Zambia Needs the Internet More than Ever

My country, Zambia, has more than 18 million people. Our new Internet Society chapter wants all of them to be online. Why? Because we need the Internet now more than ever. Globally, UNICEF and the International Telecommunication Union (ITU) estimate that 1.3 billion children between the ages of 3 and 17 – or two thirds […]
The post Zambia Needs the Internet More than Ever appeared first on Internet Society.
Announcing WARP for Linux and Proxy Mode


Last October we released WARP for Desktop, bringing a safer and faster way to use the Internet to billions of devices for free. At the same time, we gave our enterprise customers the ability to use WARP with Cloudflare for Teams. By routing all an enterprise's traffic from devices anywhere on the planet through WARP, we’ve been able to seamlessly power advanced capabilities such as Secure Web Gateway and Browser Isolation and, in the future, our Data Loss Prevention platforms.
Today, we are excited to announce Cloudflare WARP for Linux and, across all desktop platforms, the ability to use WARP with single applications instead of your entire device.
What is WARP?
WARP was built on the philosophy that even people who don’t know what “VPN” stands for should be able to still easily get the protection a VPN offers. It was also built for those of us who are unfortunately all too familiar with traditional corporate VPNs, and need an innovative, seamless solution to meet the challenges of an always-connected world.
Enter our own WireGuard implementation called BoringTun.
The WARP application uses BoringTun to encrypt traffic from your device and send it directly to Cloudflare’s edge, ensuring that no Continue reading
Questions about BGP in the Data Center (with a Whiff of SRv6)
Henk Smit left numerous questions in a comment referring to the Rethinking BGP in the Data Center presentation by Russ White:
In Russ White’s presentation, he listed a few requirements to compare BGP, IS-IS and OSPF. Prefix distribution, filtering, TE, tagging, vendor-support, autoconfig and topology visibility. The one thing I was missing was: scalability.
I noticed the same thing. We kept hearing how BGP scales better than link-state protocols (no doubt about that) and how you couldn’t possibly build a large data center fabric with a link-state protocol… and yet this aspect wasn’t even mentioned.
Questions about BGP in the Data Center (with a Whiff of SRv6)
Henk Smit left numerous questions in a comment referring to the Rethinking BGP in the Data Center presentation by Russ White:
In Russ White’s presentation, he listed a few requirements to compare BGP, IS-IS and OSPF. Prefix distribution, filtering, TE, tagging, vendor-support, autoconfig and topology visibility. The one thing I was missing was: scalability.
I noticed the same thing. We kept hearing how BGP scales better than link-state protocols (no doubt about that) and how you couldn’t possibly build a large data center fabric with a link-state protocol… and yet this aspect wasn’t even mentioned.
DNSSEC with EdDSA
The world of cryptographic algorithms is one that constantly evolves and increasing key sizes in the venerable RSA crypto algorithm is a source of concern for DNSSEC. The response to this escalation in key sizes is to look at alternative forms of public-key algorithms which have a higher cryptographic “density”, using elliptic curve cryptography. Here we will look at the level of Internet support provided for a recent crypto offering, the Edwards curve algorithm Ed25519.The Hedge 88: Todd Palino and Getting Things Done
I often feel like I’m “behind” on what I need to get done. Being a bit metacognitive, however, I often find this feeling is more related to not organizing things well, which means I often feel like I have so much to do “right now” that I just don’t know what to do next—hence “processor thrashing on process scheduler.” Todd Palino joins this episode of the Hedge to talk about the “Getting Things Done” technique (or system) of, well … getting things done.
Second Round of Grant Funding Awarded to Researchers Studying the Future of the Internet

From the environment to the economy, the Internet is reshaping several sectors of our society. What might future patterns of disruption look like? How will these changes affect all of us? At the Internet Society Foundation, we believe the answers to these questions and many others can be found in research. That’s why in September […]
The post Second Round of Grant Funding Awarded to Researchers Studying the Future of the Internet appeared first on Internet Society.
Day Two Cloud 102: Edge Cloud Isn’t Magic
Today we're talking Edge Cloud. Guest Alex Marcham has written a book on the subject and we'll get his take on edge infrastructure, what edge cloud is all about, real-world use cases, and how it differs from typical colo facilities or centralized public cloud data centers. We also look at requirements for edge deployments including networking and 5G, and the workloads driving edge infrastructure.
The post Day Two Cloud 102: Edge Cloud Isn’t Magic appeared first on Packet Pushers.
Day Two Cloud 102: Edge Cloud Isn’t Magic
Today we're talking Edge Cloud. Guest Alex Marcham has written a book on the subject and we'll get his take on edge infrastructure, what edge cloud is all about, real-world use cases, and how it differs from typical colo facilities or centralized public cloud data centers. We also look at requirements for edge deployments including networking and 5G, and the workloads driving edge infrastructure.Simplifying Device Provisioning On Private Mobile Networks
Embedded SIMs promise to radically simplify enterprise migration to 4G/5G private mobile networks.Building Waiting Room on Workers and Durable Objects
In January, we announced the Cloudflare Waiting Room, which has been available to select customers through Project Fair Shot to help COVID-19 vaccination web applications handle demand. Back then, we mentioned that our system was built on top of Cloudflare Workers and the then brand new Durable Objects. In the coming days, we are making Waiting Room available to customers on our Business and Enterprise plans. As we are expanding availability, we are taking this opportunity to share how we came up with this design.
What does the Waiting Room do?
You may have seen lines of people queueing in front of stores or other buildings during sales for a new sneaker or phone. That is because stores have restrictions on how many people can be inside at the same time. Every store has its own limit based on the size of the building and other factors. If more people want to get inside than the store can hold, there will be too many people in the store.
The same situation applies to web applications. When you build a web application, you have to budget for the infrastructure to run it. You make that decision according to how many Continue reading
Deploying Plug-and-Pray Software in Large-Scale Networks
One of my readers sent me a sad story describing how Chromium service discovery broke a large multicast-enabled network.
The last couple of weeks found me helping a customer trying to find and resolve a very hard to find “network performance” issue. In the end it turned out to be a combination of ill conceived application nonsense and a setup with a too large blast radius/failure domain/fate sharing. The latter most probably based upon very valid decisions in the past (business needs, uniformity of configuration and management).
Deploying Plug-and-Pray Software in Large-Scale Networks
One of my readers sent me a sad story describing how Chromium service discovery broke a large multicast-enabled network.
The last couple of weeks found me helping a customer trying to find and resolve a very hard to find “network performance” issue. In the end it turned out to be a combination of ill conceived application nonsense and a setup with a too large blast radius/failure domain/fate sharing. The latter most probably based upon very valid decisions in the past (business needs, uniformity of configuration and management).
Post-Pandemic Healthcare Innovations
They say there is always a silver lining in every bad thing that happens. Well for some people 2020 was the worst year of their lives. People lost their loved ones, lost their entire businesses and a lot of bad things happen. However even in such drastic times there was silver lining for the future. The pandemic has forced scientists and doctors to come up with healthcare innovations that would help the work way beyond the time of the pandemic. There were many healthcare innovations that were discussed before the pandemic however they were only put to use in urgency once the pandemic hit.
Let’s take a look at the healthcare innovations that we may keep seeing in the post pandemic times.
Innovative Mindset
In order to keep the innovations coming, the doctors, scientists and researchers should keep an innovative mindset. Without the right mindset you will never be able to carry on with the innovations after the pandemic. So in order to keep the innovations coming after the pandemic, having an innovative mindset is very important.
Remote Communication
The pandemic has shown us that remote communication can be very helpful. People used to believe that face to face communication Continue reading
Telecom APIs: A Key IT Tool to Scale Services and Improve Customer Experiences
Businesses are actively using Telecom APIs to support their distributed workforces, boost customer service and retention, and enable greater scalability of communication capabilities.Enable secure access to applications with Cloudflare WAF and Azure Active Directory


Cloudflare and Microsoft Azure Active Directory have partnered to provide an integration specifically for web applications using Azure Active Directory B2C. From today, customers using both services can follow the simple integration steps to protect B2C applications with Cloudflare’s Web Application Firewall (WAF) on any custom domain. Microsoft has detailed this integration as well.
Cloudflare Web Application Firewall
The Web Application Firewall (WAF) is a core component of the Cloudflare platform and is designed to keep any web application safe. It blocks more than 70 billion cyber threats per day. That is 810,000 threats blocked every second.
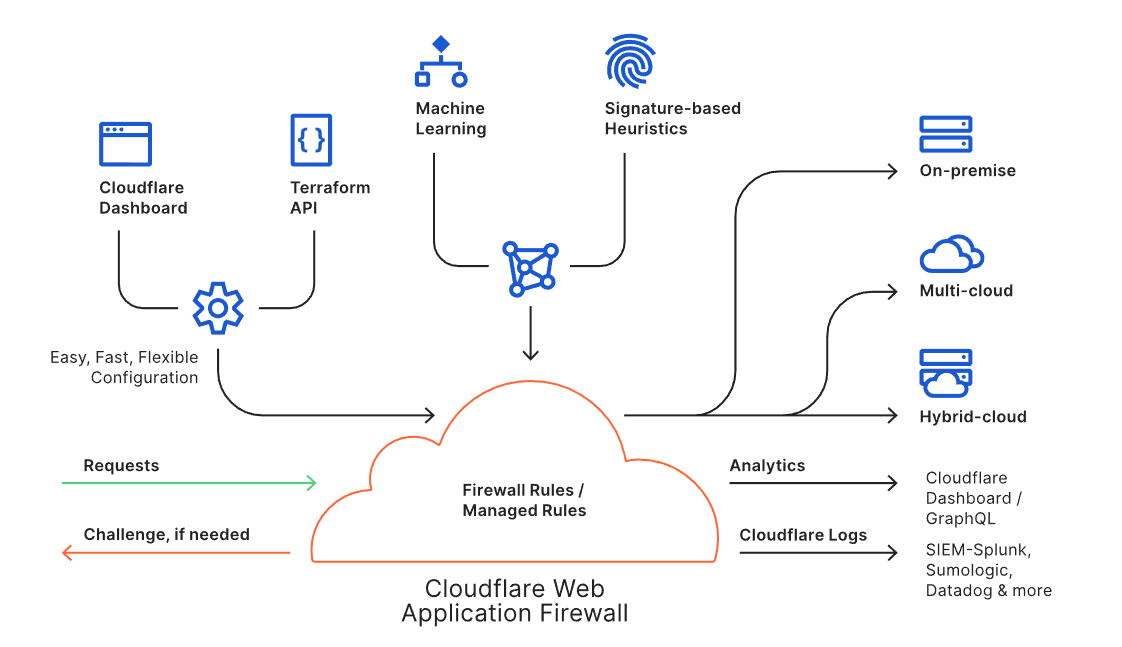
The WAF is available through an intuitive dashboard or a Terraform integration, and it enables users to build powerful rules. Every request to the WAF is inspected against the rule engine and the threat intelligence built from protecting approximately 25 million internet properties. Suspicious requests can be blocked, challenged or logged as per the needs of the user, while legitimate requests are routed to the destination regardless of where the application lives (i.e., on-premise or in the cloud). Analytics and Cloudflare Logs enable users to view actionable metrics.
The Cloudflare WAF is an intelligent, integrated, and scalable solution to protect business-critical Continue reading
DDoS mitigation using a Linux switch
Linux as a network operating system describes the benefits of using standard Linux as a network operating system for hardware switches. A key benefit is that the behavior of the physical network can be efficiently emulated using standard Linux virtual machines and/or containers.
In this article, CONTAINERlab will be used to create a simple testbed that can be used to develop a real-time DDoS mitigation controller. This solution is highly scaleable. Each hardware switch can monitor and filter terabits per second of traffic and a single controller instance can monitor and control hundreds of switches.
Create test network
The following ddos.yml file specifies the testbed topology (shown in the screen shot at the top of this article):
name: ddos
topology:
nodes:
router:
kind: linux
image: sflow/frr
attacker:
kind: linux
image: sflow/hping3
victim:
kind: linux
image: alpine:latest
links:
- endpoints: ["router:swp1","attacker:eth1"]
- endpoints: ["router:swp2","victim:eth1"]
Run the following command to run the emulation:
sudo containerlab deploy ddos.yml
Configure interfaces on router:
interface swp1
ip address 192.168.1.1/24
!
interface swp2
ip address 192.168.2.1/24
!
Configure attacker interface:
ip addr add 192.168.1.2/24 dev eth1
ip route add 192.168.2.0/24 via 192.168.1. Continue reading
Successful Strategies for Building and Growing IXPs

Insights from a comparative study launched today To bring faster, affordable, and resilient connectivity to people, local Internet stakeholders often turn to Internet exchange points (IXPs). They’re a critical digital infrastructure where networks come together to connect and exchange Internet traffic. IXPs help keep domestic Internet traffic local, reducing transit costs, lag time, and providing […]
The post Successful Strategies for Building and Growing IXPs appeared first on Internet Society.
