T-Mobile Claims 5 Standalone 5G Firsts
Today’s 5G networks are effectively piggybacking on 4G LTE, but T-Mobile and others soon plan to...
Basic Linux Networking tips and tricks part-3: ss and netstat commands

Here is the third post of the series on basic network troubleshooting and tools under RHEL / CentOS. In this post, I will talk about the netstat and ss commands. Others posts of the series This post is part of a series about basic Linux Networking tips and tricks. The others posts of this series are: The ip and nmcli commands The mtr command The ss and netstat commands The curl command netstat The netstat command is a network utility used to display network connections, protocol or interfaces…
The post Basic Linux Networking tips and tricks part-3: ss and netstat commands appeared first on AboutNetworks.net.
Network Break 282: NVIDIA Completes Mellanox Acquisition; SpaceX Sets Date For Satellite Internet Beta Testing
The latest Network Break podcast examines NVIDIA's just-completed Mellanox acquisition, beta testing dates from SpaceX, the latest version of Cumulus Networks' NetQ management software, plus quarterly financial news for Juniper, Microsoft, and AmazonNetwork Break 282: NVIDIA Completes Mellanox Acquisition; SpaceX Sets Date For Satellite Internet Beta Testing
The latest Network Break podcast examines NVIDIA's just-completed Mellanox acquisition, beta testing dates from SpaceX, the latest version of Cumulus Networks' NetQ management software, plus quarterly financial news for Juniper, Microsoft, and Amazon
The post Network Break 282: NVIDIA Completes Mellanox Acquisition; SpaceX Sets Date For Satellite Internet Beta Testing appeared first on Packet Pushers.
State of the Internet – Job Snijders, IP Development Engineer @ NTT
In this episode Job Snijders shares some of his perspective on the current state of the Internet.
As you can expect when talking to Job, one of the topics is BGP Routing Security. We also touch on his work in IETF, OpenBSD, transit vs peering and IPv4 address exhaustion.
Listen below or subscribe in your favourite podcast player on the home screen!

A single dashboard for Cloudflare for Teams

Starting today, Cloudflare Access can now be used in the Cloudflare for Teams dashboard. You can manage security policies for your people and devices in the same place that you build zero-trust rules to protect your applications and resources. Everything is now in one place in a single dashboard.
We are excited to launch a new UI that can be used across the entire Teams platform, but we didn’t build this dashboard just for the sake of a new look-and-feel. While migrating the Access dashboard, we focused on solving one of the largest sources of user confusion in the product.
This post breaks down why the original UI caused some headaches, how we think about objects in Cloudflare for Teams, and how we set out to fix the way we display that to our users.
Cloudflare Access
Cloudflare Access is one-half of Cloudflare for Teams, a security platform that runs on Cloudflare’s network. Teams protects users, devices and data without compromising experience or performance. We built Cloudflare Access to solve our own headaches with private networks as we grew from a team concentrated in a single office to a globally distributed organization.
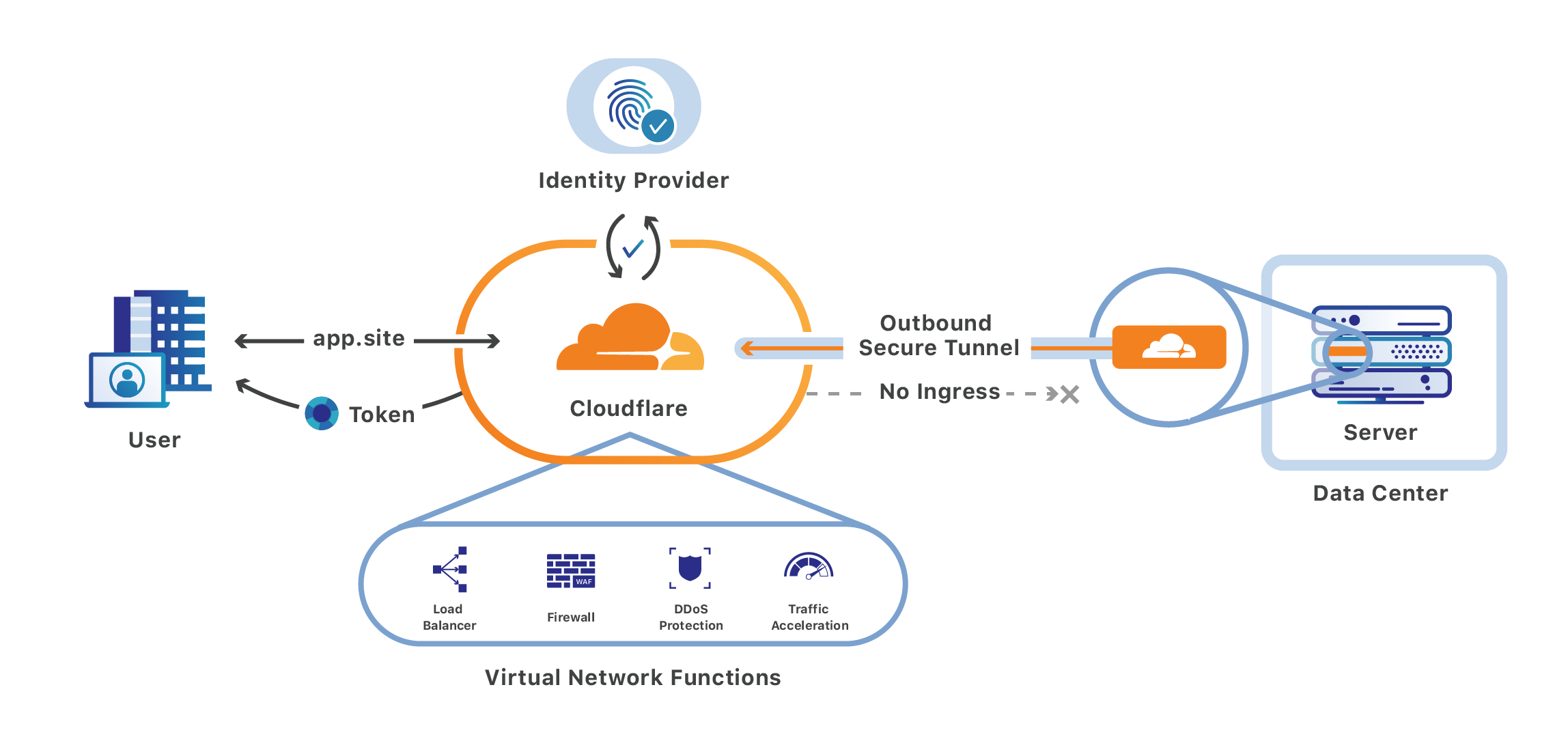
Cloudflare Access replaces corporate VPNs with Cloudflare’s Continue reading
Cisco Debunks Cybersecurity Myths
Cisco’s latest security report, based on a survey of almost 500 SMBs, aims to debunk myths about...
Key Factors in Attracting and Retaining Talent
Yesterday I posted a tweet on company culture that received a lot of positive feedback:
People thought this should be saved in a blog post, so this is it.
Company Culture
Do you want to attract and retain talent and high performers? Of course you do. Do you understand how to do that and are you willing to change your company culture?
Everything starts with culture. You may have heard the quote “Culture eats strategy for breakfast”, meaning that even the best stratety can’t compete with a company that has a great culture. Strategy without culture does not create success.
Gimmicks Are Not Culture
Most companies, such as the web scalers, often confuse gimmicks with culture. We have great company culture! We have ping pong tables, flipper games and even artists who play music for us! While these things can be entertaining, don’t mistake them for culture. Continue reading
The Week in Internet News: Classroom in a Car

Searching for a signal: CNN has a story about a teacher in rural Virginia who drives 20 minutes to find a good WiFi signal in order to work. The middle school history teacher is one of about 18 million U.S. residents who lack access to high-speed broadband, according to the Federal Communications Commission. The teacher “lives in a valley between two mountains, where the only available home internet option is a satellite connection. Her emails can take 30 seconds to load, only to quit mid-message. She can’t even open files on Google Drive, let alone upload lesson modules or get on a Zoom call with colleagues.”
Demanding access: Meanwhile, in Oakland, California, hundreds of teachers and students are calling for free access to the Internet, demanding that the school district and mayor “take all necessary measures” to ensure that students have access, KTVU reports. “There is no equity in education for our most vulnerable students if all Oakland families do not have access to the internet,” said Keith Brown, president of the Oakland Education Association, said.
Legislating access: In the U.S. Congress, Senate Democrats are introducing a bill that would create a new $4 billion fund for schools Continue reading
PATCHBOX Setup.exe Review
Over the past few months, while browsing social media, I came across an ad for the PATCHBOX Setup.exe and it …Explore: BGP in Data Center Fabrics
Got mentioned in this tweet a while ago:
Watching @ApstraInc youtube stream regarding BGP in the DC with @doyleassoc and @jtantsura.Maybe BGP is getting bigger and bigger traction from big enterprise data centers but I still see an IGP being used frequently. I am eager to have @ioshints opinion on that hot subject.
Maybe I’ve missed some breaking news, but assuming I haven’t my opinion on that subject hasn’t changed.
Time in Suzieq
Time, time, time, see what’s become of me, while I looked around for my possibilities - Simon & Garfunkel One of the powerful features of Suzieq is the ability to observe the state of the network at a time in the past, or to play back changes in state in...Headcount: Firings, Hirings, and Retirings — April 2020
AT&T selected Stankey as its new CEO; Google to slow hiring; Cisco vowed no job cuts; plus the...
Getting Started with Cluster API using Docker
Cluster API (CAPI) is a relatively new project aimed at deploying Kubernetes clusters using a declarative API (think YAML). The official documentation (a.k.a. the Cluster API book), does a very good job explaining the main concepts and goals of the project. I always find that one of the best ways to explore new technology is to see how it works locally, on my laptop, and Cluster API has a special “Docker” infrastructure provider (CAPD) specifically for that. However, the official documentation for how to setup a docker managed cluster is very poor and fractured. In this post, I’ll try to demonstrate the complete journey to deploy a single CAPI-managed k8s cluster and provide some explanation of what happens behind the scene so that its easier to troubleshoot when things go wrong.
Prerequisites
Two things must be pre-installed before we can start building our test clusters:
- kind - a tool to setup k8s clusters in docker containers, it will be used as a management (a.k.a. bootstrap) cluster.
- clusterctl - a command line tool to interact with the management cluster.
We’re gonna need run a few scripts from the Cluster API Github repo, so let’s get a copy Continue reading
Heavy Networking 515: A Decade of Network Podcasting
In this brief chat, Ethan & Greg discuss where we came from and where we are going. Note the retro music we used and check out outtro too.
The post Heavy Networking 515: A Decade of Network Podcasting appeared first on Packet Pushers.
Heavy Networking 515: A Decade of Network Podcasting
In this brief chat, Ethan & Greg discuss where we came from and where we are going. Note the retro music we used and check out outtro too.CloudGenix Key to Palo Alto Networks SASE Play
Palo Alto networks purchased CloudGenix at the end of March for $420 million in a bid to bolster...
Our Work to Make the Internet for Everyone Marches On
Over the past several months the Internet Society has been working on a transaction to sell Public Interest Registry (PIR), operator of .ORG and other top-level domains, to Ethos Capital. Under PIR’s registry agreements, the Internet Corporation for Assigned Names and Numbers (ICANN) had to consent to this indirect change of control. ICANN has now announced that it does not consent to the transaction.
I am, of course, disappointed by ICANN’s decision, though I am pleased it was finally reached. ICANN took much longer than it should have done to vote on the transaction. In my view, ICANN stepped outside its remit by acting as a regulator it was never intended to be. What began as a routine change of indirect control – the type ICANN has expeditiously approved on multiple occasions in the past – resulted in months and months of review and analysis. The outcome does not seem consistent with ICANN’s prior decisions in similar cases. It should concern the Internet community that ICANN has shown itself to be much more susceptible to political pressure than its limited mandate would recommend.
Nevertheless, ICANN has now rendered a clear decision. This brings to a close a period Continue reading
Daily Roundup: AWS Q1 Tops $10B Revenue
AWS topped $10 billion in Q1; Cisco squashed yet another SD-WAN bug; and Fortinet CISO talked...
Verizon Virtualization Efforts Vanquished COVID-19 Chaos
“If we hadn't done virtualization, this would have been a multi-week, multi-month effort to bring...