Weekend Reads 030323
https://cacm.acm.org/magazines/2023/3/270206-a-turning-point-for-cyber-insurance/fulltext
Insuring against the consequences of cybersecurity seems too good to be true given the underlying problem has perplexed researchers and practitioners for going on 50 years.
https://cacm.acm.org/magazines/2023/3/270207-mapping-the-privacy-landscape-for-central-bank-digital-currencies/fulltext
Payment records paint a detailed picture of an individual’s behavior. They reveal wealth, health, and interests, but individuals do not want the burden of deciding which are sensitive or private.
https://cacm.acm.org/magazines/2023/3/270211-the-ai-tech-stack-model/fulltext
Presently, enterprises have implemented advanced artificial intelligence (AI) technologies to support business process automation (BPA), provide valuable data insights, and facilitate employee and customer engagement.
https://www.theregister.com/2023/02/22/google_milestone_quantum/
Google is claiming a new milestone on the road to fault-tolerant quantum computers with a demonstration that a key error correction method that groups multiple qubits into logical qubits can deliver lower error rates, paving the way for quantum systems that can scale reliably.
https://telecoms.com/520115/mwc-2023-whats-the-point-of-5g/
Four years into the 5G era, the technology is still struggling to find an identity. 3G was about the introduction of mobile data, which matured in the form of 4G, but what is 5G all about?
https://www.theregister.com/2023/02/24/europe_gigabit_transformation_consultation/
The European Union yesterday decided it’s time to start “laying the ground for the transformation of the connectivity sector” in the region Continue reading
Ansible Limit When Using Netbox as Inventory
I’m currently using Ansible to template a large and growing number of devices for an ISP that I’m working for. The last part of the process is to use Netbox as a source of truth to write the configs using Jinja2 templates. The work is done as part of a CI/CD pipeline, and runs on a specific Gitlab Runner instance – finally the config is pre-staged onto the device’s filesystem to be checked by a engineer before deployment.
I’ve been finding the growing list of hosts a bit hard work, and, seemingly undocumented in the Netbox docs is how to put a site-specific limit on the playbook run. This is easily done in regular Ansible by using .ini-style host file groups like this:
[siteA]
sitea-router001
sitea-router002
[siteB]
siteb-router001
siteb-router002You can then do ‘ansible-playbook -l siteB’ to restrict what gets generated. How you do this when Netbox is the source of inventory is less clear.
It turns out that sites are pre-pended in Netbox with the string ‘sites_’. So, in your dynamic inventory file (in my case, called nb-inventory.yml) you need to tell it to group hosts by site by including the sites keyword under the group_by section:
plugin: Continue readingHow Cloudflare runs Prometheus at scale


We use Prometheus to gain insight into all the different pieces of hardware and software that make up our global network. Prometheus allows us to measure health & performance over time and, if there’s anything wrong with any service, let our team know before it becomes a problem.
At the moment of writing this post we run 916 Prometheus instances with a total of around 4.9 billion time series. Here’s a screenshot that shows exact numbers:
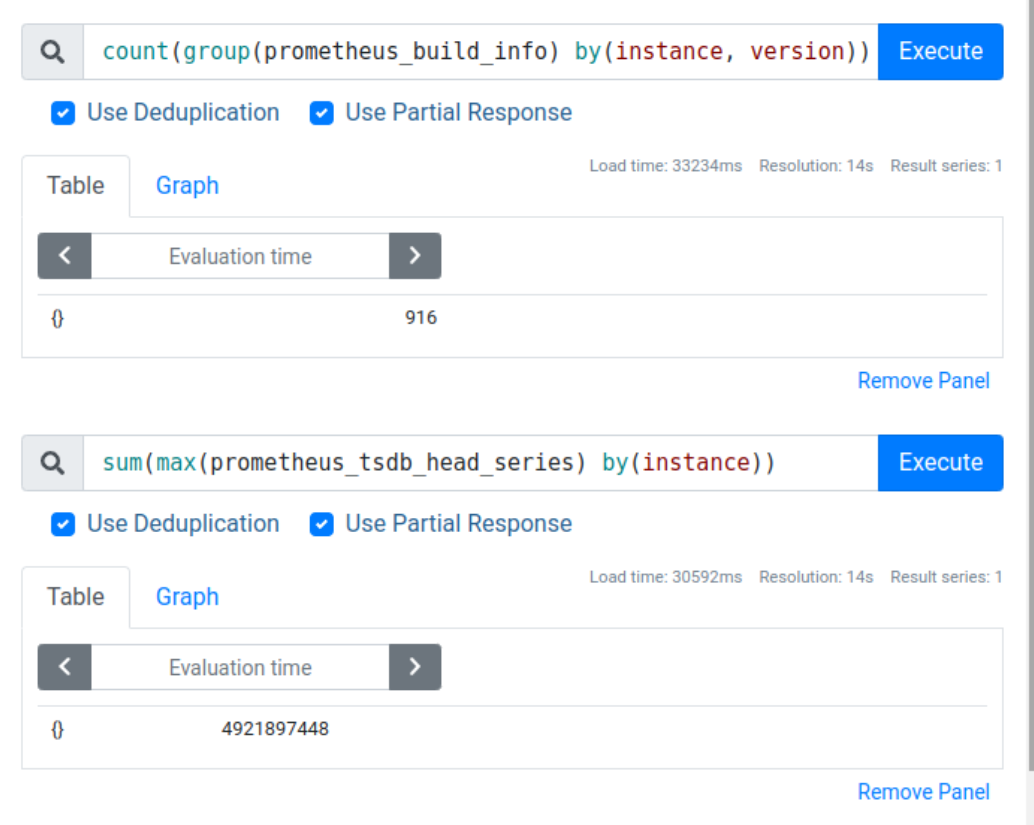
That’s an average of around 5 million time series per instance, but in reality we have a mixture of very tiny and very large instances, with the biggest instances storing around 30 million time series each.
Operating such a large Prometheus deployment doesn’t come without challenges. In this blog post we’ll cover some of the issues one might encounter when trying to collect many millions of time series per Prometheus instance.
Metrics cardinality
One of the first problems you’re likely to hear about when you start running your own Prometheus instances is cardinality, with the most dramatic cases of this problem being referred to as “cardinality explosion”.
So let’s start by looking at what cardinality means from Prometheus' perspective, when it can Continue reading
Video: Getting Started with netlab
After explaining how netlab fits into the virtual lab orchestration picture and what exactly it can do, let’s focus on what’s the easiest way to get started.
The next video in the Using netlab to Build Networking Labs series describes:
- Typical deployment scenarios: VirtualBox on Windows or MacOS, or libvirt/KVM on a Linux server or a virtual machine (running on Windows or MacOS).
- Hardware and software requirements
- Behind-the-scene operations performed by netlab create, netlab initial and netlab up commands.
Video: Getting Started with netlab
After explaining how netlab fits into the virtual lab orchestration picture and what exactly it can do, let’s focus on what’s the easiest way to get started.
The next video in the Using netlab to Build Networking Labs series describes:
- Typical deployment scenarios: VirtualBox on Windows or MacOS, or libvirt/KVM on a Linux server or a virtual machine (running on Windows or MacOS).
- Hardware and software requirements
- Behind-the-scene operations performed by netlab create, netlab initial and netlab up commands.
Introducing New Networking and Advanced Security Capabilities in NSX 4.1
We’re delighted to announce the general availability of VMware NSX 4.1, a release that delivers new functionalities for virtualized networking and advanced security for private, hybrid, and multi-clouds. This release’s new features and capabilities will enable VMware NSX customers to take advantage of enhanced networking and advanced security, increased operational efficiency and flexibility, and simplified troubleshooting.
Read on to discover the key features in the latest NSX release.
Stay Ahead of Threats and Safeguard our Network
Uncover Every Threat
NSX 4.1 introduces a new feature that allows the sending of IDS/IPS logs from the NSX Gateway firewall (GFW) to our Network Detection and Response (NDR), which is part of VMware NSX Advanced Threat Prevention (ATP). This new functionality is complementary to our existing NSX Distributed Firewall (DFW), which has had IDS/IPS logs sent to the NDR for quite some time now. With this new feature, NSX 4.1 customers can gain a more comprehensive view of network activity, allowing faster and more effective responses to threats. By analyzing IDS/IPS logs from GFW and DFW in combination with our Network Traffic Analysis (NTA) and Sandboxing, our NDR system can correlate events and identify attack patterns, providing a complete picture Continue reading
Learning EVPN? Don’t skip Route Type 3
In this post
📚 The trouble with learning RT-3s.
🎥 EVPN-VXLAN Explainer 3 is finally out!
👹 An odd choice?
After many hours of writing, recording, re-recording, and rewriting; I was finally able to release the third video in my EVPN-VXLAN Explainer series (link below). This video deals with one of the aspects of EVPN that took me a while to grasp, but is fundamental to unlocking this protocol; that being Route Type 3.
After my initial decision to tackle RT-3 as the first Route Type that I cover for this series, I started to wonder whether this may seem like an odd choice. RT-2 being the update that most are interested in, thats your actual host update.
However, the more I progressed with the video writing process, the more natural it felt to tackle RT-3s first.
After all, this is the first update that you'll see in the EVPN table or your wireshark capture, with or without end hosts.
RT-3s are fundamental to the operation of EVPN networks, no Route Type 3s, no flooding; and without that, IP networks do not run so well.
But as fundamental as RT-3s are, they do seem to be a little over-looked in Continue reading
Why, Where, and When is There a Market for 5G NR RedCap?
Until recently, 5G was focused on super high-speed networks. Now an effort has begun to expand it deep into IoT networks. Here's what IT planners need to know.Oxy is Cloudflare’s Rust-based next generation proxy framework

In this blog post, we are proud to introduce Oxy - our modern proxy framework, developed using the Rust programming language. Oxy is a foundation of several Cloudflare projects, including the Zero Trust Gateway, the iCloud Private Relay second hop proxy, and the internal egress routing service.
Oxy leverages our years of experience building high-load proxies to implement the latest communication protocols, enabling us to effortlessly build sophisticated services that can accommodate massive amounts of daily traffic.
We will be exploring Oxy in greater detail in upcoming technical blog posts, providing a comprehensive and in-depth look at its capabilities and potential applications. For now, let us embark on this journey and discover what Oxy is and how we built it.
What Oxy does
We refer to Oxy as our "next-generation proxy framework". But what do we really mean by “proxy framework”? Picture a server (like NGINX, that reader might be familiar with) that can proxy traffic with an array of protocols, including various predefined common traffic flow scenarios that enable you to route traffic to specific destinations or even egress with a different protocol than the one used for ingress. This server can be configured in many ways Continue reading
Kubernetes Unpacked 020: A Working Definition Of Kubernetes At The Edge
The edge is one of those terms that can be shaped to fit almost any use case. On today's Kubernetes Unpacked episode, host Michael Levan talks with Alan Hohn, Director of Software Strategy at Lockheed Martin, about what the defense industry means by the edge, and getting a working definition of the edge we can all live with.
The post Kubernetes Unpacked 020: A Working Definition Of Kubernetes At The Edge appeared first on Packet Pushers.
Kubernetes Unpacked 020: A Working Definition Of Kubernetes At The Edge
The edge is one of those terms that can be shaped to fit almost any use case. On today's Kubernetes Unpacked episode, host Michael Levan talks with Alan Hohn, Director of Software Strategy at Lockheed Martin, about what the defense industry means by the edge, and getting a working definition of the edge we can all live with.How we built an open-source SEO tool using Workers, D1, and Queues
Building applications on Cloudflare Workers has always been fun. Workers applications have low latency response times by default, and easy developer ergonomics thanks to Wrangler. It's no surprise that for years now, developers have been going from idea to production with Workers in just a few minutes.
Internally, we're no different. When a member of our team has a project idea, we often reach for Workers first, and not just for the MVP stage, but in production, too. Workers have been a secret ingredient to Cloudflare’s innovation for some time now, allowing us to build products like Access, Stream and Workers KV. Even better, when we have new ideas and we can use new Cloudflare products to build them, it's a great way to give feedback on those products.
We've discussed this in the past on the Cloudflare blog - in May last year, I wrote how we rebuilt Cloudflare's developer documentation using many of the tools that had recently been released in the Workers ecosystem: Cloudflare Pages for hosting, and Bulk Redirects for the redirect rules. In November, we released a new version of our API documentation, which again used Pages for hosting, and Pages functions for intelligent Continue reading