Cloudflare Pages is now Generally Available
In December, we announced the beta of Cloudflare Pages: a fast, secure, and free way for frontend developers to build, host, and collaborate on Jamstack sites.
It’s been incredible to see what happens when you put a powerful tool in developers’ hands. In just a few months of beta, thousands of developers have deployed over ten thousand projects, reaching millions of people around the world.
Today, we’re excited to announce that Cloudflare Pages is now available for anyone and ready for your production needs. We’re also excited to show off some of the new features we’ve been working on over the course of the beta, including: web analytics, built in redirects, protected previews, live previews, and optimized images (oh, my!). Lastly, we’ll give you a sneak peek into what we'll be working on next to make Cloudflare Pages your go-to platform for deploying not just static sites, but full-stack applications.
What is Cloudflare Pages?
Cloudflare Pages radically simplifies the process of developing and deploying sites by taking care of all the tedious parts of web development. Now, developers can focus on the fun and creative parts instead.
Seamless builds for developers
Getting started with Cloudflare Pages is as Continue reading
Live stream to multiple platforms with Stream Connect
Today, we are announcing the Stream Connect beta, the first step towards supporting end-to-end live broadcasting on Cloudflare. You can use Stream Connect to push RTMPS feeds to the Cloudflare edge and have it restreamed to your audience on any platform that supports RTMPS such as Facebook, YouTube and Twitch.
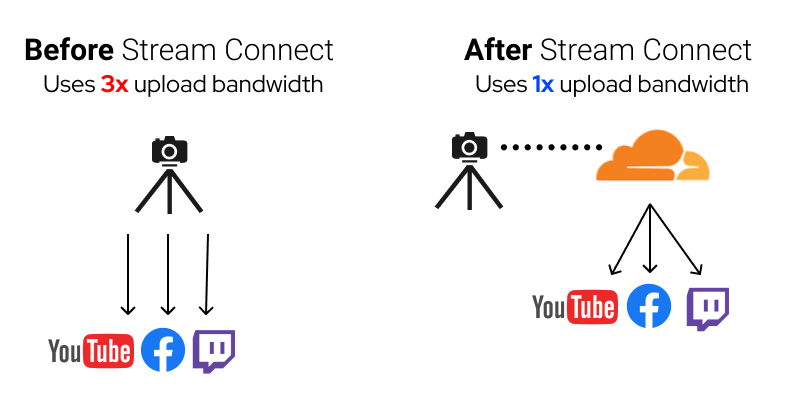
What is restreaming?
Facebook, YouTube and Twitch are great platforms for creators to broadcast live video to reach billions. They each have their own unique communities and benefits for creators. If you have a band and want to broadcast a live performance for your fans, broadcasting to only one platform limits your reach. Restreaming enables you to push the live video to multiple platforms at the same time so you can meet your fans on their preferred platform.
Live video platforms accept incoming connections using a protocol called RTMP or RTMPS. Stream Connect allows you to continue using the same protocol as before. However, instead of using your local connection to send the video feed to multiple platforms, you only send it to Stream Connect. Connect uses the Cloudflare network to send your live feed to the configured media platforms.
How Stream Connect increases reliability and lowers latency
Eliminating the Continue reading
NFA v 21.04: improved BGP reporting, extensive API, L2 MAC addresses visibility, and more.
We’re excited to announce that our latest Noction Flow Analyzer v 21.04 has just been released, giving users the: Improved and Refined BGP
The post NFA v 21.04: improved BGP reporting, extensive API, L2 MAC addresses visibility, and more. appeared first on Noction.
Why Being A Late Technology Adopter Pays Off
As a technologist helping an organization form an IT strategy, I’m usually hesitant to recommend new tech. Why? Because it’s new. Adopting technology early in its lifecycle is a risky endeavor. For most organizations, I find that shiny new tech isn’t worth the risk.
Emerging products and protocols are often accompanied by great fanfare. Talks are delivered at conferences, whitepapers are written, and Gartner Cool Vendor designations are awarded. The idea is to make you and me believe that this new tech solves a problem in a novel way that’s never been done before. This is the thing we’ve been waiting for. This is so much better than it used to be in the bad old times. Right. I’m sure it is.
Despite my cynical tone, I am hopeful when it comes to new tech. I really am. In part, technologists are employed because of tech’s ever-changing landscape. But I am also dubious during any technology’s formative years. I take a wait-and-see approach, and I’ve never been sorry for doing so. I believe that being a late, not early, adopter of technology pays off for most organizations.
You Aren’t Stuck With Abandoned Tech
If you adopt early, you are hoping Continue reading
Start Automating Public Cloud Deployments with Infrastructure-as-Code
One of my readers sent me a series of “how do I get started with…” questions including:
I’ve been doing networking and security for 5 years, and now I am responsible for our cloud infrastructure. Anything to do with networking and security in the cloud is my responsibility along with another team member. It is all good experience but I am starting to get concerned about not knowing automation, IaC, or any programming language.
No need to worry about that, what you need (to start with) is extremely simple and easy-to-master. Infrastructure-as-Code is a simple concept: infrastructure configuration is defined in machine-readable format (mostly text files these days) and used by a remediation tool like Terraform that compares the actual state of the deployed infrastructure with the desired state as defined in the configuration files, and makes changes to the actual state to bring it in line with how it should look like.
Start Automating Public Cloud Deployments with Infrastructure-as-Code
One of my readers sent me a series of “how do I get started with…” questions including:
I’ve been doing networking and security for 5 years, and now I am responsible for our cloud infrastructure. Anything to do with networking and security in the cloud is my responsibility along with another team member. It is all good experience but I am starting to get concerned about not knowing automation, IaC, or any programming language.
No need to worry about that, what you need (to start with) is extremely simple and easy-to-master. Infrastructure-as-Code is a simple concept: infrastructure configuration is defined in machine-readable format (mostly text files these days) and used by a remediation tool like Terraform that compares the actual state of the deployed infrastructure with the desired state as defined in the configuration files, and makes changes to the actual state to bring it in line with how it should look like.
Managing network devices with Golang using Netrasp
Have you let the Gophers into your network yet? With Netrasp, you can let them roam wild. Netrasp is a Go package that connects to network devices with SSH to allow you to send commands and configuration to them. The rasping sound as your network gets screenscraped would come from Netrasp. For people coming from the Python world, you could compare Netrasp to Netmiko. Continue reading
Troubleshooting steps
Introduction
Troubleshooting network issues is one of the common skills of every network engineer. And usually, we don’t think about it. We don’t study and train this skill especially. I tell about troubleshooting as a formal process. We just get experience from our daily routine or follow company workflow. I will try to formalize some basic notions. Hope it will be helpful.
Of course, it depends on the situation and business constraints but when we try to resolve some issue we should follow the next steps:
Preparing -> Information-gathering -> Isolating -> Resolving -> Escalating
Let's look at every step.
Preparing
Every network has infrastructure tools (monitoring, inventory, etc), but we should continuously improve and keep up to date them. Try to develop and integrate a new one. This stack of tools is our source of truth. If we have it, we can easily fetch a full amount of information before, during, and after problems. It’s an enormous topic but without these tools, we can’t successfully troubleshoot our network.
Mandatory tools:
- Syslog (at least simple Syslog server. And good to have e.g. Elastic stack)
- Alarm management system (e.g. Zabbix)
- Statistics collector (e. Continue reading
Developers, Developers, Developers: Welcome to Developer Week 2021
Runtimes, serverless, edge compute, containers, virtual machines, functions, pods, virtualenv. All names for things developers need to go from writing code to running code. It’s a painful reality that for most developers going from code they’ve written to code that actually runs can be hard.
Excruciatingly, software development is made hard by dependencies on modules, by scaling, by security, by cost, by availability, by deployment, by builds, and on and on. All the ugly reality of crystallizing thoughts into lines of code that actually run, successfully, somewhere, more than once, non-stop, and at scale.
And so… Welcome to Developer Week 2021!
Like we have done in previous Innovation Weeks (such as Security Week or Privacy Week), we will be making many (about 20) announcements of products and features to make developers’ lives easier. And by easy I mean removing the obstacles that stop you, dear developer, from writing code and deploying it so it scales to Internet size.
And Cloudflare Workers, our platform for software developers who want to deploy Internet-facing applications that start instantly and scale Internetly, has been around since 2017 (or to put it in perspective, since iPhone 8) and helping developers code and deploy in seconds Continue reading
Worth Reading: Fail-Fast is Failing… Fast
Here’s an interesting fact: cloud-based stuff often refuses to die; it might become insufferably slow, but would still respond to the health checks. The usual fast failover approach used in traditional high-availability clusters is thus of little use.
For more details, read the Fail-Fast is Failing… Fast ACM Queue article.
Worth Reading: Fail-Fast is Failing… Fast
Here’s an interesting fact: cloud-based stuff often refuses to die; it might become insufferably slow, but would still respond to the health checks. The usual fast failover approach used in traditional high-availability clusters is thus of little use.
For more details, read the Fail-Fast is Failing… Fast ACM Queue article.