Quantum Computing and OpenFlow
I read an excellent rant by prof. Victor Galitski describing the current explosion of Quantum Computing hype, and couldn’t help being reminded of the OpenFlow brouhaha we experienced almost a decade ago – you could do a simple search-and-replace and the article would have been equally valid.
Enjoy… and remember the details for the next time your beloved vendor comes along with Quantum Computing slide deck.
Introducing Workers Usage Notifications
So you’ve built an application on the Workers platform. The first thing you might be wondering after pushing your code out into the world is “what does my production traffic look like?” How many requests is my Worker handling? How long are those requests taking? And as your production traffic evolves overtime it can be a lot to keep up with. The last thing you want is to be surprised by the traffic your serverless application is handling. But, you have a million things to do in your day job, and having to log in to the Workers dashboard every day to check usage statistics is one extra thing you shouldn’t need to worry about.
Today we’re excited to launch Workers usage notifications that proactively send relevant usage information directly to your inbox. Usage notifications come in two flavors. The first is a weekly summary of your Workers usage with a breakdown of your most popular Workers. The second flavor is an on-demand usage notification, triggered when a worker’s CPU usage is 25% above its average CPU usage over the previous seven days. This on-demand notification helps you proactively catch large changes in Workers usage as soon as those Continue reading
Pegasus Pisses Me Off

In this week’s episode of the Gestalt IT Rundown, I jumped on my soapbox a bit regarding the latest Pegasus exploit. If you’re not familiar with Pegasus you should catch up with the latest news.
Pegasus is a toolkit designed by NSO Group from Israel. It’s designed for counterterrorism investigations. It’s essentially a piece of malware that can be dropped on a mobile phone through a series of unpatched exploits that allows you to create records of text messages, photos, and phone calls and send them to a location for analysis. On the surface it sounds like a tool that could be used to covertly gather intelligence on someone of interest and ensure that they’re known to law enforcement agencies so they can be stopped in the event of some kind of criminal activity.
Letting the Horses Out
If that’s where Pegasus stopped, I’d probably not care one way or the other. A tool used by law enforcement to figure out how to stop things that are tough to defend against. But because you’re reading this post you know that’s not where it stopped. Pegasus wasn’t merely a tool developed by intelligence agencies for targeted use. If I had to Continue reading
IT Organizations Aiming to Deploy Home Office Network Hardware
To deliver a better user experience, IT organizations may need to deploy network infrastructure in home offices.Upgrading the Cloudflare China Network: better performance and security through product innovation and partnership


Core to Cloudflare’s mission of helping build a better Internet is making it easy for our customers to improve the performance, security, and reliability of their digital properties, no matter where in the world they might be. This includes Mainland China. Cloudflare has had customers using our service in China since 2015 and recently, we expanded our China presence through a partnership with JD Cloud, the cloud division of Chinese Internet giant, JD.com. We’ve also had a local office in Beijing for several years, which has given us a deep understanding of the Chinese Internet landscape as well as local customers.
The new Cloudflare China Network built in partnership with JD Cloud has been live for several months, with significant performance and security improvements compared to the previous in-country network. Today, we’re excited to describe the improvements we made to our DNS and DDoS systems, and provide data demonstrating the performance gains customers are seeing. All customers licensed to operate in China can now benefit from these innovations, with the click of a button in the Cloudflare dashboard or via the API.
Serving DNS inside China
With over 14% of all domains on the Internet using Cloudflare’s nameservers we Continue reading
Hedge 92: The IETF isn’t the Standards Police
In most areas of life, where the are standards, there is some kind of enforcing agency. For instance, there are water standards, and there is a water department that enforces these standards. There are electrical standards, and there is an entire infrastructure of organizations that make certain the fewest number of people are electrocuted as possible each year. What about Internet standards? Most people are surprised when they realize there is no such thing as a “standards police” in the Internet.
Listen in as George Michaelson, Evyonne Sharp, Tom Ammon, and Russ White discuss the reality of standards enforcement in the Internet ecosystem.
Day Two Cloud 107: Making The Management Mistake
Today on the Day Two Cloud podcast, Ethan and Ned discuss two new AWS courses from Ned, and then tell stories about the time they took management jobs they shouldn't have. They share lessons learned about transitioning from technical to managerial roles and why it was the wrong move for them.
The post Day Two Cloud 107: Making The Management Mistake appeared first on Packet Pushers.
Day Two Cloud 107: Making The Management Mistake
Today on the Day Two Cloud podcast, Ethan and Ned discuss two new AWS courses from Ned, and then tell stories about the time they took management jobs they shouldn't have. They share lessons learned about transitioning from technical to managerial roles and why it was the wrong move for them.Automatic Reply: Working Remote Today
The hybrid work model embraced during the pandemic introduces new challenges and can lead to disruptions of our corporate networks.LISP – OMP – BGP EVPN Interoperability – Part II: VPNv4 Update from Control Plane to Border-PxTR
The previous chapter describes how Edge-xTR-11 used LISP Map-Register message to advertise EID-to-RLOC information to MapServ-22. It also explained how MapSrv-22, as a role of Mapping Server, stores the information into Mapping Data Base. MapSrv-22 is also Map-Resolver. This means that when it receives the LISP Map-Requestmessage from the xTR device, it will respond with a Map-Reply message. If MapSrv-22 knows the EID-to-RLOC mapping, it places this information into the Map-Reply message. If MapSrv-22 doesn’t have mapping information, it instructs requesting xTR to forward traffic to its Proxy-xTR. This, however, is not the case in our example. What we want to do is advertise the EP1 reachability information to Border-PxTR. In order to do that, we need to a) export EID-to-RLOC information from the Mapping Data Base to instance-specific VRF_100 RIB. Then we can advertise it by using BGP and because we want to include virtual network identifier into update we use MP-BGP VPNv4 because there we have Route Target Attribute. The next sections describe the process in detail.
Phase 1: Map-Server - RIB Update
LISP Map-Server doesn’t install EID-to-RLOC mapping information from the Mapping Database into a RIB by default. To do that we need to export the information from the LISP Mapping DataBase to RIB by using the LISP Instance-specific command route-export site-registrations. Example 1-6 illustrates the update process. Example 1-7 shows the RIB entry concerning EP1 IP address 172.16.100.10/32 in VRF 100_NWKT. Due to redistribution, the route is shown as directly connected, via Null0. If you take a look at the timestamps in example 1-6 and compare it to timestamps in example 1-3, you will see that the RIB update happens right after the unreliable EID-to-RLOC registration process.
Complete device configuration can be found in chapter 1 Appendix 1.
Figure 1-10: EID-to-RLOC information from LISP to RIB.
Continue reading
Expanding Cloudflare to 25+ Cities in Brazil
Today, we are excited to announce an expansion we’ve been working on behind the scenes for the last two years: a 25+ city partnership with one of the largest ISPs in Brazil. This is one of the largest simultaneous single-country expansions we’ve done so far.
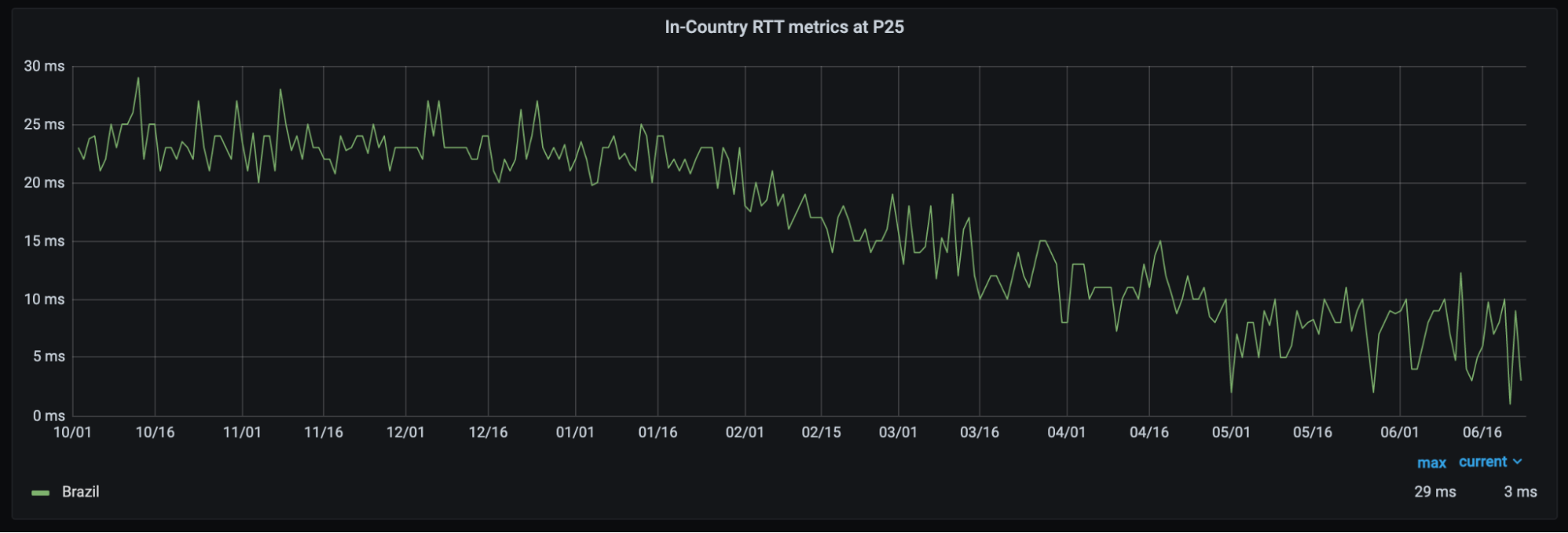
With this partnership, Brazilians throughout the country will see significant improvement to their Internet experience. Already, the 25th-percentile latency of non-bot traffic (we use that measure as an approximation of physical distance from our servers to end users) has dropped from the mid-20 millisecond range to sub-10 milliseconds. This benefit extends not only to the 25 million Internet properties on our network, but to the entire Internet with Cloudflare services like 1.1.1.1 and WARP. We expect that as we approach 25 cities in Brazil, latency will continue to drop while throughput increases.
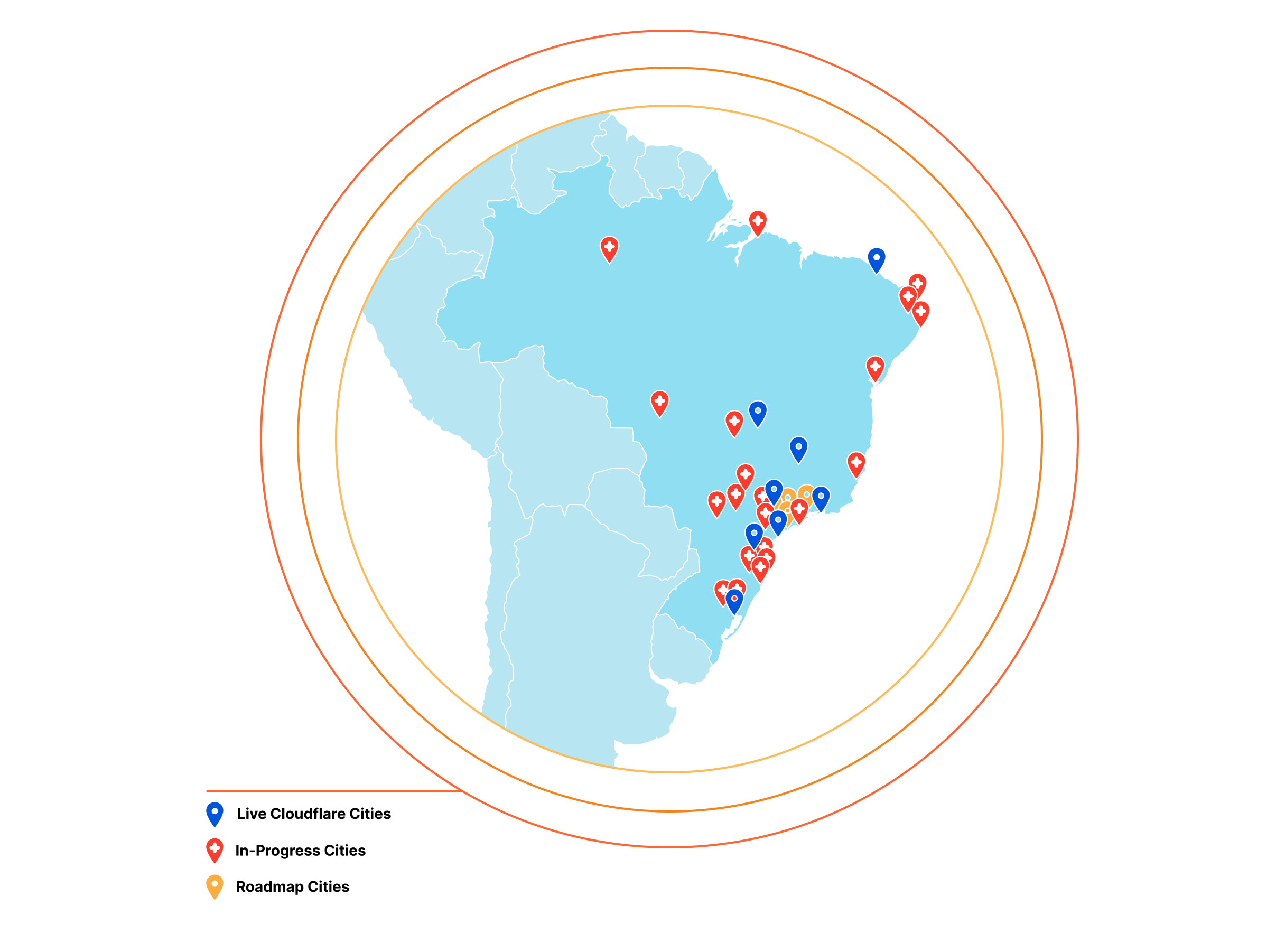
This partnership is part of our mission to help create a better Internet and the best development experience for all — not just those in major population centers or in Western markets — and we are excited to take this step on Continue reading
Cloud-based Communications Systems Offer Office Phone Alternative
Voice telephony and video conferencing combine to create the future of communication in the digital workplace.Full Stack Journey 056: Network Automation Progress And Problems
What's the latest with network automation? Where is the industry getting things right, and where is there more work to be done? How is public cloud influencing network automation? Scott Lowe welcomes Ethan Banks to the Full Stack Journey podcast for an update on the state of automation in networking.
The post Full Stack Journey 056: Network Automation Progress And Problems appeared first on Packet Pushers.
