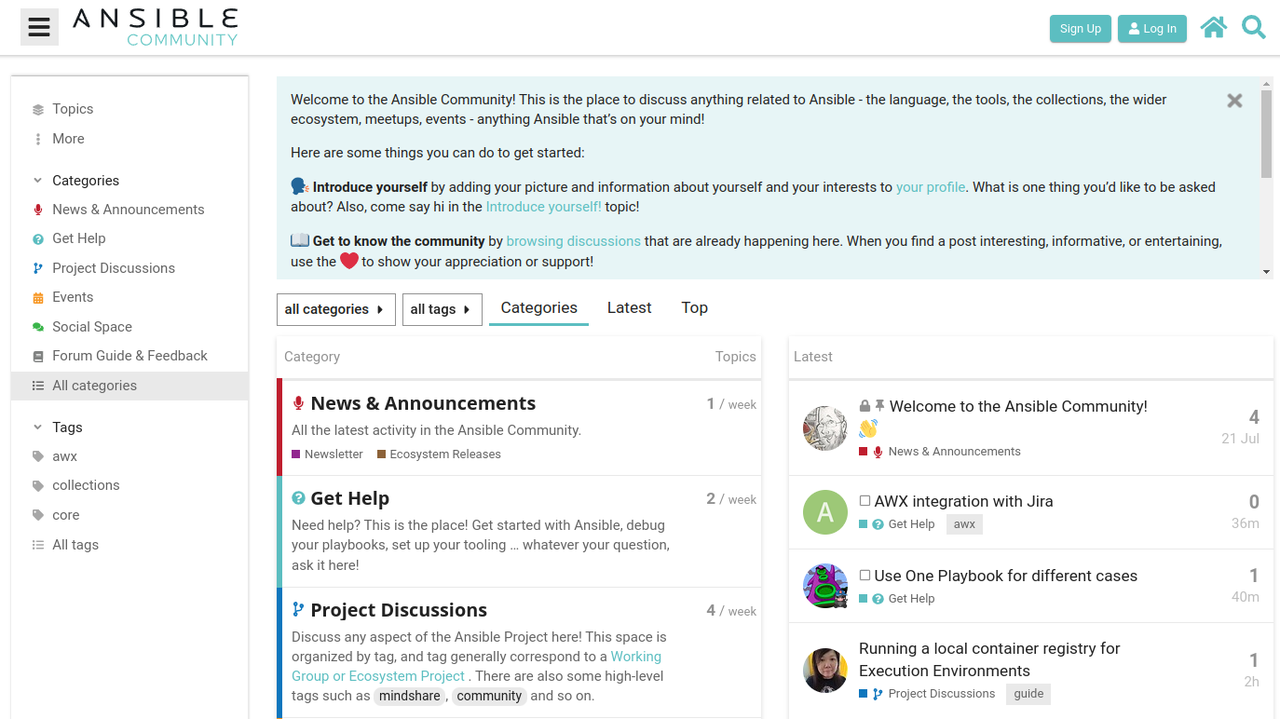
Using the comm command to compare files or directories on Linux
The comm command on Linux systems can compare file or directory contents and display the differences in a clear and useful way. Think of “comm” not so much as a reference to “compare” as to “common,” since the command writes to standard output both the lines that are common and the lines that are unique in each of the files or directories.One key requirement when using comm is that the content to be compared must be in sorted order. However, there are ways that you can get away with comparing content that isn’t sorted. Some examples of how to do this will be presented in this post.Comparing files Normally, when using the comm command, you would compare two sorted text files to see their shared and unique lines. Here’s an example in which a list of friends and a list of neighbors are compared.To read this article in full, please click here