Parallel Wireless CEO: Don’t Forget About Radios
“Everyone wants to forget the radios, and the radios are what makes wireless wireless," Steve...
“Everyone wants to forget the radios, and the radios are what makes wireless wireless," Steve...
Hello my friend,
So far you have learned about the for loop and if conditional. Both of these tools are very useful and have a wide area of the applicability inside the network automation filed. But what if we need to do some activities in your Python code continuously until a certain condition becomes False? The answer you will find in this blogpost.
Don’t wait to be kicked out of IT business. Join our network automation training to secure your job in future. Come to NetDevOps side.
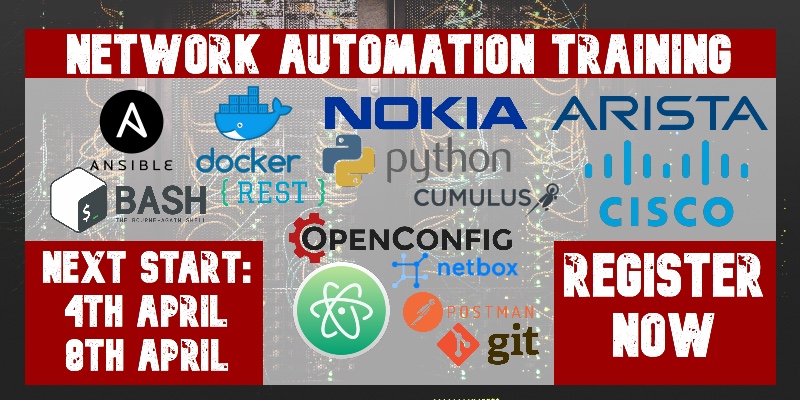
How does the training differ from this blog post series? Here you get the basics and learn some programming concepts in general, whereas in the training you get comprehensive set of knowledge with the detailed examples how to use Python for the network and IT automation. You need both.
While loop is a specific type of the loop in Python, which is being executed infinitely while the associated condition is True. All the knowledge you got about the if conditionals are applicable here as well.
Read the if conditional blogpost for more details.
Therefore, while instruction requires careful planing Continue reading
Organizations are predicting a multi-trillion-dollar boost from 5G deployments, though...


With so many people at Cloudflare now working remotely, it's worth stepping back and looking at the systems we use to get work done and how we protect them. Over the years we've migrated from a traditional "put it behind the VPN!" company to a modern zero-trust architecture. Cloudflare hasn’t completed its journey yet, but we're pretty darn close. Our general strategy: protect every internal app we can with Access (our zero-trust access proxy), and simultaneously beef up our VPN’s security with Spectrum (a product allowing the proxying of arbitrary TCP and UDP traffic, protecting it from DDoS).
Before Access, we had many services behind VPN (Cisco ASA running AnyConnect) to enforce strict authentication and authorization. But VPN always felt clunky: it's difficult to set up, maintain (securely), and scale on the server side. Each new employee we onboarded needed to learn how to configure their client. But migration takes time and involves many different teams. While we migrated services one by one, we focused on the high priority services first and worked our way down. Until the last service is moved to Access, we still maintain our VPN, keeping it protected with Spectrum.
Some of our services didn't Continue reading


It’s never been more crucial to help remote workforces stay fully operational — for the sake of countless individuals, businesses, and the economy at large. In light of this, Cloudflare recently launched a program that offers our Cloudflare for Teams suite for free to any company, of any size, through September 1. Some of these firms have been curious about how Cloudflare itself uses these tools.
Here’s how Cloudflare’s next-generation VPN alternative, Cloudflare Access, came to be.
Rewind to 2015. Back then, as with many other companies, all of Cloudflare’s internally-hosted applications were reached via a hardware-based VPN. When one of our on-call engineers received a notification (usually on their phone), they would fire up a clunky client on their laptop, connect to the VPN, and log on to Grafana.
It felt a bit like solving a combination lock with a fire alarm blaring overhead.

But for three of our engineers enough was enough. Why was a cloud network security company relying on clunky on-premise hardware?
And thus, Cloudflare Access was born.
Many of the products Cloudflare builds are a direct result of the challenges our own team is looking to address, and Access is a Continue reading
VMware withdrew FY21 guidance citing coronavirus concerns; Kubernetes 1.18 ramped up Windows...
In China’s case, being bigger than the rest plays to its advantage in positioning three Chinese...
Threat researchers at Microsoft, ClearSky, and Okta are among the hundreds of security experts...
While the long overdue upgrade to PCI-Express 4.0 is finally coming to servers, allowing for high bandwidth links between processors and peripherals. …
Pushing PCI-Express Fabrics Up To The Next Level was written by Timothy Prickett Morgan at The Next Platform.
As chipmakers scramble to limit the effect of COVID-19 on supply chains, IDC analysts reported an...

Ready, set, launch: An Internet Society Chapter launched recently in Ethiopia, with a goal of advocating for the development and expansion of open, secure, trustworthy, and affordable Internet access to everyone in the country. The idea of starting an Internet Society Chapter came from a workshop, “where we became conscious of the fact that more than 85% of the Ethiopia population is losing countless opportunities every day because they don’t have access to the Internet,” wrote Adugna Necho, a networking professor at Bahir Dar University. “We believe the Internet is for everyone and we are here to work with all people – from communities to businesses to governments and ordinary people to connect the unconnected and create a bigger and stronger Internet in Ethiopia.”
More Internet, please: The Internet will keep people connected while the world deals with the coronavirus pandemic, the India Chennai Chapter notes. Governments should resist urges to shut down service, the Chapter says. “With factories, offices, public places, transportation, schools are colleges shut down, and no clear picture of whether normal life would resume in 4 weeks or 4 months, it is the Internet that could make life go on,” the Chapter writes. “While it is Continue reading
Hey, it's HighScalability time!

Awesome explanation of how to build a PID controller to fly a rocket! (BPS.space via Orbital Index)
Do you like this sort of Stuff? Without your support on Patreon this kind of Stuff can't happen. You are that important to the fate of the intelligent world.
Know someone who wants to understand the cloud? I wrote Explain the Cloud Like I'm 10 just for them. On Amazon it has 103 mostly 5 star reviews. Here's a recent authentic unfaked review:

In an SEC filing, VMware said COVID-19 posed a risk to its “business operations, financial...

I’m a huge fan of video games. I love playing them, especially on my old consoles from my formative years. The original Nintendo consoles were my childhood friends as much as anything else. By the time I graduated from high school, everyone had started moving toward the Sony Playstation. I didn’t end up buying into that ecosystem as I started college. Instead, I just waited for my brother to pick up a new console and give me his old one.
This meant I was always behind the curve on getting to play the latest games. I was fine with that, since the games I wanted to play were on the old console. The new one didn’t have anything that interested me. And by the time the games that I wanted to play did come out it wouldn’t be long until my brother got a new one anyway. But one thing I kept hearing was that the Playstation was backwards compatible with the old generation of games. I could buy a current console and play most of the older games on it. I wondered how they managed to pull that off since Nintendo never did.
When I was older, I did Continue reading
As a leading supplier of cloud networking equipment globally, Arista plays a critical role in supporting the cloud communications and computing infrastructure that will keep the world running during these difficult times. The rapid acceleration of Covid-19 developments across the world has been sudden and shocking. It has forced us to take a new perspective on gratitude for what we have, including our families, health and an opportunity to rethink our goals.
As a leading supplier of cloud networking equipment globally, Arista plays a critical role in supporting the cloud communications and computing infrastructure that will keep the world running during these difficult times. The rapid acceleration of Covid-19 developments across the world has been sudden and shocking. It has forced us to take a new perspective on gratitude for what we have, including our families, health and an opportunity to rethink our goals.


As part of our ongoing compliance efforts Cloudflare’s PCI scope is reviewed quarterly and after any significant changes to ensure all in-scope systems are operating in accordance with the PCI DSS. This review also allows us to periodically review each product we offer as a PCI validated service provider and identify where there might be opportunities to provide greater value to our customers.
With our customers in mind, we completed our latest assessment and have increased our PCI certified product offering!
Building trust in our products is one critical component that allows Cloudflare’s mission of “Building a Better Internet” to succeed. We reaffirm our dedication to building trust in our products by obtaining industry standard security compliance certifications and complying with regulations.
Cloudflare is a Level 1 Merchant, the highest level, and also provides services to organizations to help secure their cardholder data environment. Maintaining PCI DSS compliance is important for Cloudflare because (1) we must ensure that our transmission and processing of cardholder data is secure for our own customers, (2) that our customers know they can trust Cloudflare’s products to transmit cardholder data securely, and (3) that anyone who interacts with Cloudflare’s services know that their information is Continue reading
Recently I stumbled upon the IETF draft about PIM Designated Router Load Balancing (DRLB) and it reminded me of something absolutely barbaric.

In L3 multicast, load balancing is simple. If the RPF route is ECMP, the router can choose …
When I’ve seen my good friends Christopher Werny and Enno Rey talk about IPv6 security at RIPE78 meeting, another bit of one of my puzzles fell in place. I was planning to do an update of the IPv6 security webinar I’d done with Eric Vyncke, and always wanted to get it done by a security practitioner focused on enterprise networks, making Christopher a perfect fit.
As it was almost a decade since we did the original webinar, Christopher started with an overview of IPv6 security challenges (TL&DR: not much has changed).
Server component and system maker Supermicro is known for being out in front when any X86 processor comes to market and often shoots the gap between ODMs, who have a relatively small number of large customers, and OEMs, who have a large number of relatively small customers. …
Minimalist Hyperscale Servers For The Rest Of Us was written by Timothy Prickett Morgan at The Next Platform.