NB575: AI Multipath Protocol Goes to Open Compute Project; Cisco Shrinks Workforce as Income Swells
Take a Network Break! In this week’s Red Alert we suggest an audit of your Azure environment after Microsoft says it patched four critical vulnerabilities. On the news front, Nvidia has brought the Multipath Reliable Connection (MCR) protocol to the Open Compute Project, AT&T rolls out quantum-resistant SD-WAN services, and HPE introduces new Wi-Fi automation... Read more »Project Glasswing: what Mythos showed us
For the last few months, we've been testing a range of security-focused LLMs on our own infrastructure. These LLMs help identify potential vulnerabilities in our own systems, so we can fix them – and they also show us what attackers are going to be able to do with the latest models.
None of these LLMs has captured more attention than Mythos Preview, from Anthropic. A few weeks ago, we were invited to use Mythos Preview as part of Project Glasswing. We soon pointed it at more than fifty of our own repositories – to see what it would find, and to see how it works.
This post shares what we observed, what the models did well and what they didn't, and how the architecture and process around them needs to change, so they can be used at scale.
Mythos Preview is a real step forward, and it's worth saying that plainly before getting into anything else. We've been running models against our code for a while now, and the jump from what was possible with previous general-purpose frontier models to what Mythos Preview does today is not just a refinement of what came before.
It's Continue reading
Goodbye, Ubuntu 20.04 (netlab 26.05)
netlab release 26.05 is out. I’ll write about its highlights tomorrow; today, I want to focus on one of its breaking changes: netlab no longer works with Python 3.8 (which reached end-of-life in October 2024), so you can no longer install it on a vanilla Ubuntu 20.04 (which reached end of standard support a year ago).
We wanted to get rid of old Python versions for ages, but never did because Ubuntu 20.04 shipped with Python 3.8, and many netlab early adopters installed it on Ubuntu 20.04 (and the last thing a networking engineer wants is wasting time with upgrades, right?).
Automatic SSL with Caddy, Cloudflare and Let’s Encrypt
I run a lot of applications and services in my homelab, and they usually look something like http://10.10.10.10:8000, http://10.10.10.11:8006, and so on. It works, but it comes with a few annoyances. Browsers constantly complain you about insecure connections, and remembering which IP and port maps to which service gets old fast.
The ideal setup is something like https://netbox-lab.yourdomain.com - a proper domain name with a valid SSL certificate and no port numbers to remember. In this post, I'll show you how to get there using Caddy, Cloudflare, and Let's Encrypt with very minimal effort.
Overview
To make this work, we need the following.
- A Cloudflare account with a domain (You don't necessarily need Cloudflare. Other DNS providers should work the same way, but this post uses Cloudflare as the example.)
- An LXC or VM to run Caddy
- A Cloudflare API token with DNS edit permissions
- Let's Encrypt Certificates are automatically managed by Caddy
Cloudflare Setup
I already have a domain that I use in my homelab, so I name my services like app.yourdomain.com. I purchased this domain through Cloudflare and manage it there.
To generate an API Continue reading
Using NetBox as a Dynamic Inventory Source for Nornir
If you have used Nornir before, you already know that the most common way to define your inventory is through YAML files. You list your hosts, groups, and defaults in separate files, and Nornir reads them at runtime. This works fine for small labs or quick scripts, but as your network grows, maintaining those files by hand becomes a problem. Every time you add a device, change an IP, or update a site, you have to remember to update your inventory files as well. It is easy to get out of sync.
This is where a source of truth tool like NetBox can help. NetBox is an open source network source of truth. It is a place to document your devices, IP addresses, sites, roles and pretty much anything about your network. Instead of maintaining a separate YAML inventory alongside NetBox, you can pull your inventory directly from NetBox at runtime. That way, Nornir always works with up to date data, and you only have to manage one source of truth.
In this post, we will cover how to use NetBox as a dynamic inventory source for Nornir using the nornir_netbox plugin. If you are new to Nornir, we have Continue reading
HN827: When Buffers Attack: Understanding Buffers to Better Diagnose Network Weirdness
Today’s episode covers buffers, the space between ingress and egress where a packet might have to live for a fraction of a second if the egress port is tied up transmitting other packets. This topic came courtesy of John Howard who joins Drew and Ethan as a co-host to discuss buffers with guest Rob Sherwood. How... Read more »Hedge 305: From Security to Networking
We don’t often hear the stories of those who move from some other IT career field into network engineering. Ayush Mishra, a student at University of Colorado Boulder, joins Tom and Russ to discuss why he moved from security to network engineering.
download
Lab: EVPN Asymmetric IRB with Anycast Gateways
I postponed the discussion of ARP issues with EVPN anycast gateways to keep yesterday’s blog post reasonably short. If you’re impatient and want to try that out, I have just the right lab exercise for you; you’ll have to extend VLANs into end-to-end MAC-VRF instances and add IRB and anycast gateways:

You can run the lab on your own netlab-enabled infrastructure (more details), but also within a free GitHub Codespace or even on your Apple-silicon Mac (installation, using Arista cEOS container, using VXLAN/EVPN labs).
Cisco AUTOCOR Passed
Yesterday I took and passed the Cisco AUTOCOR (previously DEVCOR) exam which is the core exam for CCNP Automation. That means I need a specialist exam to become CCNP Automation certified. It also means I’m qualified to sit the CCIE Automation lab.
What did I think of the exam?
As with any exam, there is good and bad. I’ll start with the good.
The exam aligned well with the blueprint. I didn’t feel there were any real surprises or questions on items that weren’t part of the blueprint.
There wasn’t a lot of trivia. No memorization of specific API endpoints or anything like that.
The exam experience was fine. I took it in a testing facility, which I prefer, and I had no issues. I was provided with earplugs which was nice to stay focused although this is a small facility and there was only one other candidate.
I liked the different types of questions. You have your standard multiple choice, single answer and multiple choice, multiple answer, but also fill in the blanks, and lablets. It’s nice that there is quite a bit of code in the exam, it is an automation exam after all. I also think it’s Continue reading
KubeVirt Live Migration Done Right: What it Takes to Run VMs on Kubernetes
Running VMs in Kubernetes sounds like a crazy workaround for avoiding vendor lock-in, and standardizing legacy applications and newer containerized workloads on one control plane with one set of security policies to govern them all. It is, however, a rapidly growing pattern, and KubeVirt live migration — moving running VMs between nodes without downtime — is increasingly central to platform engineering use cases that require full VMs, like on-demand CI/CD pipelines.
KubeVirt is gaining traction as a way to bring VMs into Kubernetes as first-class workloads, managed with the same tools and primitives that platform teams already use for containers. It has, however, introduced some unique challenges.
Here’s the uncomfortable truth about that migration: compute and storage are the easy parts. Networking is where migrations stall, roadblock multiple, and platform teams start questioning whether KubeVirt was the right call in the first place.
If your VMs have no fixed IP dependencies, no VLAN memberships, and no upstream firewall rules scoped to specific subnets, you can migrate them into Kubernetes without losing sleep over the networking layer. If you’re running hundreds or thousands of VMs with IP addresses hardcoded into application configs, DNS entries, and firewall ACLs — and you need Continue reading
The AI Agent Accountability Crisis: Why Governance Isn’t Keeping Up With Deployment
Every enterprise is building AI agents. Marketing has one summarizing campaign performance. Engineering has one triaging incidents. Customer support has one resolving tickets. Finance has one processing invoices. Each was built by a different team, using a different framework, with different assumptions about security.
Now those agents are talking to each other through agent-to-agent (A2A) communication. The incident-triage agent calls the customer-support agent to check affected accounts. The invoice agent calls an external payment API. The marketing agent queries a data warehouse with customer records.
When something goes wrong (and at this scale of deployment, it will), can you answer:
- Who authorized the action?
- What policy permitted it?
- What was the full chain of events?
If you can’t, you have an accountability gap.
This is part one of a five-part series on AI agent accountability for engineering and security leaders. We’ll work through the gap between agent deployment and governance, the diagnostic framework that exposes it, why your existing tools won’t close it, and the principles you’ll need to evaluate any solution that claims it can.
What is AI agent accountability?
AI agent accountability is the ability to trace, prove, and audit every action an AI agent takes. This includes Continue reading
IPB200: Yes, IPv6 Is Complicated. IPv8 Won’t Help
Why is IPv6 so much more complicated than IPv4? Could a newer version such as IPv8 be the solution? Guest Brian Carpenter joins our hosts to explain that many of IPv6’s complications are mathematical necessities. They point out that IPv6 has a 30 year head start on any IPv8 proposal that would struggle with many... Read more »N4N055: A Wired NAC Walkthrough
Today’s topic is Network Access Control (NAC) for a wired network. To help walk us through it all is Jennifer “JJ” Jabbusch, a network security architect, public speaker, book author, and co-host of the Packet Protector podcast. JJ and our hosts break down the terms and protocols behind NAC, and explain why the architecture was... Read more »Our billing pipeline was suddenly slow. The culprit was a hidden bottleneck in ClickHouse
At Cloudflare, we are heavy users of ClickHouse, an open-source analytical database management system. We redesigned one of our largest ClickHouse tables to add a column to the partitioning key. The change enabled per-tenant retention on a table that serves hundreds of internal teams. The design went through several rounds of revision and review with engineers across multiple teams before we landed on the final approach. But a few weeks after rollout, the jobs that produce most of Cloudflare's bills were running up against their hard daily deadline.
All the usual suspects looked clean: I/O, memory, rows scanned, parts read. Everything we would normally check when a ClickHouse query is slow appeared to be normal. The problem turned out to be lock contention in query planning, something we'd never had reason to look for before.
This is the story of how this migration exposed a hidden bottleneck in ClickHouse's internals, and the patches we wrote to fix it.
We use ClickHouse to store over a hundred petabytes of data across a few dozen clusters. To simplify onboarding for our many internal teams, we built a system called "Ready-Analytics" in early 2022.
The premise is Continue reading
ARP with EVPN Asymmetric IRB
In a previous blog post, I described the ARP issues you’ll encounter when using centralized routing (on a spine switch) between two EVPN MAC-VRF instances (a fancy name for a VLAN encapsulated in VXLAN or MPLS).
That blog post established a baseline that will help us unravel the ARP behavior in a more realistic scenario: asymmetric Integrated Routing and Bridging (IRB). That’s a mouthful, but it’s really quite a simple concept; the following diagram explains the asymmetric forwarding behavior:
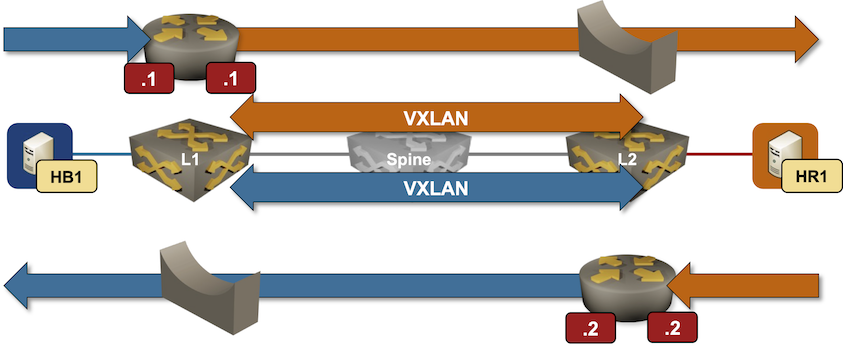
Packet forwarding in an EVPN asymmetric IRB design
Toxic Flows: When Your AI Agent Skill Becomes a Supply Chain Attack
When a developer installs an AI agent skill – granting it access to secured IT resources and data – they make a significant trust decision.What’s New in Calico v3.32
We’re excited to announce the release of Calico Open Source v3.32! 
This release corresponds with Kubernetes v1.36 (Codename Haru) and it goes beyond just sharing a cat as the mascot of the release, it actually extends capabilities and features of Kubernetes to keep you up to date with the latest innovations of the cloud.
This release brings some of the most significant architectural changes in Calico, from live-migrating KubeVirt VMs to eBPF based Maglev load balancer.
Here’s a quick look at everything that’s new:
 Breaking Changes & Deprecations
Breaking Changes & Deprecations
- ClusterNetworkPolicy (Alpha2) replaces Admin and Baseline Admin Network Policies:
AdminNetworkPolicyandBaselineAdminNetworkPolicyhave been removed. You must migrate toClusterNetworkPolicybefore upgrading to v3.32, as Calico will no longer enforce the old resources. calico-apiserverDeprecated: The aggregated API server is deprecated and will be removed in a future release. It is being replaced by Native v3 CRDs. (Requires MutatingAdmissionPolicy feature gate, Kubernetes 1.30+).
 Key Feature Updates
Key Feature Updates
1. KubeVirt VM Live Migration Support
- What it does: Allows live-migrating KubeVirt VMs between nodes without dropping TCP connections.
- How it works: Achieves IP persistence by binding the IP to the VM name rather than the ephemeral pod.
- Activation: Set
kubeVirtVMAddressPersistence: EnabledContinue reading
 Breaking Changes & Deprecations
Breaking Changes & Deprecations Key Feature Updates
Key Feature Updates