Linux Shell Recursively Remove Whitespace Lines From All Files
How to Remove the lines with only white space from all files in a directory tree.Weekend Reads 072420
Blame it on the webinar yesterday… I’m late again. 
However, there have been multiple reported attempts to exploit the transfer market as part of malicious operations — such as the hijacking of dormant address space and spamming — which, judging by exchanges between operators in mailing Continue reading
Reflecting on my first year at Cloudflare as a Field Marketer in APAC
Hey there! I am Els (short form for Elspeth) and I am the Field Marketing and Events Manager for APAC. I am responsible for building brand awareness and supporting our lovely sales team in acquiring new logos across APAC.
I was inspired to write about my first year in Cloudflare, because John, our CTO, encouraged more women to write for our Cloudflare blog after reviewing our blogging statistics and found out that more men than women blog for Cloudflare. I jumped at the chance because I thought this is a great way to share many side stories as people might not know about how it feels to work in Cloudflare.
Why Cloudflare?
Before I continue, I must mention that I really wanted to join Cloudflare after reading our co-founder Michelle’s reply on Quora regarding "What is it like to work in Cloudflare?." Michelle’s answer as follows:
“my answer is 'adult-like.' While we haven’t adopted this as our official company-wide mantra, I like the simplicity of that answer. People work hard, but go home at the end of the day. People care about their work and want to do a great job. When someone does a good job, Continue reading
Linux Shell Recursively Remove Whitespace Lines From All Files
This is just a quick post to outline how to remove the lines with only white space from all files in a directory tree. I found another method to do this with the application I am using but I wanted to keep this handy one liner in my back pocket for future reference. Dark Magic The...Heavy Networking 531: Hyperscale Multi-Cloud Networking With Arrcus (Sponsored)
Today's Heavy Networking podcast examines a new multi-cloud networking product from sponsor Arrcus. Arrcus streamlines and secures multi-cloud networks via its new ArcEdge and ArcOrchestrator products that connect the data center and edge locations to the cloud. Our guest are Keyur Patel, CTO of Arrcus; and Sree Kannan, VP of Product Management.
The post Heavy Networking 531: Hyperscale Multi-Cloud Networking With Arrcus (Sponsored) appeared first on Packet Pushers.
Heavy Networking 531: Hyperscale Multi-Cloud Networking With Arrcus (Sponsored)
Today's Heavy Networking podcast examines a new multi-cloud networking product from sponsor Arrcus. Arrcus streamlines and secures multi-cloud networks via its new ArcEdge and ArcOrchestrator products that connect the data center and edge locations to the cloud. Our guest are Keyur Patel, CTO of Arrcus; and Sree Kannan, VP of Product Management.Video Meetings and Learning Styles

Have you noticed that every meeting needs to be on video now? Of course, that’s a rhetorical question. It’s one of the first and most constant things that is brought up in the pandemic-influenced tech community of today. Meetings that used to be telephone-only or even wordy emails are now video chats that take half an hour or more. People complain that they are spending time and money to spruce up their office to look presentable at 720p to people that likely aren’t paying attention anyway. It’s a common complaint. But have you ever thought about why?
Listening and Looking to Learn
There are three major styles of learning that get brought up in academic courses.
- Physical, or kinesthetic, learners learn best from touching things. They want to manipulate and feel things as they learn. They like to gesture when they talk. They also get bored quickly when things are taking too long or they have to sit still too much.
- Visual learners learn best from seeing things. They like to look around and tend to think in pictures. They would rather see something instead of hearing someone speak.
- Auditory learners like to hear things being spoken. They want to Continue reading
A (Fairly) Non-Technical Guide to Routing Security Basics

On the MANRS website, we write about routing security. We dig into the details of technical problems, research the origins of route leaks and hijacks, analyze trends and statistics related to networks around the globe via the MANRS Observatory, and generally get pretty nerdy about how to improve the routing system that underpins the Internet. Last week, we took a step back and published a series of posts regarding Routing Security Basics.
This 5-part series covers the following topics:
- What Is Routing?
- How Does Routing Work?
- What’s Wrong with Routing?
- What Are Routing Incidents?
- What are the MANRS Actions?
While it’s difficult to explain routing security without assuming some baseline knowledge, our intent is for these posts to be as non-technical as possible to help non-experts understand this sometimes-complicated topic.
It all started with a Twitter thread on a Friday afternoon, comparing routing security to online dating. We then expanded this silly analogy into a series of blog posts. Follow along as Juan, Maria, and Bad Guy Chad help us explain the types of routing incidents that happen and how the simple, concrete MANRS actions can help.
We hope you’ll read the Routing Security Basics posts, and if you’re Continue reading
Diversity Welcome – A Latinx journey into Cloudflare


I came to the United States chasing the love of my life, today my wife, in 2015.
A Spanish native speaker, Portuguese as my second language and born in the Argentine city of Córdoba more than 6,000 miles from San Francisco, there is no doubt that the definition of "Latino" fits me very well and with pride.
Cloudflare was not my first job in this country but it has been the organization in which I have learned many of the things that have allowed me to understand the corporate culture of a society totally alien to the one which I come from.
I was hired in January 2018 as the first Business Development Representative for the Latin America (LATAM) region based in San Francisco. This was long before the company went public in September 2019. The organization was looking for a specialist in Latin American markets with not only good experience and knowledge beyond languages (Spanish/Portuguese), but understanding of the economy, politics, culture, history, go-to-market strategies, etc.—I was lucky enough to be chosen as "that person". Cloudflare invested in me to a great extent and I was amazed at the freedom I had to propose ideas and bring them Continue reading
Announcing the Tigera – Nutanix Partnership
Today we are pleased to announce our partnership with Nutanix, creators of the industry’s most popular hyper-converged infrastructure (HCI) technology. HCI combines datacenter hardware using locally-attached storage resources with intelligent software to create flexible building blocks that replace legacy infrastructure consisting of separate servers, storage networks, and storage arrays.
Networking and securing microservices running Kubernetes and securely accessing external resources can be challenging, often requiring the use of overlay networks and NATs. At scale, this becomes extremely complex. Cloud-native enterprises seeking a consistent container networking experience across multiple cloud environments have adopted Calico, the de facto standard in open-source Kubernetes networking technologies.
Nutanix is now offering Calico as a component of Karbon, Nutanix’s enterprise Kubernetes management solution that enables turnkey provisioning, operations, and lifecycle management of Kubernetes. With this integration, Karbon users can now take advantage of simplified Kubernetes networking and production-grade network security based on Calico’s native tooling, providing scalable throughput that meets the performance demands of Karbon users.
“Karbon, now with Calico embedded, gives our customers significantly more powerful networking and network security capabilities while preserving the simplicity of provisioning and operating a Kubernetes cluster,” said Greg Muscarella, VP of Products at Nutanix. “Calico eliminates Continue reading
Remove Whitespace from Rendered Templates in 11ty
How to customise the Nunjucks environment to remove whitespace from rendered templates.A Narrow Window of Opportunity for Rural Connectivity in the U.S.

As COVID-19 continues to shine a spotlight on the vital role the Internet plays, a short window of opportunity has opened for the Federal Communications Commission (FCC) to do their part in connecting rural Indigenous communities in the United States.
The Tribal Priority Window is currently open for federally-recognized tribes, Alaska Native Villages, and Hawaiian Homelands to apply for Educational Broadband Service (EBS) spectrum, but it closes on August 3rd. Access to the EBS spectrum would enable Indigenous communities to build their own Internet networks.
The FCC set this deadline before the pandemic, but Tribal governments are now overwhelmed by handling the Coronavirus with limited resources. The FCC must give them more time to apply to the priority window. COVID-19 will not simply disappear from tribal lands in time for tribal governments to pull together applications.
The need for reliable, affordable Internet access is more pressing than ever.
Need proof? One only has to look at the fact that Indigenous communities in the US face the lowest rate of broadband access and the highest per capita rate of COVID-19 infections. The need for access to accurate information and telehealth is at an all-time high. Tribal communities are at serious risk Continue reading
IPv6 Buzz 056: What’s The Deal With NAT64?
In this week's IPv6 Buzz episode, Ed and Tom speak with Sander Steffann to get his expert take on NAT64, an important IPv6 transition technology. We also delve into his critical IPv6 efforts with the European Regional Internet Registry (RIPE).
The post IPv6 Buzz 056: What’s The Deal With NAT64? appeared first on Packet Pushers.
IPv6 Buzz 056: What’s The Deal With NAT64?
In this week's IPv6 Buzz episode, Ed and Tom speak with Sander Steffann to get his expert take on NAT64, an important IPv6 transition technology. We also delve into his critical IPv6 efforts with the European Regional Internet Registry (RIPE).Dictionary: coulrophobia

The feeling you get working with ITIL consultants
The post Dictionary: coulrophobia appeared first on EtherealMind.
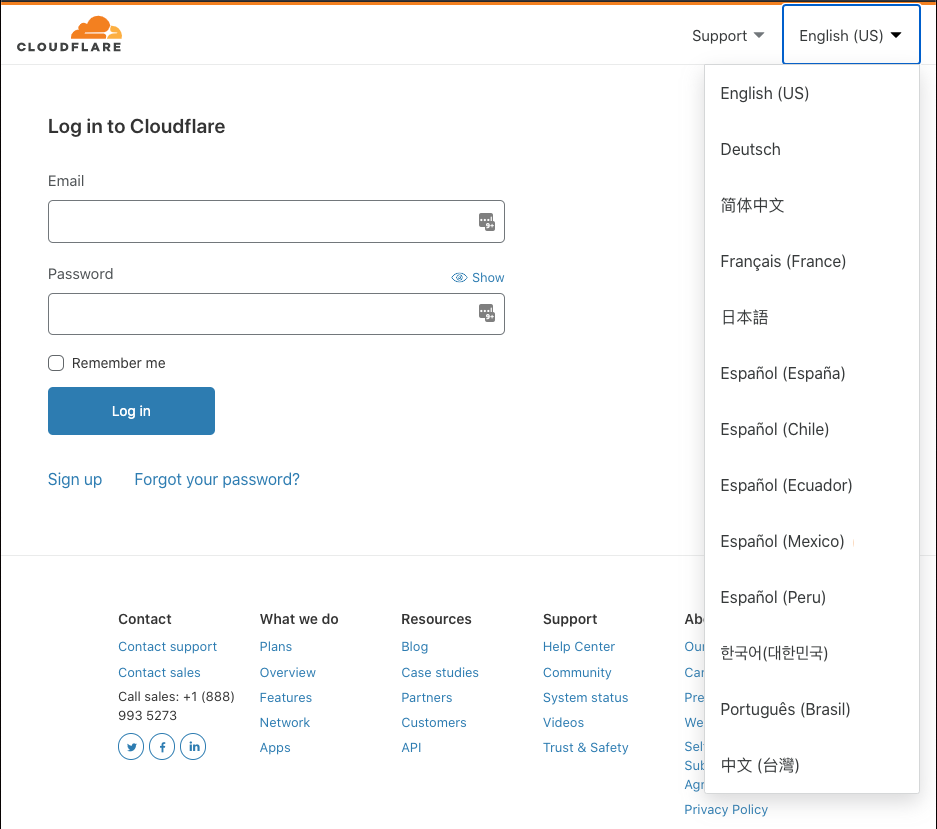
Internationalizing the Cloudflare Dashboard
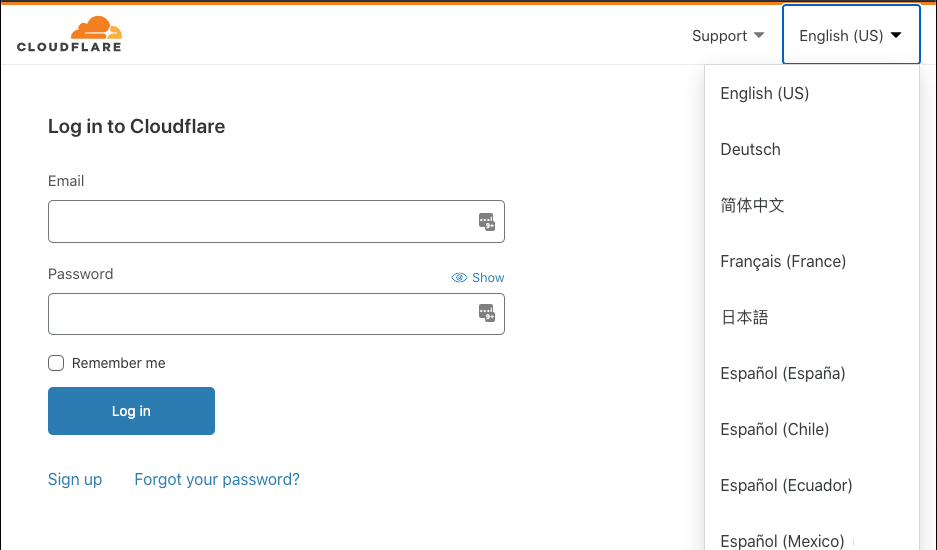
Cloudflare’s dashboard now supports four new languages (and multiple locales): Spanish (with country-specific locales: Chile, Ecuador, Mexico, Peru, and Spain), Brazilian Portuguese, Korean, and Traditional Chinese. Our customers are global and diverse, so in helping build a better Internet for everyone, it is imperative that we bring our products and services to customers in their native language.
Since last year Cloudflare has been hard at work internationalizing our dashboard. At the end of 2019, we launched our first language other than US English: German. At the end of March 2020, we released three additional languages: French, Japanese, and Simplified Chinese. If you want to start using the dashboard in any of these languages, you can change your language preference in the top right of the Cloudflare dashboard. The preference selected will be saved and used across all sessions.
In this blog post, I want to help those unfamiliar with internationalization and localization to better understand how it works. I also would like to tell the story of how we made internationalizing and localizing our application a standard and repeatable process along with sharing a few tips that may help you as you do the same.
Beginning the journey
The first Continue reading
Remove Whitespace from Rendered Templates in 11ty
The default behavour of 11ty is to just remove the template tags from rendered templates and leave behind white space in its place. This is probably mostly fine but for me it was causing large amounts of white space in my rendered templates and needless changes in git diffs. 11ty uses...NVM Install and Usage Ubuntu 2004
How to install and use Node version manager on Ubuntu 2004.Dictionary: internet

Its not capital I anymore
The post Dictionary: internet appeared first on EtherealMind.