The Week in Internet News: Mexico, NYC Push for Internet Access for All

Everyone’s invited: Politicians in Mexico and New York City announced plans for universal Internet access in recent days. Mexican President Andres Manuel Lopez Obrador announced a plan to bring access to the large swaths of the country that don’t have it, including a government investment of more than $500,000, according to AA News. Meanwhile, New York City Major Bill de Blasio is pushing an “Internet master plan” to improve access. About 18 percent of the city’s residents have neither mobile nor home Internet connections, and about 40 percent have one or the other, but not both, the New York Daily News reports.
New pressure campaign: The U.S. FBI is asking Apple for help to access encrypted communications on an iPhone that belonged to the Saudi military student who killed three people last month at a naval base in Pensacola, Fla., the Washington Post reports. It’s unclear what information the FBI is looking for, given that the shooter is dead, but the request is a new step in the long-running fight between the U.S. government and large tech vendors over the use of encryption on smartphones and other devices.
Cyber retaliation: Many cybersecurity experts expect Iran to retaliate with cyberattacks Continue reading
Dictionary: Human Permafrost

What is Human Permafrost in IT Infrastructure ?
The post Dictionary: Human Permafrost appeared first on EtherealMind.
AWS Rarely Kills a Service. What About Your Vendor?
Here’s an interesting tidbit from “Last Week in AWS” blog:
From a philosophical point of view, AWS fundamentally considers an API to be a promise. Services that aren’t promoted anymore are still available […] Think about that for a second - a service launched 13 years ago is still actively supported to the point where you can use it today.
Compare that to Killed By Google graveyard, and you might understand why I’m a bit reluctant to cover GCP in my webinars.
Read more ...Helping mitigate the Citrix NetScaler CVE with Cloudflare Access
Yesterday, Citrix sent an updated notification to customers warning of a vulnerability in their Application Delivery Controller (ADC) product. If exploited, malicious attackers can bypass the login page of the administrator portal, without authentication, to perform arbitrary code execution.
No patch is available yet. Citrix expects to have a fix for certain versions on January 20 and others at the end of the month.
In the interim, Citrix has asked customers to attempt to mitigate the vulnerability. The recommended steps involve running a number of commands from an administrator command line interface.
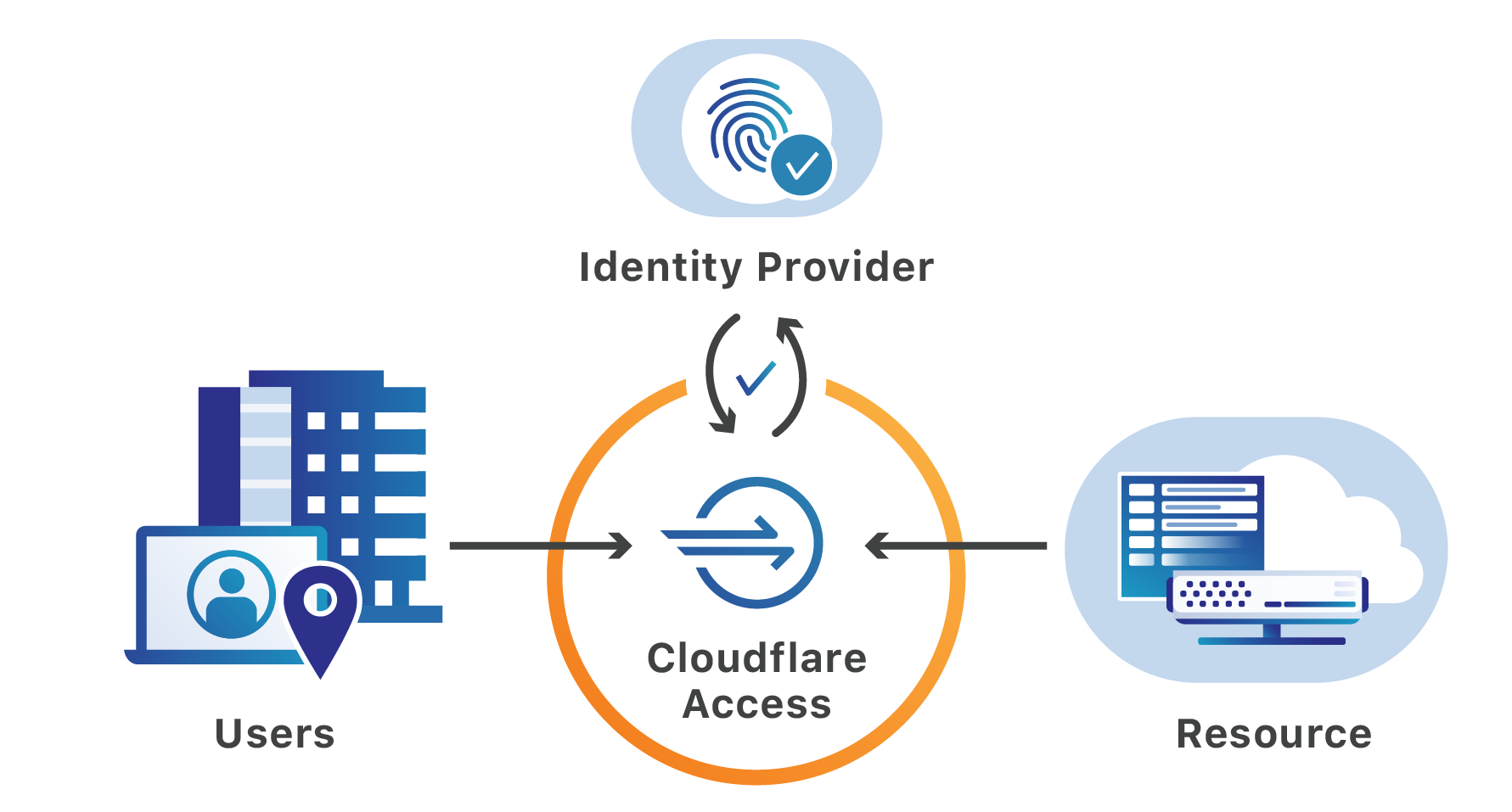
The vulnerability relied on by attackers requires that they first be able to reach a login portal hosted by the ADC. Cloudflare can help teams secure that page and the resources protected by the ADC. Teams can place the login page, as well as the administration interface, behind Cloudflare Access’ identity proxy to prevent unauthenticated users from making requests to the portal.
Exploiting URL paths
Citrix ADC, also known as Citrix NetScaler, is an application delivery controller that provides Layer 3 through Layer 7 security for applications and APIs. Once deployed, administrators manage the installation of the ADC through a portal available at a dedicated URL on Continue reading
VXLAN Book Errata 12-January 2020
Continue reading
Must Read: Ironies of Automation
Stumbled upon a 35-year-old article describing the ironies of automation (HT: The Morning Paper). Here’s a teaser…
Unfortunately automatic control can ‘camouflage’ system failure by controlling against the variable changes, so that trends do not become apparent until they are beyond control.
In simpler words: when things fail, they fail really badly because the intermittent failures were kept hidden. Keep that in mind the next time someone tells you how wonderful software-defined AI-assisted networking is going to be.
Junos SNMP via Routing Instance
Juniper routing instances are very useful when you need separate routing tables on the one device, for example to separate customers. Junos lets you configure SNMP polling of routing instances, so customers can poll “their” interfaces using 'instance_name'@'community'. All very useful. But it wasn’t obvious to me how to poll the default table via an interface in a routing instance. The trick is to just use @'community'. Here’s an example.
Network Overview
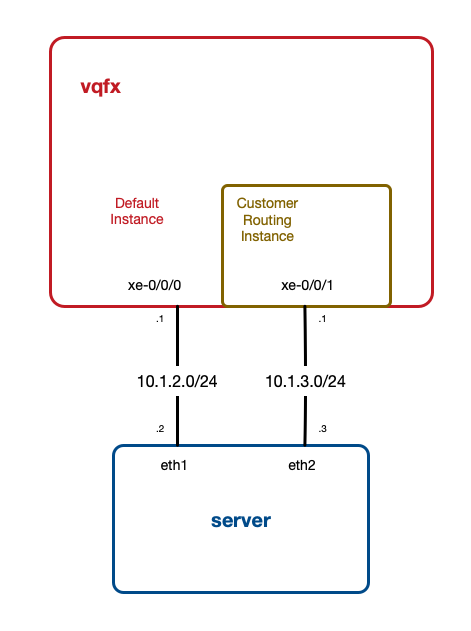
To demo this I have a simple network. I’m using a Virtual QFX plus Vagrant setup, based on the Vagrantfiles in this repo. I’m running one vqfx10k, connected to one server. The key here is that the server has two connections to the vqfx. One interface is in the default instance, one is in a “Customer” routing instance:
Here’s the routing-instance config:
1
2
3
4
5
6
7
8
vagrant@vqfx> show configuration routing-instances
Customer {
instance-type virtual-router;
interface xe-0/0/1.0;
}
{master:0}
vagrant@vqfx>
And here’s my SNMP configuration:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
vagrant@vqfx> Continue reading
Junos SNMP via Routing Instance
Juniper routing instances are very useful when you need separate routing tables on the one device, for example to separate customers. Junos lets you configure SNMP polling of routing instances, so customers can poll “their” interfaces using 'instance_name'@'community'. All very useful. But it wasn’t obvious to me how to poll the default table via an interface in a routing instance. The trick is to just use @'community'. Here’s an example.
Network Overview
To demo this I have a simple network. I’m using a Virtual QFX plus Vagrant setup, based on the Vagrantfiles in this repo. I’m running one vqfx10k, connected to one server. The key here is that the server has two connections to the vqfx. One interface is in the default instance, one is in a “Customer” routing instance:
Here’s the routing-instance config:
1
2
3
4
5
6
7
8
vagrant@vqfx> show configuration routing-instances
Customer {
instance-type virtual-router;
interface xe-0/0/1.0;
}
{master:0}
vagrant@vqfx>
And here’s my SNMP configuration:
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
vagrant@vqfx> show Continue reading
Another perspective on "engineering" in IT
Found a nice article about Margaret Hamilton, the lady who coined the term "software engineering".
Engineering—back in 1969 as well as here in 2020—carries a whole set of associated values with it, and one of the most important is the necessity of proofing for disaster before human usage. You don’t “fail fast” when building a bridge: You ensure the bridge works first.
Now be a good "networking engineer" and go and stretch another VLAN around the globe... ;)
Cuckoo Installation and Configuration on Debian 10 Buster
The tutorial covers installation and configuration of Cuckoo Malware Sandbox on Debian 10 Buster. Once you complete successfully all steps, your Cuckoo installation will be ready to perform analysis of malware uploaded to guest VM. It is Windows 7 x64 SP1 VM running on Oracle VirtualBox. The tutorial is based on an excellent YouTube videos […]Continue reading...
Heavy Networking 497: Good Reasons To Start Your Tech Blog
If one of your New Year's resolutions is to blog more, or start a blog, this episode is for you. We discuss the benefits of technical blogging including raising your profile, improving your own understanding, contributing to the community, and creating new opportunities in your professional life. Our guests are John Mark Troyer and Stephen Foskett.
The post Heavy Networking 497: Good Reasons To Start Your Tech Blog appeared first on Packet Pushers.
‘Major Initiatives in Cybersecurity’ Shows Everyone Can Contribute to Trust

How do we work toward a more secure Internet?
In the Cyber Security discussions that take place in the various policy fora around the world, there is often little appreciation that the security of the Internet is a distributed responsibility, where many stakeholders take action.
By design, the Internet is a distributed system with no central core or point of control. Instead, Internet security is achieved by collaboration where multiple companies, organizations, governments, and individuals take action to improve the security and trustworthiness of the Internet – so that it is open, secure, and available to all.
Today we’ve published Major Initiatives in Cybersecurity: Public & Private Contributions Towards Increasing Internet Security to illustrate, via a handful of examples regarding Internet Infrastructure, there are a great number initiatives working, sometimes together and sometimes independently, in improving the Internet’s security. An approach we call collaborative security.
Major Initiatives in Cybersecurity describes Internet security as the part of cybersecurity that, broadly speaking, relates to the security of Internet infrastructure, the devices connected to it, and the technical building blocks from which applications and platforms are built.
We make no claim to completeness, but we do hope that the paper illustrates the complexity, breath, Continue reading
Cisco NX-OS Graceful Insertion and Removal (GIR)

If you operate a data-center network with Cisco Nexus, you’ve probably already faced the problem of how to perform a maintenance on one of the two switches of a vPC pair, with minimum impact and risks for the production network. Cisco NX-OS contains a feature called “Graceful Insertion and Removal” or GIR to help you for that. Here is how it works. Scenario Let’s take the example below: (click on the image to see a larger version) We have two Nexus (in nx-os mode) in vPC. Doing layer-2 aggregation and …
The post Cisco NX-OS Graceful Insertion and Removal (GIR) appeared first on AboutNetworks.net.
The Art of Saying “No”

No.
It’s the shortest sentence in the English language. It requires no other parts of speech. It’s an answer, a statement, and a command all at once. It’s a phrase that some people have zero issues saying over and over again. And yet, some others have an extremely difficult time answering anything in the negative.
I had a fun discussion on twitter yesterday with some friends about the idea behind saying “no” to people. It started with this tweet:
Coincidentally, I tweeted something very similar to what Bob Plankers had tweeted just hours before:
The gist is the same though. Crazy features and other things that have been included in software and hardware because someone couldn’t tell another person “no”. Sadly, it’s something Continue reading