Serving Cloudflare Pages sites to the IPFS network


Four years ago, Cloudflare went Interplanetary by offering a gateway to the IPFS network. This meant that if you hosted content on IPFS, we offered to make it available to every user of the Internet through HTTPS and with Cloudflare protection. IPFS allows you to choose a storage provider you are comfortable with, while providing a standard interface for Cloudflare to serve this data.
Since then, businesses have new tools to streamline web development. Cloudflare Workers, Pages, and R2 are enabling developers to bring services online in a matter of minutes, with built-in scaling, security, and analytics.
Today, we're announcing we're bridging the two. We will make it possible for our customers to serve their sites on the IPFS network.
In this post, we'll learn how you will be able to build your website with Cloudflare Pages, and leverage the IPFS integration to make your content accessible and available across multiple providers.
A primer on IPFS
The InterPlanetary FileSystem (IPFS) is a peer-to-peer network for storing content on a distributed file system. It is composed of a set of computers called nodes that store and relay content using a common addressing system. In short, a set of participants Continue reading
Gaining visibility in IPFS systems

We have been operating an IPFS gateway for the last four years. It started as a research experiment in 2018, providing end-to-end integrity with IPFS. A year later, we made IPFS content faster to fetch. Last year, we announced we were committed to making IPFS gateway part of our product offering. Through this process, we needed to inform our design decisions to know how our setup performed.
To this end, we've developed the IPFS Gateway monitor, an observability tool that runs various IPFS scenarios on a given gateway endpoint. In this post, you'll learn how we use this tool and go over discoveries we made along the way.
Refresher on IPFS
IPFS is a distributed system for storing and accessing files, websites, applications, and data. It's different from a traditional centralized file system in that IPFS is completely distributed. Any participant can join and leave at any time without the loss of overall performance.
However, in order to access any file in IPFS, users cannot just use web browsers. They need to run an IPFS node to access the file from IPFS using its own protocol. IPFS Gateways play the role of enabling users to do this using only Continue reading
The Path the Resolverless DNS
Using the DNS without directly using recursive resolvers seems like an approach that is totally alien to the DNS as we know it, so it might be useful to ask: How did we get to this point where a resolverless form of DNS name resolution makes some sense? And, to whom does it make sense?Networking Hardware/Software Disaggregation in 2022
I started preparing the materials for the SDN – 10 years later webinar, and plan to publish a series of blog posts documenting what I found on various aspects of what could be considered SDN1. I’m pretty sure I missed quite a few things; your comments are most welcome.
Let’s start with an easy one: software/hardware disaggregation in network devices.
Open-Source Network Operating Systems
I found several widely-used open-source2 network operating systems:
Networking Hardware/Software Disaggregation in 2022
I started preparing the materials for the SDN – 10 years later webinar, and plan to publish a series of blog posts documenting what I found on various aspects of what could be considered SDN1. I’m pretty sure I missed quite a few things; your comments are most welcome.
Let’s start with an easy one: software/hardware disaggregation in network devices.
Open-Source Network Operating Systems
I found several widely-used open-source2 network operating systems:
Learning BGP Module 2 Lesson 2: Peering, Part 2 – Video
Russ White continues the discussion about BGP peering in part two of this lesson. Topics covered include: -Challenges with link-local next hop with IPv6 -How different BGP implementations handle these challenges -Promiscuous peering -Mitigating the attack surface of promiscuous peers -BGP Capabilities -Filtering before advertising/RFC 8212 You can subscribe to the Packet Pushers’ YouTube channel […]
The post Learning BGP Module 2 Lesson 2: Peering, Part 2 – Video appeared first on Packet Pushers.
Part 1: Rethinking Cache Purge, Fast and Scalable Global Cache Invalidation
There is a famous quote attributed to a Netscape engineer: “There are only two difficult problems in computer science: cache invalidation and naming things.” While naming things does oddly take up an inordinate amount of time, cache invalidation shouldn’t.
In the past we’ve written about Cloudflare’s incredibly fast response times, whether content is cached on our global network or not. If content is cached, it can be served from a Cloudflare cache server, which are distributed across the globe and are generally a lot closer in physical proximity to the visitor. This saves the visitor’s request from needing to go all the way back to an origin server for a response. But what happens when a webmaster updates something on their origin and would like these caches to be updated as well? This is where cache “purging” (also known as “invalidation”) comes in.
Customers thinking about setting up a CDN and caching infrastructure consider questions like:
- How do different caching invalidation/purge mechanisms compare?
- How many times a day/hour/minute do I expect to purge content?
- How quickly can the cache be purged when needed?
This blog will discuss why invalidating cached assets is hard, what Cloudflare has done to make Continue reading
Learning BGP Module 2 Lesson 1: Peering Part 1 – Video
The first video in this second module of Russ White’s BGP course covers peering, including why BGP uses TCP for transport, passive and active peer, multi-hop peering, collisions, and more. Russ White is a network architect, author, and instructor. You can subscribe to the Packet Pushers’ YouTube channel for more videos as they are published. […]
The post Learning BGP Module 2 Lesson 1: Peering Part 1 – Video appeared first on Packet Pushers.
Worth Reading: Using LEO and GEO Satellite Internet
Another interesting column by Geoff Huston: performance of TCP congestion control protocols when using Low-Earth Orbit or Geosynchronous Orbit satellites for Internet access.
Worth Reading: Using LEO and GEO Satellite Internet
Another interesting column by Geoff Huston: performance of TCP congestion control protocols when using Low-Earth Orbit or Geosynchronous Orbit satellites for Internet access.
Using Python to Calculate Cisco SD-WAN Tunnel Numbers – Part 1
When using Cisco SD-WAN on IOS-XE, it uses tunnel interfaces to configure parameters of the implementation. There is a mapping between what interface the tunnel is sourcing from and the name of the tunnel interface. For example, if the tunnel source is GigabitEthernet0, the tunnel interface is Tunnel0, if the tunnel source is GigabitEthernet0.100, the tunnel interface is Tunnel100000. When provisioning a router and not using Zero Touch Provisioning (ZTP), you build a small bootstrap configuration that configures mandatory parameters such as Site ID, System IP, Organization Name, but also a tunnel interface to be able to connect to the controllers. It is possible to create this configuration in vManage, and hence find out the tunnel interface name, but I thought it would be interesting to do this with code and not be dependent on vManage.
In this post, I will describe the code I used and what my logic was when creating different parts of the code. In this first post I will use the code that I came up with. In the second part, my friend Rodrigo who runs an excellent Python blog ,analyzed my code and came up with improvements, which I will describe in that Continue reading
IS-IS Average Flooding Rate
Introduction
In recent years, a lot of work has been done to scale IGPs for dense topologies, making IGPs again an interesting area. In this blog post, we will look at IS-IS Flooding and how we can measure the flooding rate, and in the future post explore Dynamic Flooding and Area Proxy.
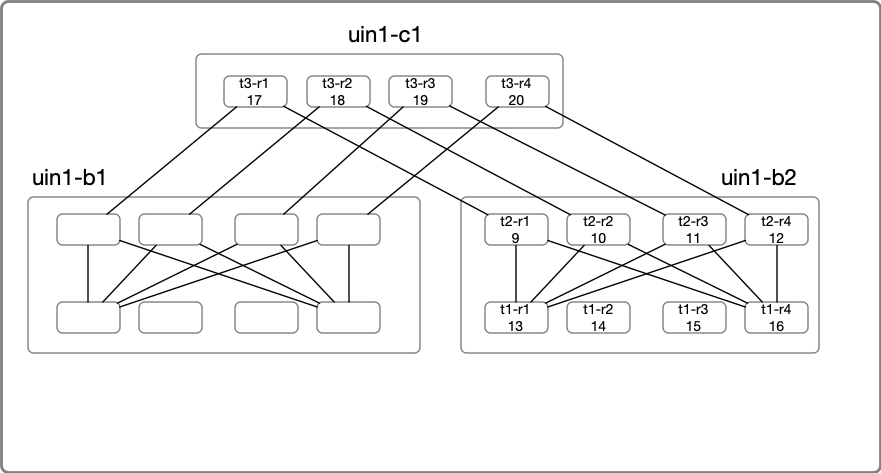
Topology Setup
For our experiment, we will use a stripped-down topology connecting Four locations. The devices are emulated using Arista cEOS, and all devices are part of a single level2 flooding domain. Topology creation was done with the help of netsim-tools and containerlabs. So my regards go to everyone involved with the tool, as it took care of the monotonous work like IP-Addressing, wiring, and base configs.
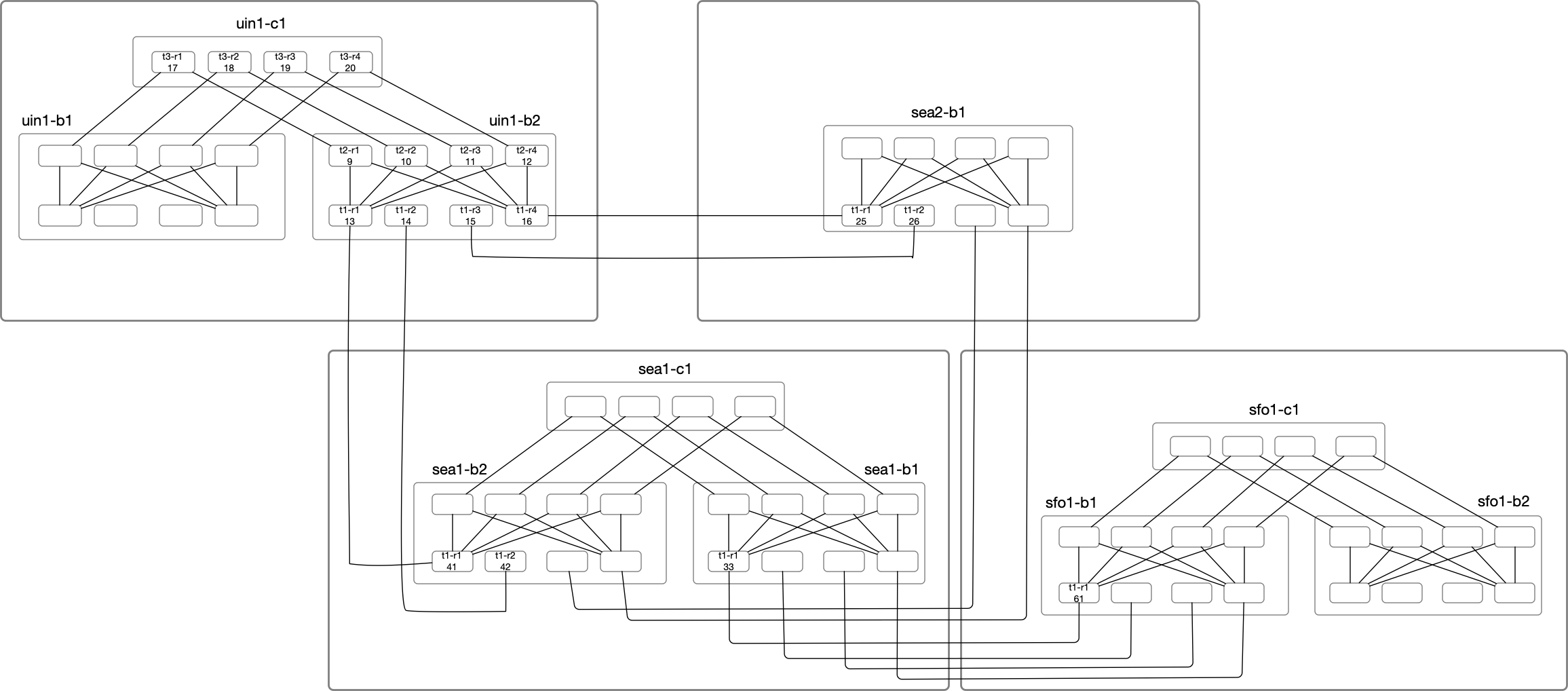
In the above diagram, Nodes under uin1-b2 will be the primary focus of our deep dive. Node Label consists of the node name
suffix and the last octet of the loopback IP. For example:
uin1-b2-t1-r1 with LSP ID of 0000.0000.0013 is highlighted as t1-r1(13) under uin1-b2 block.
uin1-b2-t2-r1 with LSP ID of 0000.0000.0009 is highlighted as t2-r1(09) under uin1-b2 block.
IS-IS Refresher
Let’s do a quick IS-IS refresher. We know that IS-IS Packets are of following types:
Learning BGP Module 1 Lesson 4: Intra-AS Models And Route Reflectors – Video
This lesson in Russ White’s BGP course delves into synchronization within an Autonomous System (AS) and confederation within an AS. It also discusses route reflectors, including how they prevent loops, route reflector clients, route reflector multi-path, and multi-path pros and cons. Russ White is a network architect, author, and instructor. You can subscribe to the […]
The post Learning BGP Module 1 Lesson 4: Intra-AS Models And Route Reflectors – Video appeared first on Packet Pushers.
Heavy Networking 630: Palo Alto Networks Introduces Okyo Garde And SD-WAN Bandwidth On Demand (Sponsored)
Today's Heavy Networking podcast explores two new offerings from sponsor Palo Alto Networks. First is Okyo Garde, a home wireless mesh appliance to connect and secure remote workers while reducing the management burden from IT. We also discuss a new licensing program to make provisioning bandwidth for branch and remote offices for Prisma SD-WAN simpler and more flexible.
The post Heavy Networking 630: Palo Alto Networks Introduces Okyo Garde And SD-WAN Bandwidth On Demand (Sponsored) appeared first on Packet Pushers.
Heavy Networking 630: Palo Alto Networks Introduces Okyo Garde And SD-WAN Bandwidth On Demand (Sponsored)
Today's Heavy Networking podcast explores two new offerings from sponsor Palo Alto Networks. First is Okyo Garde, a home wireless mesh appliance to connect and secure remote workers while reducing the management burden from IT. We also discuss a new licensing program to make provisioning bandwidth for branch and remote offices for Prisma SD-WAN simpler and more flexible.Try the Simplest Thing First to Address Hybrid Network Performance Issues
Quite often, the Wi-Fi link between a home user's computer and the in-home router is the culprit when hybrid network performance issues arise.Network Zen: The Duality of Bandwidth
 Understanding a dual nature can be hard
Understanding a dual nature can be hard
Juniper Extends Contrail To Kubernetes For Cloud-Native Virtual Networking
Juniper Networks’ network virtualization software Contrail can now integrate with Kubernetes. Originally designed for OpenStack, Juniper calls this new version of Contrail “CN2.” Contrail is a Software Defined Networking (SDN) platform for spinning up, configuring, and managing virtual networks on compute nodes rather than traditional network hardware. Contrail enables virtualized routing, switching, load balancing, and […]
The post Juniper Extends Contrail To Kubernetes For Cloud-Native Virtual Networking appeared first on Packet Pushers.