Announcing Virtual DNS: DDoS Mitigation and Global Distribution for DNS Traffic
It’s 9am and CloudFlare has already mitigated three billion malicious requests for our customers today. Six out of every one hundred requests we see is malicious, and increasingly, more of that is targeting DNS nameservers.
DNS is the phone book of the Internet and fundamental to the usability of the web, but is also a serious weak link in Internet security. One of the ways CloudFlare is trying to make DNS more secure is by implementing DNSSEC, cryptographic authentication for DNS responses. Another way is Virtual DNS, the authoritative DNS proxy service we are introducing today.
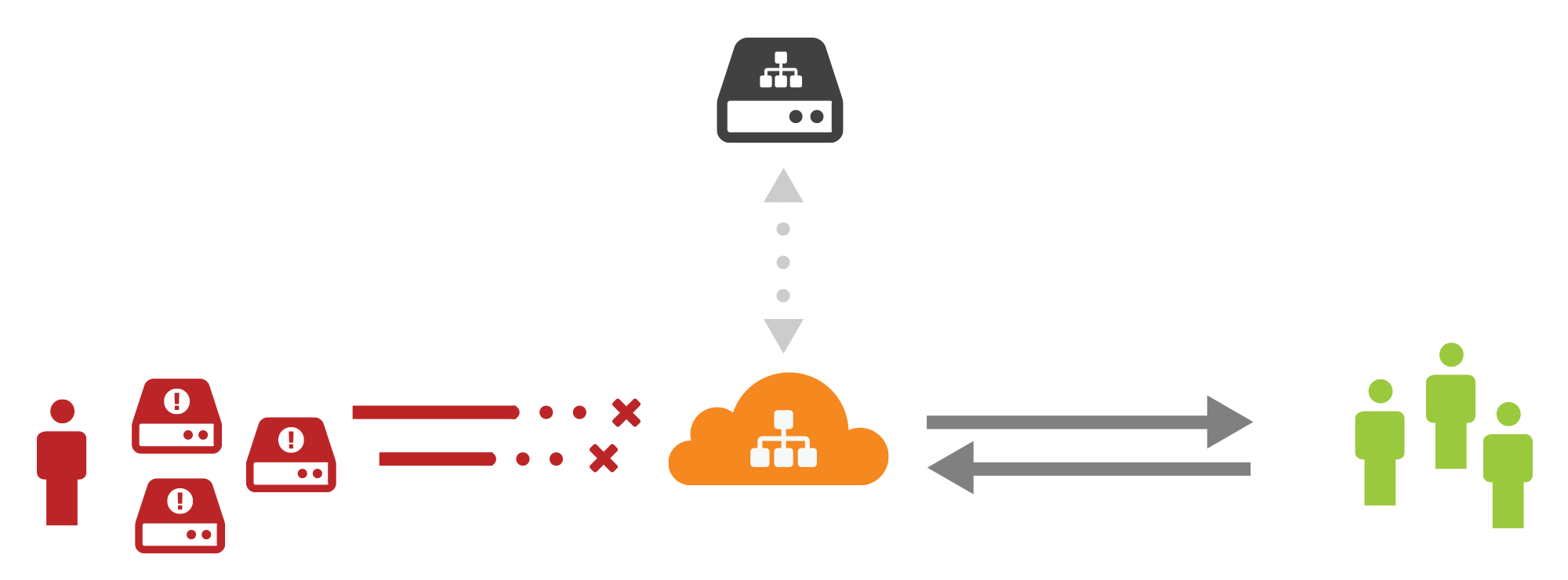
Virtual DNS provides CloudFlare’s DDoS mitigation and global distribution to DNS nameservers. DNS operators need performant, resilient infrastructure, and we are offering ours, the fastest of any providers, to any organization’s DNS servers.
Many organizations have legacy DNS infrastructure that is difficult to change. The hosting industry is a key example of this. A host may have given thousands of clients a set of nameservers but now realize that they don't have the performance or defensibility that their clients need.
Virtual DNS means that the host can get the benefits of a global, modern DNS infrastructure without having to contact every customer Continue reading
Whitebox Switching and Open-Source Networking Are not SDN
One of my readers left this comment to the Four Paths to SDN blog post:
You didn't mention Cumulus. SDN protocols become much less important when you have an open Linux switch platform. You can compile and install your own management daemon and implement whatever protocol best suits the task (and blend local and remote control).
Here’s my usual response to this line of thinking:
Read more ...CCIE R&S – By the Numbers
When I started studying in earnest for my CCIE, I started a log of how I was spending my time studying, which books and papers I’d read, videos I’d watched, and so on. I thought it would be a neat exercise to look back afterwards at what it took to achieve this goal. I’m also somewhat self-deprecating and tend to minimize my accomplishments, so having this data is a way for me to remember that this wasn’t a small accomplishment at all.
1,041,248 bytes of digital notes taken
13,916 km traveled (8,711 mi)
1,432 total study hours
652 hours in the lab
321 hours of just reading
223 videos watched
161 hours spent watching those videos
128 PDF documents read
23 books read
5 figures worth of expenses and costs
1 completely trashed USB mouse
Beyond these numbers there’s the intangibles that went into this goal too. No vacations. Giving up free time on evenings and weekends. Not seeing friends as much. Not spending as much time with family. Maintaining focus constantly on the end goal. Constantly staying up late and getting up early.
Looking back at all of this, I realize that becoming CCIE certified isn’t just about Continue reading
Cisco Live Europe 2015 – and the year ahead
Cisco Live Europe 2015
Commonly known as the biggest networking/’networking’ event in the industry for Europe, Cisco Live has something for everyone. Some great breakout technical sessions, meet the engineer, the World of Solutions and of course this year, the DevNet hall that also had a weekend hackathon which this blogger would have loved to have taken part in.
It was pretty obvious (you would have to be blind and deaf not to notice) that whilst walking around the Milano Congressi venue that houses the event, that Cisco have cottoned on to the idea that a copy and replace of product names to ‘software defined <$PRODUCT>’ is a bit of a unique to them tide turner. There are only so many ways problems like ‘resistance to change’ and the ‘adoption of technology to a risk averse’ industry can be addressed. If everything is based on the same naming schema, then the problem becomes less of a thing. Even if people use the same product they used before with a different name, guess what, it’s now software defined and the maturity cycle is already under way. Clever move. Not that I appreciate new startups calling everything software or hardware defined. Yikes. Continue reading