Video: Machine Learning Techniques
After Javier Antich walked us through the AI/ML hype and described the basics of machine learning it was time for a more thorough look at:
- Machine learning techniques, including unsupervised learning (clustering and anomaly detection), supervised learning (regression, classification and generation) and reinforced learning
- Machine learning implementations, including neural networks, deep neural networks and convolutional neural networks.
Juniper Networks’ SD-WAN Can Now Be Operated Via Mist Cloud
Juniper Networks’ SD-WAN appliances and software can now be fully managed from Juniper’s Mist Cloud. It’s part of Juniper’s larger goal to Mist-ify its LAN and WAN portfolio. Juniper’s SD-WAN product is based on the Session Smart Routers (SSRs) from Juniper’s acquisition of 128 Technology. Customers can now use Mist Cloud to onboard SSR hardware, […]
The post Juniper Networks’ SD-WAN Can Now Be Operated Via Mist Cloud appeared first on Packet Pushers.
Hedge 115: Mat Duggan and DevOps

Devops is the new normal—but, far too often, operations folks (like network engineers) are expected to become full-on developers, and developers are expected to understand operations in ways they never had to before. Mat Duggan joins Tom Ammon and Russ White to discuss why operations is not development IT
HS015: Targeting in IT Marketing – Who and When
With so much money allocated to marketing teams, why do customers find it disagreeable and unpleasant to be a victim of their activities ?
The post HS015: Targeting in IT Marketing – Who and When appeared first on Packet Pushers.
HS015: Targeting in IT Marketing – Who and When
With so much money allocated to marketing teams, why do customers find it disagreeable and unpleasant to be a victim of their activities ?A Safety Inquiry on 5G Deployments at U.S. Airports Balloons
The DOT, wireless carriers, the FAA, the aviation industry, and Biden Administration are all now involved in resolving a complex situation that airline CEOs claim could worsen air travel operations chaos beyond continuing Covid cancellations level.Day Two Cloud 130: Getting Started With OpenShift For Kubernetes Orchestration
On today's Day Two Cloud we have a career conversation with Angela Andrews, a Solution Architect at Red Hat. Angela provides an introduction to OpenShift, a cloud-based offering for running and orchestrating Kubernetes containers in public clouds and on premises from Red Hat. We also discuss how to integrate communication skills with technical knowledge, the role of a Solution Architect, how to stay on top of new and changing technologies, and more.
The post Day Two Cloud 130: Getting Started With OpenShift For Kubernetes Orchestration appeared first on Packet Pushers.
Day Two Cloud 130: Getting Started With OpenShift For Kubernetes Orchestration
On today's Day Two Cloud we have a career conversation with Angela Andrews, a Solution Architect at Red Hat. Angela provides an introduction to OpenShift, a cloud-based offering for running and orchestrating Kubernetes containers in public clouds and on premises from Red Hat. We also discuss how to integrate communication skills with technical knowledge, the role of a Solution Architect, how to stay on top of new and changing technologies, and more.VMware Network Automation with NSX-T 3.2 and vRealize Automation
VMware Network Automation combines the modern microservices architecture of vRealize with VMware NSX network virtualization to enable rapid application rollout. The solution automates VMware NSX via VMware vRealize Automation to deliver complete workload lifecycle automation through networking, compute, and security services that make it simple to template, provision, and update complete environments. That, in turn, enables businesses to accelerate application delivery and drive overall agility.

The latest iterations of vRealize Automation native integration with NSX-T features include multiple new capabilities, such as support for NSX-T Federation, distributed firewall configurations from NSX-T, a shared gateway across on-demand networks, and many others.
In this post, we will provide an overview of the feature-set available with this native integration. The post doesn’t aim to be exhaustive, so don’t hesitate to look at the vRealize Automation documentation for more details.
Setting up the Environment
The native integration allows for consumption of NSX-T constructs from vRealize Automation after a simple configuration.
The goal is for the cloud admin to be able to offer users a self-service catalog, through Service Broker that enables the deployment of complex topologies with consistent governance policies across the cloud — all while abstracting the underlying infrastructure and its complexity from Continue reading
Tonga’s likely lengthy Internet outage

2022 only has 19 days of existence but so far this January, there have already been four significant Internet disruptions:
1. An Internet outage in The Gambia because of a cable problem.
2. An Internet shutdown in Kazakhstan because of unrest.
3. A mobile Internet shutdown in Burkina Faso because of a coup plot.
4. An Internet outage in Tonga because of a volcanic eruption.
The latest Internet outage, in the South Pacific country of Tonga (with 169 islands), is still ongoing. It started with the large eruption of Hunga Tonga–Hunga Haʻapai, an uninhabited volcanic island of the Tongan archipelago on Friday, January 14, 2022. The next day, Cloudflare Radar shows that the Internet outage started at around 03:00 UTC (16:00 local time) — Saturday, January 15, 2022 — and is ongoing for more than four days. Tonga’s 105,000 residents are almost entirely unreachable, according to the BBC.
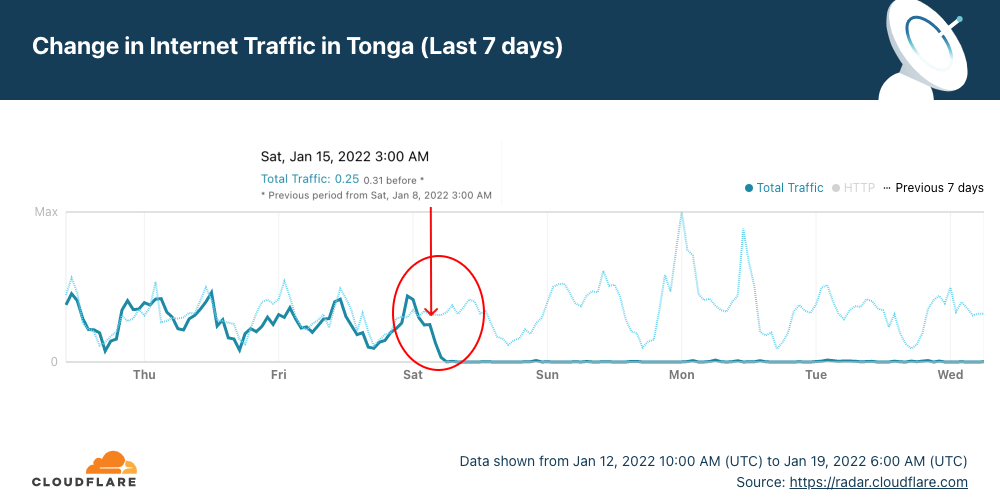
When we focus on the number of requests by ASN, the country’s main ISPs Digicel and Kalianet started to lose traffic after 03:00 UTC and by 05:30 UTC January 15, 2022, Cloudflare saw close to no traffic at all from them, as shown in the graph below.
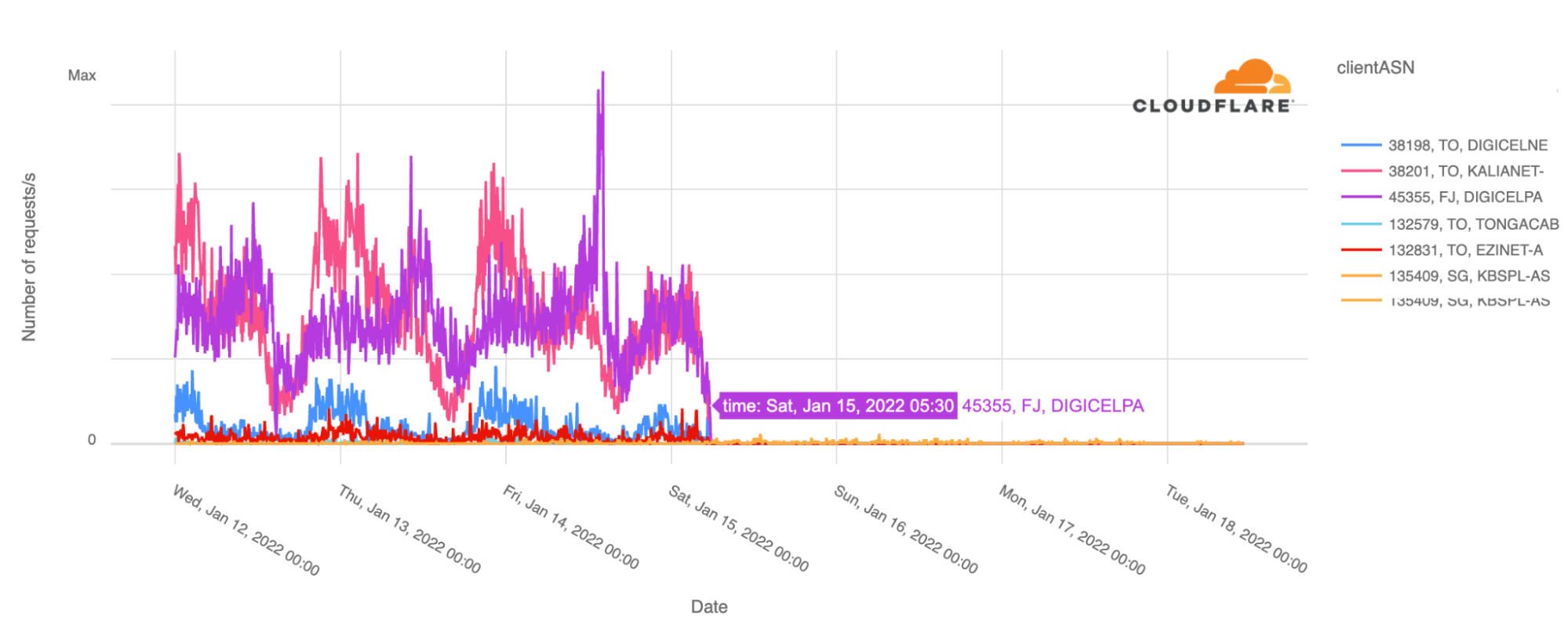
Looking at the BGP Continue reading
Introducing netsim-tools Plugins
Remember the BGP anycast lab I described in December 2021? In that blog post I briefly mentioned a problem of extraneous IBGP sessions and promised to address it at a later date. Let’s see how we can fix that with netsim-tools plugin.
We always knew that it’s impossible to implement every nerd knob someone would like to have when building their labs, and extending the tool with Python plugins seemed like the only sane way to go. We added custom plugins to netsim-tools release 1.0.6, but I didn’t want to write about them because we had to optimize the internal data structures first.