BGP Route Reflector routing loop problem !
BGP Route reflector routing loop arise in IP networks. In this post, I will illustrate the topology which will loop the IP packets between the routers and I will describe multiple possible solution and share a best practice to design BGP Route Reflector in an IP network. BGP Route Reflector Routing loop […]
The post BGP Route Reflector routing loop problem ! appeared first on Cisco Network Design and Architecture | CCDE Bootcamp | orhanergun.net.
 I made a couple changes to the RouterJockey store this week and I wanted to make sure I got the word out. Previously the store worked in sprints that I tried to open up 2-3x a year. Instead of trying to manage these sprints, and keep the products updated, I’ve now made the store available year round. It still operates in sprints, but instead of being 2-3 weeks long, they’re only 3-4 days each.
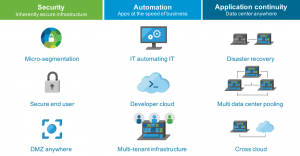
I made a couple changes to the RouterJockey store this week and I wanted to make sure I got the word out. Previously the store worked in sprints that I tried to open up 2-3x a year. Instead of trying to manage these sprints, and keep the products updated, I’ve now made the store available year round. It still operates in sprints, but instead of being 2-3 weeks long, they’re only 3-4 days each. Broader system support, security, and automation are added to EE tiers.
Broader system support, security, and automation are added to EE tiers. The company and its trial partners are pushing for this to become part of the 5G standard.
The company and its trial partners are pushing for this to become part of the 5G standard. Adtran’s Mosaic OS gives CenturyLink a way to interact with its PON technology.
Adtran’s Mosaic OS gives CenturyLink a way to interact with its PON technology.