Heavy Networking 537: Ansible Vs. Terraform For Network Automation
The networking community seems to have coalesced around Ansible for network device automation and Terraform for cloud. Why this divide? Are the two tools really that different? Today's Heavy Networking explores how and where you can use both these tools, with guests Ned Bellavance and Josh VanDeraa.
The post Heavy Networking 537: Ansible Vs. Terraform For Network Automation appeared first on Packet Pushers.
Heavy Networking 537: Ansible Vs. Terraform For Network Automation
The networking community seems to have coalesced around Ansible for network device automation and Terraform for cloud. Why this divide? Are the two tools really that different? Today's Heavy Networking explores how and where you can use both these tools, with guests Ned Bellavance and Josh VanDeraa.Iron Chef: Certification Edition

My friend Joshua Williams (@802DotMe) texted me today with a great quote that I wanted to share with you that made me think about certifications:
You’ve probably already thought through this extensively, and maybe even written about it, but after sitting through another 8 hour practical exam yesterday I’m more convinced than ever that expert level exams from technical companies are more analogous to a gimmicky Food Network TV show than real world application of technical acumen. They don’t care so much about my skill level as they do about what kind of meal I can prepare in 30 minutes using Tialapia, grapes, and Dr. Pepper syrup with my salt shaker taken away halfway through.
I laughed because it’s true. And then I thought about it more and realized he’s way more than right. We know for a fact that companies love to increase the level of challenge in their exams from novice to expert. It’s a way to weed out the people that aren’t committed to learning about something. However, as the questions and tasks get harder it becomes much more difficult to get a good sense of how candidates are going to perform.
Boiling Water Isn’t Continue reading
Asynchronous HTMLRewriter for Cloudflare Workers
Last year, we launched HTMLRewriter for Cloudflare Workers, which enables developers to make streaming changes to HTML on the edge. Unlike a traditional DOM parser that loads the entire HTML document into memory, we developed a streaming parser written in Rust. Today, we’re announcing support for asynchronous handlers in HTMLRewriter. Now you can perform asynchronous tasks based on the content of the HTML document: from prefetching fonts and image assets to fetching user-specific content from a CMS.
How can I use HTMLRewriter?
We designed HTMLRewriter to have a jQuery-like experience. First, you define a handler, then you assign it to a CSS selector; Workers does the rest for you. You can look at our new and improved documentation to see our supported list of selectors, which now include nth-child selectors. The example below changes the alternative text for every second image in a document.
async function editHtml(request) {
return new HTMLRewriter()
.on("img:nth-child(2)", new ElementHandler())
.transform(await fetch(request))
}
class ElementHandler {
element(e) {
e.setAttribute("alt", "A very interesting image")
}
}
Since these changes are applied using streams, we maintain a low TTFB (time to first byte) and users never know the HTML was transformed. If you’re interested in how we’re Continue reading
Video: Networks Are Not Homogenous
The last Fallacy of Distributed Computing I addressed in the introductory part of How Networks Really Work webinar was The Network Is Homogenous. No, it’s not and it never was… for more details watch this video.
Navigating the open network operating systems space
Subscribe to Kernel of Truth on iTunes, Google Play, Spotify, Cast Box and Sticher!
Click here for our previous episode.
Some of your favorites are back together on this episode of the Kernel of Truth podcast— specifically Roopa Prabhu, Brian O’Sullivan and Pete Lumbis. Things have changed a little around here since the last time the three of them were chatting together on the podcast but one thing hasn’t, how much they love to talk all things open networking. In this episode the group talks about how to navigate the open networking operating systems space. From figuring out how to choose an open network operating system, to understanding what works best for deployments, and even what resources and communities are out there for you to tap into. We have it all here for you to help you get started. All you have to do is sit back and enjoy the episode and don’t forget to also check out the links below with resources referenced in the podcast.
Guest Bios
Roopa Prabhu: Roopa is a Linux Architect at NVIDIA, formally Cumulus Networks. She and her team work on all things kernel networking and Linux system infrastructure areas. Her primary Continue reading
Leveraging OpenStack to Orchestrate Distributed Cloud Deployments
The industry is seeing an increasing distribution of data centers, driven by a desire to improve the end user experiences,...Announcing VMware Container Networking with Antrea for Kubernetes
By Cody McCain, Senior Product Manager and Susan Wu, Senior Product Marketing Manager, Networking and Security Business Unit
Enterprises benefit from collaborative engineering and receive the latest innovations from open source projects. However, it’s a challenge for enterprise to rely solely on community support to run their operations. This is because community support is best-effort and cannot provide a pre-defined SLA.
While Kubernetes itself is open source, and part of Cloud Native Computing Foundation (CNCF), it takes an ecosystem of surrounding technologies as curated by CNCF—from the container registry and storage engine to the container network plugin to run Kubernetes.
Announcing VMware Container Networking with Antrea
With the new release of VMware Container Networking with Antrea, enterprises get the best of both worlds – access to the latest innovation from Project Antrea and world-class support from VMware. Container Networking with Antrea is the commercial offering consisting of and 24/7 support for Project Antrea.
Container Networking with Antrea will package the latest release of Project Antrea version 0.9.1. Antrea is a purpose-built Kubernetes networking solution for public and private clouds building upon Open vSwitch, the open source technology optimized for distributed multi-layer switching performance. Antrea is designed to run anywhere Kubernetes Continue reading
How Argo Tunnel engineering uses Argo Tunnel
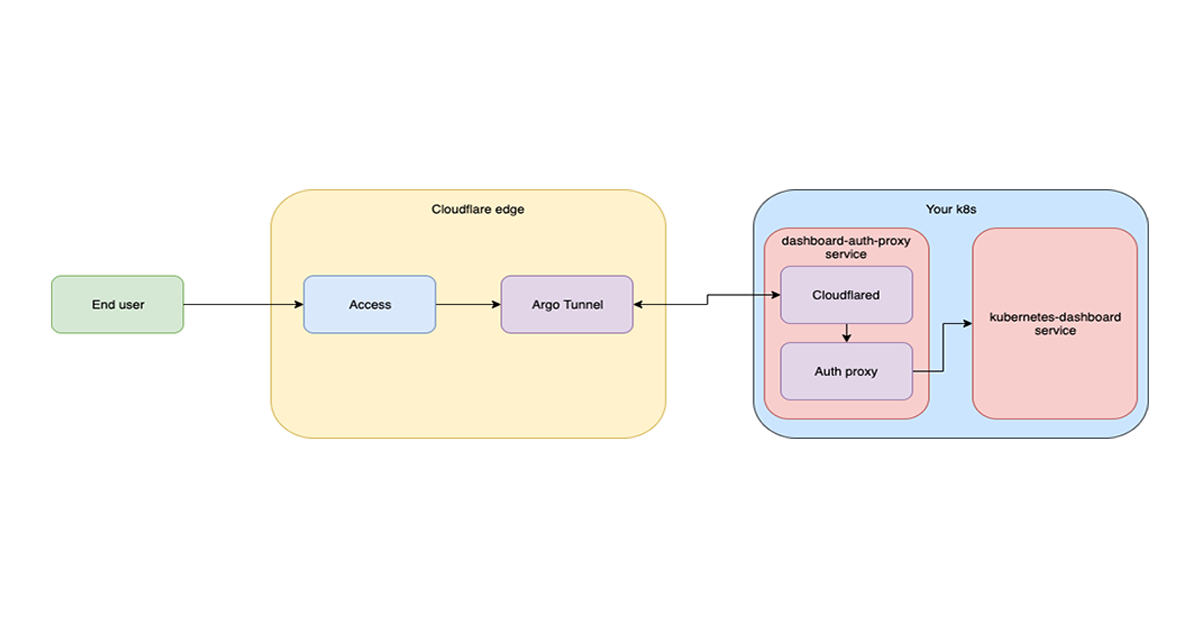
Whether you are managing a fleet of machines or sharing a private site from your localhost, Argo Tunnel is here to help. On the Argo Tunnel team we help make origins accessible from the Internet in a secure and seamless manner. We also care deeply about productivity and developer experience for the team, so naturally we want to make sure we have a development environment that is reliable, easy to set up and fast to iterate on.
A brief history of our development environment (dev-stack)
Docker compose
When our development team was still small, we used a docker-compose file to orchestrate the services needed to develop Argo Tunnel. There was no native support for hot reload, so every time an engineer made a change, they had to restart their dev-stack.
We could hack around it to hot reload with docker-compose, but when that failed, we had to waste time debugging the internals of Docker. As the team grew, we realized we needed to invest in improving our dev stack.
At the same time Cloudflare was in the process of migrating from Marathon to kubernetes (k8s). We set out to find a tool that could detect changes in source code and Continue reading
Review Questions: Switching, Bridging and Routing
One of the most annoying part in every training content development project was the ubiquitous question somewhere at the end of the process: “and now we’d need a few review questions”. I’m positive anyone ever involved in a similar project can feel the pain that question causes…
Writing good review questions requires a particularly devious state of mind, sometimes combined with “I would really like to get the answer to this one” (obviously you’d mark such questions as “needs further research”, and if you’re Donald Knuth the question would be “prove that P != NP").
Security Policy Self-Service for Developers and DevOps Teams
In today’s economy, digital assets (applications, data, and processes) determine business success. Cloud-native applications are designed to iterate rapidly, creating rapid time-to-value for businesses. Organizations that are able to rapidly build and deploy their applications have significant competitive advantage. To this end, more and more developers are creating and leading DevOps teams that not only drive application development, but also take on operational responsibilities formerly owned by platform and security teams.
What’s the Value of a Self-Service Approach?
Cloud-native applications are often designed and deployed as microservices. The development team that owns the microservice understands the behavior of the service, and is in the best position to define and manage the network security of their microservice. A self-service model enables developers to follow a simple workflow and generate network policies with minimal effort. When problems occur with. application connectivity, developers should be able to diagnose connectivity issues and resolve them quickly without having to depend on resources outside of the team.
Developers and DevOps teams can also take a leading role in managing security, which is an integral part of cloud-native applications. There are two aspects to security in the context of Kubernetes.
- Cluster security – is a uniform set Continue reading