Fortinet Quadruples Q1 Revenues, Posts Triple-Digit Cloud Growth
 Investors were not as impressed as the company's stock was trading down early Friday off of a recent 52-week high.
Investors were not as impressed as the company's stock was trading down early Friday off of a recent 52-week high.
 Investors were not as impressed as the company's stock was trading down early Friday off of a recent 52-week high.
Investors were not as impressed as the company's stock was trading down early Friday off of a recent 52-week high.
 Intel classified four of the new flaws as “high risk” and four as “medium,” and it's working on patches.
Intel classified four of the new flaws as “high risk” and four as “medium,” and it's working on patches.
 Arista reported excellent earnings for its Q1 2018, but Wall Street, with its insatiable appetite, is concerned the company's growth rates are slowing.
Arista reported excellent earnings for its Q1 2018, but Wall Street, with its insatiable appetite, is concerned the company's growth rates are slowing.
 Google releases workflow creation beta; Deutsche Telekom puts 5G technology on German soil; HPE and Red Hat collaborate on containers.
Google releases workflow creation beta; Deutsche Telekom puts 5G technology on German soil; HPE and Red Hat collaborate on containers.
The Future of Networking series continues with guest Kyle Mestery.
Kyle is well known to many corners of the networking community including the open source community. He recently re-joined Cisco as a Distinguished Engineer.
We talk with Kyle to get his take on where the packets are flowing over the next several years, including the tech conference scene, open-source networking, the proliferation of open-source networking OSs, what’s inside Open Network Linux (ONL), and cloud-native network functions virtualization.
ThousandEyes gives you performance visibility from every user to every app over any network, both internal and external, so you can smoothly migrate to the cloud, transform your WAN, troubleshoot faster and deliver exceptional user experiences. Sign up for a free account at thousandeyes.com/packetpushers and choose a free ThousandEyes t-shirt.
Silicon Loons.com – Kyle’s blog
Network Service Mesh – GitHub
Three Years On: Open Standards, Open Source, Open Loop – Cisco Systems
Verizon Launches Virtual Service Bundles – Light Reading
The post Show 388: The Future Of Networking With Kyle Mestery appeared first on Packet Pushers.
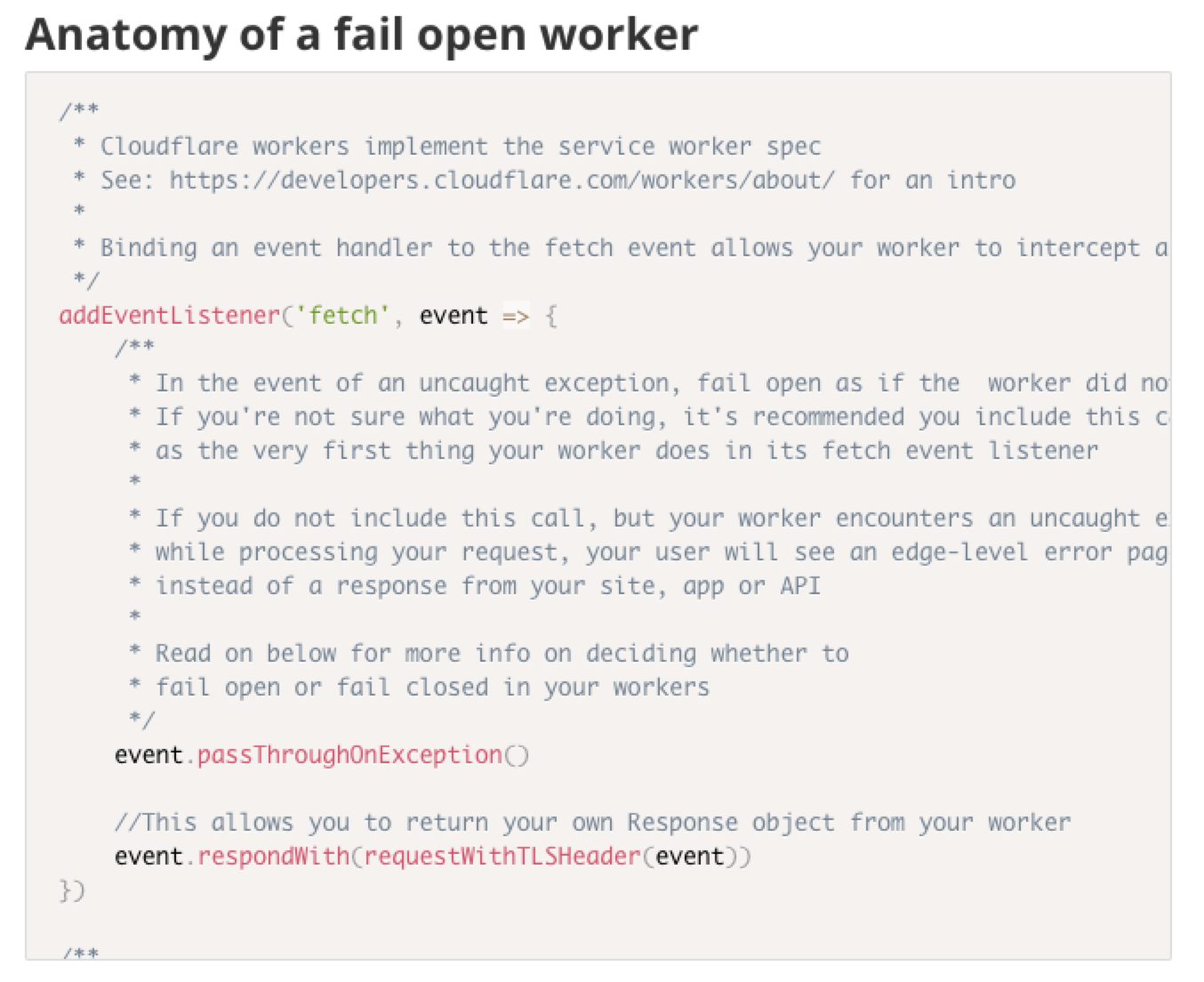
On the WWW team, we’re responsible for Cloudflare’s REST APIs, account management services and the dashboard experience. We take security and PCI compliance seriously, which means we move quickly to stay up to date with regulations and relevant laws.
A recent compliance project had a requirement of detecting certain end user request data at the edge, and reacting to it both in API responses as well as visually in the dashboard. We realized that this was an excellent opportunity to dogfood Cloudflare Workers.
In this blog post, we’ll break down the problem we solved using a single worker that we shipped to multiple hosts, share the annotated source code of our worker, and share some best practices and tips and tricks we discovered along the way.
Since being deployed, our worker has served over 400 million requests for both calls to api.cloudflare.com and the www.cloudflare.com dashboard.
First, we needed to detect when a client was connecting to our services using an outdated TLS protocol. Next, we wanted to pass this information deeper into our application stack so that we could act upon it and Continue reading
It is fair to say that containers in HPC are a big deal. Nothing more clearly shows the critical nature of any technology than watching the community reaction when a new security issue is discovered and released.
In a recent announcement from the team over at Sylabs, they stated that multiple container systems on kernels that do not support PR_SET_NO_NEW_PRIVS were now vulnerable. This was big news, and it obviously spread like a proverbial wildfire through the HPC community, with many mostly voicing their upset that the initial announcement came out at the start of a long holiday weekend …
HPC Container Security: Fact, Myth, Rumor, And Kernels was written by James Cuff at The Next Platform.
There has been plenty of change throughout the evolution of information technology. Now it's time for the corporate world to catch up and reshape how they do business and serve their customers.
It’s that time again! Tune in on May 7 at 10 am PST/ 1 pm EST for our monthly CCNA Kickoff session with expert instructor Keith Bogart.
This is a FREE session in which Keith (CCIE #4923) will present everything you need to know to get started on your CCNA journey.
What Keith will cover in this months webinar:
You can view this, and all of our other webinars here.
 The pre-owned car marketplace app sometimes processes upwards of 20,000 vehicles in a busy weekend.
The pre-owned car marketplace app sometimes processes upwards of 20,000 vehicles in a busy weekend.
The year 2017 was an important milestone in moving forward the European agenda for Digital for Development (D4D). The European Commission (EC) paper on mainstreaming digital technologies into EU development policy and the European Council conclusions on Digital for Development have activated the European development community to share opinions and ideas on how to help bridge the global digital divide.
In the past month, we have had a couple of open events in Brussels to discuss this important issue. The European Parliament’s EPP group hosted a public hearing on Digitalisation for Development to collect ideas and to push for more progress. Two weeks later, the EC held the first multistakeholder meeting for Digital4Development with a focus on Africa.
Building a Balanced Agenda
There are a number of pillars of activities that most stakeholders agree on. These include Internet access with a focus on last mile; Internet as an enabler across different sectors; skills; and entrepreneurship. During the recent meetings, the EC, the national development agencies and the private sector showcased impressive and innovative digitalisation programmes.
However, several stakeholders pointed out that while it is important to continue to invest in Internet access, this is no longer enough. We need Continue reading
In this Network Collective Short Take, guest commentator Nick Buraglio shares his thoughts on field area networking after watching Cisco’s presentation on the topic at Networking Field Day 17. You can see the original NFD17 presentation here: https://vimeo.com/253197120
The post Short Take – Cisco Field Area Networking appeared first on Network Collective.
With KubeCon EU happening in Copenhagen, we looked back at the most popular posts with our readers on Docker and Kubernetes. For those of you that have yet to try Docker EE 2.0, this blog highlights how in Docker for Desktops you can use Docker compose to directly deploy an application onto a Kubernetes cluster.
If you’re running an edge version of Docker on your desktop (Docker for Mac or Docker for Windows Desktop), you can now stand up a single-node Kubernetes cluster with the click of a button. While I’m not a developer, I think this is great news for the millions of developers who have already been using Docker on their Macbook or Windows laptop because they now have a fully compliant Kubernetes cluster at their fingertips without installing any other tools.
Developers using Docker to build containerized applications often build Docker Compose files to deploy them. With the integration of Kubernetes into the Docker product line, some developers may want to leverage their existing Compose files but deploy these applications in Kubernetes.
With Docker on the desktop (as well as Docker Enterprise Edition) you can use Docker compose to directly deploy an application Continue reading
David Barroso was sick-and-tired of using ZX Spectrum of Network Automation and decided to create an alternative with similar functionality but a proper programming language instead of YAML dictionaries masquerading as one. The result: Brigade, an interesting network automation tool we discussed in Episode 90 of Software Gone Wild.
Notes:
Performance analysis of cloud applications Ardelean et al., NSDI’18
Today’s choice gives us an insight into how Google measure and analyse the performance of large user-facing services such as Gmail (from which most of the data in the paper is taken). It’s a paper in two halves. The first part of the paper demonstrates through an analysis of traffic and load patterns why the only real way to analyse production performance is using live production systems. The second part of the paper shares two techniques that Google use for doing so: coordinated bursty tracing and vertical context injection.
Let’s start out just by consider Gmail requests explicitly generated by users (called ‘user visible requests,’ or UVRs, in the paper). These are requests generated by mail clients due to clicking on messages, sending messages, and background syncing (e.g., IMAP).
You can see a clear diurnal cycle here, with the highest QPS when both North America and Europe are active in the early morning, and lower QPS at weekends. (All charts are rescaled using some unknown factor, to protect Google information).

Request response sizes vary by about 20% over time. Two contributing factors are bulk mail senders, Continue reading
 Software-defined storage is rising to the top of the storage market, but before selecting a solution, it’s important to determine the features and capabilities for your specific set of needs.
Software-defined storage is rising to the top of the storage market, but before selecting a solution, it’s important to determine the features and capabilities for your specific set of needs.