Cisco Warns of ‘Continued Attempts’ to Exploit Critical Bug
Cisco disclosed more than two dozen vulnerabilities in its network automation software and one...
Deep Dive: How Do Banks Score on Privacy and Security?

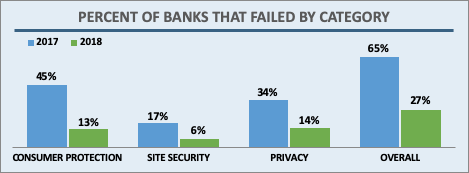
In April 2019 the Internet Society’s Online Trust Alliance published its 10th annual Online Trust Audit & Honor Roll assessing the security and privacy of 1,200 top organizations. The Banking sector includes the top 100 banks in the U.S., based on assets according to the Federal Deposit Insurance Corporation (FDIC). Banks had a standout year, with a dramatic increase in scores across the board. Let’s take a closer look.
Overall, 73% of banks made the Honor Roll, putting the banking sector 4th behind the News and Media (78%), Consumer Services (85%), and the U.S. Federal Government (91%) sectors. In the previous Audit, only 27% made the grade. This large jump is due to improvements in all three scoring categories: email authentication, site security, and privacy.
Banks, like most sectors, came close to 100% adoption in the two main email security technologies studied in the Audit: SPF (93%) and DKIM (87%). In addition, banks saw a marked improvement in how many sites implemented both both technologies at 87% in 2018, up from 60% in 2017. This puts banks among the most improved sectors in this area.
DMARC builds on SPF and DKIM results, provides a means for Continue reading
HTTP/3: the past, the present, and the future

During last year’s Birthday Week we announced preliminary support for QUIC and HTTP/3 (or “HTTP over QUIC” as it was known back then), the new standard for the web, enabling faster, more reliable, and more secure connections to web endpoints like websites and APIs. We also let our customers join a waiting list to try QUIC and HTTP/3 as soon as they became available.
Since then, we’ve been working with industry peers through the Internet Engineering Task Force, including Google Chrome and Mozilla Firefox, to iterate on the HTTP/3 and QUIC standards documents. In parallel with the standards maturing, we’ve also worked on improving support on our network.
We are now happy to announce that QUIC and HTTP/3 support is available on the Cloudflare edge network. We’re excited to be joined in this announcement by Google Chrome and Mozilla Firefox, two of the leading browser vendors and partners in our effort to make the web faster and more reliable for all.
In the words of Ryan Hamilton, Staff Software Engineer at Google, “HTTP/3 should make the web better for everyone. The Chrome and Cloudflare teams have worked together closely to bring HTTP/3 and QUIC from nascent standards to widely Continue reading
Volta Networks Virtualizes Routing on Edgecore White Boxes
Volta Networks aims to squeeze legacy vendors’ service provider business by bringing its virtual...
Hey Dropbox, I Don’t Want The Bloat. Or the Constant Ads.

TL-DR: Dropbox is harassing me about new products. Combined with poor performance of their bloated app and enormous waisting of my disk space, I’m getting close to quitting. I want to use Dropbox to synchronise files between my various devices aka desktop, laptop, tablet and smartphone for quite some time. I like it enough to […]
The post Hey Dropbox, I Don’t Want The Bloat. Or the Constant Ads. appeared first on EtherealMind.
Upcoming Events and Webinars (October 2019)
The autumn 2019 webinar season is in full swing ;) We’re almost done with Azure Networking webinar (the last session will take place on October 10th) and the network automation course is nicely chugging along – a few weeks ago Matthias Luft talked about supply-chain security in open-source software and today we’ll enjoy the start with a single source of truth presentation by Damien Garros.
Dinesh Dutt is coming back on October 8th with another installment of EVPN saga, this time focused on running EVPN on Linux hosts, and on October 22nd Donald Sharp will tell us all about the underlying magic box – the Free Range Routing software.
But there are even more open-source goodies waiting for you: on October 15th we’ll have Pete Lumbis describing the new features Cumulus Linux got in the last year, including AutoBGP and AutoMLAG.
Most everything I mentioned above apart is accessible with Standard ipSpace.net Subscription, and you’ll need Expert Subscription to enjoy the automation course contents.
Matt Oswalt – Portfolio
Short Bio Matt Oswalt hails from Portland, OR, and focuses on the intersection of network infrastructure, automation, systems, and software engineering. He’s passionate about enabling engineers to evolve their careers to the next level, and sharing the bright spots that exist within the technology industry with the masses. You can often find him speaking at conferences or meetups about these topics, as well as writing about them on his blog (https://keepingitclassless.The Bookshelf
I am a big fan of Audible for books. Every once in a while I have time and patience to read a physical book, but often times I find myself needing to do things like washing dishes, going on a long walk or drive, and Audible has made it so much easier for me to get back into “reading”. Since I started doing this, I’d like to share the books that I’ve been able to get through this way.LF Edge Sharpens Its Focus With Baetyl, Fledge
China's Baidu donated the Baetyl seed code, while Dianomic contributed Fledge.
EVPN-PIM: Anycast VTEPs
This is the second of the two part EVPN-PIM blog series exploring the feature and network deployment choices. If you missed part one, learn about BUM optimization using PIM-SM here.
Anycast VTEPs
Servers in a data-center Clos are typically dual connected to a pair of Top-of-Rack switches for redundancy purposes. These TOR switches are setup as a MLAG (Multichassis Link Aggregation) pair i.e. the server sees them as a single switch with two or more bonded links. Really there are two distinct switches with an ISL/peerlink between them syncing databases and pretending to be one.

The MLAG switches (L11, L12 in the sample setup) use a single VTEP IP address i.e. appear as an anycast-VTEP or virtual-VTEP.
Additional procedures involved in EVPN-PIM with anycast VTEPs are discussed in this blog.
EVPN-PIM in a MLAG setup vs. PIM-MLAG
Friend: “So you are working on PIM-MLAG?”
Me: “No, I am implementing EVPN-PIM in a MLAG setup”
Friend: “Yup, same difference”
Me: “No, it is not!”
Friend: “OK, OK, so you are implementing PIM-EVPN with MLAG?”
Me: “Yes!”
Friend: “i.e. PIM-MLAG?”
Me: “Well, now that you put it like that….……..NO, I AM NOT!! Continue reading
Oracle Slashes Data Cloud Workforce
Oracle reportedly cut 10% to 15% of its Data Cloud business unit this week amid its ongoing...
Why Every Size IT Team Should Strive to Implement a Software-Defined Data Center (SDDC)
Part One of a Five-Part Series on Software-Defined Data Centers in a Multi-Cloud World Business of all shapes and sizes...Alibaba Unsheaths AI Chip, Goes Head-to-Head With AWS, Google
Alibaba said it developed a new chip for AI inference that speeds up machine learning tasks on its...
CloudGenix SD-WAN Arrives On Hypercore Networks
In a win for CloudGenix, Hypercore Networks today announced a partnership with the SD-WAN vendor to...
Follow the Yellowbrick Data Road to Cloud Warehousing and DR
With the addition of its cloud offerings, Yellowbrick offers enterprise customers a platform to run...
Qualcomm Waxes 5G Vision, Downplays Early Challenges
Qualcomm showcased its long history of innovation in wireless technology and contends that it’s...