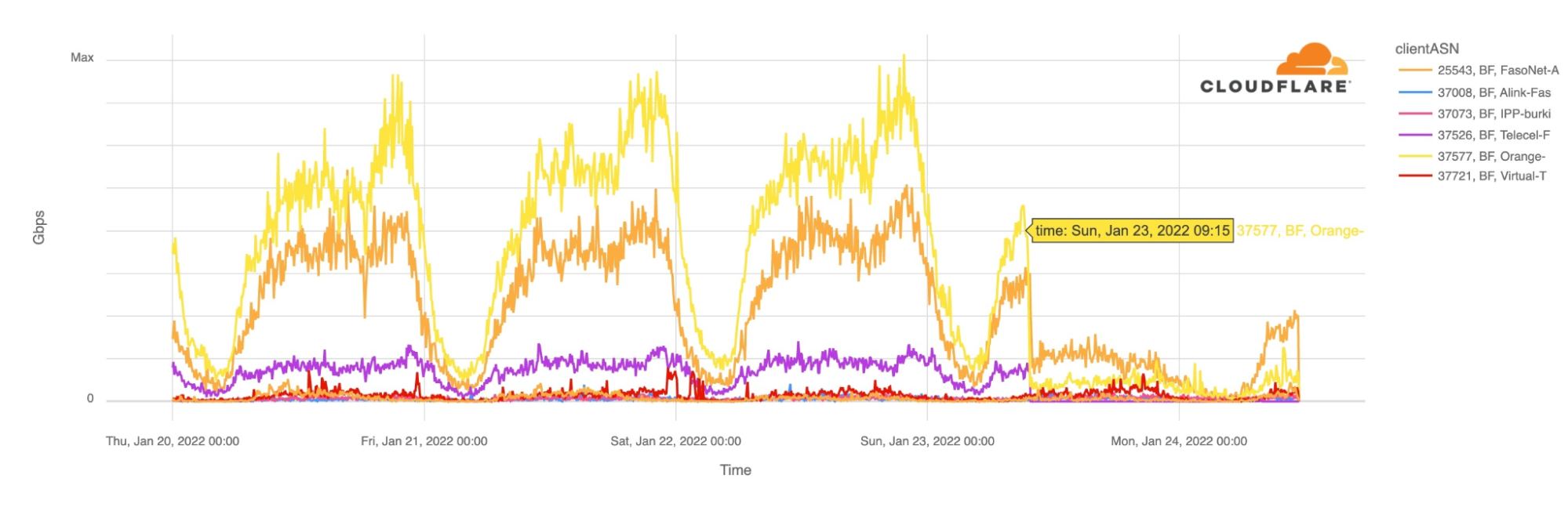
The main ISPs from Burkina Faso were affected. The two leading Internet Service Providers Orange and FasoNet lost Internet traffic after 09:15 UTC, but also Telecel Faso, as the next chart shows. This morning, at around 10:00 UTC there was some traffic from FasoNet but less than half of what we saw at the same time in preceding days.
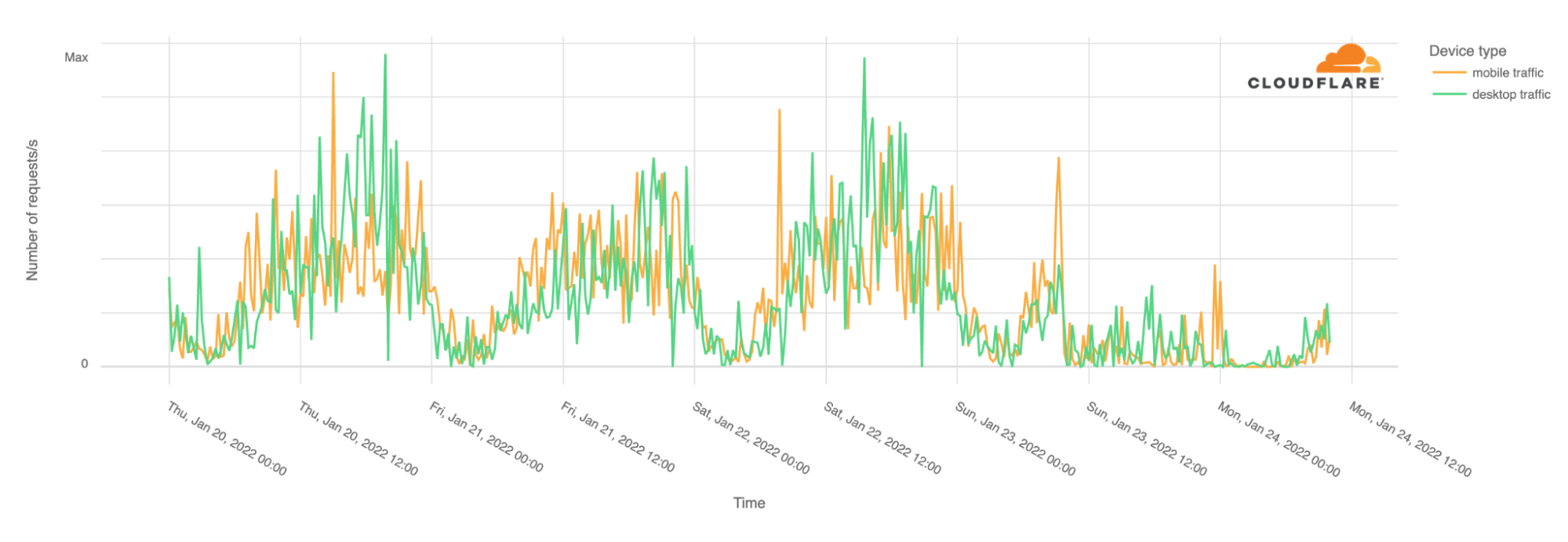
It’s not only mobile traffic that is affected. Desktop traffic is also impacted. In Burkina Faso, our data shows that mobile devices normally represent 70% of Internet traffic.
With the Burkina Continue reading
Sample Lab: RSVP TE on Junos
It’s amazing how creative networking engineers become once they have the basic tools to get the job done a bit quicker. Last week Pete Crocker published the largest topology I’ve seen built with netsim-tools so far: a 13-router lab running RSVP TE to transport IP traffic between external autonomous systems1.

Lab topology
Sample Lab: RSVP TE on Junos
It’s amazing how creative networking engineers become once they have the basic tools to get the job done a bit quicker. Last week Pete Crocker published the largest topology I’ve seen built with netlab so far: a 13-router lab running RSVP TE to transport IP traffic between external autonomous systems1.
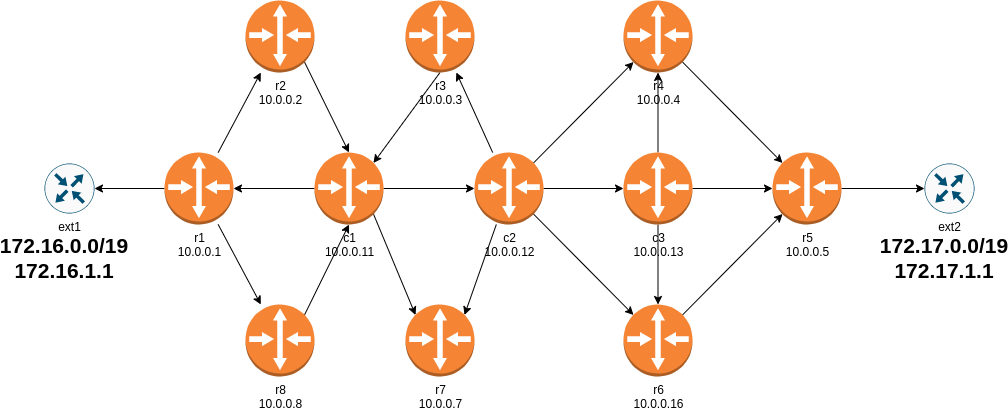
Lab topology