Rubrik Cozies Up With NetApp On Data Security
The joint service aims to simplify how large organizations with vast network-attached software...
NSX Cloud – Choice of Agented or Agentless Modes of Operation
VMware NSX through its NSX Cloud offering enables customers to implement a consistent networking and security framework for workloads hosted across on-premises data center (DC) and public clouds such as AWS and Azure.
Every cloud orchestration and management tool, immaterial of what use case it has set out to solve has one question to answer: If it is an agent-based solution or an agentless solution. More often than not, the answer to this question has direct implications for the ability of the cloud admin team to deploy and manage the solution.
But, do we really have to choose?! What if we can have both agented and agentless modes of operation?! That’s the question we asked ourselves with VMware NSX and here we are with NSX-T 2.5.
Meet the New NSX Cloud Modes of Operation
What is NSX Enforced Mode?
NSX Enforced Mode provides a “consistent” security and networking policy framework between your on-premises DC and public cloud environment. You can have a unified–corporate-wide-firewall-policy which will be enforced as an NSX Policy, by having an nsx footprint inside each virtual machine running in the cloud.
Why is it Required?
Well, NSX architecture has 3 layers:
- Management-plane
- Control-plane
- Data-plane
Carriers’ Messaging Joint Venture Destined To Fail
Rich Communications Service still hasn’t arrived and I doubt it will ever become the standard...
AT&T Lobs 3-Year Plan Amid Investor Backlash
AT&T isn’t fully out of the woods, but it has made good progress on its plan to reduce total...
Microsoft Unleashes a Tsunami of IoT Updates
The company unveiled a bevy of new updates to its burgeoning IoT portfolio aimed at addressing...
Network Break 258: Aruba Stacks Up New Switches; SpaceX Promises Satellite Broadband In 2020
Today's Network Break examines new campus and data center switches from Aruba, looks at new SD-WAN gear from Riverbed, discusses Teridion PoPs in China for SD-WAN, explores financial results from Juniper and AWS, and much more. Guest Ed Horley joins as guest commentator.
The post Network Break 258: Aruba Stacks Up New Switches; SpaceX Promises Satellite Broadband In 2020 appeared first on Packet Pushers.
Network Break 258: Aruba Stacks Up New Switches; SpaceX Promises Satellite Broadband In 2020
Today's Network Break examines new campus and data center switches from Aruba, looks at new SD-WAN gear from Riverbed, discusses Teridion PoPs in China for SD-WAN, explores financial results from Juniper and AWS, and much more. Guest Ed Horley joins as guest commentator.Microsoft Strikes Down AWS With ‘Big’ JEDI Win
“From the looks of it, the DoD process looked unstructured and was full of fits and starts ......
The Week in Internet News: U.S. Big Tech Firms Skip Chinese Internet Conference

Not our model: Google, Twitter, Facebook, and Apple skipped a Chinese conference focused on a global governance model for the Internet, Asia One reports. During the conference, China promoted its highly restrictive model of the Internet. Google, Twitter, and Facebook are blocked in China, while Apple must use a local partner to offer cloud services, the story notes.
No news for you: Meanwhile, the Chinese government’s Great Firewall blocks 23 percent of the news organizations that have journalists stationed in the country, reports the South China Morning Post, citing statistics from the Foreign Correspondents’ Club of China. Nearly a third of English-language sites are blocked. Blocked sites include the BBC, The Guardian, The New York Times, The Wall Street Journal, and the Washington Post.
Flying cars and smart mirrors: Among the Internet of Things trends to look for in 2020 are flying cars and mirrors that deliver news and weather while you’re brushing your hair, What Mobile says. Widespread use of flying cars may be a way off, but one startup is working on them. Multilingual voice assistants and flexible displays are other things to watch for.
Opposed to encryption: A large U.S. Internet service provider is lobbying lawmakers in opposition to Continue reading
Supporting the latest version of the Privacy Pass Protocol


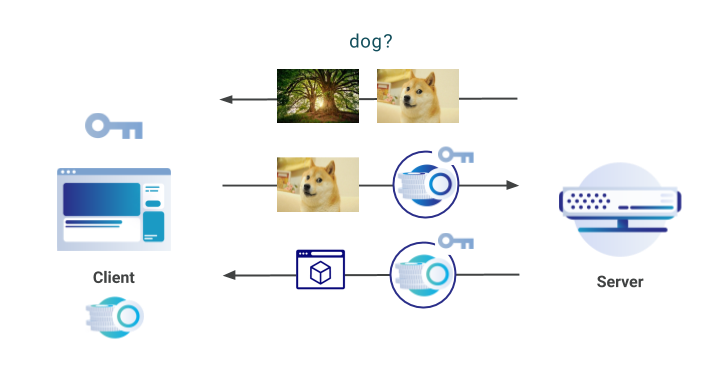
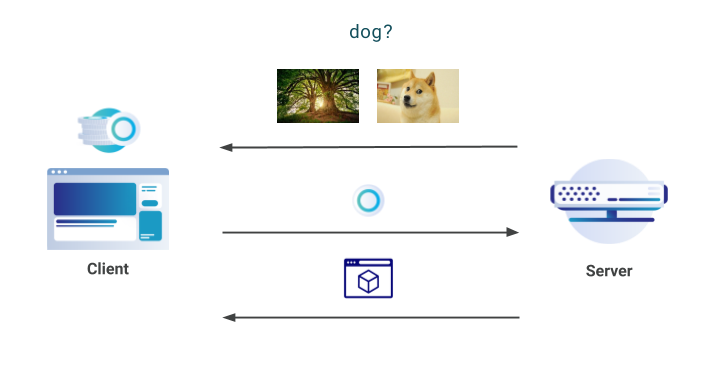
At Cloudflare, we are committed to supporting and developing new privacy-preserving technologies that benefit all Internet users. In November 2017, we announced server-side support for the Privacy Pass protocol, a piece of work developed in collaboration with the academic community. Privacy Pass, in a nutshell, allows clients to provide proof of trust without revealing where and when the trust was provided. The aim of the protocol is then to allow anyone to prove they are trusted by a server, without that server being able to track the user via the trust that was assigned.
On a technical level, Privacy Pass clients receive attestation tokens from a server, that can then be redeemed in the future. These tokens are provided when a server deems the client to be trusted; for example, after they have logged into a service or if they prove certain characteristics. The redeemed tokens are cryptographically unlinkable to the attestation originally provided by the server, and so they do not reveal anything about the client.
To use Privacy Pass, clients can install an open-source browser extension available in Chrome & Firefox. There have been over 150,000 individual downloads of Privacy Pass worldwide; approximately 130,000 in Chrome and Continue reading
Whitebox Hardware and Open-Source Software
One of my subscribers was interested in trying out whitebox solutions. He wrote:
What open source/whitebox software/hardware should I look at if I wanted to build a leaf-and-spine VXLAN/EVPN/BGP data center.
I don’t think you can get a fully-open-source solution because the ASIC manufacturers hide their SDK behind a mountain of NDAs (that strategy must make perfect sense – after all, it generated such awesome PR for NVIDIA). Anyway, the closest you can get (AFAIK) if you're a mere mortal is Cumulus Linux, and you just choose any whitebox hardware off their Hardware Compatibility List.
Read more ...Junos – Loading Configs – 1 of 5 – Merge
In this post series, we will cover one of the wonderful things with Junos, which is loading configurations to the …
The post Junos – Loading Configs – 1 of 5 – Merge appeared first on Fryguy's Blog.