Introducing Cache Analytics
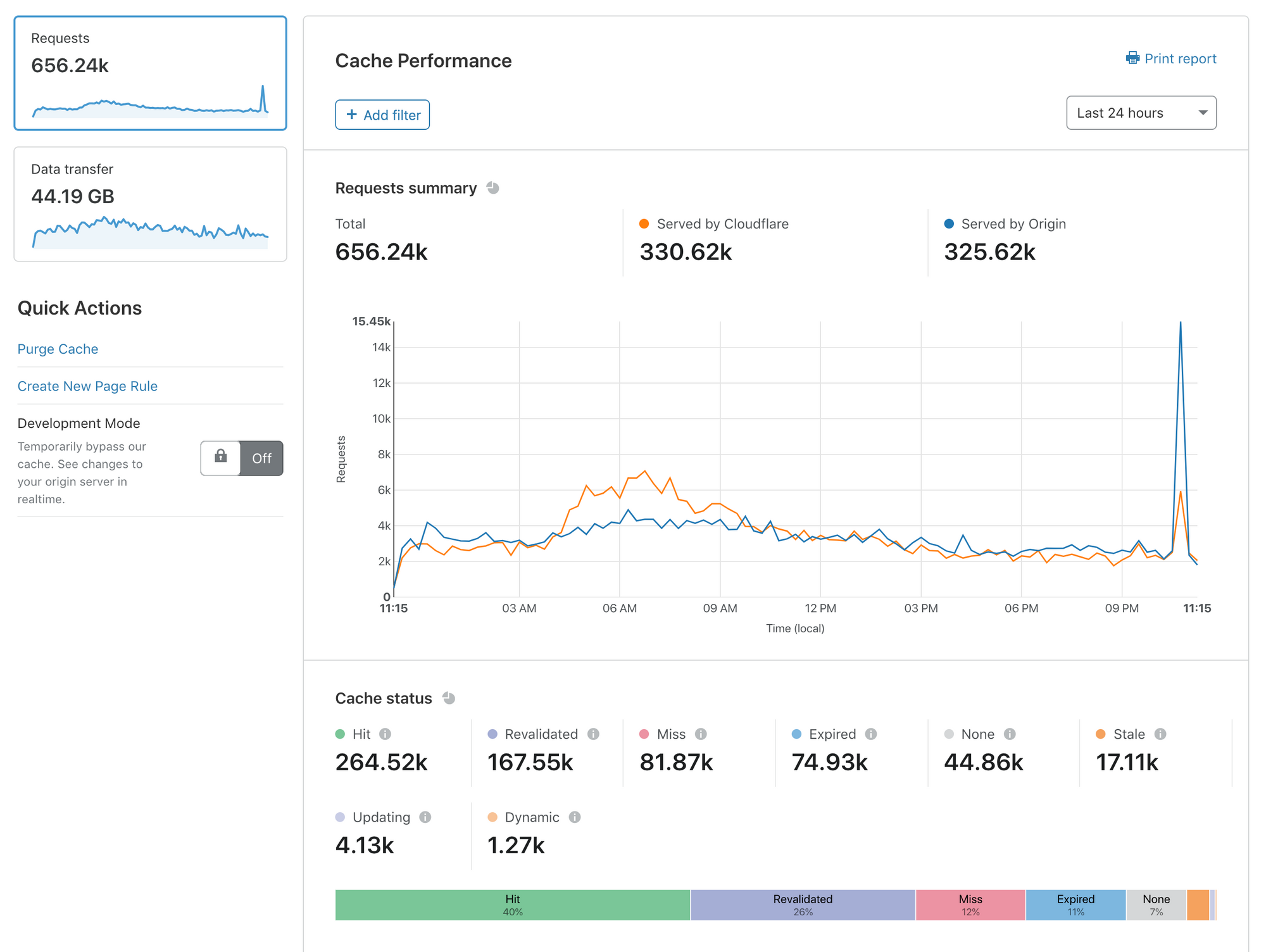
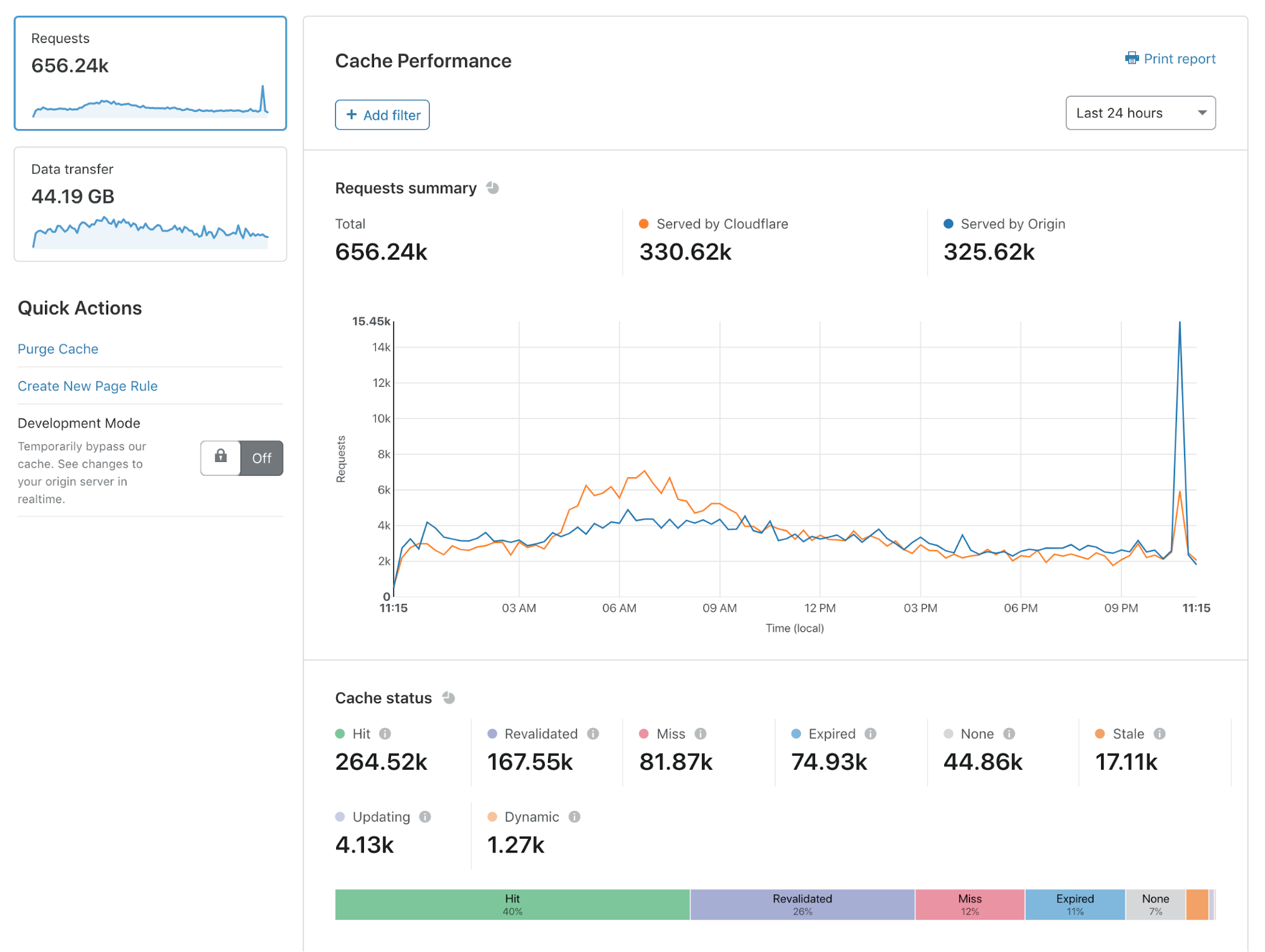
Today, I’m delighted to announce Cache Analytics: a new tool that gives deeper exploration capabilities into what Cloudflare’s caching and content delivery services are doing for your web presence.
Caching is the most effective way to improve the performance and economics of serving your website to the world. Unsurprisingly, customers consistently ask us how they can optimize their cache performance to get the most out of Cloudflare.
With Cache Analytics, it’s easier than ever to learn how to speed up your website, and reduce traffic sent to your origin. Some of my favorite capabilities include:
- See what resources are missing from cache, expired, or never eligible for cache in the first place
- Slice and dice your data as you see fit: filter by hostnames, or see a list of top URLs that miss cache
- Switch between views of requests and data Transfer to understand both performance and cost
Cache Analytics is available today for all customers on our Pro, Business, and Enterprise plans.
In this blog post, I’ll explain why we built Cache Analytics and how you can get the most out of it.
Why do we need analytics focused on caching?
If you want Continue reading


