Microsoft Beats AWS in Cloud Revenues for the First Quarter of 2018
 Microsoft reported cloud revenues of $6 billion, while AWS reported revenues of $5.4 billion for the quarter.
Microsoft reported cloud revenues of $6 billion, while AWS reported revenues of $5.4 billion for the quarter.
 Microsoft reported cloud revenues of $6 billion, while AWS reported revenues of $5.4 billion for the quarter.
Microsoft reported cloud revenues of $6 billion, while AWS reported revenues of $5.4 billion for the quarter.
Have you ever wondered why spine-and-leaf networks are the “standard” for data center networks? While the answer has a lot to do with trial and error, it turns out there is also a mathematical reason the fat-tree spine-and-leaf is is used almost universally. There often is some mathematical reason for the decisions made in engineering, although we rarely explore those reasons. If it seems to work, there is probably a reason.
The fat-tree design is explored in a paper published in 2015 (available here at the ACM, and now added to my “classic papers” page so there is a local copy as well), using a novel technique to not only explore why the spine-and-leaf fat-tree is so flexible, but even what the ideal ratio of network capacity is at each stage. The idea begins with this basic concept: one kind of network topology can be emulated on top of another physical topology. For instance, you can emulate a toroid topology on top of a hierarchical network, or a spine-and-leaf on top of of hypercube, etc. To use terms engineers are familiar with in a slightly different way, let’s call the physical topology the underlay, and the emulated topology the overlay. Continue reading
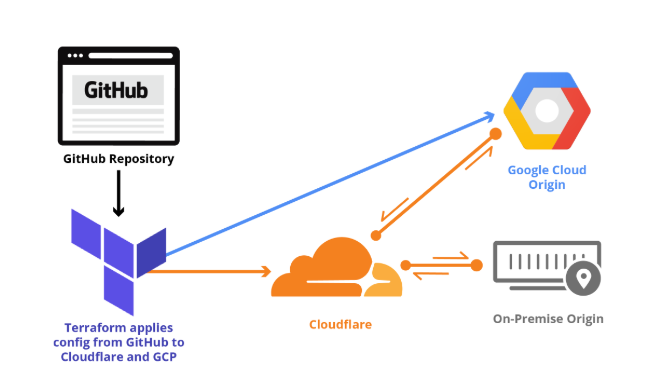
In Part 1 of Getting Started with Terraform, we explained how Terraform lets developers store Cloudflare configuration in their own source code repository, institute change management processes that include code review, track their configuration versions and history over time, and easily roll back changes as needed.
We covered installing Terraform, provider initialization, storing configuration in git, applying zone settings, and managing rate limits. This post continues the Cloudflare Terraform provider walkthrough with examples of load balancing, page rules, reviewing and rolling back configuration, and importing state.
Before we build on Part 1, let's quickly review what we configured in that post. Because our configuration is in git, we can easily view the current configuration and change history that got us to this point.
$ git log
commit e1c38cf6f4230a48114ce7b747b77d6435d4646c
Author: Me
Date: Mon Apr 9 12:34:44 2018 -0700
Step 4 - Update /login rate limit rule from 'simulate' to 'ban'.
commit 0f7e499c70bf5994b5d89120e0449b8545ffdd24
Author: Me
Date: Mon Apr 9 12:22:43 2018 -0700
Step 4 - Add rate limiting rule to protect /login.
commit d540600b942cbd89d03db52211698d331f7bd6d7
Author: Me
Date: Sun Apr 8 22:21:27 2018 -0700
Step 3 - Enable TLS 1.3, Continue reading
Why BGPSec turned out the way it did ?
Well, not exactly Fishin', but I'll be on a month long vacation starting today. I won't be posting new content, so we'll all have a break. Disappointing, I know. Please use this time for quiet contemplation and other inappropriate activities. Se vidiva kmalu!

If you really need a quick fix there's always all the back catalog of Stuff the Internet Says. Odds are there's a lot you didn't read yet.
Take a Network Break! A cryptocurrency heist combines BGP hijacking with some DNS tomfoolery, Juniper targets enterprise multicloud with Contrail enhancements, and Big Switch adds packet capture and analytics appliances to its product line.
The Linux community swaps out iptables for BPF, Google pushes the Rich Communication Service (RCS) to compete on messaging, and Cisco unbundles Nexus 9000.
Apple exits the home WiFi router market, Innovium snags $77 million to market its programmable ASIC, and Net Neutrality rules have yet to be revoked–why?
Get links to all these stories after our sponsor messages.
Find out how Cisco and its trusted partners Equilibrium Security and ePlus/IGX can help your organization tackle the General Data Protection Regulation, or GDPR. Tune into Packet Pushers Priority Queue episode 147 to get practical insights on how to get your arms around these wide-ranging rules.
MyEtherWallet DNS Attack Offers Opt-In Lessons – Dark Reading
Make Way for Secure and Automated Multicloud for Any Cloud, Any Workload and Any Deployment – Juniper Networks
Juniper Preaches Multicloud To Win Contrail Converts In The Enterprise – Packet Pushers
Big Mon Recorder and Analytics Nodes Enable Traffic Capture and App-aware Analytics for Cloud-Native Network Defense & Continue reading
In 2017, the Internet Society unveiled the 2017 Global Internet Report: Paths to Our Digital Future. The interactive report identifies the drivers affecting tomorrow’s Internet and their impact on Media & Society, Digital Divides, and Personal Rights & Freedoms. In April 2018, we interviewed two stakeholders –Getachew Engida, Deputy Director-General of the United Nations Educational, Scientific and Cultural Organization (UNESCO), and Augusto Mathurin, who created Virtuágora, an open source digital participation platform – to hear their different perspectives on the forces shaping the Internet.
Augusto Mathurin is a 25-year-old Argentinian who strongly believes in the need to enable all people to participate in decision-making which can impact them and their communities. With this in mind, Augusto developed an open source digital participation platform as part of a university project. The main goal of this platform, Virtuágora, was to create a common space in which citizens’ opinions and their representatives’ proposals could converge. The concept was derived from the Greek agora – the central square of ancient Grecian cities where citizens met to discuss their society. In 2017, Augusto was awarded the Internet Society’s 25 under 25 award for making an impact in his community and beyond. (You can Continue reading
Breaking into any part of the IT stack against incumbents with vast installed bases is not easy task. Cutting edge technology is table stakes, and targeting precise customers with specific needs is the only way to get a toehold. It also takes money. Lots of money. Innovium, the upstart Ethernet switch chip maker, has all three and is set to make some inroads among the hyperscalers and cloud builders.
We told you all about Innovium back in March last year, when the company, founded by former networking executives and engineers from Intel and Broadcom, dropped out of stealth and …
Feeding The Insatiable Bandwidth Beast was written by Timothy Prickett Morgan at The Next Platform.
In 2017, the Internet Society unveiled the 2017 Global Internet Report: Paths to Our Digital Future. The interactive report identifies the drivers affecting tomorrow’s Internet and their impact on Media & Society, Digital Divides, and Personal Rights & Freedoms. In April 2018, we interviewed two stakeholders – Getachew Engida, Deputy Director-General of the United Nations Educational, Scientific and Cultural Organization (UNESCO), and Augusto Mathurin, who created Virtuágora, an open source digital participation platform – to hear their different perspectives on the forces shaping the Internet.
Getachew Engida is the Deputy Director-General of UNESCO. He has spent the past twenty years leading and managing international organizations and advancing the cause of poverty eradication, peace-building, and sustainable development. He has worked extensively on rural and agricultural development, water and climate challenges, education, science, technology and innovation, intercultural dialogue and cultural diversity, communication and information with emphasis on freedom of expression, and the free flow information on and offline. (You can read Augusto Mathurin’s interview here).
The Internet Society: You have, in the past, stressed the role that education has played in your own life and can play in others’ lives. Do you see technology helping to promote literacy and Continue reading
Blockchain takes on censorship: Students looking into sexual harassment accusations involving a professor at Peking University in China wrote a letter accusing the school of trying to silence one of them, but the letter was removed from social media outlets for “violating rules.” So some supporters distributed the letter using the Ethereum blockchain, reports Yahoo finance.
Why routing security matters: Hackers used a well-known weakness in Border Gateway Protocol routing to hijack Amazon Web Services’ DNS traffic for about two hours last Tuesday. Attackers were able to redirect an Ethereum wallet developer’s website to a phishing site and steal about $150,000 from MyEtherWallet.com users, ZDNet reports.
Hacking-for-hire site attacked: In this case, law enforcement agencies from 12 countries were the people who shut down hacking-for-hire site Webstresser.org. The site had 136,000 customers and its hackers launched more than 4 million DDoS attacks in recent years, according to Europol. GovTech.com has a story.
Inspecting the IoT: Researchers at Princeton University are launching IoT Inspector, an open-source tool designed to give Internet of Things users insight into the security of their devices. There’s even Raspberry Pi code for the project, says The Register.
Cryptocurrency for the suits: The Continue reading
The growing amounts of data that are being generated due to such trends as the Internet of Things (IoT) and cloud computing have naturally beget the need for data scientists who can collect, analyze and, most importantly, interpret these massive stockpiles of complex information to help their companies more quickly and accurately make better business decisions to give them a competitive edge over competitors and to improve their operations and make them more efficient.
That in turn has created something of a land rush in what’s become a rapidly expanding data science platform market of more than a dozen vendors …
Playing Dominoes In Data Science was written by Jeffrey Burt at The Next Platform.