Feedback: Ansible for Networking Engineers
One of ipSpace.net subscribers sent me the following feedback on Ansible for Networking Engineers webinar:
The “Ansible for Network Engineers” webinar is of the highest caliber. I’ve taken Ansible courses with your CCIE peers, and though they are good, I objectively feel, that I get more of a total comprehensive understanding with network automation here at ipSpace. Also, I enjoy your professional care-free tone, and how you pepper humor into the subject matter.
I’ve setup a virtual lab with Ubuntu 18.04 LTS server, and am using both Aruba and Cisco switches/routers. Ansible has lots of nuances that will take me time to fully get a grip-on– but, that’s why I subscribe with the network pros like ipSpace.
Feedback: Ansible for Networking Engineers
One of ipSpace.net subscribers sent me the following feedback on Ansible for Networking Engineers webinar:
The “Ansible for Network Engineers” webinar is of the highest caliber. I’ve taken Ansible courses with your CCIE peers, and though they are good, I objectively feel, that I get more of a total comprehensive understanding with network automation here at ipSpace. Also, I enjoy your professional care-free tone, and how you pepper humor into the subject matter.
I’ve setup a virtual lab with Ubuntu 18.04 LTS server, and am using both Aruba and Cisco switches/routers. Ansible has lots of nuances that will take me time to fully get a grip-on– but, that’s why I subscribe with the network pros like ipSpace.
Tools 8. Monitoring Network Performance with Dockerised Prometheus, Iperf3 and Speedtest
Hello my friend,
in the time when the business is conducted online, it is vital to have a clear visibility into the health of your services and their performance, especially if they rely on the media or other components outside of your immediate control. Earlier in our blogpost we have covered how and why to use iperf3 for measurements of a performance between your hosts and speediest to measure a performance of an Internet connectivity. Today we’ll show how to automate this process with the help of Prometheus.
2
3
4
5
retrieval system, or transmitted in any form or by any
means, electronic, mechanical or photocopying, recording,
or otherwise, for commercial purposes without the
prior permission of the author.
How Can We Automate Monitoring?
Automation is not only about Ansible and Python. Knowing how you can properly use various applications, especially those great open source tools available on the market is a key to your success. At the same time, Ansible plays a key role in rolling out application these days, as it helps to ensure that deployment is done in a consistent way. Ansible is like Continue reading
Welcome to Security Week 2022!


Recent events are bringing cybersecurity to the forefront of many conversations.
Governments around the world are encouraging businesses to go “shields up” following Ukraine’s invasion. The current threat is significantly higher than before and any organization with Internet-facing infrastructure should put security as a top priority for the year.
To help keep services online, Cloudflare is also participating in the Critical Infrastructure Defense Project ensuring teams can get the best help to secure networks and applications more vulnerable to cyber threats, such as those in the medical, water and energy sectors.
As another example, not too long ago, Log4J, a high-severity vulnerability affecting many Java-based applications, also highlighted how important good security is on the Internet as attackers immediately started scanning for vulnerable applications within hours of the attack vector becoming public.
Unfortunately, these events are almost certainly not going to be our last reminders.
Over the next six days, we intend to tackle the broad topic of cyber security with a simple goal: ensure security is no longer an afterthought.
Security, however, is also hard, and you never know when “you’ve done enough”. The importance of good security practices should never be underestimated. Reliable and secure Continue reading
Worth Reading: Switching the Technology Stack
Did you ever wonder why a company would replace a working technology with an overhyped pile of half-baked code? Why we at $FAMOUS_COMPANY Switched to $HYPED_TECHNOLOGY by Saagar Jha is a hilarious take on the subject.
Want more? How about migrating your Exadata database to AWS?
Worth Reading: Switching the Technology Stack
Did you ever wonder why a company would replace a working technology with an overhyped pile of half-baked code? Why we at $FAMOUS_COMPANY Switched to $HYPED_TECHNOLOGY by Saagar Jha is a hilarious take on the subject.
Want more? How about migrating your Exadata database to AWS?
Maximum Flow Problems
Introduction
In optimization theory, Maximum Flow problems involve finding the maximum flow (or traffic) that can be sent from one place to another, subject to certain constraints. In this post, we will look at Maximum Flow algorithms applied to Networking and the questions they can help answer.
The main focus here will be the applied part, and we will only cover the surface of most algorithms as many of them requires Linear Programming and Optimization theory background.
Problem Setup
Assume that we have a small network connecting a few locations in the US using RSVP-TE for traffic management.
RSVP-TE allows us to find paths if there is not enough room on the shortest path, which removes the restriction that the
flows need to travel only on the shortest path.
In the below picture, we can see the Capacity and IGP cost of the links. From a graph representation perspective,
we will use MultiDigraph. Multi to represent multiple links, like between lax<-->iad, and Digraph for capturing the
unidirectional behavior of RSVP LSPs.
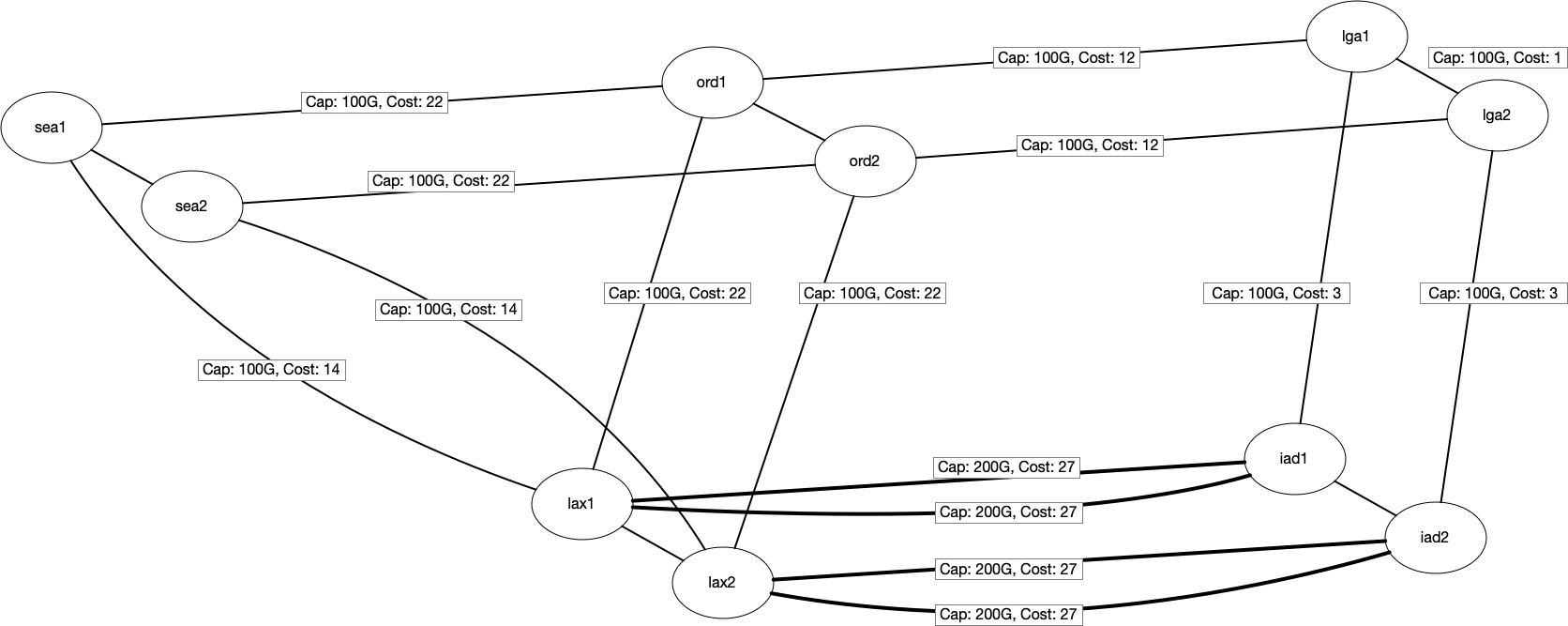
We will also assume that we already have some traffic routed between a few locations. The below table shows the existing traffic traveling between locations. For example, we Continue reading
AI Workloads Require Infrastructure Upgrades
Artificial intelligence workloads often require special infrastructure that previously was not considered needed for other demanding computational jobs.Trust Will Do You In
loc
If you’re a fan of the Gestalt IT Rundown that I do every week on the Gestalt IT YouTube channel, you have probably heard about the recent hacks of NVIDIA and Samsung. The original investigation into those hacks talked about using MDM platforms and other vectors to gain access to the information that was obtained by the hacking groups. An interesting tweet popped up on my feed yesterday that helped me reframe the attacks:
It would appear that the group behind these attacks are going after their targets the old fashioned way. With people. For illustration, see XKCD from 2009:

The Weakest Links
People are always the weakest link in any security situation. They choose to make something insecure through bad policy or by trying to evade the policy. Perhaps they are trying to do harm to the organization or even try to shine a light on Continue reading
Multi-vendor EVPN VXLAN setup with Containerlab
In this post, we deploy a multivendor EVPN L2 overlay fabric, with BGP in the underlay as well. The entire fabric deployment is automated with Ansible, and Containerlab is used to define and deploy the actual topology.
Dell 2161DS-2 serial port pinout
I picked up a Dell (Avocent) 2161DS-2 (same as 4161DS?) KVM recently, and needed to use the serial port to upgrade the software.
Naturally, the serial port pinout is non-standard and requires a proprietary cable which comes with the KVM. Dell part numbers 80DH7 and 3JY78 might be involved. I don't have, and have never seen these cables.
I was able to to find the RX, TX and Ground pins and interact with the system using 9600, 8, N, 1.
 |
| Pinout in red text |
 |
| Is the color coding inside these adaptors standardized? If so this may help. |
The system prints some unsolicited messages ("welcome" or somesuch) a little while after power-up.
Notes from upgrading the firmware from MacOS 12:
# Grab the firmware
URL="https://dl.dell.com/RACK SOLUTIONS/DELL_MULTI-DEVICE_A04_R301142.exe"
wget -P /tmp "$URL"
# Start MacOS tftp service
sudo launchctl load -w /System/Library/LaunchDaemons/tftp.plist
# Extract the firmware (it's a self-extracting exe, but we can open it with unzip)
sudo unzip -d /private/tftpboot "/tmp/$(basename "$URL")" Omega_DELL_1.3.51.0.fl
# Now, using the menu on the KVM serial port, point it toward the MacOS TFTP service
# to retrieve the Omega_DELL_1.3.51.0.fl file
Kremlin’s Aggression Divides Digital Ecosystems Along Tech Trenches
The invasion of Ukraine prompted providers to cease operations in Russia, setting the stage for a different kind of conflict as bullets still fly.External Lab Access With Ngrok and Containerlab
Thank you all for checking out my inaugural post on the Packet Pushers platform. I’ve been a long time fan of the content here and its pretty exciting to be one of the contributors. Sif Baksh recently asked John Capobianco and myself a very interesting question. @John_Capobianco and @Julio_PDX do know of a service where […]
The post External Lab Access With Ngrok and Containerlab appeared first on Packet Pushers.
Heavy Networking 621: Get Scalable Network Automation With Itential (Sponsored)
On today's Heavy Networking, sponsor Itential joins us to discuss how you can deliver a scalable and sustainable network automation system for your enterprise. Our guest is Peter Sprygada, VP of Product Management at Itential.
The post Heavy Networking 621: Get Scalable Network Automation With Itential (Sponsored) appeared first on Packet Pushers.