Juniper Networks Announces AI-Native Networking Platform
Bob Friday, Chief AI Officer for Juniper Networks, explains how the advanced technology is transforming operations.LangChain Support for Workers AI, Vectorize and D1
During Developer Week, we announced LangChain support for Cloudflare Workers. Langchain is an open-source framework that allows developers to create powerful AI workflows by combining different models, providers, and plugins using a declarative API — and it dovetails perfectly with Workers for creating full stack, AI-powered applications.
Since then, we’ve been working with the LangChain team on deeper integration of many tools across Cloudflare’s developer platform and are excited to share what we’ve been up to.
Today, we’re announcing five new key integrations with LangChain:
- Workers AI Chat Models: This allows you to use Workers AI text generation to power your chat model within your LangChain.js application.
- Workers AI Instruct Models: This allows you to use Workers AI models fine-tuned for instruct use-cases, such as Mistral and CodeLlama, inside your Langchain.js application.
- Text Embeddings Models: If you’re working with text embeddings, you can now use Workers AI text embeddings with LangChain.js.
- Vectorize Vector Store: When working with a Vector database and LangChain.js, you now have the option of using Vectorize, Cloudflare’s powerful vector database.
- Cloudflare D1-Backed Chat Memory: For longer-term persistence across chat sessions, you can swap out LangChain’s default Continue reading
Precedence of Ansible Extra Variables
I stay as far away from Ansible as possible these days and use it only as a workflow engine to generate device configurations from Jinja2 templates and push them to lab devices. Still, I manage to trigger unexpected behavior even in these simple scenarios.
Ansible has a complex system of variable (fact) precedence, which mostly makes sense considering the dozen places where a variable value might be specified (or overwritten). Ansible documentation also clearly states that the extra variables (specified on the command line with the -e keyword) have the highest precedence.
Now consider these simple playbooks. In the first one, we’ll set a fact (variable) and then print it out:
Precedence of Ansible Extra Variables
I stay as far away from Ansible as possible these days and use it only as a workflow engine to generate device configurations from Jinja2 templates and push them to lab devices. Still, I manage to trigger unexpected behavior even in these simple scenarios.
Ansible has a complex system of variable (fact) precedence, which mostly makes sense considering the dozen places where a variable value might be specified (or overwritten). Ansible documentation also clearly states that the extra variables (specified on the command line with the -e keyword) have the highest precedence.
Now consider these simple playbooks. In the first one, we’ll set a fact (variable) and then print it out:
NX-OS Forwarding Constructs For VXLAN/EVPN
In this post we will look at the forwarding constructs in NX-OS in the context of VXLAN and EVPN. Having knowledge of the forwarding constructs helps both with understanding of the protocols, but also to assist in troubleshooting. BRKDCN-3040 from Cisco Live has a nice overview of the components involved:
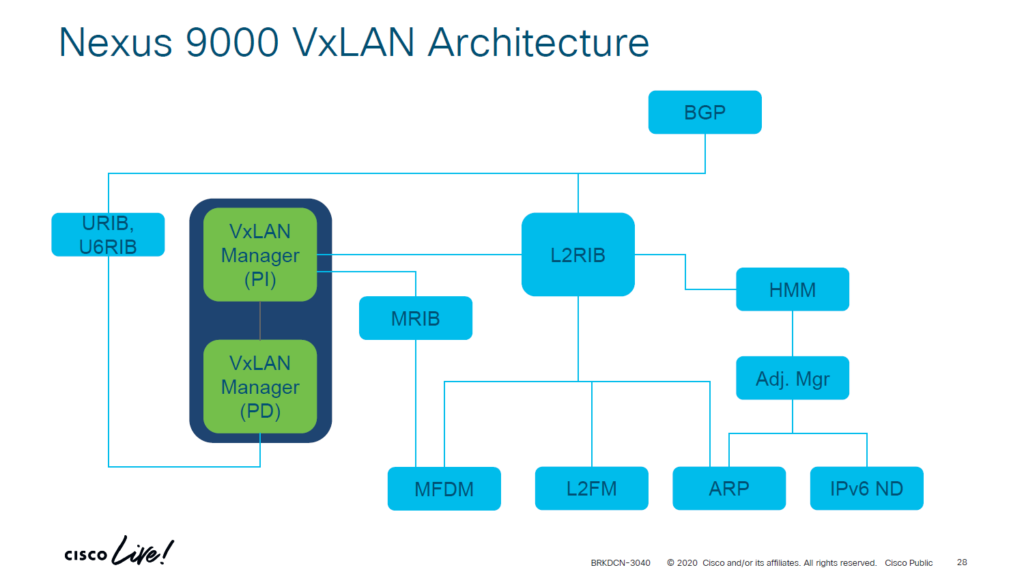
There are components that are platform independent (PI) and platform dependent (PD). Below I’ll explain what each component does:
- ARP – Information from ARP requests/responses is needed to build adjacencies. The information learned from ARP is used to populate IP address field in RT2 and hence also to populate the ARP suppression cache.
- IPv6 ND – ND fills the role of ARP, but for IPv6.
- Adjacency Manager – Resolves directly attached hosts MAC addresses.
- Host Mobility Manager – Tracks the endpoints and their movements.
- L2FM – The Layer2 Forwarding Manager. A platform dependent component that programs ASICs for L2 forwarding. Keeps track of MAC addresses, their placement and moves, and synchronizes this information across ASICS, line cards, and vPC peers when vPC is in use.
- MFDM – Multicast Forwarding Database Manager. A platform dependent component that programs ASICs with information to perform multicast forwarding.
- L2RIB – The component that handles Continue reading
NetFlow data and its fields vs packet capture
The post NetFlow data and its fields vs packet capture appeared first on Noction.
Hull and cabin
When it comes to working with steel it is a bit outside my comfort zone so I got the professionals in to do the blacking of the hull and a few different things to the cabin shell.
Supermicro Racks Up The AI Servers And Rakes In The Big Bucks
It was only six months ago when we were talking about how system maker Supermicro was breaking through a $10 billion annual revenue run rate and was setting its sights on a $20 billion target. …
Supermicro Racks Up The AI Servers And Rakes In The Big Bucks was written by Timothy Prickett Morgan at The Next Platform.
ICANN Launches 10-Year, $200 Million Program to Expand and Protect Internet Ecosystem
The grant program will support the next phase of global Internet growth and will emphasize digital inclusivity.BGP Labs: Override Neighbor AS Number in AS Path
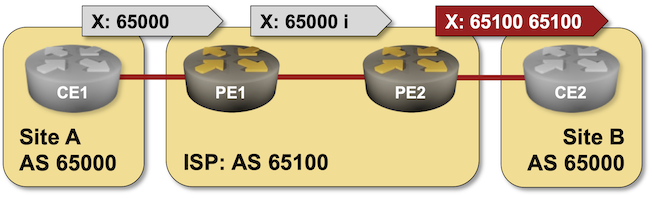
When I described the need to turn off the BGP AS-path loop prevention logic in scenarios where a Service Provider expects a customer to reuse the same AS number across multiple sites, someone quipped, “but that should be fixed by the Service Provider, not offloaded to the customer.”
Not surprisingly, there’s a nerd knob for that (AS override), and you can practice it in the next BGP lab exercise: Fix AS-Path in Environments Reusing BGP AS Numbers.
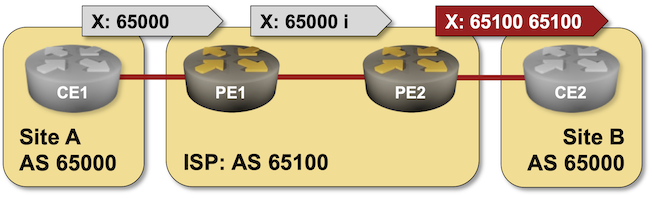
BGP Labs: Override Neighbor AS Number in AS Path
When I described the need to turn off the BGP AS-path loop prevention logic in scenarios where a Service Provider expects a customer to reuse the same AS number across multiple sites, someone quipped, “but that should be fixed by the Service Provider, not offloaded to the customer.”
Not surprisingly, there’s a nerd knob for that (AS override), and you can practice it in the next BGP lab exercise: Fix AS-Path in Environments Reusing BGP AS Numbers.
With Vista, TACC Now Has Three Paths To Its Future Horizon Supercomputer
The national supercomputing centers in the United States, Europe, and China are not only rich enough to build very powerful machines, but they are rich enough, thanks to their national governments, to underwrite and support multiple and somewhat incompatible architectures to hedge their bets and mitigate their risk. …
With Vista, TACC Now Has Three Paths To Its Future Horizon Supercomputer was written by Timothy Prickett Morgan at The Next Platform.
Understanding SASE Architecture
SASE converges the functions of network and security point solutions into a unified, global, cloud-native service. Such capabilities provide enterprises with a number of benefits.Tech Bytes: Building An Automation-Ready Service Catalog With NetOrca (Sponsored)
Let’s say you’ve built a set of automations for your network infrastructure, and now you want teams or departments within your organization to use those automations. Our Tech Bytes sponsor NetOrca offers a service catalog that provides a simple front-end to make it easy for internal customers to come and consume those capabilities you’ve worked... Read more »NB464: Juniper Begins AI Push Into The Data Center; VMware Customers Confront Higher Prices
This week we discuss new products from Juniper including synthetic testing software for its Mist wireless networks and its first step toward integrating its Apstra data center software with AI. VMware clarifies its product strategy as customers face rising prices, and undersea cables in the Red Sea face potential threats. Nokia and Chinese mobile device... Read more »Cerebras To Ride The AI Wave To An IPO This Year?
Having commercialized its waferscale AI computing platform to a certain extent over the past several year, Cerebras Systems reportedly wants to get an initial public offering done before the AI hype peaks. …
Cerebras To Ride The AI Wave To An IPO This Year? was written by Tobias Mann at The Next Platform.