Heavy Networking 553: Why Does BGP Need Link State?
Hannes Gredler stops by the Heavy Networking virtual studios to educate us on what BGP-LS is, the problems it aims to solve, how it differs from segment routing, and whether the industry is loading too many features onto the back of the BGP workhorse.
The post Heavy Networking 553: Why Does BGP Need Link State? appeared first on Packet Pushers.
Heavy Networking 553: Why Does BGP Need Link State?
Hannes Gredler stops by the Heavy Networking virtual studios to educate us on what BGP-LS is, the problems it aims to solve, how it differs from segment routing, and whether the industry is loading too many features onto the back of the BGP workhorse.Seeking Knowledge and Willful Ignorance
I had a great time recording a fun episode of Seeking Truth in Networking, an awesome podcast with my friends Derick Winkworth and Brandon Heller. We talked a lot about a variety of different topics, but the one I want to spend a few more minutes on here came in the first five minutes. Brandon asked me what question I liked to be asked and I mentioned that love to be asked about learning. My explanation included the following line:
I feel like the gap between people that don’t understand something and the willfully ignorant is that ability to take a step out and say “I don’t know the answer to this but I’m going to find out.”
I’ve always said that true learners are the ones that don’t accept the unknown. They want to find the answer. They want to be able to understand something as completely as they can. Those that I consider to be willfully ignorant choose not to do that.
Note that there is a difference between incidentally ignorant and willfully ignorant. People who are incidentally ignorant are unaware they don’t know something. They haven’t had the opportunity to learn or change their thought Continue reading
Explore VMware’s Virtual Cloud Network Vision with Tom Gillis
The past year has been filled with challenges. It’s been difficult to adapt to the new realities of how we work, how users access applications, and how we build out and scale our network infrastructures. But challenges lead to opportunities. In his Virtual Cloud Network keynote at VMworld 2020, Tom Gillis, general manager of the networking and security business unit at VMware, urged participants to rethink how they operate and then come up with new processes and approaches that will help them move faster into the future.
In his presentation, Gillis describes how forward-thinking companies are able to:
- Take the corporate network and stretch it into remote users’ living rooms,
- Deliver public cloud experiences to on-premises data centers, and
- Bridge the virtual and physical worlds in a true hybrid cloud environment with consistent policy and management enforcement.
With these capabilities (and there are VMware customers doing this today!), organizations can deploy a completed workload to any user across any infrastructure, including all the necessary networking and security bells and whistles, with a single click.
VMware enables this new approach via its Virtual Cloud Networking (VCN) portfolio. Whether through our SD-WAN technology delivering a LAN-like experience to distributed users, or Continue reading
Building A Network (no, the other kind)
A conversation in the Network Collective Slack prompted some conversation about how to build a network. No, not the packet switched networks that we’re all so familiar with, but rather a personal network of peers. Not everyone has the privilege to attend trade shows and conferences throughout the year, and all of us have lacked that privilege for a while now due to Covid, so how does one build a pervasive network without in-person events. We also discuss some methods to set yourself apart from the crowd in ways that don’t include peer relationships.
| Thank you to Bluecat Networks for sponsoring today’s episode. Bluecat is putting together some great content and a great community surrounding the topics of DNS, DHCP, and IPAM. You can join the Network VIP community and register for the next roundtable by going to bluecatnetworks.com/certainty. |  |
 |
Thank you to Unimus for sponsoring today’s episode. Unimus is a fast to deploy and easy to use Network Automation and Configuration Management solution. You can learn more about how you can start automating your network in under 15 minutes at unimus.net/nc. |
Outro Music:
Danger Storm Kevin MacLeod (incompetech.com)
Licensed under Continue reading
New White Paper: Considerations for Mandating Open Interfaces

People all around the world depend on the Internet to live their lives and do their jobs. Behind the surface of applications, online services depend on “interoperability” – the ability of software to work together.
For instance, this is what allows you to send a document from the Outlook account on your iPhone to a friend’s Gmail, then edit the document on a Samsung tablet before saving it in Alibaba cloud, and finally posting it on Twitter using an application like Hootsuite.
But as we recognized in the 2019 Global Internet Report, trends of consolidation in the Internet economy, particularly at the application layer and in web services, have spurred concerns and public debates on the need to regulate Big Tech. Among the proposed measures by policymakers, academics, and other thought leaders across the world is for software services and systems to be legally required to provide interoperability or open interfaces. Today we release a new white paper on this topic, with the aim to support and add depth to the discussions about the key considerations involved.
The general sentiment among competition experts, policymakers and other stakeholders is that existing competition policy is not addressing the economic and societal Continue reading
An introduction to three-phase power and PDUs
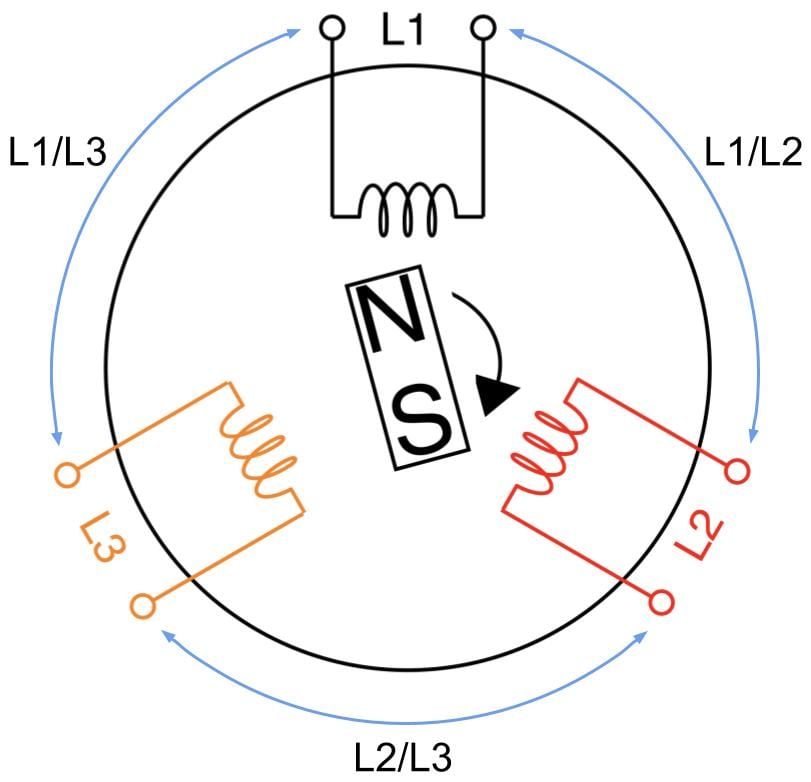
Our fleet of over 200 locations comprises various generations of servers and routers. And with the ever changing landscape of services and computing demands, it’s imperative that we manage power in our data centers right. This blog is a brief Electrical Engineering 101 session going over specifically how power distribution units (PDU) work, along with some good practices on how we use them. It appears to me that we could all use a bit more knowledge on this topic, and more love and appreciation of something that’s critical but usually taken for granted, like hot showers and opposable thumbs.
A PDU is a device used in data centers to distribute power to multiple rack-mounted machines. It’s an industrial grade power strip typically designed to power an average consumption of about seven US households. Advanced models have monitoring features and can be accessed via SSH or webGUI to turn on and off power outlets. How we choose a PDU depends on what country the data center is and what it provides in terms of voltage, phase, and plug type.

For each of our racks, all of our dual power-supply (PSU) servers are cabled to one of the two vertically mounted PDUs. Continue reading
Diversity and The Digital Divide: Thoughts From Tech Leaders

Leaders from across the tech industry and beyond recently joined us for Cloudflare’s Birthday Week, helping us celebrate Cloudflare’s 10th birthday. Many of them touched on the importance of diversity and making the Internet accessible to everyone.
Here are some of the highlights.
On the value of soliciting feedback
Selina Tobaccowala
Chief Digital Officer at Openfit, Co-Founder of Gixo
Former President & CTO of SurveyMonkey

When you think about diversity and inclusion, unfortunately, it's often only the loudest voice, the squeakiest wheel [who gets heard]. And what a survey allows you to do is let people's voices be heard who are not always willing to raise their hand or speak the loudest.
So at SurveyMonkey, we always made sure that when we were thinking about user testing and we were thinking about usability testing — that it was that broad swath of the customer because you wanted people across all different segments to submit their opinion.
I think that collecting data in a way that can be anonymized, collecting data in a way that lets people have a thoughtful versus always off the cuff conversation is really important. And what we also provided was a benchmarking product, because if you Continue reading
Video: Should You Build or Buy a Solution?
After figuring out what business problem you’re trying to solve and what the users expect to get from you it’s time for the next crucial question: should you buy a shrink-wrapped product/solution or build your own? I addressed that question in the third part of Focus on Business Challenges First presentation.
Not surprisingly, the same dilemma applies to network automation solutions, and is often the source of endless time-wasting discussions that I really should have stopped engaging in, but sometimes duty calls ;)
Video: Should You Build or Buy a Solution?
After figuring out what business problem you’re trying to solve and what the users expect to get from you it’s time for the next crucial question: should you buy a shrink-wrapped product/solution or build your own? I addressed that question in the third part of Focus on Business Challenges First presentation.
Not surprisingly, the same dilemma applies to network automation solutions, and is often the source of endless time-wasting discussions that I really should have stopped engaging in, but sometimes duty calls ;)
Rails Generators Cheat Sheet
Ruby on Rails generators quick reference.What Does A Good Network Design Look Like? – James Bensley, Senior Network Design Engineer
Is a good network design just about technical specifications or should you take into account business drivers and needs? James is a network design veteran and presented on this topic at UKNOF45. We talk about design considerations, tips and tricks, drivers and motivations, asking the question behind the question and even about a book that is ‘in the works’. James is very active on Twitter, LinkedIn and can be reached via [email protected].

Tom Hollingsworth | Lessons from Tech Field Day and How to Spot BS
Brandon and Derick explore communities of IT folks, the wisdom of backup plans, and shifty vendors with Tech Field Day Organizer Tom Hollingsworth, also known as "The Networking Nerd."