Coalition Forms to Address Open RAN Policies
The Open RAN Policy Coalition has support from seven operators and 24 vendors, though it's...
Microsoft Azure Sentinel Powers Open Systems’ Threat Detection
Open Systems’ customers liked the Sentinel technology, but wanted the threat detection and...
Cinco de Mayo – What are we celebrating anyway?
Greetings from Latinflare, Cloudflare’s LatinX Employee Resource Group, with members all over the US, the UK, and Portugal. Today is Cinco de Mayo! Americans everywhere will be drinking margaritas and eating chips and salsa. But what is this Mexican holiday really about and what exactly are we celebrating?
About Cinco de Mayo
Cinco de Mayo, Spanish for "Fifth of May", is an annual celebration held in Mexico on May 5th. The date is observed to commemorate the Mexican Army's victory over the French Empire at the Battle of Puebla, on May 5, 1862, under the leadership of General Ignacio Zaragoza. The victory of the smaller Mexican force against a larger French force was a boost to morale for the Mexicans. Zaragoza died months after the battle due to illness. A year after the battle, a larger French force defeated the Mexican army at the Second Battle of Puebla, and Mexico City soon fell to the invaders.
In the United States, Cinco de Mayo has taken on a significance beyond that in Mexico. More popularly celebrated in the United States than Mexico, the date has become associated with the celebration of Continue reading
Automate file uploads to your Cisco Nexus switches

If you have more than three Cisco Nexus switches in nx-os mode, and you are not using Cisco DCNM or any other similar tool, you probably already have encountered this question: How to automate file uploads to your Cisco Nexus switches? Here is a turnkey Python script using Netmiko’s SCP function to do this. This script is very simple, it relies only on Netmiko functions and SCP. But it does its job very well and I share it here because it can certainly help you to save time. What…
The post Automate file uploads to your Cisco Nexus switches appeared first on AboutNetworks.net.
Former Check Point Execs Score $20M for Orca Security
With the Series A round, in addition to $6.5 million in seed funding, Orca plans to double its team...
Setting up Cloudflare for Teams as a Start-Up Business
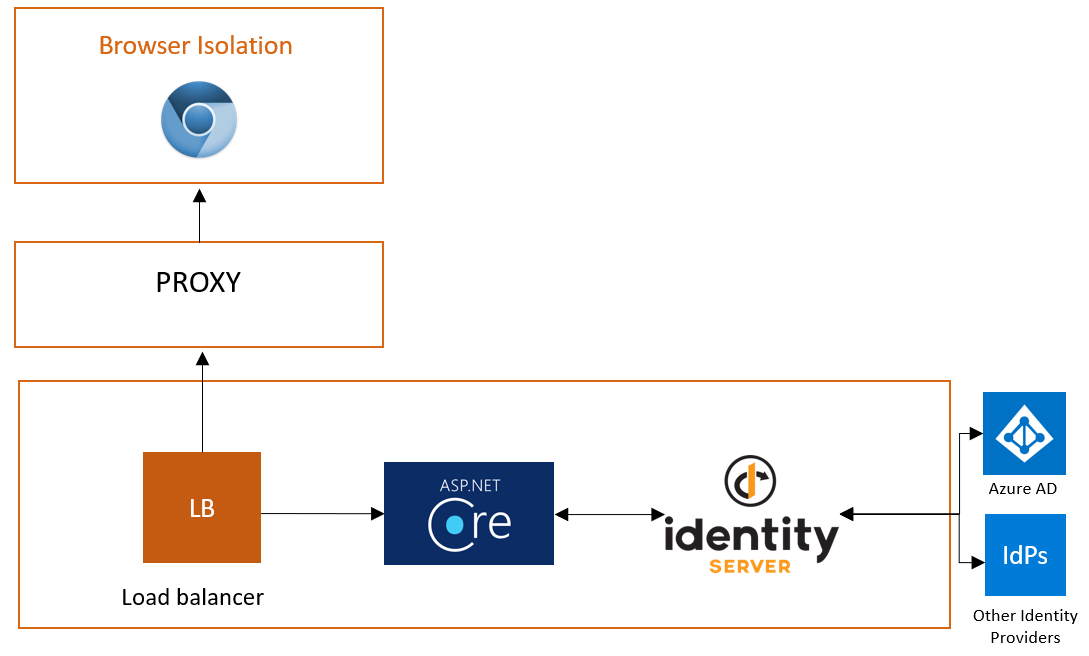
Earlier this year, Cloudflare acquired S2 Systems. We were a start-up in Kirkland, Washington and now we are home to Cloudflare’s Seattle-area office.
Our team developed a new approach to remote browser isolation (RBI), a technology that runs your web browser in a cloud data center, stopping threats on the Internet from executing any code on your machine. The closer we can bring that data center to the user, the faster we can make that experience. Since the acquisition, we have been focused on running our RBI platform in every one of Cloudflare’s data centers in 200 cities around the world.
The RBI solution will join a product suite that we call Cloudflare for Teams, which consists of two products: Access and Gateway.
Those two products solve a number of problems that companies have with securing users, devices, and data. As a start-up, we struggled with a few of these challenges in really painful ways:
- How do we let prospects securely trial our RBI platform?
- How do we keep our small office secure without an IT staff?
- How can we connect to the powerful, but physically clunky and heavy development machines, when we are not in that office?
Dogfooding Continue reading
Dictionary: fauxpology

Define fauxpology
The post Dictionary: fauxpology appeared first on EtherealMind.
HS. Part 5. Automation at high-scale: Bringing network up (Docker SONIC-P4 and Linux bridges) based on the network graph.
Hello my friend,
Finally we approached the point where we start dealing with the network functions again, now at a high scale. After we have successfully generated the configuration files for our Microsoft Azure SONiC network functions, it is a time to boot them, span them and get the emulated data centre up and running.
2
3
4
5
retrieval system, or transmitted in any form or by any
means, electronic, mechanical or photocopying, recording,
or otherwise, for commercial purposes without the
prior permission of the author.
Network automation training – now as a self-paced course as well
Following your asks we open a new format for the network automation training – self-paced format:
- It doesn’t matter what your timezone is.
- It doesn’t matter how much hours weekly do you have to study.
- It doesn’t matter how solid is your current background in automation, scripting and software development.
Because you decide on your own when, how often and how quickly you can learn.

At this training we teach you all the necessary concepts such as YANG data modelling, working with JSON/YAML/XML data formats, Linux administration basics, programming in Continue reading
Using Elastic Stack in Networking and Security
Andrea Dainese is continuing his journey through open-source NetDevOps land. This time he decided to focus on log management systems, chose Elastic Stack, and wrote an article describing what it is, why a networking engineer should look at it, and what’s the easiest way to start.
Building a Scalable Document Pre-Processing Pipeline
This article was originally posted on the Amazon Web Services Architecture blog.
In a recent customer engagement, Quantiphi, Inc., a member of the Amazon Web Services Partner Network, built a solution capable of pre-processing tens of millions of PDF documents before sending them for inference by a machine learning (ML) model. While the customer's use case--and hence the ML model--was very specific to their needs, the pipeline that does the pre-processing of documents is reusable for a wide array of document processing workloads. This post will walk you through the pre-processing pipeline architecture.
Daily Roundup: Cisco Debunks Security Myths
Cisco debunked security myths; Nvidia bought Cumulus; and T-Mobile claimed 5 standalone 5G firsts.
How Rakuten Mobile Corralled Vendors for Its Open RAN Vision
Complexities were abundant and corralling vendors for a virtualized, cloud-native, open radio...
UCMP: Augmenting L3 only designs
An aspiration of modern web scale networking is to leverage a pure L3 solution and integrate it with anycast addresses to allow for load balancing functionality. So why is this design aspirational? Well it requires discipline in the way that applications are architected— specifically around tenancy requirements and application redundancy. In this blog I’ll discuss a recent augmentation that was introduced into Cumulus Linux 4.1 that makes this style of design much more flexible in web scale networks.
Common challenges
Two common challenges when using anycast addressing in layer 3 only solutions are:
- Resilient hashing to support the change in ECMP paths
- Balancing traffic across unequal cost advertisements
Solutions
The first solution was implemented back in the early version of Cumulus Linux and is well documented. This solution is also known as “RASH” as the colloquial term.
The second solution addresses an interesting artifact of the way Layer 3 routes are advertised and learned, specifically with regards to next hop selection. Let us imagine the following simplified design:

The IP address of 192.168.1.101 is an anycast address that is being advertised by 3 different hosts in our environment. These three hosts are all serving the exact Continue reading
Nvidia Will Buy Cumulus Networks
Together with Mellanox, Nvidia says Cumulus’ open networking platform will help accelerate the...
T-Mobile Claims 5 Standalone 5G Firsts
Today’s 5G networks are effectively piggybacking on 4G LTE, but T-Mobile and others soon plan to...
Basic Linux Networking tips and tricks part-3: ss and netstat commands

Here is the third post of the series on basic network troubleshooting and tools under RHEL / CentOS. In this post, I will talk about the netstat and ss commands. Others posts of the series This post is part of a series about basic Linux Networking tips and tricks. The others posts of this series are: The ip and nmcli commands The mtr command The ss and netstat commands The curl command netstat The netstat command is a network utility used to display network connections, protocol or interfaces…
The post Basic Linux Networking tips and tricks part-3: ss and netstat commands appeared first on AboutNetworks.net.